FM 3-0 OPERATIONS
Foreword
The United States Army has always served to protect the Nation and preserve the peace. Historically, this has always meant preparing for and, when necessary, fighting and winning our Nation’s wars. The Army must always be ready to fight and win. In this era of great power competition, the Army must always campaign aggressively to protect our national interests.
We are living in very challenging times. There is not a time in recent history that is so potentially dangerous. Russia, our acute threat, is conducting an unprovoked war on the sovereign country of Ukraine. Our pacing challenge, China, with an economy nearly equal in size to ours, is building a world-class military to challenge us and threatening its neighbors, including Taiwan. As we focus on China and Russia, we cannot take our eyes off our other persistent threats: North Korea, Iran, and violent extremists. In addition, we are still dealing with the challenges of COVID and unprecedented natural disasters throughout the country. Despite all these challenges and threats, we continue to advance in the Army’s greatest transformation in over 40 years, as we pivot from decades of counterinsurgency and counterterrorism to large-scale combat operations.
Every 40 years the Army experiences a major transformation. In 1973, the Arab–Israeli War drove Army senior leaders and General Don Starry to relook the lessons learned in that conflict to counter the Soviet Union. Those efforts resulted in what we know today as Air-Land Battle. In 1991, the Army and the joint force executed that doctrine with great efficacy in OPERATION DESERT STORM, quickly liberating Kuwait. We are at a similar inflection point with lessons learned coming in from the 2nd Nagorno-Karabakh War and the ongoing Russo-Ukraine War. These lessons have and continue to shape our transformational war fighting concept of multidomain operations. Multidomain operations started as an operating concept, and now we are solidifying it into doctrine. This concept is shaping the Army and transforming our people, readiness, and modernization efforts to meet current and future challenges and define the Army of 2030.
FM 3-0 demonstrates the first principles of speed, range, and convergence of the cutting-edge technologies needed to achieve future decision dominance and overmatch against our adversaries. It reflects the vital role the Army plays as the force that joint force commanders need to hold critical terrain, assure allies and partners, defeat the most dangerous enemies in close combat anywhere in the world, and consolidate gains to achieve enduring strategic outcomes for the Nation. Two critical elements of multidomain operations, space and cyberspace capabilities, have been employed by Army forces for more than two decades, but never during conflict with opponents capable of effectively contesting the U.S. joint force in space or cyberspace. Air and maritime capabilities have long enabled successful operations on land, but it has been decades since air-ground integration and close cooperation between land and naval forces have been effectively challenged by a threat.
FM 3-0 remains rooted in the principles of war and reinforces the offensive mindset. It provides a simple definition of multidomain operations that applies at all echelons. The new operational environment model helps leaders visualize the five domains and understand their interrelationship through the physical, information, and human dimensions. FM 3-0 introduces new tenets and imperatives and provides an operational framework that helps echelons better organize forces in terms of time, space, and purpose. It describes operations in the context of competition, crisis, and armed conflict. It also addresses the unique considerations for applying landpower in maritime environments and the unique demands of, and requirements for, combat leadership.
Success demands competent leaders who apply doctrine with judgment. Therefore, I challenge you all to learn and then assess doctrine during training and operations. Engage about it in professional discourse and make it better. That is how the Army will fight and win in the future.
People first, winning matters, and we remain Army strong!
JAMES C. MCCONVILLE
GENERAL, UNITED STATES ARMY
CHIEF OF STAFF
Contents
PREFACE
INTRODUCTION
Chapter 1 - FOUNDATIONS OF OPERATIONS
Army Operations
Multidomain Operations
Challenges for Army Forces
Lethality: Overcoming Challenges
War and Warfare
Understanding an Operational Environment
Chapter 2 - GENERATING AND APPLYING COMBAT POWER
Warfighting Functions
Combat Power
Strategic Environment
Unified Action and Army Forces
Chapter 3 - FUNDAMENTALS OF OPERATIONS
Section I – Multidomain Operations: The Army’s Operational Concept
Section II – Tenets and Imperatives
Tenets
Imperatives
Section III – Operational Approach and Operational Framework
Operational Approach
Strategic Framework
Operational Framework
Chapter 4 - OPERATIONS DURING COMPETITION BELOW ARMED CONFLICT
Overview of Operations During Competition
Adversary Methods During Competition
Preparation for Large-Scale Combat Operations
Relative Advantages During Competition
Interagency Coordination
Competition Activities
Roles of Army Echelons during Competition
Consolidating Gains During Competition
Transition to Crisis and Armed Conflict
Chapter 5 - OPERATIONS DURING CRISIS
Overview of Operations During Crisis
Adversary Methods During Crisis
Operations Security
Relative Advantages
Army Support to the Joint Force During Crisis
Force Projection
Army Echelons During Crisis
Consolidating Gains
Transition to Competition or Armed Conflict
Chapter 6 - OPERATIONS DURING ARMED CONFLICT
Section I – Armed Conflict and Large-Scale Combat Operations
Enemy Approaches to Armed Conflict
Relative Advantages During Armed Conflict
Operating as Part of the Joint Force
Applying Defeat Mechanisms
Enabling Operations
Section II – Defensive Operations
Purpose and Conditions for the Defense
Characteristics of the Defense
Enemy Offense
Types of Defensive Operations
Defensive Operational Framework Considerations
Transition to Offense
Section III – Offensive Operations
Purpose and Conditions for the Offense
Characteristics of the Offense
Enemy Defense
Types of Offensive Operations
Offensive Operational Framework Considerations
Transition to Defense and Stability
Transition to Post-Conflict Competition
Chapter 7 - ARMY OPERATIONS IN MARITIME ENVIRONMENTS
Section I – Overview of the Maritime Environment
Physical Characteristics of the Maritime Environment
Considerations Unique to the Maritime Environment
Section II – Maritime Environment Planning and Operational Framework
Planning Considerations for a Maritime Environment
Applying the Operational Framework
Section III – Operational Considerations for a Maritime Environment
Establish Command and Control
Defend and Control Key Terrain
Defeat Components of Enemy Antiaccess and Area Denial and Enable Joint Offensive Operations
Sustain Large-Scale Combat Operations in Maritime Environments
Chapter 8 - LEADERSHIP DURING OPERATIONS
The Art of Command and the Commander
Applying the Art of Command
Driving the Operations Process
Adapting Formations for Missions and Transitions
Appendix A - THE PRINCIPLES OF WAR
Appendix B - COMMAND AND SUPPORT RELATIONSHIPS
Appendix C - CONTESTED DEPLOYMENTS
GLOSSARY
INDEX
Figures
Introductory figure. FM 3-0 logic chart
Figure 1-1. Operational categories and the spectrum of violence
Figure 1-2. Levels of warfare
Figure 1-3. Army strategic contexts and operational categories
Figure 1-4. Domains and dimensions of an operational environment
Figure 2-1. Notional U.S. European Command preclusion example
Figure 2-2. Notional U.S. Indo-Pacific Command preclusion example
Figure 2-3. Examples of operations and activities
Figure 3-1. Convergence
Figure 3-2. The operational framework in the context of the strategic framework
Figure 3-3. Notional corps area of operations with noncontiguous divisions
Figure 3-4. Notional corps deep, close, and rear areas with contiguous divisions
Figure 5-1. Simultaneous flexible deterrent and response option examples
Figure 6-1. Doctrinal template of depths and frontages
Figure 6-2. Notional roles and responsibilities in terms of time, space, and purpose at different echelons
Figure 6-3. Fires assets of a notional theater-level integrated fires command
Figure 6-4. Notional enemy offensive operation
Figure 6-5. Notional operational framework during defensive operations
Figure 6-6. Notional enemy maneuver defense
Figure 6-7. Notional operational framework during offensive operations
Figure 7-1. Operations in Malaya
Figure 7-2. Notional corps area of operation with maritime aspects
Figure 8-1. The operations process
Figure B-1. Joint command relationships
Tables
Introductory table. New and modified terms
Table 1-1. Principles of war
Table 5-1. Potential Army contributions to joint flexible deterrent and response options
Table B-1. Joint support categories
Table B-2. Army command relationships
Table B-3. Army support relationships
Table B-4. Other relationships
Table B-5. North Atlantic Treaty Organization command relationships
Vignettes
Systems Warfare and Sanctuary: Eastern Ukraine 2014
Second Nagorno Karabakh War: September–November 2020
Failure to Prepare for War: Philippines, 1941
Successful Engagement: State Partnership Program
Liberia: OPERATION UNITED ASSISTANCE
Effective Response: OPERATION PAUL BUNYAN
Deployment Friction: Task Force Ironhorse in OPERATION IRAQI FREEDOM
Crisis Response: Baghdad Embassy Attack
Defeat of the North Korean People’s Army, September 1950
Disintegration of Egyptian Defense: 1973 Arab-Israeli War
Faulty Assumptions—Defeat Across Multiple Domains in Malaya
Commanding Forward—LTG Eichelberger at Buna
Initiative in the Absence of Orders – Naval Bombers at Midway
Crosstalk in the Desert—VII Corps in the Gulf War
Notional Threat Open Source and Cyberspace Collection
Adversary Impacts on Civilian Infrastructure
Preface
FM 3-0 expands on the Army’s capstone doctrine for multidomain operations described in ADP 3-0. It describes how Army forces contribute landpower to the joint force and integrate joint capabilities into operations on land to achieve military objectives and fulfill policy aims. FM 3-0 focuses on large-scale combat operations and their relationship to the full range of military operations that support joint campaigning.
FM 3-0 is applicable to all members of the profession of arms: leaders, Soldiers, and Army Civilians. The principal audience for FM 3-0 is commanders, staffs, and leaders of theater armies, corps, divisions, and brigades. This manual provides the foundation for training and Army education system curricula and future capabilities development across doctrine, organization, training, materiel, leadership and education, personnel, facilities, and policy (known as DOTMLPF-P).
To comprehend the doctrine contained in FM 3-0, readers must first understand the Army’s mission, organization, and roles described in ADP 1. They must understand the operations process, operational art, and warfighting functions (command and control [C2], intelligence, fires, movement and maneuver, protection, and sustainment) described in ADP 3-0. Readers must understand the tactics described in ADP 3-90 and stability operations covered in ADP 3-07. They should also understand irregular warfare, described across multiple manuals, including ADP 3-05, FM 3-05, FM 3-18, and FM 3-24.
Army leaders must understand joint doctrine and use it when communicating and coordinating directly with the joint force. JP 3-0 establishes the baseline operations doctrine for the joint force.
When conducting multinational operations, commanders use the allied or other appropriate doctrine according to the situation. Readers must be familiar with FM 3-16 to understand multinational operations.
AJP-01 establishes the capstone doctrine for North Atlantic Treaty Organization (NATO) military operations. Commanders, staffs, and subordinates ensure that their decisions and actions comply with all applicable United States, international, and host-nation laws and regulations, and all applicable international treaties and agreements. Commanders at all levels ensure that their Soldiers operate in accordance with the law of armed conflict and applicable rules of engagement. (See FM 6-27 for more information on the law of war.) They also adhere to the Army Ethic as described in ADP 6-22.
FM 3-0 uses joint terms where applicable. Selected joint and Army terms and definitions appear in both the glossary and the text. Terms for which FM 3-0 is the proponent publication (the authority) are presented in italics and bold font in the text and marked with an asterisk (*) in the glossary. When first defined in the text, a term for which FM 3-0 is the proponent publication is boldfaced and italicized, and the definition is boldfaced. When first defining other proponent definitions in the text, the term is italicized, and the number of the proponent publication follows the definition.
The proponent of FM 3-0 is the United States Army Combined Arms Center. The preparing agency is the Combined Arms Doctrine Directorate, United States Army Combined Arms Center. Send comments and recommendations by e-mail to usarmy.leavenworth.mccoe.mbx.cadd-org-mailbox@army.mil on DA Form 2028 (Recommended Changes to Publications and Blank Forms) to Commander, United States Army Combined Arms Center and Fort Leavenworth, ATZL-MCD (FM 3-0), 300 McPherson Avenue, Fort Leavenworth, KS 66027-2337; or submit an electronic DA Form 2028.
Introduction
This version of FM 3-0 establishes multidomain operations as the Army’s operational concept. Conceptually, multidomain operations reflect an evolutionary inflection point, building on the incremental changes in doctrine as the operational environment has changed over the last forty years. In practice, however, these conceptual changes will have revolutionary impacts on how the Army conducts operations in the coming decades. The 2017 version of FM 3-0 introduced many multidomain considerations and ideas. This version of FM 3-0 codifies the multidomain approach to operations in terms of the combined arms employment of capabilities from multiple domains. The multidomain operations concept draws from previous Army operational concepts, including AirLand Battle, Full Spectrum Operations, and Unified Land Operations.
General Donn A. Starry’s description of the “extended battlefield” and the associated concept of AirLand Battle helped visualize the battlefield of the time—a battlefield now also extended into the maritime, space, and cyberspace domains. AirLand Battle demanded the integration of air and ground capabilities to attack enemy second echelon forces at extended ranges. Today, multidomain operations require integration of Army and joint capabilities from all domains to defeat the enemy’s integrated fires complexes and air defense systems so that maneuver forces can exploit the resulting freedom of action. The ability to maneuver to seize or retain key terrain and exert control over resources and people for as long as is necessary to achieve tactical, operational, and strategic objectives makes ground forces foundational to joint force success. During competition and crisis, forward-stationed Army forces holding key land areas provide “stand-on” capabilities that counter adversary standoff approaches, reduce risk to joint force projection, deter adversary aggression, and achieve national and joint objectives. During conflict, maneuvering ground forces with the right capabilities ultimately enable operations in the other domains.
Full Spectrum Operations accounted for the operations that Army forces conducted outside the bounds of armed conflict. This version of FM 3-0 updates this material for the present by describing how Army forces operate during competition below armed conflict and during crisis. It goes a step further than Full Spectrum Operations by describing how these operations set conditions for success during armed conflict.
Unified Land Operations emphasized the integration and synchronization of Army, joint, and other unified action partners during operations. The 2017 version of FM 3-0 updated unified land operations and shifted the Army’s readiness focus from counterinsurgency to large-scale combat operations. It incorporated elements of the multidomain operations concept, particularly the operational environment and its considerations. This version of FM 3-0 retains the focus on large-scale combat operations. It also builds on the importance of integrating joint and multinational capabilities and expands the combined arms approach with a focus on creating complementary and reinforcing effects with capabilities from multiple domains. By deliberately looking beyond traditional methods of integration generally focused on one or two domains, Army forces can expand opportunities for the joint force and create more dilemmas for the enemy.
The nature of war remains unchanged. The model for understanding an operational environment, specifically the physical, information, and human dimensions, reinforces the Clausewitzian idea that war is an act of force to compel the enemy’s will. In other words, physical action can influence human perceptions, behavior, and decision making. Although there are new capabilities in space and cyberspace, Army forces use them just as they employ any other capability—to accomplish missions on land.
The logic chart for this manual is shown in the introductory figure on page x. The logic chart begins with identifying the methods used by peer threats to contest the joint force and how the joint force and Army forces counter those approaches through multidomain operations. Multidomain operations are the Army’s contribution to unified action, conducted by Army echelons in an operational environment consisting of five domains and three dimensions, and the strategic contexts of competition, crisis, and armed conflict. It concludes with a description of multidomain operations through guiding principles of war, tenets, and imperatives that enable Army forces to accomplish missions, defeat enemy forces, and meet objectives.

FM 3-0 contains eight chapters and three appendixes:
Chapter 1 describes the challenges faced by Army forces and how multidomain operations help resolve them. It describes the Army’s vision of war and warfare, the strategic contexts in which Army forces conduct operations, and the operational environment, including the domains and dimensions.
Chapter 2 describes how the synchronization of warfighting functions generates combat power to apply against enemy forces. It then describes threats and their methods, and how Army forces counter these threat methods through unified action and joint capabilities.
Chapter 3 explains multidomain operations in detail, describing the tenets and imperatives of operations. It then highlights key elements of an operational approach and the operational framework.
Chapter 4 describes how Army forces operate during competition to set conditions for armed conflict and counter adversary malign behavior.
Chapter 5 describes how Army forces provide options during crisis to prevent armed conflict while continuing to fulfill political aims.
Chapter 6 describes how Army forces operate during armed conflict, with a focus on how to enable the joint force and integrate capabilities from all domains in large-scale combat operations.
Chapter 7 describes how Army forces operate in the unique conditions of maritime environments.
Chapter 8 describes the role of commanders and leaders in the demanding conditions of large-scale combat operations.
Appendix A provides an overview of the principles of war.
Appendix B describes command and support relationships.
Appendix C describes considerations for when enemy forces contest deployment.
The introductory table on page xii outlines changes to Army terminology reflected in FM 3-0.
| Term | Action |
|---|
| agility | New term and definition |
| close operations | New term and definition |
| conventional warfare | New term and definition |
| convergence | New term and definition |
| conventional warfare | New term and definition |
| cyberspace domain | New term and definition |
| deep operations | New term and definition |
| disintegrate | FM 3-0 becomes proponent and modifies term. |
| dislocate | FM 3-0 becomes proponent and modifies term. |
| domain | New term and definition |
| endurance | New term and definition |
| human dimension | New term and definition |
| informational considerations | New term and definition |
| information dimension | New term and definition |
| irregular warfare | New Army-specific definition |
| lethality | New term and definition |
| multidomain operations | New term and definition |
| national strategic level of warfare | New term and definition |
| physical dimension | New term and definition |
| multidomain operations | FM 3-0 becomes proponent and modifies term. |
| protection warfighting function | New term and definition |
| rear operations | New term and definition |
| relative advantage | New term and definition |
| sector | New term and definition |
| setting the theater | New term and definition |
| space domain | FM 3-0 becomes proponent and modifies term. |
| support area operations | New term and definition |
| theater strategic level of warfare | New term and definition |
| zone | New term and definition |
Chapter 1 - Foundations of Operations
This chapter describes the range of military operations and the Army’s focus on readiness to conduct large-scale combat operations. It describes how Army forces meet challenges and conduct multidomain operations as part of a joint and multinational force. Beginning with the Army’s view of war and warfare, this chapter describes key concepts that help leaders understand an operational environment.
ARMY OPERATIONS
1-1. The Army’s primary mission is to organize, train, and equip its forces to conduct prompt and sustained land combat to defeat enemy ground forces and seize, occupy, and defend land areas. It supports four strategic roles for the joint force. Army forces shape operational environments, counter aggression on land during crisis, prevail during large-scale ground combat, and consolidate gains. The Army fulfills its strategic roles by providing forces for joint campaigns that enable integrated deterrence of adversaries outside of conflict and the defeat of enemies during conflict or war. The strategic roles clarify the overall purposes for which Army forces conduct multidomain operations on behalf of joint force commanders (JFCs) in the pursuit of a stable environment and other policy objectives. Fulfilling policy objectives requires national-level leaders to orchestrate all instruments of national power throughout the entire government and coalition, in a manner commensurate with national will. (See JP 3-0 for more information on joint campaigns and deterrence. See ADP 3-0 for more information on the Army’s strategic roles.)
1-2. Military operations on land are foundational to operations in other domains because almost all capabilities, no matter where employed, are ultimately based on or controlled from land. While any particular domain may dominate military considerations in a specific context, conflicts are usually resolved on land because that is where people live and make political decisions and where the basis of national power exists.
1-3. Army forces achieve objectives through the conduct of operations. An operation is a sequence of tactical actions with a common purpose or unifying theme (JP 1, Volume 1). Operations vary in many ways. They occur in all kinds of physical environments, including urban, subterranean, desert, jungle, mountain, maritime, and arctic. Operations vary in scale of forces involved and duration. Operations change factors in the physical, information, and human dimensions of an operational environment.
1-4. The complex environment in which operations occur demands leaders who understand both the science and art of operations. Understanding the science of operations—such as combat power ratios, weapons ranges, and movement tables—helps leaders improve synchronization and reduce risk. However, there is no way to eliminate uncertainty, and leaders must exercise operational art to make decisions and assume risk. Intangible factors, such as the impact of leadership on morale, using shock effect to defeat enemy forces, and supportive populations are fundamentally human factors that can overcome physical disadvantages and often decide the outcomes of an operation. (See ADP 3-0 for more information on the art and science of operations.)
1-5. Army forces meet a diverse array of challenges and contribute to national objectives across a wide range of operational categories, including large-scale combat operations, limited contingency operations, crisis response, and support to security cooperation. (See figure 1-1 on page 1-2 for a depiction of operational categories and the spectrum of violence.)
1-6. Most operations occur on the lower end of the spectrum of violence, and their objectives do not reach the level of vital national interests or national survival. These operations typically shape operational environments in ways that stabilize global security and facilitate conditions that are generally favorable to the United States. They provide valuable options to JFCs because they achieve objectives best supported by persistent presence, often at relatively low cost.
1-7. While the overwhelming majority of operations conducted by Army forces occur either below the threshold of armed conflict or during limited contingencies, the focus of Army readiness is on large-scale combat operations. The United States always retains the option to employ greater levels of force when less coercive methods are ineffective, and when a vital interest or national survival is at stake. This requires Army forces to be prepared for the most demanding and dangerous types of operations. Army forces contribute to conventional deterrence through their demonstrated capability, capacity, and will to wage war on land in any environment against any opponent. Credible combat forces make the other instruments of national power more potent, and they help deter the enemy’s escalation of violence during other types of operations.
1-8. Credible combat forces are those able to overcome the advantages peer threats generate within a specific regional context. Enemies typically initiate their aggression under conditions optimal for their success, requiring U.S. forces to respond at a disadvantage. U.S. combat operations typically involve force projection over long distances, providing advantages for enemy forces operating closer to their bases of support. Enemies typically have a degree of popular support cultivated through decades of propaganda and isolation from the free flow of information. This increases the enemy’s will to fight and can make local populations hostile to U.S. forces and objectives. Although a combatant command and theater army may accrue a variety of advantages as they set the theater and prepare for armed conflict during periods of competition, Army forces are typically faced with challenges they have to overcome at the onset of hostilities and throughout the conduct or armed conflict.
MULTIDOMAIN OPERATIONS
1-9. Multidomain operations are the combined arms employment of joint and Army capabilities to create and exploit relative advantages that achieve objectives, defeat enemy forces, and consolidate gains on behalf of joint force commanders. Employing Army and joint capabilities makes use of all available combat power from each domain to accomplish missions at least cost. Multidomain operations are the Army’s contribution to joint campaigns, spanning the competition continuum. Below the threshold of armed conflict, multidomain operations are how Army forces accrue advantages and demonstrate readiness for conflict, deterring adversaries while assuring allies and partners. During conflict, they are how Army forces close with and destroy the enemy, defeat enemy formations, seize critical terrain, and control populations and resources to deliver sustainable political outcomes.
1-10. Army forces conduct operations in support of joint campaigns which for the most part occur as part of a larger coalition operation. Leaders must understand the interdependencies between their own assigned forces and the forces or capabilities provided by others to generate the complementary and reinforcing effects of combined arms approaches. Army forces employ joint and other unified action partner capabilities to the degree they are available. However, because peer threats can contest the force in all domains, Army forces must be prepared to conduct operations when some or all joint capabilities are unavailable to support mission accomplishment.
1-11. All operations are multidomain operations. Army forces employ organic capabilities in multiple domains, and they continuously benefit from air and maritime strategic transportation and space and cyberspace capabilities that they do not control, including global positioning, satellite communications, and intelligence, surveillance, and reconnaissance (ISR). Lower echelons may not always notice the opportunities created by higher echelons or other forces that operate primarily in other domains; however, leaders must understand how the absence of those opportunities affects their concepts of operations, decision making, and risk assessment.
1-12. During operations, small advantages can have significant impacts on the outcome of the mission, particularly when they accrue over time. Creating and exploiting relative advantages are therefore necessary for all operations, and they become even more critical when opposing sides are evenly matched. A relative advantage is a location or condition, in any domain, relative to an adversary or enemy that provides an opportunity to progress towards or achieve an objective. Commanders seek and create relative advantages to exploit through action, and they continually assess the situation to identify ways to expand opportunities. (See paragraphs 1-106 through 1-117 for more information on physical, information, and human advantages.)
1-13. Army leaders are accustomed to creating and exploiting relative advantages through the combined-arms approach that traditionally focuses on capabilities from the land, air, and maritime domains. The proliferation of space and cyberspace capabilities further requires leaders who understand the advantages those capabilities create in their operational environment. The ability to integrate and synchronize space and cyberspace capabilities at the most effective tactical echelon expands options for creating advantages to exploit.
1-14. Multidomain operations fracture the coherence of threat operational approaches by destroying, dislocating, isolating, and disintegrating their interdependent systems and formations, and exploiting the opportunities these disruptions provide to defeat enemy forces in detail. Army forces therefore require timely, accurate, relevant, and predictive intelligence to understand threat characteristics, capabilities, objectives, and courses of action. Intelligence initially drives what combinations of defeat mechanisms commanders pursue as they employ the capabilities of their forces in space and time against enemy forces. Army forces combine maneuver and targeting methods to defeat enemy formations and systems. Army forces employ maneuver to close with and destroy enemy formations in close operations. Targeting generally sets priorities for information collection, fires, and other key capabilities to disintegrate enemy networks and systems. Leaders execute the targeting process to create advantages that enable freedom of maneuver and exploit the positional advantages created by maneuver. Targeting is a key way for leaders to integrate the joint capabilities required to create depth in the battlefield and protect friendly formations.
CHALLENGES FOR ARMY FORCES
1-15. The joint force deters most adversaries from seeking to achieve strategic objectives through direct military confrontation with the United States. As a result, adversaries pursue their objectives indirectly through malign activities and armed conflict targeting others in ways calculated to avoid war with the United States. These activities include subversive political and legal strategies, establishing physical presence on the ground to buttress resource claims, coercive economic practices, supporting proxy forces, and spreading disinformation. However, several adversaries have both the ability and the will to conduct armed conflict with the United States under certain conditions, which requires Army forces to be prepared at all times for limited contingencies and large-scale combat operations.
1-16. Global and regional adversaries apply all instruments of national power to challenge U.S. interests and the joint force. Militarily, they have extended the battlefield by employing network-enabled sensors and long-range fires to deny access during conflict and challenge friendly forces’ freedom of action during competition. These standoff approaches seek to—
Counter U.S. space, air, and naval advantages to make the introduction of land forces difficult and exploit the overall joint force’s mutual dependencies.
Increase the cost to the joint force and its partners in the event of armed conflict.
Hold the joint force at risk both in the U.S. and at its overseas bases and contest Army forces’ deployment from home station to forward tactical assembly areas overseas.
1-17. Adversaries increase risk to the U.S. joint force in order to raise the threshold at which the United States might respond to a provocation with military force. By diluting the joint force’s conventional deterrence, adversaries believe they have greater freedom of action to conduct malign activities both within and outside the U.S. homeland. Adversaries exploit this freedom of action through offensive cyberspace operations, disinformation, influence operations, and the aggressive positioning of ground, air, and naval forces to support territorial claims. Adversaries employ different types of forces and capabilities to attack private and government organizations, threaten critical economic infrastructure, and disrupt political processes, often with a degree of plausible deniability that reduces the likelihood of a friendly military response. Conducting these activities in support of policy goals threatens allied cohesion, weakens responses, and creates additional opportunities. (See paragraphs 2-40 through 2-44 for description of enemy information warfare.)
1-18. Threat standoff approaches intensify other friendly challenges. These challenges include—
Gaining and maintaining support of allies and partners.
Maintaining the continuous information collection needed to determine composition, disposition, strength, and activities of enemy forces.
Integrating and synchronizing intelligence at all echelons, distributed across large operational areas with diverse requirements.
Preparing forward-stationed forces to fight and win while outnumbered and isolated.
Protecting forward-positioned forces and those moving into a theater.
Minimizing vulnerability to weapons of mass destruction.
Maintain C2 and sustainment of units distributed across vast distances in noncontiguous areas and outside supporting ranges and distances.
Maintaining a desirable tempo while defeating fixed and bypassed enemy forces.
Defeating threat information and irregular warfare attacks against the United States and strategic lines of communications.
1-19. Army forces prepare to conduct operations in contested theaters prior to and during armed conflict, including in the United States. Army forces must account for being under constant observation and the threat’s ability to gain and maintain contact in all domains, wherever they are located. Army forces must be ready to deploy on short notice to austere locations and be capable of immediately conducting combat operations. During the initial phases of an operation, Army units may find themselves facing superior threats in terms of both numbers and capabilities. The first deploying units require the capability to defend themselves and continuously collect information on threat activities, as they provide reaction time and freedom of maneuver for follow-on forces. Army units with limited joint support may have to defend while at risk from enemy long-range fires. Forward-stationed forces may defend critical terrain with other coalition forces to delay enemy offensive operations. Some forward-stationed forces may defend joint bases to mitigate the impact of enemy attacks against strategic and operational lines of communications. In both cases, forward-stationed Army forces must be prepared to fight while relatively isolated in the early stages of an enemy attack.
1-20. The likelihood of the enemy force’s use of massed long-range fires and weapons of mass destruction increases during large-scale combat operations—particularly against command and control (C2) and sustainment nodes, assembly areas, and critical infrastructure. To survive and operate against massed longrange fires and in contaminated environments, commanders ensure as much dispersion as tactically prudent. Army forces seek every possible advantage using dispersion, deception, counterreconnaissance, terrain, cover, concealment, masking, and other procedures to avoid detection and mitigate the impact of enemy fires. In the offense, Army forces maneuver quickly along multiple axes, concentrating only to the degree required to mass effects, and then dispersing to avoid becoming lucrative targets for weapons of mass destruction and enemy conventional fires. Although dispersion disrupts enemy targeting efforts, it increases the difficulty of both C2 and sustainment for friendly forces. Success demands agile units that are able to adjust dispositions rapidly, assume risk, and exploit opportunities when they are available.
1-21. The high tempo of large-scale combat operations creates gaps and seams, generating both opportunities and risks as enemy formations disintegrate, disperse, or displace. After generating sufficient combat power for offensive operations, friendly forces may intermingle with or fix and bypass enemy formations. This requires follow-on and supporting units to protect themselves and to defeat enemy remnants in detail within the rear area as part of consolidating gains.
1-22. Army forces deploying from the United States and elsewhere face a wide range of threats that are difficult to counter without joint support. The disruptive effects of enemy action may occur at unit home stations, ports of embarkation, while in transit to the theater, and upon arrival at ports of debarkation. Army forces may not have the capability, or the authority, to preempt these attacks, although counterintelligence may aid in early identification of threats. The threat’s ability to contest the deployment of forces may degrade combat power available to forward forces and cause unit personnel and equipment to arrive in piecemeal fashion at ports of debarkation. (See Appendix C for more information on deployments contested by threat forces.)
LETHALITY: OVERCOMING CHALLENGES
1-23. Army forces overcome challenges posed by threats and the environment with credible formations able to employ lethal capabilities. Lethality is the capability and capacity to destroy. Employing and threatening the employment of lethal force lies at the core of how Army forces achieve objectives and enable the rest of the instruments of national power to achieve objectives.
1-24. Lethality is enabled by formations maneuvering into positions of relative advantage where they can employ weapon systems and mass effects to destroy enemy forces or place them at risk of destruction. The speed, range, and accuracy of weapon systems employed by a formation enhance its lethality. The demands of large-scale combat rapidly deplete available stockpiles and require forces to retain large reserves of ammunition, weapons, and other warfighting capabilities. Leaders multiply the effects of lethal force by employing combinations of capabilities through multiple domains to create, accrue, and exploit relative advantages—imposing multiple dilemmas on enemy forces and overwhelming their ability to respond effectively. Overcoming challenges in the operational environment further requires lethal Army forces that employ all available capabilities to—
Continuously cultivate landpower networks with allies and partners to facilitate interoperability.
Be demonstrably prepared for large-scale combat operations to deter conflict on land.
Employ capabilities in a combined arms manner to create exploitable opportunities.
Maneuver, mass effects, and preserve combat power to defeat threats to other Service components of the joint force.
Defend forward-positioned critical joint infrastructure and key terrain.
Conduct offensive operations to create and exploit opportunities and achieve objectives.
Consolidate gains during competition, crisis, and armed conflict to enable sustainable political outcomes.
1-25. The effective employment of Army forces depends on leaders who understand war, warfare, and the environment within which military forces fight. Gaps in understanding are often causes of failures to achieve sustainable political outcomes with military means.
WAR AND WARFARE
1-26. War is a state of armed conflict between different nations, state-like entities, or armed groups to achieve policy objectives. Wars are fought between nations locally, regionally, or on a global scale. Wars are fought within a nation by a central government against insurgent, separatist, or resistance groups. Armed groups in semiautonomous regions also fight wars to achieve their objectives. Wars range from intense clashes between large military forces—sometimes backed by an official declaration of war—to more subtle hostilities that intermittingly breach the threshold of violence.
1-27. The object of war is to impose a nation’s or group’s will on its enemy in pursuit of policy objectives. Regardless of the specific objectives, the decision to wage war represents a major policy decision and changes how Army forces use military capabilities. The nature of war, its principles, and its elements remain consistent over time. However, warfare, the conduct and characteristics of war, reflects changing means and contexts.
1-28. The Army’s multidomain operations concept accounts for the constant nature of war and the changing character of warfare. Its balanced approach guides how Army forces operate across the competition continuum given the prevailing characteristics of anticipated operational environments now and in the near future. Doctrine for the conduct of operations begins with a view of war and warfare that includes the—
Nature of war.
Principles of war.
Characteristics of warfare.
Methods of warfare.
Offense, defense, and stability.
Large-scale combat operations.
Combined arms.
Levels of warfare.
Army strategic contexts.
Consolidating gains.
(See Chapter 3 for more information on the multidomain operations concept.)
THE NATURE OF WAR
1-29. While the term war has multiple uses depending on the context (for example, the war on drugs or the war on poverty), it is the threat or use of violence to achieve political purposes that distinguishes war in the military context from other human activities. This distinction accounts for three elements of the Army’s view of war. War is—
Fought to achieve a political purpose.
A human endeavor.
Inherently chaotic and uncertain.
Note. War, by definition, includes at least two opposing sides. However, not all violence for political gain causes a war. For example, in the current security environment China imposes low levels of violence and new types of violence (including space and cyberspace attacks against government, economic institutions, private industry, and infrastructure) that do not trigger significant military responses. In these cases, China sees itself in a state of war with its adversaries, but its adversaries do not. Such a disparity in perspective is dangerous for those nations opposing China that may endure low levels of violence for long periods, while slowly ceding interests until it is too late to respond effectively. Responding to such situations requires a comprehensive government approach supported by joint and Army forces.
1-30. All U.S. military operations share a common purpose—to achieve or contribute to national policy objectives. As a principle of war, objective reinforces the proper relationship between military operations and policy. War must always be subordinate to policy and serve a political end. In conjunction with political leaders, military leaders develop strategies to achieve the desired policy outcomes. Policy outcomes often relate to the nation’s ability to influence, control, or secure populations, civil infrastructure, natural resources, and access to global commons in all domains. (See Appendix A for a discussion of the principles of war.)
1-31. War is shaped by human nature and the complex interrelationships of cognition, emotion, and uncertainty. National sentiments are often targets to be affected or manipulated by one or both sides. Values and ethics are some of the cognitive factors that motivate both the cause for going to war and restrictions in the conduct of war. Fear, passion, camaraderie, grief, and many more emotions affect the resolve of a war’s participants. They affect the behavior of combatants, including how and when leaders decide to persevere and when to give up. Individuals react differently to the stress of war; an act that may break the will of one enemy may only serve to stiffen the resolve of another. Human will, instilled through commitment to a cause and leadership, is the driving force of all action in war. The human dimension infuses war with its intangible moral factors. (See paragraphs 1-115 through 1-117 for more information on the human dimension.)
1-32. War is inherently chaotic and uncertain due to the clash of wills and intense interaction of innumerable factors. Orders are misunderstood, enemy forces do the unexpected, units make wrong turns, unforeseen obstacles appear, the weather changes, and units consume supplies at unexpected rates. This friction affects all military operations, and it must be anticipated by leaders. The chaotic nature of war makes discerning the precise cause and effect of actions difficult, impossible, or delayed. The unintended effects of operations are difficult to anticipate and identify. Such chaos imposes a great deal of uncertainty on all operations and drives the importance of leaders who are skilled at assuming risk.
PRINCIPLES OF WAR
1-33. From a U.S. military perspective, war involves nine principles, collectively and classically known as the principles of war. The nine principles of war represent the most important factors that affect the conduct of operations, and they are derived from the study of history and experience in battle. (See table 1-1 on page 1-8 for a concise listing of the principles of war.)
1-34. The principles of war capture broad and enduring fundamentals for the employment of forces in combat. They are not a checklist that guarantees success. Rather, they summarize considerations commanders and their staffs account for during successful operations, applied with judgment in specific contexts. While applicable to all operations, they do not apply equally or in the same way to every situation. (For more information on the principles of war, see Appendix A.)
Maneuver: Place the enemy in a position of disadvantage through the flexible application of combat power.
Objective: Direct every military operation toward a clearly defined, decisive, and attainable goal.
Offensive: Seize, retain, and exploit the initiative.
Surprise: Strike at a time and place or in a manner for which the enemy is unprepared.
Economy of force: Expend minimum-essential combat power on secondary efforts to allocate the maximum possible combat power on the main effort.
Mass: Concentrate the effects of combat power at the most advantageous place and time to produce decisive results.
Unity of command: Ensure unity of effort under one responsible commander for every objective.
Security: Prevent the enemy from achieving surprise or acquiring unexpected advantage.
Simplicity: Increase the probability that plans can be executed as intended by preparing clear, uncomplicated plans and orders.
CHARACTERISTICS OF WARFARE
1-35. Warfare, the conduct and characteristics of war, is affected by changes in technology, national policy, operational concepts, public opinion, and many other factors. Warfare may retain similarities over time, but it inevitably also has great variations. Rapid advances in, and the proliferation of, air, space, and cyberspace capabilities with military applications are changing warfare. Space technology enables persistent overhead surveillance and global communications, navigation, timing, missile warning, and environmental monitoring. Cyberspace technology is integrated into most military capabilities, and it enables near-instantaneous communications and information sharing, creating both opportunities and vulnerabilities that can be exploited by both sides during competition, crisis, and conflict.
METHODS OF WARFARE
1-36. Although the nature and principles of war reflect the continuity of war, the conduct of warfare, like dynamic operational environments, reflects wide variation. Therefore, depending on the situation, strategic actors pursue their objectives in war through different methods of warfare. There are many different methods, but they generally fall into two broad categories: conventional and irregular. Each method of warfare serves the same strategic purpose—to defeat an enemy—but they take fundamentally different approaches to achieving their purpose. Both methods share one characteristic, which is that they involve the use of lethal force to achieve a political end. Warfare rarely fits neatly into any of these subjective categories, and it almost always entails a blend of both methods over the course of a conflict.
Note. These broad categories describe the overall approaches to warfare. Other categories attempt to describe the dominant means used in a particular application, for example “information warfare,” “cyber warfare,” or “anti-submarine warfare,” In these cases, the terms “warfare,” “operations,” and “activities” are often used interchangeably.
1-37. Conventional warfare is a violent struggle for domination between nation-states or coalitions of nation-states. Conventional warfare is generally carried out by two or more military forces through armed conflict. It is commonly known as conventional warfare because it means to fight enemy forces directly, with comparable military systems and organizations. A nation-state’s strategic purpose for conducting conventional warfare is to impose its will on an enemy government and avoid imposition of the enemy government’s will on it and its citizens. Joint doctrine refers to conventional warfare as “traditional” because it has been understood that way in the West since the Peace of Westphalia (1648), which reserved, for the nation-state alone, a monopoly on the legitimate use of force. However, irregular warfare has a longer history, and it has been just as common as the “traditional” method of warfare in some societies.
1-38. Conventional warfare normally focuses on defeating enemy armed forces, enemy warfighting capabilities, and controlling key terrain and populations to decisively influence an enemy government’s behavior in favorable ways. During conventional warfare, enemies engage in combat openly against each other and generally employ similar capabilities. Conventional war may escalate to include nation-state use of weapons of mass destruction. Like the other branches of the armed forces, the Army is organized, trained, and equipped primarily to conduct or deter conventional warfare, especially its most lethal manifestation— large-scale combat operations.
1-39. Conventional deterrence creates the paradox that although combat-ready forces reduce the probability of large-scale combat, they increase the frequency of adversaries pursuing irregular warfare and malign activity short of armed conflict to achieve objectives. The tradeoff is acceptable because conducting irregular warfare with forces prepared for large-scale ground combat incurs less risk than conducting large-scale ground combat with forces unprepared to do so.
1-40. Irregular warfare is the overt, clandestine, and covert employment of military and non-military capabilities across multiple domains by state and non-state actors through methods other than military domination of an adversary, either as the primary approach or in concert with conventional warfare. Irregular warfare may include the use of indirect military activities to enable partners, proxies, or surrogates to achieve shared or complementary objectives. The main objective of irregular warfare varies with the political context, and it can be successful without being combined with conventional warfare (for example, the Cuban Revolution). While it often focuses on establishing influence over a population, irregular warfare has also historically been an economy of force effort to fix enemy forces in secondary theaters of conflict or to cause enemy leaders to commit significant forces to less critical lines of effort. Two characteristics distinguish irregular warfare from conventional warfare:
The intent is to erode a political authority’s legitimacy and influence or to exhaust its resources and will—not to defeat its armed forces—while supporting the legitimacy, influence, and will of friendly entities engaged in the struggle.
The nonmilitary instruments of power are more prominent because the military instrument of power alone is insufficient to achieve desired objectives.
1-41. JFCs can employ most Army forces and capabilities during irregular warfare. Certain forces and capabilities are irregular warfare focused (for example Army special operations forces), in that they are specifically designed and organized for irregular warfare, but they can also be employed effectively in conventional warfare (for example as combat advisors to host-nation forces). Other forces are irregular warfare capable, in that they are primarily designed and organized for conventional warfare, but they can also be employed effectively in irregular warfare. Historically, the overwhelming majority of Army forces employed to conduct irregular warfare have been conventional forces.
OFFENSE, DEFENSE, AND STABILITY
1-42. Offense, defense, and stability are inherent elements of conventional and irregular warfare. Divisions and higher echelons typically perform some combination of all three elements in their operations simultaneously. However, the lower the echelon, the more likely it is for that formation to be focused on one element at a time.
1-43. An offensive operation is an operation to defeat or destroy enemy forces and gain control of terrain, resources, and population centers (ADP 3-0). Offensive operations are how commanders impose their will on an enemy. The offense is the most direct means of seizing, retaining, and exploiting the initiative to gain a physical and psychological advantage. Offensive operations typically include a sudden action directed toward enemy weaknesses, capitalizing on speed, surprise, and shock. The offense compels an enemy force to react, creating new or larger weaknesses the attacking force can exploit. (See ADP 3-90 for a detailed discussion of the offense.)
1-44. A defensive operation is an operation to defeat an enemy attack, retain key terrain, gain time, and develop conditions favorable for offensive or stability operations (ADP 3-0). Normally the defense cannot achieve a decisive victory. However, it sets conditions for a counteroffensive or a counterattack that enables forces to regain the initiative. Defensive operations are a counter to an enemy offensive action, and they seek to destroy as many of the enemy forces as possible. Defensive operations preserve control over land, resources, and populations, and they protect lines of communications and critical capabilities against attack. Commanders can conduct defensive operations in one area to free forces for offensive operations elsewhere. (See ADP 3-90 for a detailed discussion of the defense.)
1-45. A stability operation is an operation conducted outside the United States in coordination with other instruments of national power to establish or maintain a secure environment and provide essential governmental services, emergency infrastructure reconstruction, and humanitarian relief (ADP 3-0). These operations support governance by a host nation, an interim government, or a military government. Stability involves coercive and constructive action. (See ADP 3-07 for more information on stability operations.)
LARGE-SCALE COMBAT OPERATIONS
1-46. The focus of Army readiness is on large-scale combat operations. Large-scale combat operations are extensive joint combat operations in terms of scope and size of forces committed, conducted as a campaign aimed at achieving operational and strategic objectives (ADP 3-0). During ground combat, they typically involve operations by multiple corps and divisions, and they typically include substantial forces from the joint and multinational team. Large-scale combat operations often include both conventional and irregular forces on both sides.
1-47. Conflicts encompassing large-scale combat operations are more intense and destructive than limited contingencies, often rapidly amassing heavy casualties. Peer threats employ networks of sensors and longrange massed fires that exploit electromagnetic signatures and other detection methods to create high risk for ground forces, particularly when they are static. Army forces must account for constant enemy observation, including the threat from unmanned systems that saturate the operational environment. Army forces take measures to defeat the enemy’s ability to effectively mass effects while creating exploitable advantages to mass effects against enemy capabilities and formations.
1-48. Urban areas are high risk areas that are a factor in many operational environments. Avoiding urban areas during large-scale combat through deception or other means is ideal, but generally not possible. Commanders may conduct urban operations because they provide a tactical, political, or economic advantage, or when not doing so threatens the joint campaign. Army forces conduct large-scale combat operations in urban areas either as specific, unique operations, or more typically, as one of a larger series of operations in a joint campaign. Urban operations focus on the threat to or within the urban area and allow other forces to conduct operations elsewhere. Conducting operations in dense urban terrain is complex and resource intensive. Combined arms operations that integrate joint capabilities, allies and partners, and conventional and irregular forces are essential to success. Commanders voice concern to higher headquarters when they do not have sufficient forces for the task issued, and they must arrange their forces and operations according to purpose, time, and space to accomplish the mission. Success in defeating enemy forces in large urban areas typically requires the ability to isolate them from physical, information, and human support. (See ATP 3-06 for more information on urban operations.) During large-scale combat operations, Army forces focus on the defeat and destruction of enemy ground forces as part of the joint team, and they contribute to the defeat of forces in other domains. Army forces close with and destroy enemy forces in all types of terrain, exploit success, and break the enemy’s will to resist. Army forces attack, defend, perform stability tasks, and continuously consolidate gains to accomplish objectives that support a desirable political outcome. Corps and divisions are the formations central to the conduct of large-scale combat. The ability to prevail in ground combat is a decisive factor in breaking an enemy’s capability and will to continue a conventional conflict. Conflict resolution requires Army forces to consolidate gains with unified action partners as long as necessary to accomplish national objectives.
1-49. Planning for large-scale combat operations must account for possible enemy use of chemical, biological, radiological, and nuclear (CBRN) weapons and allied retaliatory response options. Planning must also account for toxic industrial hazards caused by combat operations. Enemy employment of CBRN weapons and the allied response would affect all domains, but they present disproportionate effects in the land domain. Some adversaries plan for the employment of nuclear and chemical weapons by incorporating them into their doctrine and training, and they maintain delivery systems for their employment on the battlefield. Furthermore, the use of these weapons does not terminate a conflict and may cause it to escalate. Units must be prepared to operate in, around, and through contaminated environments. This is fundamental to deterring adversaries from employing weapons of mass destruction. CBRN considerations should inform both operational planning and force readiness. (See FM 3-11 for doctrine on operating in a CBRN environment, and see ATP 3-72 for more information operations in a nuclear environment.)
COMBINED ARMS
1-50. Combined arms is the synchronized and simultaneous application of arms to achieve an effect greater than if each element was used separately or sequentially (ADP 3-0). Leaders combine arms in complementary and reinforcing ways to protect capabilities and amplify their effects. Confronted with a constantly changing situation, leaders create new combinations of capabilities, methods, and effects to pose new dilemmas for adversaries. The combined arms approach to operations during competition, crisis, and armed conflict is foundational to exploiting capabilities from all domains and their dimensions.
1-51. Complementary capabilities compensate for the vulnerabilities of one system or organization with the capabilities of a different one. Infantry protects tanks from enemy infantry and antitank systems, while tanks provide mobile protected firepower for the infantry. Ground maneuver can make enemy forces displace and become vulnerable to joint fires, while joint fires can disrupt enemy reserves and C2 to enable operations on the ground. Cyberspace and space capabilities and electromagnetic warfare can prevent enemy forces from detecting and communicating the location of friendly land-based fires capabilities, and Army fires capabilities can destroy enemy ground-based cyberspace nodes and electromagnetic warfare platforms to protect friendly communications.
1-52. Reinforcing capabilities combine similar systems or capabilities to amplify the overall effects a formation brings to bear in a particular context. During urban operations, for example, infantry, aviation, and armor units working in close coordination reinforce the protection, maneuver, and direct fire capabilities of each unit type while creating cascading dilemmas for enemy forces. Army artillery can be reinforced by close air support, air interdiction, and naval surface fire support, greatly increasing both the mass and range of fires available to a commander. Space and cyberspace capabilities used to disrupt enemy communications can reinforce a brigade combat team’s (BCT’s) ground-based jamming effort to increase the disruption to enemy C2. Military information support operations can amplify the effects of physical isolation on an enemy echelon, making it more vulnerable to friendly force exploitation.
1-53. The organic composition, training, and task organization of Army units set conditions for effective combined arms. Throughout operations, commanders assess the operational environment and adjust priorities, change task organization, and request capabilities to create exploitable advantages, extend operational reach, preserve combat power, and accomplish missions.
LEVELS OF WARFARE
1-54. The levels of warfare are a framework for defining and clarifying the relationship among national objectives, the operational approach, and tactical tasks (ADP 1-01). While the various methods of warfare are ultimately expressed in concrete military action, the four levels of warfare—national strategic, theater strategic, operational, and tactical—link tactical actions to achievement of national objectives as shown in figure 1-2.
1-55. The levels of warfare distinguish four broad overlapping activities—providing national direction and creating national strategy (national strategic), conducting continuous theater campaigning (theater strategic); planning and conducting campaigns and major operations (operational); or planning and executing operations, battles, engagements, and actions (tactical). Some commanders act at more than one level of war. For example, a combatant commander (CCDR) formulates theater strategy and designs the campaign plan. A land component commander assists a CCDR in campaign design and may lead a field army during major operations. The levels of warfare are conceptual, without finite limits or boundaries. They do, however, correlate to specific activities and responsibilities. They help commanders visualize the relationships and actions required to link strategic objectives, military operations at various echelons, and tactical actions. Among the levels of warfare, planning horizons, methods, and products differ greatly. Without this context, tactical operations become disconnected from operational end states and strategic objectives. There are skills and practices related to strategic, theater strategic, operational, and tactical level that differ from each other and are enhanced by specific training and education.
1-56. The national strategic level of warfare is the level of warfare at which the U.S. government formulates policy goals and ways to achieve them by synchronizing action across government and unified action partners and employing the instruments of national power. The instruments of national power are all of the means available to the government in its pursuit of national objectives, expressed as diplomatic, economic, informational, and military. The national strategic level of warfare focuses on developing global strategy and providing global strategic direction. Strategic direction provides context, tasks, and purpose for the employment of the instruments of national power. The specifics of strategic direction address long-term, emerging, and anticipatory issues or concerns that may quickly evolve due to rapidly changing circumstances. Strategic direction is always evolving and adapting.
1-57. The theater strategic level of warfare is the level of warfare at which combatant commanders synchronize with unified action partners and employ all elements of national power to fulfill policy aims within the assigned theater in support of the national strategy. Based on strategic guidance, CCDRs with assigned areas of responsibility and staffs—with input from subordinate commands, including theater armies and supporting commands and agencies—update their strategic estimates and develop theater strategies. A theater strategy is an overarching construct outlining a combatant commander’s vision for integrating and synchronizing military activities and operations with the other instruments of national power to achieve national strategic objectives. The theater strategy prioritizes the ends, ways, and means within the limitations established by the budget, global force management processes, and strategic guidance. The theater strategy serves as the basis for development of the combatant command campaign plan (CCP).
1-58. The operational level of warfare is the level of warfare in which campaigns and operations are planned, conducted, and sustained to achieve operational objectives to support achievement of strategic objectives (JP 3-0). The operational level links the employment of tactical forces to the achievement of strategic objectives.
1-59. The operational level of warfare generally is the realm of combatant commands and their Service or functional components and subordinate joint task force (JTF) headquarters and their Service or functional components. This includes the theater army headquarters as the Army Service component to a combatant command and any other echelon operating as an ARFOR, JTF headquarters, or land component command. The focus at this level is on operational art—the design of campaigns and operations by integrating ends, ways, and means, while accounting for risk. (See ADP 3-0 for more information on operational art.)
1-60. Actions at the operational level of warfare usually involve broader aspects of time and space than tactical actions. The theater army’s activities continuously support the CCDR in shaping the operational and strategic situation. Operational-level commanders need to understand the complexities of the operational environment and look beyond the immediate situation. Operational-level commanders seek to create the most favorable conditions possible for subordinate commanders by preparing for future events.
1-61. The operational level of warfare demands leaders with a unique set of skills. Because the operational level is fundamentally about linking tactical action to strategic objectives, leaders must understand both strategy and tactics. They must have some expertise in the capabilities and operations of all Services and components and those of allies and partners. Leaders at the operational level must be able to assess large, complex operational environments and be expert planners. They must understand the application of warfighting functions on a large scale and how this application differs from application at the tactical level. The elements of operational art help operational leaders understand, visualize, and describe their campaigns and major operations. (See ADP 3-0 for details on the elements of operational art.)
1-62. The tactical level of warfare is the level of warfare at which forces plan and execute battles and engagements to achieve military objectives (JP 3-0). Activities at this level focus on tactics—the employment, ordered arrangement, and directed actions of forces in relation to each other (ADP 3-90). Operational-level headquarters determine objectives and provide resources for tactical operations. Tactical-level commanders plan and execute operations to include battles, engagements, and small-unit actions.
1-63. Tactical-level combat operations rise to the level of battles or engagements. A battle is a set of related engagements that lasts longer and involves larger forces than an engagement (ADP 3-90). Battles can affect the course of a campaign or major operation, and they are typically conducted by corps and divisions over the course of days or months. An engagement is a tactical conflict, usually between opposing lower echelon maneuver forces (JP 3-0). Engagements are typically conducted at brigade echelons and below. They are usually short, executed in minutes or hours.
1-64. The strategic and operational levels of warfare provide the context for tactical operations. Without this context, tactical operations devolve into a series of disconnected and unfocused actions. Likewise, tactical operations inform strategic and operational objectives, ensuring that those objectives remain tethered to reality and adjust, when necessary, according to the situation. Strategic and operational success is a measure of how the achievement of objectives in one or more battles contributes to winning a major operation or campaign. (See ADP 3-90 for more information on tactics.)
ARMY STRATEGIC CONTEXTS
1-65. Joint doctrine describes the strategic environment in terms of a competition continuum. Rather than a world either at peace or at war, the competition continuum describes three broad categories of strategic relationships—cooperation, competition below armed conflict, and armed conflict. Each relationship is defined as between the United States and another strategic actor relative to a specific set of policy aims. Cooperation, competition, and even armed conflict commonly go on simultaneously in different parts of the world. Because of this, the needs of CCDRs and Army component commanders in one area are affected by the strategic needs of others. (See JP 3-0 for more information about the joint competition continuum.)
Note. This manual uses “competition” to mean “competition below armed conflict.”
1-66. Although combatant commands and theater armies campaign across the competition continuum, Army tactical formations typically conduct operations within a context dominated by one strategic relationship at a time. Therefore, Army doctrine describes the strategic situation through three contexts in which Army forces conduct operations:
Competition below armed conflict.
Crisis.
Armed conflict.
1-67. The Army strategic contexts generally correspond to the joint competition continuum and the requirements of joint campaigns. Because cooperation is generally conducted with an ally or partner to counter an adversary or enemy, Army doctrine considers it part of competition. Army doctrine adds crisis to account for the unique challenges facing ground forces that often characterize transition between competition and armed conflict. (See figure 1-3 for an illustration of Army strategic contexts.)
1-68. Competition below armed conflict exists when two or more state or non-state adversaries have incompatible interests, but neither seeks armed conflict. Nation-states compete with each other using all instruments of national power to gain and maintain advantages that help them achieve their goals. Low levels of lethal force can be a part of competition below armed conflict. Adversaries often employ cyberspace capabilities and information warfare to destroy or disrupt infrastructure, interfere with government processes, and conduct activities in a way that does not cause the United States and its allies to respond with force. Competition provides military forces time to prepare for armed conflict, opportunities to assure allies and partners of resolve and commitment, and time and space to set the necessary conditions to prevent crisis or conflict. Examples of competition include return of forces to Europe (known as REFORGER) exercises conducted during the Cold War, security assistance provided to Ukraine since 2014, and Pacific Pathways activities to improve readiness in the Indo-pacific region. (See Chapter 4 for a detailed discussion of Army forces during competition.)
1-69. A crisis is an emerging incident or situation involving a possible threat to the United States, its citizens, military forces, or vital interests that develops rapidly and creates a condition of such diplomatic, economic, or military importance that commitment of military forces and resources is contemplated to achieve national and/or strategic objectives (JP 3-0). Commanders have to consider the possibility that overt military action may escalate a crisis towards armed conflict. The use of space and cyberspace capabilities provides other options that are less likely to cause escalation. The context of crisis is relative to an adversary, which is different from crisis response, which can result from a natural or human disaster. During crisis, armed conflict has not yet occurred, but it is either imminent or a distinct possibility that requires rapid response by forces prepared to fight if deterrence fails.
Note. A crisis can be long in duration, but it can also reflect a near-simultaneous transition to armed conflict. Leaders do not assume that a crisis provides additional time for a transition to armed conflict.
1-70. Army forces contribute to joint operations, seeking to deter further provocation and compel an adversary to de-escalate aggression and return to competition under conditions acceptable for the United States and its allies or partners. Through rapid movement and integration with the joint force, Army forces help signal the readiness and willingness to prevail in combat operations. When authorized, Army forces can inform or influence perceptions about an operation’s goals and progress to amplify effects on the ground during a crisis; however, commanders ensure their message aligns with reality and that their narratives are truthful and credible.
1-71. Army forces help the joint force maintain freedom of action and associated positions of relative advantage through the activities they conduct and their presence on the ground. They operate in a way that disrupts adversary risk calculations about the cost of acting contrary to U.S. national interests, compels deescalation, and fosters a return to competition conditions favorable to the United States. If deterrence fails to end a crisis, Army forces are better postured for operations during armed conflict. Examples of crisis include the Cuban missile crisis of 1962, Iraq’s invasion of Kuwait in 1990, North Korean missile and rocket provocations in 2017-2018, and the Russian attacks into Ukraine in 2014 and 2022. (See Chapter 5 for a detailed discussion of Army forces during crisis.)
1-72. Armed conflict occurs when a state or non-state actor uses lethal force as the primary means to satisfy its interests. Armed conflict can range from irregular warfare to conventional warfare and combinations of both. Entering into and terminating armed conflict is a political decision. Army forces may enter conflict with some advanced warning during a prolonged crisis or with little warning during competition. How well Army forces are prepared to enter into an armed conflict ultimately depends upon decisions and preparations made during competition and crisis.
1-73. At the onset of armed conflict, forward-positioned Army forces may defend key terrain or infrastructure while seeking opportunities to gain the initiative or reposition to more favorable locations with partner forces. Army forces help JFCs gain and maintain the initiative, defeat enemy forces on the ground, control territory and populations, and consolidate gains to establish conditions for a political settlement favorable to U.S. interests. Army forces provide landpower to the joint force and conduct limited contingency or large-scale combat operations to ensure enduring political outcomes favorable to U.S. interests. Examples of armed conflict include the Vietnam War, OPERATION DESERT STORM, and OPERATION INHERENT RESOLVE. (See Chapter 6 for a detailed discussion of Army forces conducting operations during armed conflict. See Chapter 7 for a discussion of Army forces in large-scale combat in maritime environments.)
CONSOLIDATING GAINS
1-74. Army commanders must exploit successful operations by continuously consolidating gains during competition, crisis, and armed conflict. Consolidate gains are activities to make enduring any initial operational success and to set the conditions for a sustainable security environment, allowing for a transition of control to other legitimate authorities (ADP 3-0). Consolidation of gains is an integral and continuous part of competition, and it is necessary for achieving success across the range of military operations. Successful consolidation of gains requires a realistic and pragmatic assessment of strategic conditions, ally and partner legitimacy, friendly and adversary relative advantages, and the viability of a sustainable political outcome. Operations to inform and influence foreign audiences also play a key role in achieving lasting outcomes.
1-75. During competition, Army forces may consolidate gains from previous conflicts for many years as JFCs seek to maintain relative advantages against a specific adversary and sustain enduring political outcomes. U.S. forces in Europe, Japan, the Republic of Korea, and the Middle East remained in place for decades to consolidate gains made in earlier conflicts. Army forces also consolidate gains by continuously developing multinational interoperability and readiness for large-scale combat operations.
1-76. During armed conflict, Army forces deliberately plan to consolidate gains throughout an operation as part of defeating the enemy in detail to accomplish overall policy and strategic objectives. Early and effective consolidation activities are a form of exploitation performed while other operations are ongoing, and they enable the achievement of lasting favorable outcomes in the shortest time span. Tactical units consolidating on an objective can be the first step in consolidating gains. In some instances, Army forces will be the lead for integrating forces and synchronizing activities to consolidate gains. In other situations, Army forces will be in support of allies and partners. Army forces may consolidate gains for a sustained period over large land areas. Military governments in occupied territories stabilize civilian populations. Military authorities may temporarily govern areas until populations are stable enough for transition to legitimate civilian authorities. This transition of control to civil authorities reduces demands on combat power.
1-77. While Army forces must continuously consolidate gains throughout an operation, consolidating gains becomes the overall focus of Army forces when large-scale combat operations have concluded. During competition, Army forces may consolidate gains from previous conflicts for many years as JFCs seek to maintain relative advantages against a specific adversary. During crisis, Army forces seek to consolidate whatever gains are made relative to a specific adversary so that the crisis does not occur again.
UNDERSTANDING AN OPERATIONAL ENVIRONMENT
1-78. An operational environment is the aggregate of the conditions, circumstances, and influences that affect the employment of capabilities and bear on the decisions of the commander (JP 3-0). For Army forces, an operational environment includes portions of the land, maritime, air, space, and cyberspace domains understood through three dimensions (human, physical, and information). The land, maritime, air, and space domains are defined by their physical characteristics. Cyberspace, a manmade network of networks, transits and connects the other domains as represented by the dots shown in figure 1-4.
Note. Joint doctrine describes the components of an operational environment as the physical areas of the land, maritime, air, and space domains; the information environment (which includes cyberspace); the electromagnetic spectrum; and other factors. (See JP 2-0 and JP 5-0 for more information on describing and analyzing an operational environment from a joint perspective.)
1-79. The operational environment model aids in accounting for the totality of factors, specific circumstances, and conditions that impact the conduct of operations. This understanding enables leaders to better identify problems; anticipate potential outcomes; and understand the results of various friendly, enemy, adversary, and neutral actions and the effects these actions have on achieving the military end state. A description of an operational environment includes all the factors that the commander and staff need to capture and understand to inform the conduct of operations.
1-80. Knowledge of the operational environment is the precursor to effective action. Obtaining knowledge about an operational environment requires aggressive and continuous intelligence, surveillance, reconnaissance, and security operations to acquire information. Information collected from multiple sources and analyzed becomes intelligence that answers commanders’ intelligence requirements. Using all available relevant information to determine how the operational environment affects operations is essential to understanding which courses of action are the most feasible, suitable, and acceptable. Throughout the course of operations, commanders and staffs rely on an integrated information collection effort to develop an accurate picture of their operational environment. Information collection is an activity that synchronizes and integrates the planning and employment of sensors and assets and as well as the processing, exploitation, and dissemination systems in direct support of current and future operations (FM 3-55).
1-81. An operational environment is the totality of factors that affect what occurs in an assigned area. These factors include actors, events, or actions that occur outside the assigned area. How the many entities behave and interact with each other is difficult to discern. No two operational environments are the same, and all of them continually change. Changes result, in part, from opposing forces and actors interacting, learning, and adapting. The complex and dynamic nature of an operational environment makes determining the relationship between cause and effect challenging, and it contributes to the uncertain nature of war and human competition. This requires that commanders, supported by their staffs, develop and maintain the best possible understanding of their operational environment. Several tools and processes assist commanders and staffs in understanding their operational environment. They include—
Domains.
Dimensions.
Operational and mission variables (detailed in FM 6-0).
Running estimates (described in ADP 5-0).
Army design methodology (described in ATP 5-0.1).
The military decision-making process (described in ADP 5-0).
Building intelligence knowledge (described in FM 2-0).
Intelligence preparation of the battlefield (described in ATP 2-01.3).
Sustainment preparation of the operational environment (described in FM 4-0).
DOMAINS
1-82. Within the context of an operational environment, a domain is a physically defined portion of an operational environment requiring a unique set of warfighting capabilities and skills. Each military Service and branch trains and educates its leaders to be experts about operations in a primary domain, although each Service has some capability in each of the domains, and each develops shared understanding of how to integrate capabilities from different domains. Land operations require mastery of terrain and ground maneuver. Cyberspace operations require mastery of digital information systems and computer code. Space, air, and maritime operations likewise require specific capabilities and skills, which manifest themselves in separate Services within the joint force. Although most domains align with the skills developed in a particular Service, no Service focuses entirely upon or exerts total control of that single domain during operations. Joint commanders assign responsibilities and task-organize based on mission requirements. However, the domains present very different conditions of warfare and require the specialized warfighting skills developed by the different Services and subcomponents within each of the Services. Army leaders do not need to understand all the technical components of what the joint force does in other domains, but they do need to understand the complementary and reinforcing ways in which they can request and employ those capabilities and methods in support of operations on land. (See Chapter 3 for a discussion of convergence.)
1-83. The land domain is the area of the Earth’s surface ending at the high water mark and overlapping with the maritime domain in the landward segment of the littorals (JP 3-31). Variations in climate, terrain, and the diversity of populations have a far greater impact on operations in the land domain than in any other domain. The most distinguishing characteristic of the land domain is the human dimension. Humans transit the maritime, air, and space domains, but they ultimately live, make political decisions, and seek conflict resolution on land.
1-84. The nature of combat on land is unique due to the impacts of terrain on all warfighting functions and the application of combat power. For example, terrain provides forces opportunities for evading detection and increasing survivability. It also provides enemy forces the same opportunities. Although technology increases the range of capabilities, complex terrain causes opposing forces to fight at close ranges. Land combatants routinely come face-to-face with one another in large numbers in a wide variety of operational environments containing all types of terrain and potentially nuclear, biological, and chemically degraded environments. When other means fail to drive enemy forces from their positions, Army forces close with and destroy or capture them through close combat. Close combat is warfare carried out on land in a direct-fire fight, supported by direct and indirect fires and other assets (ADP 3-0). The outcome of battles and engagements depends on the ability of Army forces to close with enemy forces and prevail in close combat.
1-85. Land-based domain capabilities are able to use or alter the terrain, operate in all forms of weather, and operate among populations. Land capabilities extend operational reach and provide options for enabling joint operations. Long-range artillery provides the joint force with a fires capability that is more survivable in some circumstances than air and maritime fires. Land-based electromagnetic capabilities are capable of jamming enemy communications and C2 systems. Land-based air and missile defense (AMD) capabilities, enabled by space and cyberspace capabilities, provide protection for Army and joint forces.
1-86. The other four domains depend, in some way, on land. Airfields, ports, servers, ground control stations and land-based radars support or enable operations in other domains. Most cyberspace capabilities and all the electricity that powers them depend on land-based networks. The energy that fuels air, space, and most maritime platforms comes from locations on land.
1-87. Operations on land depend on capabilities from other domains. Air lift, sea lift, cyberspace networks, and all non-land based examples of ISR and fires enable operations on land. (See JP 3-31 for information on joint land operations.)
1-88. The maritime domain is the oceans, seas, bays, estuaries, islands, coastal areas, and the airspace above these, including the littorals (JP 3-32). It overlaps with the land domain in the seaward segment of the littoral. Maritime capability may be viewed as global, regional, territorial, coastal, and self-defense forces. Only a few navies are capable of sustained employment far from their countries’ shores. However, whether or not their navies are capable of global power projection, most maritime nations also maintain air forces capable of conducting operations over the adjacent maritime domain. This air capability, combined with land-based long-range fires, greatly impacts operations in the maritime domain.
1-89. The Navy and its partners employ five functions in a combined arms approach to provide a unique relative advantage for the joint force. These functions are deterrence, operational access, sea control, power projection, and maritime security.
1-90. Maritime forces move strategic fires capabilities globally, conceal strategic capabilities below the surface of the ocean, transport personnel and equipment over vast distances, and sustain maritime operations for long periods. Maritime forces depend on or require support from the joint force to—
Protect maritime capabilities from enemy interdiction.
Protect ports.
Secure geographic choke points.
Influence populations.
Mitigate long timelines associated with maritime movement.
Compensate for the limited number of available maritime platforms.
Mitigate the inability to replace ships lost during a conflict.
1-91. Army forces rely on maritime capabilities for deployment and sustainment. Additionally, maritime fires and AMD complement and reinforce land-based systems. Army forces assist maritime forces with sea control, projecting power ashore to neutralize threats or control terrain in the landward portion of the littorals. Army long-range fires, attack aviation, AMD, and cyberspace capabilities contribute to local and regional maritime superiority.
1-92. For intratheater operations, Army watercraft provide a capability to move maneuver formations and sustain operations in a maritime environment. Army watercraft systems support joint and combined seabasing and joint logistics over-the-shore (JLOTS). In some circumstances, Army watercraft capabilities can mitigate enemy antiaccess (A2) or area denial (AD) approaches by providing access to shallow coastal waters, rivers, and narrow inland waterways where mature ports or road networks are unavailable. (See JP 3-32 for information on joint maritime operations.)
1-93. The air domain is the atmosphere, beginning at the Earth’s surface, extending to the altitude where its effects upon operations become negligible (JP 3-30). The speed, range, and payload of aircraft, rockets, missiles, and hypersonic glide vehicles operating in the air domain directly and significantly affect operations on land and sea. Likewise, advances in AMD, electromagnetic warfare, directed energy, and cyberspace capabilities increasingly contest freedom of maneuver in the air.
1-94. Control of the air and control of the land are often interdependent requirements for successful campaigns and operations. Control of the air provides a significant advantage when attacking strategically valuable targets at long ranges. However, control of the land is necessary for operating secure airfields and protecting other key terrain that enables air operations. The desired degree of control of the air may vary geographically and over time from no control, to parity, to local air superiority, to air supremacy, all depending upon the situation and the JFC’s approved concept of operations.
1-95. Army forces rely on the Air Force and other joint and multinational air capabilities for ISR, strategic attack, close air support, interdiction, personnel recovery, communications, sustainment, and mobility. Air platforms are unencumbered by terrain, but they are vulnerable to detection and interdiction. Effectiveness of air platforms can be contingent upon weather conditions. Aerial reconnaissance and surveillance cannot always detect enemy capabilities concealed by vegetation or terrain. The number of sorties air platforms can conduct depends on having control of airfields and their proximity to targets.
1-96. Army aviation provides ground commanders and the joint force with land-focused air capabilities. Joint force commanders and land component commanders establish control measures to enable Army forces to operate unimpeded in the air domain, coordinated when necessary with air capabilities from the other Services. Army aviation (including fixed-wing, rotary-wing, and unmanned aircraft) provides reconnaissance and surveillance, fires, intelligence, communications, and movement capabilities to Army, joint, and multinational forces. Army rotary-wing aviation uses terrain to protect it from enemy detection. Army forces also have aerial ISR capabilities that support security operations, targeting, delivering precision fires, and information collection. Army land-based AMD capabilities provide protection against enemy air and missile attack. (See JP 3 30 for more information on joint air operations.)
1-97. The space domain is the area above the altitude where atmospheric effects on airborne objects become negligible. Like the air, land, and maritime domains, space is a physical domain in which military, civil, and commercial activities are conducted. The U.S. Space Command (known as USSPACECOM) has an area of responsibility that surrounds the earth at altitudes equal to, or greater than, 100 kilometers (54 nautical miles) above mean sea level. It has responsibility for planning and execution of global space operations, activities, and missions.
1-98. Proliferation of advanced space technology provides access to space-enabled technologies to a global audience. Some adversaries have their own space capabilities, while commercially available systems allow almost universal access to some level of space-enabled capability with military applications.
1-99. Space capabilities provide information collection; early warning; target acquisition; electromagnetic warfare; environmental monitoring; satellite-based communications; and positioning, navigation, and timing information for ground forces. Activities in the space domain enable freedom of action for operations in all other domains, and operations in the other domains can create effects in and through the space domain.
1-100. Army forces rely on space-based capabilities to enable each warfighting function and effectively conduct operations. Commanders and staffs require an understanding of space capabilities and their effects and the ability to coordinate activities between involved agencies and organizations. Commanders cannot assume that U.S. forces will have unconstrained use of space-based capabilities, including data communications. Therefore, Army forces must be prepared to operate under the conditions of a denied, degraded, and disrupted space domain. (See FM 3-14 for doctrine on Army space operations.)
1-101. For Army forces, the cyberspace domain is the interdependent networks of information technology infrastructures and resident data, including the Internet, telecommunication networks, computer systems, embedded processors and controllers, and relevant portions of the electromagnetic spectrum. Cyberspace is an extensive and complex global network of wired and wireless links connecting nodes that permeate every domain. Cyberspace networks cross geographic and political boundaries to connect individuals, organizations, and systems around the world. Cyberspace allows interactivity among individuals, groups, organizations, and nation-states. Friendly, enemy, adversary, and host-nation networks, communications systems, computers, cellular phone systems, social media, and technical infrastructures are all part of cyberspace. Cyberspace is congested, contested, and critical to successful operations.
1-102. Cyberspace is dependent on the land, maritime, air, and space domains. Cyberspace operations use links and nodes located in these domains and perform functions to gain access and create effects first in cyberspace and then, as needed, in the other domains. Virtually all space operations depend on cyberspace, and a critical portion of cyberspace bandwidth can only be provided via space operations. These interrelationships are important considerations during planning.
1-103. Army forces conduct cyberspace operations and supporting activities as part of both Army and joint operations. Because cyberspace is a global communications and data-sharing medium, it is inherently joint, interorganizational, multinational, and often a shared resource, with signal and intelligence organizations maintaining significant equities.
1-104. Commanders can use cyberspace and electromagnetic warfare capabilities to gain situational awareness and understanding of the enemy through reconnaissance and sensing activities. These reconnaissance and sensing activities augment and enhance the understanding a commander gains from other forms of information collection and intelligence processes. Cyberspace and electromagnetic warfare capabilities enable decision making and protect friendly information. They are a significant means for informing and influencing audiences.
1-105. Leaders maintain situational understanding of friendly electromagnetic signatures to assess vulnerabilities. By protecting friendly information systems and signals from disruption or exploitation by an adversary or enemy, a commander can ensure C2 and maintain operations security. Conversely, a commander might use cyberspace and electromagnetic warfare capabilities to slow or degrade an enemy’s decision-making processes by disrupting enemy sensors, communications, or data processing. To achieve an information advantage, a commander must plan early to integrate cyberspace operations and electromagnetic warfare activities into the overall scheme of maneuver. (See FM 3-12 for more details on cyberspace.)
DIMENSIONS
1-106. Understanding the physical, information, and human dimensions of each domain helps commanders and staffs assess and anticipate the impacts of their operations. Operations reflect the reality that war is an act of force (in the physical dimension) to compel (in the information dimension) the decision making and behavior of enemy forces (in the human dimension). Actions in one dimension influence factors in the other dimensions. Understanding the interrelationship enables decision making about how to create and exploit advantages in one dimension and achieve objectives in the others without causing undesirable consequences.
1-107. The physical dimension is the material characteristics and capabilities, both natural and manufactured, within an operational environment. While war is a human endeavor, it occurs in a material environment, and it is conducted with physical things. Each of the domains is inherently physical. Terrain, weather, military formations, electromagnetic radiation, weapons systems and their ranges, and many of the things that support or sustain forces are part of the physical dimension. Activities or conditions in the physical dimension create effects in the human and information dimensions.
1-108. The electromagnetic spectrum is one of the material characteristics that crosses all the domains. It consists of a range of frequencies of electromagnetic radiation from zero to infinity divided into 26 alphabetically designated bands. The electromagnetic spectrum is relevant in the land, maritime, and air domains because capabilities in those domains depend on electromagnetic spectrum-enabled communications and weapon systems. The electromagnetic spectrum plays a key role in the ability to detect enemy forces that can be identified by their electromagnetic signatures. Conversely, friendly forces must take efforts to mask their electromagnetic signatures to degrade enemy surveillance and reconnaissance efforts.
1-109. A physical advantage occurs when a force holds the initiative in terms of a combination of quantitative capabilities, qualitative capabilities, or geographical positioning. Physical advantages are most familiar to tactical forces, and they are typically the immediate goal of most tactical operations. Finding enemy forces, defeating enemy forces, and seizing land areas typically requires the creation and exploitation of multiple physical advantages, including occupation of key terrain, the physical isolation of enemy forces, and the destruction of enemy units. While this dominates tactical operations, leaders understand that physical advantages both complement and are complemented by human and information advantages.
1-110. Examples of physical advantage include favorable geography, superior equipment, quantity of resources, and favorable combat power ratios. Superior equipment and favorable geography provide options for seizing the initiative. Superior combat power allows friendly forces to engage enemy forces on favorable terms. The exploitation of physical advantages reduces an enemy force’s capacity to fight, creating information and human advantages. Physical advantages implicitly communicate a message that can influence enemy forces’ will to fight, sway popular support, and influence enemy risk calculus.
1-111. The information dimension is the content, data, and processes that individuals, groups, and information systems use to communicate. Information systems include the technical processes and analytics used to exchange information. The information dimension contains the information itself, including text and images. It also includes the flow or communication pathways of information. Information exchange may be in the form of electromagnetic transmission, print, or speech. The information dimension connects humans to the physical world.
1-112. Information transits through all domains in some way or another, whether in electromagnetic transmissions through cyberspace, radar data collected by a destroyer, leaflets dropped from aircraft, social media messaging, books, or satellite photography collected in and transmitted from space. Information, whether true, false, or somewhere in between, is used by friendly, enemy, adversary, and neutral actors to influence the perceptions, decision making, and behavior of individuals and groups. Effective employment of information depends on the audience, message, and method of delivery.
1-113. Information is available globally in near-real time. The ability to access information—from anywhere, at any time—broadens and accelerates human interaction, including person to person, person to organization, person to government, and government to government. Social media enables the swift mobilization of people and resources around ideas and causes, even before they are fully understood. Disinformation creates malign narratives that can disseminate quickly and instill an array of emotions and behaviors among groups, ranging from disinterest to violence. From a military standpoint, information enables decision making, leadership, and combat power; it is also a key component of combat power necessary for seizing, retaining, and exploiting the initiative and consolidating gains.
1-114. An information advantage is the operational benefit derived when friendly forces understand and exploit the informational considerations of the operational environment to achieve information objectives while denying the threat’s ability to do the same. Army forces employ human and physical aspects of the operational environment to gain information advantages. Most types of information advantage result from physical and human factors or activities intrinsic to the operations Army forces conduct. The side possessing better information and using that information more effectively to understand and make decisions has an information advantage. A force that effectively communicates and protects its information while preventing the enemy from doing the same has an advantage. A force that uses information to deceive and confuse an opponent has an advantage. Using information to influence relevant actor behavior more effectively than an adversary or enemy is another information advantage.
1-115. The human dimension encompasses people and the interaction between individuals and groups, how they understand information and events, make decisions, generate will, and act within an operational environment. The will to act and fight emerges from the complex interrelationship of culture, emotion, and behavior. Influencing these factors—by affecting attitudes, beliefs, motivations, and perceptions—underpins the achievement of military objectives.
1-116. Commanders and staffs identify relevant actors and anticipate their behavior. Actors are individuals, groups, networks, and populations. Relevant actors are actors who, through their behavior, could substantially impact campaigns, operations, or tactical actions. From this understanding, commanders develop ways to influence relevant actor behavior, decision making, and will through physical and informational means.
1-117. A human advantage occurs when a force holds the initiative in terms of training, morale, perception, and will. Human advantages enable friendly morale and will, degrade enemy morale and will, and influence popular support. Examples of human advantages include leader and Soldier competence, morale of troops, and the health and physical fitness of the force. Forces with a cultural affinity to the population in which they operate are also a form of a human advantage. For Army forces, the mission command approach to C2 is a significant human advantage that enhances the friendly decision cycle. (See ADP 6-0 for more information on mission command.)
OPERATIONAL AND MISSION VARIABLES
1-118. The operational and mission variables are tools to assist commanders and staffs in refining their understanding of the domains and dimensions of an operational environment. Commanders and staffs analyze and describe an operational environment in terms of eight interrelated operational variables: political, military, economic, social, information, infrastructure, physical environment, and time (known as PMESII-PT). The operational variables help leaders understand the land domain and its interrelationships with information, relevant actors, and capabilities in the other domains.
1-119. Commanders analyze information categorized by the operational variables in the context of the missions they are assigned. They use the mission variables, in combination with the operational variables, to refine their understanding of the situation and to visualize, describe, and direct operations. The mission variables are mission, enemy, terrain and weather, troops and support available, time available, and civil considerations, each of which have informational considerations. The mission variables are represented as METT-TC (I). (See FM 5-0 for more information on operational and mission variables.) Informational considerations are those aspects of the human, information, and physical dimensions that affect how humans and automated systems derive meaning from, use, act upon, and are impacted by information. (See FM 5-0 for more details about informational considerations.)
Note. METT-TC (I) represents the mission variables leaders use to analyze and understand a situation in relationship to the unit’s mission. The first six variables are not new. However, the pervasiveness of information and its applicability in different military contexts requires leaders to continuously assess its various aspects during operations. Because of this, “I” has been added to the METT-TC mnemonic. Information considerations are expressed as a parenthetical variable because they are not an independent consideration, but an important component of each variable of METT-TC that leaders must understand when developing understanding of a situation.
Chapter 2 - Generating and Applying Combat Power
Army forces integrate capabilities and synchronize warfighting functions to generate combat power and apply it against enemy forces. Successful application of combat power requires leaders to understand the enemy and understand friendly capabilities. A broad understanding of the strategic environment and threat methods provides a basis for understanding specific enemy situations. Leaders must understand how Army forces enable joint operations through multiple domains and the basic roles of Army echelons. They must also understand how the joint force enables the Army to integrate capabilities through all domains to generate more effective landpower.
WARFIGHTING FUNCTIONS
2-1. A warfighting function is a group of tasks and systems united by a common purpose that commanders use to accomplish missions and training objectives (ADP 3-0). The warfighting functions are—
Command and control (C2).
Movement and maneuver.
Intelligence.
Fires.
Sustainment.
Protection.
2-2. The purpose of warfighting functions is to provide an intellectual organization for common critical capabilities available to commanders and staffs at all echelons and levels of war. Warfighting functions are not confined to single domain, and they typically include capabilities from multiple domains. Warfighting functions are not branch specific. Although some branches, staff sections, and types of units have a role or purpose that mainly aligns with a warfighting function, each warfighting function is relevant to all types of units.
THE COMMAND AND CONTROL WARFIGHTING FUNCTION
2-3. The command and control warfighting function is the related tasks and a system that enable commanders to synchronize and converge all elements of combat power (ADP 3-0). The primary purpose of the C2 warfighting function is to assist commanders in integrating the other warfighting functions (movement and maneuver, intelligence, fires, sustainment, and protection) effectively at each echelon, and to apply combat power to achieve objectives and accomplish missions.
2-4. The C2 system includes people, processes, networks, and command posts. All elements of the system are critical in supporting effective decision making and the tempo required to defeat enemy forces. C2 supports the creation and exploitation of information advantages through the activities of developing situational understanding, decision making, and operating networks.
2-5. C2 synchronizes the systems and capabilities that comprise the other warfighting functions. Strategy, operational art, planning, operational approaches, operational frameworks, risk assessment, and decision making are all part of C2. C2 reflects leader action and how Army forces achieve unity of effort and unity of purpose during operations. (See ADP 6-0 for more information on C2.)
THE MOVEMENT AND MANEUVER WARFIGHTING FUNCTION
2-6. The movement and maneuver warfighting function is the related tasks and systems that move and employ forces to achieve a position of relative advantage over the enemy and other threats (ADP 3-0). Direct fire and close combat are inherent in maneuver. The movement and maneuver warfighting function includes tasks associated with force projection. Movement is necessary to position and disperse the force as a whole or in part when maneuvering. Maneuver directly gains or exploits positions of relative advantage. Commanders use maneuver for massing effects to achieve surprise, shock, and momentum.
2-7. Effective maneuver requires some combination of reconnaissance, surveillance, and security operations to provide early warning and protect the main body of the formation. Every Soldier on the battlefield is a potential sensor that makes key contributions to information collection and the development of intelligence. Effective maneuver requires close coordination of fires and movement. Movement and maneuver contribute to the development of information advantages through the positioning of units able to employ capabilities in close proximity to the enemy, as well as by physically establishing the facts on the ground that an enemy or adversary cannot refute.
2-8. Maneuver requires sustainment. The movement and maneuver warfighting function does not include routine transportation of personnel and materiel that support operations, which falls under the sustainment warfighting function.
THE INTELLIGENCE WARFIGHTING FUNCTION
2-9. The intelligence warfighting function is the related tasks and systems that facilitate understanding the enemy, terrain, weather, civil considerations, and other significant aspects of the operational environment (ADP 3-0). Intelligence involves analyzing information from all sources, which includes the other warfighting functions, and conducting operations to collect information. The integration of intelligence into operations facilitates understanding of an operational environment and assists in determining when and where to employ capabilities against adversaries and enemies. Intelligence likewise facilitates responses by Army forces to other situations, such as public health crises and events precipitating noncombatant evacuation. The intelligence warfighting function provides support to force generation, situational understanding, targeting and information operations, and information collection. The intelligence warfighting function fuses the information collected through reconnaissance, surveillance, security operations, and intelligence operations. Commanders drive intelligence and intelligence drives operations. Army forces execute intelligence, surveillance, and reconnaissance (ISR) through the operations and intelligence processes, with an emphasis on intelligence analysis and information collection.
2-10. Timely, accurate, relevant, and predictive intelligence enables decision making, tempo, and agility during operations. Due to the fog and friction of warfare, commanders must fight for intelligence and share it with adjacent units and across echelons. (See ADP 2-0 for additional information on the intelligence warfighting function.)
THE FIRES WARFIGHTING FUNCTION
2-11. The fires warfighting function is the related tasks and systems that create and converge effects in all domains against the adversary or enemy to enable operations across the range of military operations (ADP 3-0). These tasks and systems create lethal and nonlethal effects delivered from both Army and joint forces and other unified action partners. The fires warfighting function does not entirely encompass, nor is it wholly encompassed by, any particular branch or function. Many of the capabilities that contribute to fires also contribute to other warfighting functions, often simultaneously. For example, an aviation unit may simultaneously execute missions that contribute to the movement and maneuver, fires, intelligence, sustainment, protection, and C2 warfighting functions. Space and cyberspace capabilities can provide commanders with options to defeat, destroy, disrupt, deny, or manipulate enemy networks, information, and decision making. (See ADP 3-19 for additional information on the fires warfighting function.)
THE SUSTAINMENT WARFIGHTING FUNCTION
2-12. The sustainment warfighting function is the related tasks and system that provide support and services to ensure freedom of action, extended operational reach, and prolong endurance (ADP 3-0). Sustainment employs capabilities from all domains and enables operations through each domain. Sustainment determines the limits of depth and endurance during operations. Sustainment demands joint and strategic integration, and it should be meticulously coordinated across echelons to ensure continuity of operations and that resources reach the point of employment.
2-13. Sustainment employs an integrated network of information systems linking sustainment to operations. As a result, commanders at all levels see an operational environment, anticipate requirements in time and space, understand what is needed, track and deliver what is requested, and make timely decisions to ensure responsive sustainment. Because the situation is always changing, sustainment requires leaders capable of improvisation. Because sustainment operations are often vulnerable to enemy attacks, sustainment survivability depends on active and passive measures and maneuver forces for protection. (See ADP 4-0 and FM 4-0 for more information on sustainment.)
THE PROTECTION WARFIGHTING FUNCTION
2-14. The protection warfighting function is the related tasks, systems, and methods that prevent or mitigate detection, threat effects, and hazards to preserve combat power and enable freedom of action. Protection encompasses everything that makes Army forces hard to detect and destroy. Protection requires commanders and staffs to understand threats and hazards throughout the operational environment, prioritize their requirements, and commit capabilities and resources according to their priorities. Commanders balance their protection efforts with the need for tempo and resourcing the main effort. They may assume risk in operations or areas that may be vulnerable, but that are considered low enemy priorities for targeting or attack. Commanders account for threats from space, cyberspace, and outside their assigned area of operations (AO) as they develop protection measures. Protection results from many factors, including operations security, dispersion, deception, survivability measures, and the way forces conduct operations. Planning, preparing, executing, and assessing protection is a continuous and enduring activity. Defending networks, data, and systems; implementing operations security; and conducting security operations contribute to information advantages by protecting friendly information. Prioritization of protection capabilities is situationally dependent and resource informed. (See ADP 3-37 for additional information on protection.)
COMBAT POWER
2-15. Combat power is the total means of destructive and disruptive force that a military unit/formation can apply against an enemy at a given time (JP 3-0). It is the ability to fight. The complementary and reinforcing effects that result from synchronized operations yield a powerful blow that overwhelms enemy forces and creates friendly momentum. Army forces deliver that blow through a combination of five dynamics. The dynamics of combat power are—
Leadership.
Firepower.
Information.
Mobility.
Survivability.
2-16. All warfighting functions contribute to generating and applying combat power. Well sustained units able to move and maneuver bring combat power to bear against the opponent. Joint and Army indirect fires complement and reinforce organic firepower in maneuver units. Survivability is a function of protection tasks, the protection inherent to Army platforms, and schemes of maneuver that focus friendly strengths against enemy weaknesses. Intelligence determines how and where to best apply combat power against enemy weaknesses. C2 enables leadership, the most important qualitative aspect of combat power.
LEADERSHIP
2-17. Leadership is the most essential dynamic of combat power. Leadership is the activity of influencing people by providing purpose, direction, and motivation to accomplish the mission and improve the organization (ADP 6-22). It is the multiplying and unifying dynamic of combat power, and it represents the qualitative difference between units. Leadership drives C2 but is also dependent upon it. The collaboration and shared understanding inherent in the operations process prepare leaders for operations, expand shared understanding, hone leader judgment, and improve the flexibility that leaders apply to the other dynamics of combat power against enemy forces.
2-18. Commanders communicate their will to their formations through leadership. Sound leadership manifests as an unrelenting will to accomplish the mission, the ability to understand and adapt to changing conditions, and the motivation to persevere through hardship. Leadership inspires individuals to push past their perceived breaking point, and to fight for their unit and fellow Soldiers under the most difficult circumstances. It provides the intangible qualitative difference in how much combat power a formation can generate against enemy forces. (See ADP 6-22 for information on leadership.)
FIREPOWER
2-19. Firepower is the primary source of lethality, and it is essential to defeating an enemy force’s ability and will to fight. Leaders generate firepower through direct and indirect fires, using mass, precision, or, typically, a combination of the two. Intelligence enables the identification and selection of targets and objectives for the application of lethal force. Movement and maneuver enable the positioning of fires capabilities where they can be most lethal.
2-20. Firepower facilitates maneuver by suppressing enemy fires and disrupting or preventing the movement of enemy forces. Firepower exploits maneuver by neutralizing enemy forces when they react, destroying equipment and people, and degrading the will of enemy forces to fight.
2-21. Leaders increase firepower by using capabilities from all domains in combinations that overwhelm an enemy force’s ability to effectively respond. This is ammunition intensive. Discretion may require leaders to reserve limited numbers of precision munitions for specific, important targets, while they rely on conventional unguided munitions against enemy units and area targets. Large-scale combat requires large reserves of both precision and unguided munitions and the sustainment capacity to move them to forward locations. Air, maritime, space, and cyberspace-based fires enhance the firepower of ground forces. Similarly, ground-based firepower complements firepower from other domains. A multidomain approach to firepower requires understanding the techniques for controlling and integrating joint fires. This includes requesting and integrating space and cyberspace capabilities, electromagnetic attack capabilities, and air capabilities.
INFORMATION
2-22. Information contributes to the disruption and destruction of enemy forces. It is central to the application and amplification of combat power. It enables decision making and influences enemy perceptions, decision making, and behavior. Information, like leadership, provides a qualitative advantage to friendly combat power when it can be acted upon more quickly and effectively than the enemy.
2-23. Army forces collect data and information for analysis and process it to understand situations, make decisions, and direct actions that apply combat power against enemy forces. Army forces must fight for information about enemy forces while protecting their own information. Friendly counterintelligence, counterreconnaissance, and security operations prevent enemy access to friendly information. Offensively, commanders fight for information about enemy forces and terrain through continuous reconnaissance and surveillance and offensive tasks such as movement to contact or reconnaissance in force.
2-24. Army forces also use information to enhance the effects of destructive or disruptive physical force to create psychological effects that disrupt morale, cause human error, and increase uncertainty. Using information to manipulate shock and confusion amplifies the psychological effects of lethality and other dynamics of combat power.
2-25. Employing information to confuse, manipulate, or deceive can induce threats to act in ways that make them more vulnerable to destruction by Army forces. Employing information creatively can enable Army forces to achieve surprise, cause enemy forces to misallocate or expend combat power, or mislead them as to the strength, readiness, locations, and intended missions of friendly forces.
MOBILITY
2-26. Mobility is a quality or capability of military forces which permits them to move from place to place while retaining the ability to fulfill their primary mission (JP 3-36). Mobility encompasses the capability of a formation to move and apply capabilities in specific terrain under specific conditions relative to enemy forces. Exploiting mobility requires intelligence of an enemy force’s disposition, composition, strength, and course of action. This understanding allows leaders to assess their mobility in relation to adversary or enemy forces. Maneuver and fires increase relative mobility by fixing enemy units, reducing obstacles, and providing obscuration.
2-27. The environment impacts mobility and the level of combat power a unit can produce. For example, an armored brigade combat team’s (BCT’s) mobility is limited in dense jungle or urban terrain, but it increases in steppes, in deserts, and on modern roads. Weather affects mobility when it degrades route conditions, or when it increases risks to fixed- and rotary- wing aviation operations. Space-based environmental monitoring provides real-time understanding of the impacts of weather on terrain and mobility. Enemy forces also influence conditions that affect mobility. For example, enemy standoff approaches can isolate land forces operating on islands in maritime environments by destroying maritime transportation capabilities and denying friendly air support.
2-28. Mobility is a function of how quickly units can move in specific terrain under specific conditions. At the tactical level, Army forces exploit mobility to conduct information collection, posture forces in advantageous locations, position fires to range enemy forces, and move classes of supply around an AO. During offensive operations, mobility enables forces to concentrate and then disperse rapidly, achieve surprise, attack enemy forces in unexpected locations, exploit opportunity, and evade enemy fires. During defensive operations, mobility enables counterattacks and the ability to rapidly shift resources between fixed positions. The ability to conduct gap crossings and passage of lines are other operations that can facilitate mobility.
SURVIVABILITY
2-29. Survivability is a quality or capability of military forces which permits them to avoid or withstand hostile actions or environmental conditions while retaining the ability to fulfill their primary mission (ATP 3-37.34). It represents the degree to which a formation is hard to kill. Survivability is relative to a unit’s capabilities and the type of enemy effects it must withstand, its ability to avoid detection, and how well it can deceive enemy forces. Survivability is also a function of how a formation conducts itself during operations. For example, an infantry BCT’s survivability against indirect fire is contingent on it not being detected, being dispersed, digging in, and adding overhead cover when stationary. An armor BCT’s survivability is a function of logistics, security, and avoiding situations that constrain its mobility or freedom of action.
2-30. Leaders assess survivability as the ability of a friendly force to withstand enemy effects while remaining mission capable. Armor protection, mobility, tactical skill, avoiding predictability, and situational awareness contribute to survivability. Enforcement of operations security techniques and avoiding detection while initiating direct fire contact on favorable terms also increases survivability. Situational awareness regarding the nine forms of contact and minimizing friendly signatures contributes to survivability.
2-31. To increase survivability, units employ air defense systems, reconnaissance and security operations, modify tempo, take evasive action, maneuver to gain positional advantages, decrease electromagnetic signatures, and disperse forces. Dispersed formations improve survivability by complicating targeting and making it more difficult for enemy forces to identify lucrative targets. Tactical units integrate procedures for the use of camouflage, cover, concealment, and conducting electromagnetic protection—including noise and light discipline. During large-scale combat operations, survivability measures may include radio silence, communication through couriers, or alternate forms of communication. Space-based missile warning systems provide early warning of adversary artillery and missile attacks, allowing friendly forces to seek cover. Application of chemical, biological, radiological, and nuclear (CBRN) defense measures increase survivability in CBRN environments. (See ATP 3-37.34 for more information on survivability.)
STRATEGIC ENVIRONMENT
2-32. The central challenge to U.S. security is the reemergence of long-term, great power competition with China and Russia as individual actors and as actors working together to achieve common goals. China uses its rapidly modernizing military, information warfare, and predatory economics to coerce neighboring countries to reorder the Indo-Pacific region to its advantage. Concurrently, Russia seeks veto authority over nations on its periphery in terms of its governmental, economic, and diplomatic decisions, to subvert the North Atlantic Treaty Organization (NATO), and to change European and Middle East security and economic structures to its favor.
2-33. In addition to China and Russia, several other states threaten U.S. security. North Korea seeks to guarantee survival of its regime and increase its leverage. It is pursuing a mixture of CBRN, conventional, and unconventional weapons and a growing ballistic missile capability to gain coercive influence over South Korea, Japan, and the United States. Similarly, Iran seeks dominance over its neighbors by asserting an arc of influence and instability while vying for regional hegemony. Iran uses state-sponsored terrorist activities, a network of proxies, and its missile capabilities to achieve its objectives.
2-34. While states are the principal actors on the global stage, non-state actors also threaten the strategic environment with increasingly sophisticated capabilities. Terrorists, transnational criminal organizations, threat cyber actors, and other malicious non-state actors have transformed global affairs with increased capabilities of mass disruption. Terrorism remains a persistent tactic driven by ideology and enabled by political and economic structures.
THREATS
2-35. A threat is any combination of actors, entities, or forces that have the capability and intent to harm United States forces, United States national interests, or the homeland (ADP 3-0). Threats faced by Army forces are, by nature, hybrid. They include individuals, groups of individuals, paramilitary or military forces, criminal elements, nation-states, or national alliances. In general, a threat can be categorized as an enemy or an adversary:
An enemy is a party identified as hostile against which the use of force is authorized (ADP 3-0). An enemy is also a combatant under the law of war.
An adversary is a party acknowledged as potentially hostile to a friendly party and against which the use of force may be envisaged (JP 3-0). Adversaries pursue interests that compete with those of the United States and are often called competitors.
2-36. Army forces are organized, trained, and equipped primarily for large-scale combat operations against peer threats. Army units supporting combatant commanders (CCDRs) where no peer threat exists focus on other missions, but they can alter their priorities to support large-scale combat operations when necessary. Peer threats are adversaries or enemies with capabilities and capacity to oppose U.S. forces across multiple domains worldwide or in a specific region where they enjoy a position of relative advantage. Peer threats possess roughly equal combat power to U.S. forces in geographic proximity to a conflict area. Peer threats may also have a cultural affinity with specific regions, providing them relative advantages in the human and information dimensions.
2-37. Peer threats employ strategies that capitalize on their advantages to achieve objectives. When these objectives are at odds with the interests of the United States and its allies, conflict becomes more likely. Peer threats prefer to achieve their goals without directly engaging U.S. forces in combat. They often employ information warfare in combination with conventional and irregular military capabilities to achieve their goals. They exploit friendly sensitivity to world opinion and attempt to exploit American domestic opinion and sensitivity to friendly casualties. Peer threats believe they have a comparative advantage because of their willingness to endure greater hardships, casualties, and negative public opinion. They also believe their ability to pursue long-term goals is greater than that of the United States.
2-38. Peer threats employ capabilities from and across multiple domains against Army forces, and they seek to exploit vulnerabilities in all strategic contexts. During conflict, peer threats seek to inflict significant damage across multiple domains in a short amount of time. They seek to delay friendly forces long enough to achieve their goals and end hostilities before friendly forces can decisively respond.
THREAT METHODS
2-39. Peer threats use various methods to render U.S. military power irrelevant whenever possible. Five broad peer threat methods, often used in combination during conventional or irregular conflicts, and below the threshold of conflict, include—
Information warfare.
Systems warfare.
Preclusion.
Isolation.
Sanctuary.
2-40. In the context of the threat, information warfare refers to a threat’s orchestrated use of information activities (such as cyberspace operations, electronic warfare, and psychological operations) to achieve objectives. Operating under a different set of ethics and laws than the United States, and under the cloak of anonymity, peer threats conduct information warfare aggressively and continuously to influence populations and decision makers. They can also use information warfare to create destructive effects during competition and crisis. During armed conflict, peer threats use information warfare in conjunction with other methods to achieve strategic and operational objectives.
Note. Threat forces use the term electronic warfare, which differs from U.S. doctrine’s use of electromagnetic warfare. Electronic warfare consists of the measures threats conduct to control or deny friendly use of the electromagnetic spectrum, while ensuring its use by the threat. For U.S. forces, electromagnetic warfare is military action involving the use of electromagnetic and directed energy to control the electromagnetic spectrum or to attack the enemy (JP 3-85).
2-41. Threats seek to employ information warfare to attack or disrupt in depth, including within the continental United States, viewing it as a low-cost and low-risk activity. A cyberspace attack may disrupt U.S. infrastructure that impedes deployment of forces, or a disinformation campaign can reduce morale and the will to fight. In some situations, threats use proxies for information warfare to achieve policy aims without having to incur the risks associated with employing military forces or official government entities.
2-42. Peer threats typically have fewer policy and legal restrictions than U.S. forces on how they employ information warfare, giving them an initial advantage. They exploit the nature of open societies while restricting their population’s access to information. They often obscure their activities to prevent detection or attribution.
2-43. Peer threats are free to sow disinformation among U.S. and allied populations while at the same time strictly limiting access to and manipulating the information their own populations receive. They employ all available means to influence a wide range of audiences, including both civilian and military and domestic and international, in support of their goals. Information warfare is a means to exploit shared cultural norms, historical grievances, and a self-serving interpretation of international law to limit U.S. military options and degrade U.S. political will. Peer threats use diverse means to conduct information warfare, and these means may include—
Cyberspace operations.
Perception management.
Deception.
Electronic warfare.
Physical destruction.
Political warfare.
Legal warfare.
Proxies and non-state actors.
2-44. Peer threats systematically and continuously combine all of these means to create specific effects within the human, information, and physical dimensions of an operational environment. Peer threats use misinformation, disinformation, propaganda, and information for effect to create doubt, confuse, deceive, and influence U.S. and partner decision makers, forces, and target audiences. They also use information warfare to destroy essential network-based capabilities, such as economic infrastructure, private and government communications, and electrical grids. This use of information warfare is not merely disruptive. It can result in the loss of immense resources and human life, depending on the scale and duration of the attack. (See FM 3-53 for a discussion of threat information categories.)
2-45. Systems warfare is the identification and isolation or destruction of critical subsystems or components to degrade or destroy an opponent’s overall system. Peer threats view the battlefield, their own instruments of power, and an opponent’s instruments of power as a collection of complex, dynamic, and integrated systems composed of subsystems and components. They use systems warfare to attack critical components of a friendly system while protecting their own system. Simple examples of attacking critical components are adversary use of electronic warfare to disable the links between unmanned aircraft system (UAS) controllers and the aircraft in a specific area, and the emplacement of layered integrated air defense systems from a position of sanctuary to prevent the integration of opposing airpower with ground operations.
2-46. Peer threats believe that a qualitatively or quantitatively weaker force can defeat a superior force, if the weaker force can dictate the terms of combat. Peer threats believe that the systems warfare approach allows them to move away from the conventional approach to combat. Systems warfare makes it unnecessary to match an opponent system-for-system or capability-for-capability. Peer threats seek to locate the critical components of the opposing combat system, determine patterns of interaction and dependencies among components, and identify opportunities to exploit this connectivity.
2-47. Systems warfare approaches work in concert with other approaches, and they manifest themselves at the tactical level in terms of integrated fires complexes characterized by surface-to-surface and surface-toair systems enabled by long-range ISR capabilities. They generally represent one means by which adversaries achieve preclusion at the strategic and operational levels, and they are adversaries’ preferred means for destroying friendly forces at the tactical level. An example of systems warfare occurred in Ukraine in 2014.
During the Russia-Ukraine conflict, an attack on Ukrainian forces demonstrated the lethality of the modern battlefield and the impact created by the threat’s use of sanctuary and systems warfare. In July 2014, the Armed Forces of Ukraine moved several mechanized brigades into a position near the Russian border to prevent the illegal movement of military equipment across the frontier to rebels in eastern Ukraine. Early on the morning of 11 July, soldiers at the position noticed a drone orbiting above them for some time. Not long after the drone disappeared, rockets fired from 9A52-4 Tornado multiple launch rocket systems located in Russian territory began landing on one of the brigades. Reporting indicated that the UAS was cued by other systems that located civilian cell phones in the assembly area.
The barrage lasted four minutes. Rockets carrying a mixture of high explosive, cluster, and thermobaric munitions impacted the unit’s position. Cannon rounds followed the rockets with devastating effect. The Ukrainian units took heavy losses. One battalion was virtually destroyed, and others were rendered combat ineffective due to heavy losses in vehicles and personnel. Casualties quickly overwhelmed army and local medical facilities. In the days that followed, rocket and cannon strikes continued, disrupting the Ukrainian army’s ability to defend that region of eastern Ukraine.
The lethality of the attacks was enabled by a sophisticated real-time targeting system that used inexpensive unmanned aircraft systems for ISR, target acquisition, and fire control. Rockets were likely fired from within a town in Russian territory, hampering potential Ukrainian military responses due to the sanctuary provided by both an international border and proximity to civilian noncombatants. Additionally, Russia extended its integrated air defense system, located within Russian territory, over the conflict zone in Ukraine. This action denied Ukraine’s ability to use its air power, which separated Ukraine’s air capability from its ground forces. Without air power for close air support and counter-UAS operations, the Ukrainian ground forces were left vulnerable to the sophisticated targeting systems used by Russian and pro-Russian forces.
Over the following months and years, Ukraine military forces adapted. In 2022, Russia began an unprovoked conventional attack along multiple axes throughout Ukraine. Ukrainian forces responded effectively. They exercised a more disciplined and efficient use of the electromagnetic spectrum, complicating Russian detection efforts. Ukrainian forces also defended in more mobile, dispersed formations, providing fewer lucrative targets for Russian fires.
2-48. To preclude is to keep something from happening by taking action in advance. Peer threats use a wide variety of actions, activities, and capabilities to preclude a friendly force’s ability to shape an operational environment and mass and sustain combat power. Antiaccess (A2) and area denial (AD) are two strategic and operational approaches to preclusion. Antiaccess is an action, activity, or capability, usually long-range, designed to prevent an enemy force from entering an operational area (JP 3-0). For example, A2 activities prevent or deny forces the ability to project and sustain forces into a desired area. The employment of A2 capabilities against Army forces begins in the continental United States and extends throughout the strategic support area into a theater. Peer threats have the means to disrupt the United States’ force projection capability at home station. These means include ballistic missiles; cruise missiles; and space, cyberspace, and information warfare capabilities.
2-49. Area denial is an action, activity, or capability, usually short-range, designed to limit an enemy force’s freedom of action within an operational area (JP 3-0). Usually adversaries do not design area denial to keep friendly forces out, but rather to limit their freedom of action and ability to accomplish their mission within an operational area. Threat forces pursue AD using long-range fires, integrated air defense systems, electronic warfare, CBRN, manmade obstacles, and conventional ground maneuver forces. Figure 2-1 and figure 2-2 depict employment of A2 and AD approaches in different types of theaters. For illustration purposes, A2 and AD reach are tied to specific capabilities. However, adversary forces can use different actions, activities, or capabilities in an A2 or AD approach.


2-50. Isolation is the containment of a force so that it cannot accomplish its mission. Peer threats will attempt to isolate U.S. forces in several ways. Some examples include—
Attacking political bonds with allies and partners.
Preventing or limiting communications to and in an AO.
Interdicting or severing lines of communication to block support or reinforcement of forward-positioned units.
Deceiving friendly forces about the current situation and their role in the operational environment.
Deceiving the public about the current situation to reduce its support of friendly operations that counter threat goals.
Exploiting inadequate friendly understanding of an operational environment or cultural affinity in an area or region.
Blocking support or reinforcement of forward-positioned units through direct and indirect fires.
Using economic coercion.
Preventing friendly access and overflight.
2-51. During competition, peer threats may attempt to isolate friendly forces using disinformation campaigns and the threat of aggression. During crisis, peer threats seek to isolate U.S. forward-positioned forces and prevent their support from the United States or elsewhere in theater. During armed conflict, enemy forces identify isolated friendly forces using a variety of capabilities and rapidly attempt to destroy them through long-range, massed, and precision fires.
2-52. Sanctuary is the positioning of threat forces beyond the reach of friendly forces. It is a form of protection derived by some combination of political, legal, and physical boundaries that restricts freedom of action by a friendly force commander. Peer threats will use any means necessary, including sanctuary, to protect key capabilities from destruction, particularly by air and missile capabilities. Peer threats will also protect their key interests, whether these interests reside in their homeland or in another country. To create a sanctuary that protects key interests, adversaries employ combinations of both physical and nonphysical means to protect key interests, including—
International borders.
Complex terrain.
Hiding among noncombatants and culturally sensitive structures.
Counterprecision techniques, including camouflage, concealment, and deception.
Countermeasures, including decoys, hardened and buried facilities, integrated air defense systems, and long-range fires.
Information warfare.
Threatening attacks against the U.S. homeland, possibly using including weapons of mass destruction.
International law, treaties, and treaty agreements.
Internal population information control (by denying the internet or jamming external radio and television).
2-53. Most means of sanctuary cannot protect an entire enemy force for an extended time. Therefore, a threat will seek to protect selected elements of its forces for enough time to gain the freedom of action necessary to pursue its strategic or diplomatic goals. Threat forces seek to protect their conventional forces, advanced aircraft, and extended-range fires systems. Many peer threats invest in long-range rocket and missile systems, such as the Russian Smerch 9A52 and Chinese PHL-03, capable of counterfire at extreme ranges to allow sanctuary behind international borders. Improved air defense systems, including counter ballistic missile systems, often provide protection for these advanced fires capabilities.
UNIFIED ACTION AND ARMY FORCES
2-54. To counter threats and protect national interests worldwide, the Armed Forces of the United States operate as a joint force in unified action. Unified action is the synchronization, coordination, and/or integration of the activities of governmental and nongovernmental entities with military operations to achieve unity of effort (JP 1, Volume 1). Unity of effort is coordination and cooperation toward common objectives, even if the participants are not necessarily part of the same command or organization, which is the product of successful unified action (JP 1, Volume 2). Army forces, as part of unified action, conduct operations in support of the joint force, with multinational allies and partners, and in coordination with other agencies and organizations. The Army’s contribution to unified action is multidomain operations which seek to employ all available capabilities in unexpected combinations that create and exploit relative advantages. Leaders must be capable of employing all unified action partners to the greatest extent possible, including conventional forces, special operations forces, allies, partner-nation forces, territorial defense forces, and any other organization or individual whose efforts can legally be harnessed to help achieve objectives.
JOINT OPERATIONS AND ACTIVITIES
2-55. Single Services may perform tasks and missions to support Department of Defense (DOD) objectives. However, the DOD primarily employs two or more Services (from two military departments) in a single operation from, in, and across multiple domains, particularly in combat, through joint operations. Joint operations are military actions conducted by joint forces and those Service forces employed in specified command relationships with each other, which, of themselves, do not establish joint forces (JP 3-0). A joint force is a force composed of elements, assigned or attached, of two or more military departments operating under a single joint force commander (JP 3-0). Joint operations exploit the advantages of interdependent Service capabilities in multiple domains through unified action. Joint planning integrates military power with other instruments of national power (including diplomatic, economic, and informational) to achieve a desired military end state. The end state is the set of required conditions that defines achievement of the commander’s objectives (JP 3-0). Joint planning connects the strategic end state to the joint force commander’s (JFC’s) campaign design and ultimately to tactical missions. JFCs use campaigns and major operations to translate their operational-level actions into strategic results.
2-56. The joint force is organized, trained, and equipped for sustained large-scale combat anywhere in the world. The capabilities to conduct large-scale combat operations enable a wide variety of other operations and activities. In particular, opportunities exist prior to large-scale combat to shape an operational environment to prevent, or at least mitigate, the effects of war. Characterizing the employment of military capabilities (including people, organizations, and equipment) as one or another type of military operation has several benefits. For example, the Army can develop publications that describe the nature, tasks, and tactics associated with specific types of diverse operations, such as counterinsurgency and peace operations.
2-57. Doctrine categorizes joint operations and activities by their focus, as shown in figure 2-3. In some cases, the title covers a variety of missions, tasks, and activities. Many activities are accomplished by Army forces and do not constitute joint operations, such as tasks associated with security cooperation. Nonetheless, most of these occur under a joint “umbrella,” because they contribute to achievement of CCDRs’ campaign objectives.

MULTINATIONAL OPERATIONS
2-58. Multinational operations is a collective term to describe military actions conducted by forces of two or more nations, usually undertaken within the structure of a coalition or alliance (JP 3-16). While each nation has its own interests and often participates within the limitations of national caveats, all nations bring value to an operation. Each nation’s force has unique capabilities, and each usually contributes to an operation’s legitimacy in terms of international or local acceptability. Army forces should anticipate that most operations will be multinational and plan accordingly. (See FM 3-16 for more information on multinational operations.)
2-59. Multinational operations present challenges and demands. These include culture and language issues, unresolved policy issues, technical and procedural interoperability challenges, national caveats on the use of respective forces, the authorities required for sharing of information and intelligence, and rules of engagement. Commanders analyze the particular requirements of a mission in the context of friendly force capabilities to exploit the multinational force’s advantages and compensate for its limitations. Establishing effective liaison with multinational partners through embedded teams, collaborative systems, and leader contact is critical to establishing a common operational picture (COP) and maintaining situational understanding.
2-60. Multinational operations also present many opportunities. Having multinational forces as part of an operation provides international legitimacy that helps isolate adversary or enemy forces. They may provide cultural awareness, foreign language skills, and affinities with populations that help with understanding the environment, conducting stability tasks, and transitioning to legitimate authorities. Allies and partners often operate with different authorities to employ key capabilities in space, cyberspace, and the information dimension of an operational environment. Lastly, multinational allies and partners bring additional forces to an operation, and they often possess capabilities U.S. Army forces may lack.
INTERAGENCY COORDINATION AND INTERORGANIZATIONAL COOPERATION
2-61. Interagency coordination is a key part of unified action. Interagency coordination is the planning and synchronization of efforts that occur between elements of Department of Defense and participating United States Government departments and agencies (JP 3-0). Army forces conduct and participate in interagency coordination using established liaison, personal engagement, and planning processes.
2-62. Unified action may require interorganizational cooperation to build the capacity of unified action partners. Interorganizational cooperation is the interaction that occurs among elements of the Department of Defense; participating United States Government departments and agencies; state, territorial, local, and tribal agencies; foreign military forces and government agencies; international organizations; nongovernmental organizations; and the private sector (JP 3-08). Interorganizational cooperation includes civil-military integration. (See FM 3-57 for more information on civil-military integration.)
CONVENTIONAL AND SPECIAL OPERATIONS FORCES INTEGRATION
2-63. Army forces integrate conventional and special operations forces to create complementary and reinforcing effects during operations. The mission and operational environment drive the command and support relationships between conventional and special operations forces during an operation. Regardless of C2 and support arrangements, both types of forces integrate and synchronize operations to increase effectiveness, promote interdependence, provide mutual support, limit the redundant use of resources, and reduce the risk of fratricide.
2-64. During large-scale combat, conventional forces contribute mass across all warfighting functions required to defeat enemy forces. Special operations forces complement conventional forces by performing their core activities:
Civil affairs operations.
Countering weapons of mass destruction.
Counterinsurgency.
Counterterrorism.
Direct action.
Foreign humanitarian assistance.
Foreign internal defense.
Hostage rescue and recovery.
Military information support operations.
Security force assistance
Special reconnaissance.
Unconventional warfare.
SOF contributions during deep and extended deep operations are often critical to setting conditions for conventional close and rear operations.
SOF contributions during deep and extended deep operations are often critical to setting conditions for conventional close and rear operations.
2-65. Because operations often include conventional and irregular forces from multinational partners, commanders must consider how they will maintain unity of effort without direct command authority. Security force assistance brigades (SFABs) provide the ability to partner with conventional allies and partners. Special operations forces enhance unity of effort by integrating irregular forces through security force assistance, foreign internal defense, and unconventional warfare. (See ATP 3-96.1 for more information on security force assistance brigades. See FM 6-05 for more information on integrating conventional forces and special operations forces.)
JOINT INTERDEPENDENCE
2-66. Joint interdependence is the purposeful reliance by one Service on another Service’s capabilities to maximize complementary and reinforcing effects of both. The degree of interdependence varies with specific circumstances.
2-67. The Army depends on the other Services for strategic and operational mobility, joint fires, and other key enabling capabilities. The Army supports the other Services, combatant commands, and unified action partners with ground-based indirect fires and air and missile defense (AMD), defensive cyberspace operations, electromagnetic warfare, communications, intelligence, rotary-wing aircraft, logistics, and engineering. The Army’s ability to set and sustain a theater of operations is essential to allowing the joint force freedom of action. The Army establishes, maintains, and defends vital infrastructure. It also provides the JFC with unique capabilities, such as port and airfield opening, logistics, CBRN defense, and reception, staging, onward movement, and integration of forces (RSOI).
DOMAIN INTERDEPENDENCE
2-68. The Army provides forces and capabilities from all domains to the joint force. Army forces employ joint capabilities from all domains to complement and reinforce their own capabilities. Understanding domain interdependences helps leaders better mitigate friendly vulnerabilities while creating and exploiting relative advantages. Successful operations in an environment where the enemy can contest every domain requires continuous joint integration down to the lowest tactical echelons.
2-69. Land capabilities enable air operations in multiple ways. Some of these ways include—
Fixing enemy ground forces for destruction from the air.
Providing air-delivered fires through rotary-wing and UAS platforms.
Controlling, securing, and defending airports and airfields.
Securing land-based C2 nodes for air operations.
Destroying enemy surface-to-air systems.
Employing surface-to-air fires.
Integrating all-source intelligence to identify threats to friendly air capabilities.
Providing logistics support to other Service components.
2-70. Air capabilities enable land operations in multiple ways. Some of these ways include—
Providing air-to-ground fires.
Providing offensive and defensive depth through air interdiction and strategic attack.
Protecting ground forces from air attack.
Employing airborne platforms for information collection.
Providing aerial movement of personnel, equipment, and supplies.
Employing airborne electromagnetic warfare platforms.
2-71. Land capabilities enable space operations in multiple ways. Some of these ways include—
Destroying enemy space ground stations, ground links, and launch sites with surface-to-surface fires.
Securing ground links and launch sites.
Securing bases and C2 nodes for units controlling space capabilities.
Securing bases and C2 nodes from which to launch attacks against enemy space capabilities.
2-72. Space capabilities enable land operations in multiple ways. Some of these ways include—
Enabling geolocation and timing-dependent technology, including global positioning systems and precise and accurate fires.
Enabling a global C2 network through satellite communications.
Enhancing situational understanding by providing meteorological, oceanographic, and space environmental factors and detailed imagery of land areas and enemy dispositions on land.
Deceiving, disrupting, degrading, denying, or destroying enemy space systems.
Conducting navigation warfare to disrupt enemy use of positioning, navigation, and timing-enabled devices.
Enabling theater missile warning and other warning intelligence.
2-73. Land capabilities enable cyberspace operations in multiple ways. These include—
Securing critical cyberspace infrastructure including data storage facilities, wired network transport, ground-based repeaters, and terminals.
Conducting information activities that protect and defend joint communications networks and data.
Conducting physical attacks against enemy cyberspace-based capabilities and infrastructure on land.
Defeating enemy forces collecting information through cyberspace.
2-74. Cyberspace capabilities enable land operations in multiple ways. Some of these ways include—
Enabling secure global communications and a shared COP.
Supporting decision making and logistics.
Facilitating high-volume data storage and knowledge management.
Networking sensors and fires platforms.
Attacking enemy networks including C2, integrated air defense systems, and integrated long-range fires systems.
Enabling rapid communication to audiences through social media and other applications.
Enabling targeted influence operations.
2-75. Land capabilities enable maritime operations in multiple ways. Some of these ways include—
Attacking land-based threats to maritime capabilities, including enemy air bases, surface-to-surface fires, and sensors.
Protecting ports and defending land areas that control maritime choke points.
Denying maritime areas with surface-to-surface fires and surface-to-air fires.
Integrating joint all-source intelligence to identify threats to maritime capabilities.
Providing directed logistics support to maritime oriented forces operating from land.
2-76. Maritime capabilities enable land operations in multiple ways. Some of these ways include—
Increasing operational reach and lethality through long-range fires systems and information collection.
Providing access to otherwise inaccessible land areas.
Providing and protecting transportation of units, equipment, and supplies on a large scale, over strategic distances.
Integrating with all-source intelligence.
Preventing enemy forces from using sea lines of communications and supply routes.
Attacking enemy maritime threats to land forces.
ARMY FORCE POSTURE
2-77. The Army postures forces in a way that balances the need for sustainable readiness with the need for responsiveness. Forward-stationed and rotational forces provide CCDRs with support to operations during competition and rapid response during crisis. These forces are usually small in number and may be vulnerable if the situation rapidly escalates to armed conflict. Forces based in strategic support areas allow for unit training and a sustainable readiness cycle. These forces are part of the Army’s global response capability, or they are in support of regional contingency plans that typically have deployment timelines that occur over months.
2-78. Army Reserve Components support a wide variety of domestic and global Army operations. Although they constitute about half of the Army’s organized units, they provide about 80 percent of the Army’s sustainment units, over 70 percent of maneuver support units, a fourth of the Army’s mobilization base expansion capability, and most of its civil affairs capacity. The Army Reserve Components are also the Army’s major source of trained individual Soldiers for strengthening headquarters and filling vacancies in the Regular Army during a crisis. Reserve Components provide a key resource for reconstitution operations during armed conflict. It is critical for planners to understand that Reserve Components forces have mobilization requirements that take time and typically have deployment time limits that must factor into force management and contingency plans. (See ADP 1 for more information on Army reserve forces. See Chapter 6 for more information on reconstitution. See Chapter 5 for information on reserve mobilization.)
ARMY ECHELONS
2-79. The Army operates through the use of echelons to ensure manageable spans of control for leaders. Echelons generally correspond to a particular level of warfare, but they may contribute to two or more levels depending on the situation.
2-80. Generally, higher echelons (for example, divisions and higher) have greater experience in their command teams and staffs. They have the expertise and perspective to coordinate large-scale operations and complex or politically sensitive tasks. They retain control of scarce resources so that they can employ them at the right time and place. This often includes joint air, space, maritime, and cyberspace capabilities. Higher echelons generally employ these critical capabilities to set conditions for lower echelon success and to weight the main effort appropriately. Higher echelons maneuver subordinate formations and use capabilities from all domains to shape the environment and create and exploit relative advantages. Generally speaking, the joint force command degrades enemy strategic capabilities to enable forcible entry and sustained operations. The land component command sets the theater, defeats enemy long- and mid-range fires, provides operational-level sustainment, and apportions joint capabilities to corps. Corps, operating as tactical formations, defeat enemy mid-range fires, employ joint capabilities to set conditions for divisions to maneuver, and maintain the tempo of operations through sustainment and other rear operations. Divisions defeat enemy short-range fires, mass effects on enemy forward echelons, and synchronize BCT maneuver in close combat with enemy forces. BCTs conduct close operations to defeat and destroy enemy forces during battles and engagements.
2-81. Generally, subordinate echelons (for example, brigades and lower) contribute to the overall mission by executing tasks and fulfilling the purpose assigned to their unit. They provide awareness to the higher echelon with their proximity to the current situation at the point of execution. While higher echelons provide broad perspective, subordinate echelons provide tactical fidelity. Combining the higher echelon perspective with the perspectives of subordinates creates the shared situational understanding that fosters disciplined initiative. Shared situational understanding does not require all leaders to agree. Instead, leaders use differences of opinion to frame the problem, assess operations, understand risk, and guide information collection.
2-82. The focus of echelons changes across strategic contexts as do their responsibilities for integrating multidomain capabilities into operations. Their broad roles are listed in paragraphs 2-79 through 2-94. (See Chapters 4, 5, and 6 for descriptions of each strategic context and more detailed information on echelon roles and responsibilities.)
2-83. The theater army’s mission is the most diverse and complex of any Army echelon. The theater army headquarters is tailored to a specific CCDR with the ability to conduct both operational and administrative C2 over Army forces theater wide. It provides enabling capabilities appropriate to theater conditions, such as theater intelligence, theater sustainment, theater signal, theater fires, theater information activities, civil affairs, engineer, and theater medical. In theaters without assigned field armies, corps, or divisions, the theater army assumes direct responsibility across warfighting functions for its tactical commands. The theater army is the Army Service component command to a geographic combatant command. The seven functions performed as the Army Service component command are—
Execute the CCDR’s daily operational requirements.
Provide administrative control (ADCON) of Army forces.
Set and maintain the theater.
Set and support operational areas.
Exercise C2 of Army forces in the theater.
Perform joint roles of limited scope, scale, and duration.
Plan and coordinate for the consolidation of gains in support of joint operations.
(See FM 3-94 and ATP 3-93 for additional information on theater army administrative and operational requirements.)
2-84. A field army is constituted to meet specific requirements. A field army may consist of a headquarters battalion with subordinate companies and special troops, a variable number of attached corps, an attached expeditionary sustainment command, a variable number of divisions normally attached to corps, and other attached functional and multifunctional brigades.
2-85. When required, a field army is an operational headquarters that provides C2 over multiple corps. During operations, forces are assigned or attached to the field army. Although it may employ subordinate units during operations, these units are provided by external Army, joint, and multinational sources based on the situation and the field army’s role and mission. When constituted, a field army is tailored to mission requirements and designed to perform operational ARFOR tasks; it is the Army component to the JFC to which it is assigned.
2-86. The field army provides additional operational capacity to a CCDR facing peer adversaries in its AOR. The field army is tailored based on the capabilities of the peer adversary. As the adversary’s capabilities change, so do those of the field army. When constituted, the field army provides Army, joint, and multinational forces with a headquarters capable of performing in a variety of ways across the range of military operations. Field armies are most likely to be employed in theaters where peer adversaries have the capability of conducting large-scale combat. These regions include the U.S. European Command and U.S. Indo-Pacific Command.
2-87. The corps is the most versatile echelon above brigade due to its ability to operate at both the tactical and operational levels. While it is organized, staffed, trained, and equipped to fight as a tactical formation, the corps may be called upon to become a joint and multinational headquarters for conducting operations. When operating as the senior Army headquarters under a joint task force (JTF), the corps will serve as the ARFOR. The corps can also serve as the coalition forces land component commander (CFLCC) when properly augmented with joint and multinational personnel. If the corps is uncommitted to specific CCDR requirements, it focuses on building and sustaining readiness to prevail in large-scale combat operations. The roles of the corps include acting as the—
Senior Army tactical formation in large-scale combat, commanding two to five Army divisions together with supporting brigades and commands.
ARFOR (with augmentation) within a joint force for campaigns and major operations when a field army is not present.
JTF headquarters (with significant augmentation) for crisis response and limited contingency operations.
CFLCC (with significant augmentation) commanding Army, Marine Corps, and multinational divisions together with supporting brigades and commands when a field army is not present.
2-88. During large-scale combat operations, a corps headquarters normally functions as a tactical headquarters under a joint or multinational land component. The corps is the echelon best positioned and resourced to achieve convergence with Army and joint capabilities. (See FM 3-94 and ATP 3-92 for more information about Army corps.)
2-89. The division is the Army’s principal tactical warfighting formation during large-scale combat operations. Its primary role is to serve as a tactical headquarters commanding brigades. A division conducts operations in an AO assigned by its higher headquarters—normally a corps. It task-organizes its subordinate forces according to the mission variables to accomplish its mission. A division typically commands between two and five BCTs, a mix of functional and multifunctional brigades, and a variety of smaller enabling units. The division is typically the lowest tactical echelon that employs capabilities from multiple domains to achieve convergence during large-scale combat operations. Winning battles and engagements remains the division’s primary purpose. During limited contingencies, it can organize itself to serve in multiple roles. The roles of the division include acting as a—
Tactical headquarters.
ARFOR headquarters (with significant augmentation).
CFLCC (with significant augmentation).
JTF headquarters (with significant augmentation).
(See FM 3-94 and ATP 3-91 for more information about Army divisions.)
2-90. A BCT is the Army’s primary combined arms, close-combat maneuver force. BCTs maneuver against, close with, and destroy enemy forces. BCTs seize and retain key terrain, exert constant pressure, and break the enemy’s will to fight. They are the principal ground maneuver units of a division or a JTF. Divisions seek to employ BCTs in mutually supporting ways to the greatest extent possible. However, BCTs must be capable of fighting isolated from higher echelon headquarters and adjacent units during periods of degraded communication and when operations are widely distributed.
2-91. There are three types of BCT: the infantry BCT, the armored BCT, and the Stryker BCT. Depending on the tactical situation, these three types of organizations are augmented with additional Army and joint capabilities to help them accomplish their missions. (See FM 3-96 for more information on Army BCTs.)
2-92. Theater armies, corps, and divisions are task-organized with an assortment of multifunctional and functional brigades to support their operations. These brigades add capabilities such as intelligence, attack and reconnaissance aviation, fires, protection, contracting support, or sustainment. The theater army may tailor subordinate corps and divisions with combinations of multifunctional brigades.
2-93. Multifunctional brigades provide a variety of functions in support of operations. Normally, they are attached to a corps or division, but they may be under the command of a joint or multinational headquarters. Multifunctional brigades include combat aviation brigades, field artillery brigades, sustainment brigades, and maneuver enhancement brigades.
2-94. A functional brigade provides a single function or capability. These brigades can provide support to a theater, corps, or division, depending on how each is tailored. Functional brigade organization varies extensively. Examples of functional brigades include SFABs, air defense artillery (ADA) brigades, civil affairs brigades, expeditionary military intelligence brigades, and engineer brigades.
Chapter 3 - Fundamentals of Operations
There are not more than five primary dataSetColors, yet in combination they produce more hues than can ever been seen.
There are not more than five cardinal tastes, yet combinations of them yield more flavors than can ever be tasted.
This chapter describes the Army’s operational concept, multidomain operations. It provides an overview of multidomain operations and describes it in terms of tenets, imperatives, an operational approach, a strategic framework, and an operational framework.
SECTION I – MULTIDOMAIN OPERATIONS: THE ARMY’S OPERATIONAL CONCEPT
3-1. The Army’s operational concept is multidomain operations. Multidomain operations are how Army forces contribute to and operate as part of the joint force. Army forces, enabled by joint capabilities provide the lethal and resilient landpower necessary to defeat threat standoff approaches and achieve joint force objectives.
3-2. The employment of joint and Army capabilities, integrated across echelons and synchronized in a combined arms approach, is essential to defeating threats able to contest the joint force in all domains. Army forces integrate land, maritime, air, space, and cyberspace capabilities that facilitate maneuver to create physical, information, and human advantages joint force commanders exploit across the competition continuum. Commanders and staffs require the knowledge, skills, and attributes to integrate capabilities rapidly and at the necessary scale appropriate to each echelon.
3-3. During competition, theater armies strengthen landpower networks, set the theater, and demonstrate readiness for armed conflict through the command and control (C2) of Army forces supporting the CCP. During crisis, theater armies provide options to combatant commanders (CCDRs) as they facilitate the flow and organization of land forces moving into theater. During armed conflict, theater armies enable and support joint force land component commander (JFLCC) employment of land forces. The JFLCC provides C2 of land forces and allocates joint capabilities to its corps and other subordinate tactical formations. Corps integrate joint and Army capabilities at the right tactical echelons and employ divisions to achieve JFLCC objectives. Divisions, enabled and supported by the corps, defeat enemy forces, control land areas, and consolidate gains for the joint force. Defeating or destroying enemy capabilities that facilitate the enemy’s preferred layered stand-off approaches are central to success. Ultimately, operations by Army forces both enable and are enabled by the joint force.
3-4. Because uncertainty, degraded communications, and fleeting windows of opportunity characterize operational environments during combat, multidomain operations require disciplined initiative cultivated through a mission command culture. Leaders must have a bias for action and accept that some level of uncertainty is always present. Commanders who empower leaders to make rapid decisions and to accept risk within the commander’s intent enable formations at echelon to adapt rapidly while maintaining unity of effort. (See ADP 6-0 for a detailed description of mission command.)
SECTION II – TENETS AND IMPERATIVES
3-5. There are no absolute rules for warfare. However, given analysis of the current strategic environment and assessments of the best ways to employ Army forces, doctrine emphasizes tenets and imperatives for operations that improve their prospects of success without dictating how exactly to solve a tactical or operational problem.
TENETS
3-6. The tenets of operations are desirable attributes that should be built into all plans and operations, and they are directly related to how the Army’s operational concept should be employed. Commanders use the tenets of operations to inform and assess courses of action throughout the operations process. The degree to which an operation exhibits the tenets provides insight into the probability for success. The tenets of operations are—
Agility.
Convergence.
Endurance.
Depth.
3-7. The Army provides forces capable of transitioning to combat operations, fighting for information, producing intelligence, adapting to unforeseen circumstances, and defeating enemy forces. Army forces employ capabilities from multiple domains in a combined arms approach that creates complementary and reinforcing effects through multiple domains, while preserving combat power to maintain options for the joint force commander (JFC). Creating and exploiting relative advantages require Army forces to operate with endurance and in depth. Endurance enables the ability to absorb the enemy’s attacks and press the fight over the time and space necessary to accomplish the mission. Depth applies combat power throughout the enemy’s formations and the operational environment, securing successive operational objectives and consolidating gains for the joint force.
AGILITY
3-8. The ability to act faster than the enemy is critical for success. Agility is the ability to move forces and adjust their dispositions and activities more rapidly than the enemy. Agility requires sound judgment and rapid decision making, often gained through the creation and exploitation of information advantages. Agility requires leaders to anticipate needs or opportunities, and it requires trained formations able to change direction, tasks, or focus as quickly as the situation requires. Change may come in the form of a transition between phases of an operation or the requirement to adapt to a new opportunity or hazard.
3-9. The time available to create and exploit opportunities against adaptive threats is usually limited. Agile units rapidly recognize an opportunity and take action to exploit it. Speed of recognition, decision making, movement, and battle drills enable agility. During armed conflict, this often requires units to change their location and disposition rapidly. Units must be able to employ capabilities and then rapidly task-organize them again for movement or new tasks while remaining dispersed for survivability. C2 and sustainment nodes must maintain a level of functionality on the move and be able to rapidly emplace and displace in order to reduce the probability of enemy detection. Nodes that are critical to success and susceptible to enemy detection and destruction are most vulnerable, and they must be the most agile.
3-10. Below the threshold of armed conflict, security force assistance teams and forward-stationed and rotational forces provide agility to the CCDR because they are able to perform a wide variety of missions and create options for the combatant command. These forces expand situational awareness through their presence and access to key land areas and populations. Their influence assures allies and partners, and they improve interoperability and agility of the multinational force.
3-11. Agility helps leaders influence tempo. Tempo is the relative speed and rhythm of military operations over time with respect to the enemy (ADP 3-0). It implies the ability to understand, decide, act, assess, and adapt. During competition, commanders act quickly to control events and deny enemy forces relative advantages. By acting faster than the situation deteriorates, commanders can change the dynamics of a crisis and restore favorable conditions. During armed conflict, commanders normally seek to maintain a higher tempo than enemy forces do. A rapid tempo can overwhelm an enemy force’s ability to counter friendly actions, and it can enable friendly forces to exploit a short window of opportunity.
CONVERGENCE
3-12. Convergence is an outcome created by the concerted employment of capabilities from multiple domains and echelons against combinations of decisive points in any domain to create effects against a system, formation, decision maker, or in a specific geographic area. Its utility derives from understanding the interdependent relationships among capabilities from different domains and combining those capabilities in surprising, effective tactics that accrue advantages over time. When combined, the complementary and reinforcing nature of each friendly capability presents multiple dilemmas for enemy forces and produces an overall effect that is greater than the sum of each individual effect. The greater degree to which forces achieve convergence and sustain it over time the more favorable the outcome.
3-13. Convergence occurs when a higher echelon and its subordinate echelons create effects from and in multiple domains in ways that defeat or disrupt enemy forces long enough for friendly forces to effectively exploit the opportunity. Convergence broadens the scope of mass, synchronization, and combined arms, by applying combat power to combinations of decisive points, instead of just one, across time, space, and domains. Convergence is a way to balance the principles of mass, objective, and economy of force, massing combat power on some parts of the enemy force while employing different techniques against other decisive points to create cumulative effects the enemy cannot overcome.
3-14. Convergence requires the synchronization of specific targets and broad objectives by the senior tactical echelon below the land component command. The degree to which a formation achieves convergence in an operation depends on how well leaders are able to—
Develop an understanding of the enemy system, its capabilities, requirements, decision processes, and vulnerabilities through effective surveillance that provides mixed, redundant, and overlapping coverage.
Determine the desired overall effect or opportunity and the individual effects and objectives that precipitate the opportunity.
Integrate Army and joint capabilities at the echelons where they are most effective.
Consider all domains and redundant methods of attack to increase the probability of success.
Synchronize the employment of each capability and echelon to generate simultaneous, sequential, and enduring effects against the enemy system.
Assess the individual effects and the probability that the desired overall effect has been achieved. Commanders prepare to re-attack or adapt a course of action if the desired effect is not achieved, or if other opportunities emerge.
Assume risk and rapidly exploit the opportunities convergence provides.
(See figure 3-1 for a simplified illustration of convergence. See JP 3-60 for more information about targeting.)

3-15. Convergence requires the integration of the capabilities at the echelons where their employment is most effective. Integration is the arrangement of military forces and their actions to create a force that operates by engaging as a whole (JP 1, Volume 1). Commanders generally integrate Army capabilities through task organization and support relationships. Commanders allocate the employment of joint capabilities to subordinate echelons; integrating these capabilities requires an understanding of joint processes. The degree to which commanders effectively integrate joint and Army capabilities at all echelons directly influences success during operations.
3-16. Military forces comprise a wide variety of components that leaders must arrange into a coherent and effective whole. Army leaders integrate—
Joint capabilities.
Multinational, interagency, and interorganizational capabilities.
Echelons and staffs.
Different types of units to achieve a combined arms approach.
3-17. Almost every leader activity, in some way, orients on integrating parts of the force to achieve unity of purpose and unity of effort. There are many intellectual tools leaders use to facilitate integration. Common ones include—
The joint and Army targeting processes (which includes working groups, boards, and other activities to help integrate joint intelligence, surveillance, and reconnaissance [ISR] and fires).
Mission analysis to integrate the activities of multiple staff proponents.
The nesting concept advocated for in the mission command approach to C2 that helps lower echelons integrate their purpose with higher echelons.
Reception, staging, onward movement, and integration (RSOI) for new forces entering an operation.
Engagement area development to integrate all weapons systems into a defense.
3-18. Once leaders have integrated the right capabilities, they must synchronize their employment and effects. Synchronization is the arrangement of military actions in time, space, and purpose to produce maximum relative combat power at a decisive place and time (JP 2-0).
3-19. Understanding the following factors enables leaders to determine when to initiate employment of a capability and how to adapt to changes in the operational environment during execution:
The desired overall effect over time.
How the individual effects complement each other over time.
The time it takes each capability or formation to generate its individual effects from the start of employment.
Whether each individual effect is enduring, simultaneous, or sequenced with the other effects.
The consequences of an individual effect not occurring at the planned time.
3-20. Individual effects can be enduring, simultaneous, or sequential. Enduring effects provide a continuous impact on the threat until they are no longer necessary. Enduring effects can have a debilitating effect on enemy forces, but they may require significant resources to sustain. Simultaneity is the execution of related and mutually supporting tasks at the same time across multiple locations and domains (ADP 3-0). Simultaneous effects, the result of attacking enemy forces in multiple domains at the same time and across the depth of the enemy’s echelons, can have a paralyzing effect on enemy decision making and the effectiveness of the enemy’s most critical systems for a limited period of time. They can degrade enemy reactions and facilitate the path to eventual culmination and defeat. Sequencing effects against a threat can create successive dilemmas and opportunities for deception when enemy forces begin to expect a pattern.
3-21. Leaders synchronize actions and effects through C2 and the operations process. The mission, commander’s intent, and concept of operations form the basis for detailed synchronization. Commanders determine the degree of control necessary to synchronize operations. They balance synchronization with agility and initiative, but they never surrender the initiative for the sake of synchronization. Excessive synchronization can lead to too much control, which limits the initiative of subordinates and undermines mission command.
3-22. Achieving convergence requires detailed, centralized planning and mission orders that enable decentralized execution. Redundant and resilient communications enable synchronized action. However, leaders must anticipate degraded communications and be prepared to rely on mission orders, accept risk, and make decisions to accomplish the mission. During execution, leaders seek to maintain the conditions of convergence through rapid transitions, adjusting priorities, shifting the main effort, or adapting to maintain momentum. Longer periods of convergence allow for greater opportunities to expand advantages and achieve objectives.
3-23. Leaders must understand the various processes for requesting joint capabilities and integrating them with ground maneuver. Air, space, and cyberspace tasking cycles operate on different time horizons and have different requirements for requesting effects. These cycles may vary depending on the theater and the situation. Whenever possible, leaders anticipate requirements for these effects during planning and provide ample time for the joint force to generate them. Leaders may request effects on shorter timelines, but they should not make them essential to mission success.
3-24. During competition, the theater army establishes conditions for convergence that enable deterrence, provide options during crisis, and enable success at the outset of armed conflict. Intelligence, sustainment, positioning of forces, and other activities to set the theater facilitate situational understanding, decision making, integration, and synchronization during armed conflict. The theater army requests cyberspace and space effects through the combatant command to ensure there is enough time to integrate and synchronize these capabilities. The theater army balances the use of these capabilities during competition with the need to preserve them for use by Army formations during crisis or armed conflict. When armed conflict occurs in a theater, the theater army continues to facilitate convergence by providing capabilities to the land component command and shaping the operational environment outside the joint operational area.
3-25. During armed conflict, the land component command apportions joint capabilities to subordinate echelons. Corps integrate joint capabilities with ground maneuver at the appropriate echelon where forces employ them to achieve convergence and achieve objectives. The advantages provided by maritime, air, space, and cyberspace capabilities will not be available all the time, so tactical echelons must be ready to exploit their effects when generated. (See FM 3-14 for more information on space effects. See FM 3-12 for more information on cyberspace effects.)
3-26. Convergence is most effective when its effects accrue and create a cycle of expanding opportunity. Employing multiple and redundant methods of attack increases the probability of success by avoiding dependence on a single method of detecting, tracking, and attacking. Success causes enemy forces to react and activate more of their capabilities, creating another opportunity in one or more domains. The corps and its subordinate echelons align their operations on land with the opportunities created by the effects generated by the other components of the joint force, preserving combat power to maximize their ability to exploit the opportunities convergence presents.
ENDURANCE
3-27. Endurance is the ability to persevere over time throughout the depth of an operational environment. Endurance enhances the ability to project combat power and extends operational reach. Endurance is about resilience and preserving combat power while continuing operations for as long as is necessary to achieve the desired outcome. During competition, Army forces improve endurance by setting the theater across all warfighting functions and improving interoperability with allies and other unified action partners.
3-28. Endurance reflects the ability to employ combat power anywhere for protracted periods in all conditions, including environments with degraded communications, chemical, biological, radiological, and nuclear (CBRN) contamination, and high casualties. Endurance stems from the ability to organize, protect, and sustain a force, regardless of the distance from its support area and the austerity of the environment. Endurance involves anticipating requirements and making the most effective and efficient use of resources.
3-29. As forces fight through successive engagements, maintaining mutual support among units helps prevent them becoming isolated, being defeated in detail, and culminating early. Protection prevents or mitigates enemy effects and preserves combat power, postponing culmination and prolonging effective operations. One way Army forces preserve combat power is by maintaining dispersion to the greatest degree possible. Leaders can mass combat power from dispersed positions and generate the desired effects without concentrating forces any more than is necessary. During operations, commanders and staffs integrate, synchronize, and simultaneously apply protection capabilities.
3-30. Leadership and tactics contribute to endurance. Plans that allow for different units to be the main effort using follow and support or follow and assume techniques prevent early culmination in the units first committed to close combat. Realistically determining what tempo friendly forces can maintain given enemy resistance, weather, and physical distances and the impact they have on Soldiers, leaders, and equipment increases endurance over time. Schemes of maneuver that avoid enemy strengths and preserve combat power are less likely to negatively affect morale.
3-31. Sustainment operations are essential to endurance. Using all methods for continuously delivering sustainment through land, maritime, and air capabilities improves endurance. When possible, sustainment units employ a space- and cyberspace-enabled communications network to transmit sustainment requirements and coordinate the delivery of materiel or services. However, leaders must anticipate degraded communications and combine analog systems for communication with predictive analysis and disciplined initiative to ensure commanders can maintain acceptable tempo for as long as necessary.
DEPTH
3-32. Depth is the extension of operations in time, space, or purpose to achieve definitive results (ADP 3-0). While the focus of endurance is on friendly combat power, the focus of depth is on enemy locations and dispositions across all domains. Commanders achieve depth by understanding the strengths and vulnerabilities of the enemy’s echeloned capabilities, then attacking them throughout their dispositions in simultaneous and sequential fashion. Although simultaneous attacks through all domains in depth are not possible in every situation, leaders seek to expand their advantages and limit enemy opportunities for sanctuary and regeneration. Leaders describe the depth they can achieve in terms of operational reach.
3-33. Operational reach is the distance and duration across which a force can successfully employ military capabilities (JP 3-0). Staffs assess operational reach based on available sustainment, the range of capabilities and formations, and courses of action compared with the intelligence estimates of enemy capabilities and courses of action. This analysis helps the commander understand the limits on friendly operations, the risks inherent in the mission, and likely points in time and space for transitions.
3-34. Below the threshold of armed conflict, the theater army creates depth by improving the infrastructure for force projection and by improving interoperability with multinational forces to the degree required by operation plans (OPLANs) and contingency operations. It also adds depth to its operations by expanding influence with allies and partners, populations, and other relevant actors through joint exercises, sustained forward positioning of advisor teams, and forward basing of combat formations.
3-35. During armed conflict, the JFLCC creates depth by facilitating access to Army and other joint capabilities, especially space and cyberspace capabilities that improve the protection of tactical formations and degrade enemy integrated air defense systems. The JFLCC also requests that the JFC influence the extended deep area in support of land operations. The corps directs fires into its deep area to defeat enemy long-range fires, disrupt enemy sustainment and C2, separate maneuver echelons, and shape the success of future close operations. Special operations forces operating in the extended deep area can detect targets and enable the employment of joint fires to support conventional operations.
3-36. Leaders enhance the depth of their operations by orchestrating effects in one dimension to amplify effects in the others. For example, a commander might decide to destroy an elite enemy formation first because it undermines the confidence of the enemy’s other units. Commanders exploit this through information activities to reduce the will of other enemy forces to fight.
IMPERATIVES
3-37. Imperatives are actions Army forces must take to defeat enemy forces and achieve objectives at acceptable cost. They are informed by the operational environment and the characteristics of the most capable threats Army forces can encounter. Imperatives include—
See yourself, see the enemy, and understand the operational environment.
Account for being under constant observation and all forms of enemy contact.
Create and exploit relative physical, information, and human advantages in pursuit of decision dominance.
Make initial contact with the smallest element possible.
Impose multiple dilemmas on the enemy.
Anticipate, plan, and execute transitions.
Designate, weight, and sustain the main effort.
Consolidate gains continuously.
Understand and manage the effects of operations on units and Soldiers.
SEE YOURSELF, SEE THE ENEMY, AND UNDERSTAND THE OPERATIONAL ENVIRONMENT
3-38. Commanders visualize operational environments in terms of the factors that are relevant to decision making. Operational environments are dynamic and contain vast amounts of information that can overload C2 systems and impede decision making. Commanders simplify information collection, analysis, and decision making by focusing on how they see themselves, see the enemy, and understand the operational environment. These three categories of factors are interrelated, and leaders must understand how each one relates to the others in the current context.
3-39. As part of the operations process, Army leaders use different methodologies to understand and weigh options. These methodologies include the Army design methodology, the military decision-making process, and the rapid decision-making and synchronization process. Each methodology provides a process that allows commanders and staffs to see themselves, see the enemy, and understand the operational environment. (See ADP 5-0 and FM 5-0 for more information on Army planning methodologies.)
3-40. Commanders develop an understanding of their forces relative to mission requirements, enemy capabilities, and impacts from the operational environment. This understanding helps to inform current and potential future advantages relative to enemy forces, allowing staffs to develop and adapt courses of action that exploit advantages and mitigate disadvantages. Commanders and staffs maintain this understanding of their forces through running estimates, subordinate commander updates, and friendly forces information requirements (known as FFIRs): A friendly force information requirement is information the commander and staff need to understand the status of friendly force and supporting capabilities (JP 3-0). Friendly force information requirements identify the information the commander considers most important to make critical decisions during the execution of operations. The operations officer manages friendly force information requirements for the commander.
3-41. Leaders attempt to see themselves from the enemy perspective, in part by understanding essential elements of friendly information. An essential element of friendly information is a critical aspect of a friendly operation that, if known by a threat would subsequently compromise, lead to failure, or limit success of the operation and therefore should be protected from enemy detection (ADP 6-0).
3-42. Leaders see their formation in relation to their mission and in the broader context of the higher command, adjacent unit, and all domains. Part of “seeing yourself” is understanding how land-based operations enable operations in the other domains, and how capabilities from all domains can enable operations on land. (See paragraphs 2-66 through 2-67 for a discussion of joint interdependence.)
3-43. Commanders see the enemy in terms of its combat power, advantages, and intentions within the operational environment and broader strategic context. Commanders develop their understanding of enemy forces from their individual knowledge, experience, and judgment honed through self-study, training, and education. From this base of knowledge commanders and staffs build shared understanding of enemy forces and environment through intelligence preparation of the battlefield. Intelligence preparation of the battlefield is the systematic process of analyzing the mission variables of enemy, terrain, weather, and civil considerations in an area of interest to determine their effect on operations (ATP 2-01.3).
3-44. Intelligence preparation of the battlefield provides commanders with awareness of information gaps about enemy forces and the operational environment. Staffs translate these gaps into information requirements and assist the commander in determining priority intelligence requirements. A priority intelligence requirement is the intelligence component of commander’s critical information requirements used to focus the employment of limited intelligence assets and resources against competing demands for intelligence support (JP 2-0). More importantly, priority intelligence requirements (known as PIRs) identify information about the threat and operational environment that a commander considers most important to making decisions in a specific context. Intelligence about civil considerations may be as critical as intelligence about enemy forces in some cases. The intelligence officer, in coordination with the rest of the staff, manages priority intelligence requirements for the commander.
3-45. Enemy forces attempt to hide from, deceive, disrupt, and deny friendly collection efforts to prevent friendly forces from perceiving the enemy’s true intentions. This requires commanders plan to develop the situation through action and fight for information. Information collection operations may require the commander to assume significant risk to determine enemy dispositions and anticipate enemy intentions.
3-46. Leaders do not limit their understanding of the enemy to those forces in their assigned area. Enemy forces are capable of employing capabilities from great distances and multiple domains. Leaders must be aware of those capabilities so they can take appropriate action. (See paragraphs 3-75 through 3-79 for more information on making enemy contact.)
3-47. Leaders view the operational environment in terms of domains, dimensions, operational variables, and mission variables that are relevant to their decisions. The most difficult aspect of an operational environment to understand is how the different factors interact to affect operations.
3-48. Understanding is, in the context of decision making, knowledge that has been synthesized and had judgment applied to comprehend the situation’s inner relationships, enable decision making, and drive action (ADP 6-0). Understanding is judgment applied to knowledge in the context of a particular situation. Understanding is knowing enough about a situation to make an informed decision. Judgment is based on experience, expertise, and intuition—and it informs what decision to make.
3-49. Successful operations demand timely and effective decisions based on the information available. As such, commanders and staffs seek to build and maintain situational understanding throughout an operation. Situational understanding is the product of applying analysis and judgment to relevant information to determine the relationships among the operational and mission variables (ADP 6-0). Situational understanding allows commanders to make effective decisions and enables commanders and staffs to assess operations accurately. Commanders and staffs continually strive to maintain their situational understanding and work through periods of uncertainty, accepting that they cannot eliminate them. They train their staffs and subordinates to function in uncertain environments.
3-50. A critical challenge for commanders, staffs, and unified action partners is creating common understanding of an operational environment, an operation’s purpose, its challenges, and the approaches to solving those problems. Shared understanding of the situation, which requires effective flow of information between echelons, forms the basis for unity of effort and subordinate initiative.
3-51. Effective decentralized execution depends on shared understanding. Shared understanding starts with Army doctrine and leader development that instill a common approach to the conduct of operations, a common professional language, and a common understanding of the principles of mission command. It is this shared understanding that allows even hastily task-organized units to operate effectively. Commanders and staffs actively create shared understanding throughout the operations process (of planning, preparation, execution, and assessment). They collaboratively frame an operational environment and its problems, and then they visualize approaches to solving those problems. (See ADP 6-0 for a more detailed description of shared understanding.)
3-52. A common operational picture (COP) is key to achieving and maintaining shared situational understanding in all domains and making effective decisions faster than the threat. The common operational picture is a display of relevant information within a commander’s area of interest tailored to the user’s requirements and based on common data and information shared by more than one command (ADP 6-0). Although the COP is ideally a single display, it may include more than one display and information in other forms, such as graphic representations or written reports.
3-53. The COP facilitates collaborative planning and helps commanders at all echelons achieve shared situational understanding. The COP must account for relevant factors in domains affecting the operation, and it provides and enables a common understanding of the interrelationships between actions and effects through the physical, information, and human dimensions. Shared situational understanding allows commanders to visualize the effects of their decisions on other elements of the force and the overall operation.
3-54. Command posts draw on a common set of shared and relevant information to create a digital COP. Units always maintain an analog COP in the event that the digital COP is compromised. During large-scale combat operations, communications are likely to be degraded or denied during the course of operations. Army forces maintain shared situational understanding by updating physical maps and graphics, and using rehearsed and reliable primary, alternate, contingency, and emergency (known as PACE) communication plans. Command posts are typically responsible for maintaining the digital and analog COP. Units develop standard operating procedures (known as SOPs), reporting timelines, and battle rhythm events to ensure the COP is accurate, relevant, and current.
3-55. The difficulty of maintaining a COP in a multinational environment varies based on training level, language differences, level of data sharing, technical compatibility of systems, restrictions based on classification, and other national caveats. Unified action partners may not have the technical capability or compatible systems to create and share a digital COP. Commanders must recognize and plan for this possibility by using alternate methods, such as liaison officers, messengers, and voice communication.
ACCOUNT FOR BEING UNDER CONSTANT OBSERVATION AND ALL FORMS OF ENEMY CONTACT
3-56. Air, space, and cyberspace capabilities increase the likelihood that threat forces can gain and maintain continuous visual and electromagnetic contact with Army forces. Enemy forces possess a wide range of space-, air-, maritime-, and land-based ISR capabilities that can detect U.S. forces. Leaders must assume they are under constant observation from one or more domains and continuously ensure they are not providing lucrative targets for the enemy to attack.
3-57. Leaders consider nine forms of contact in multiple domains. They are—
Direct: interactions from line-of-sight weapon systems (including small arms, heavy machine guns, and antitank missiles).
Indirect: interactions from non-line-of-sight weapons systems (including cannon artillery, mortars, and rockets).
Non-hostile: neutral interactions that may degrade or compromise military operations (including civilians on the battlefield).
Obstacle: interactions from friendly, enemy, and natural obstacles (including minefields and rivers).
CBRN: interactions from friendly, enemy, and civilian CBRN effects (including chemical attacks, nuclear attacks, industrial accidents, and toxic or hazardous industrial materials).
Aerial: interactions from air-based combat platforms (including attack helicopters, armed unmanned aircraft systems [UASs], air interdiction, and close air support).
Visual: interactions from acquisition via the human eye, optical, or electro-optical systems (including ground reconnaissance, telescopic, thermal, and infrared sights on weapons and sensor platforms such as unmanned aircraft systems and satellites).
Electromagnetic: interactions via systems used to acquire, degrade, or destroy using select portions of the electromagnetic spectrum (including radar, jamming, cyberspace, space, and electromagnetic systems).
Influence: interactions through the information dimension intended to shape the perceptions, behaviors, and decision making of people relative to a policy or military objective (including through social media, telecommunications, human interaction, and other forms of communication).
3-58. In all contexts, direct, indirect, non-hostile, CBRN, and aerial contacts are sporadic. However, Army forces are typically in continuous visual, electromagnetic, and influence contact with adversaries. Army forces are under persistent visual surveillance by space and other capabilities. Army forces and individuals are in constant electromagnetic contact with adversaries who persistently probe and disrupt individual, group, and Army capabilities dependent on space and cyberspace. Army forces are subject to adversary influence through disinformation campaigns targeting Soldiers and their family and friends through social media and other platforms.
3-59. During competition, adversary forces employ multiple methods of collecting on friendly forces to develop an understanding of U.S. capabilities, readiness status, and intentions. They do this in and outside the continental United States. They co-opt civilians and employ space-based surveillance platforms to observe unit training and deployment activities. They also penetrate networks and gain access to individual and group cyberspace personas to create options for future intimidation, coercion, and attack. Soldiers and their families should use telecommunications, the internet, and social media in ways that do not make them or their units vulnerable to adversary surveillance.
3-60. During armed conflict, enemy networked land-, maritime-, air-, and space-based capabilities enable threats to detect and rapidly target friendly forces with fires. Forces that are concentrated and static are easy for enemy forces to detect and destroy. Dispersing forces has multiple survivability benefits. It increases opportunities to use cover and concealment to reduce probability of detection. In the event the enemy detects elements of the friendly force, dispersion acts as a form of deception, helping to conceal the intentions of the friendly force. Leaders only concentrate forces when necessary and balance the survivability benefits of dispersion with the negative impacts dispersion has on mission effectiveness. In addition to dispersion, leaders integrate and synchronize deception, operations security, and other actions to thwart enemy detection efforts. (See JP 3-13.3 and ATP 3-13.3 for detailed information on operations security. See FM 3-13.4 for more information on deception.)
3-61. Command posts are extremely vulnerable to detection from air and space, as well as in the electromagnetic spectrum. Army forces must ensure their command posts are difficult to detect, dispersed to prevent a single strike from destroying more than one node, and rapidly displaceable. Once a command post is detected it has only a few minutes to displace far enough to avoid enemy indirect fire effects. Leaders should focus command posts on the minimum functions necessary to retain their mobility and do everything possible to avoid detection. When the risk of enemy fires is high, commanders consider making their operations more decentralized, dispersing command post nodes into smaller component nodes, and greater dispersion of electromagnetic signatures. Use of existing hardened structures and restrictive terrain to conceal headquarters equipment and vehicles, instead of tents organized in standard configurations, are options commanders have to improve command post survivability.
3-62. Enemy forces possess a wide range of space-, air-, maritime-, and land-based reconnaissance and surveillance capabilities that can detect U.S. forces. To counter these robust and persistent capabilities requires counterintelligence efforts and the disciplined application of operations security.
3-63. Enemy forces employ UASs in large numbers and with a diverse array of capabilities. Leaders account for enemy capabilities and likely reconnaissance objectives as they develop their counter-UAS plan. Leaders implement techniques and procedures for countering enemy UASs based on their organic capabilities, attached capabilities, and the mission variables.
3-64. Leaders combine multiple measures, including deception, to make it more difficult for enemy forces to detect friendly forces. These measures include—
Counterreconnaissance, including counter-UAS operations.
Cover and concealment, both natural and manmade.
False battle positions and deception obstacles.
Obscuration.
Dispersion.
Noise and light discipline.
Limited visibility operations, particularly for sustainment functions and large unit movements.
Electromagnetic emission control and masking, to include social media and personal communication discipline.
3-65. Because Army forces employ an increasing number of capabilities that emit electromagnetic radiation that enemies can target, leaders must apply emission control measures, balancing the risks to the force with the risks to the mission. As risk to the force increases, leaders increase their emission control measures. There may be times that the risk of friendly emissions being detected and targeted is assessed as too high, causing Army forces to use methods of communications with no electromagnetic signature. Understanding threat systems, their capabilities, and their disposition supports effective planning and the execution of emission control measures including—
Minimizing length and frequency of radio transmissions.
Dispersing formations and command posts.
Using lowest effective power settings.
Establishing and enforcing the primary, alternate, contingency, and emergency communication plan.
Using remote antennas.
Using brevity codes, pro-word execution matrices, and communications windows.
Using secure landlines.
Using directional antennas.
Using data-burst transmissions.
Using proper encryption and equipment configuration.
Moving command posts and formations.
Masking emissions using terrain and manmade structures.
Recognizing and reporting jamming of Global Positioning System, radar, and satellite communications.
Employing deceptive emitters.
3-66. Leader efforts to preempt and mitigate enemy detection are essential, but they cannot eliminate the risk of enemy massed and precision fires, including CBRN and weapons of mass destruction. To improve survivability from enemy indirect fires, Army forces maintain dispersion and remain as mobile as possible to avoid presenting themselves as lucrative targets to the enemy’s most capable systems. When mission demands require units to remain static for more than short periods of time, those units must dig in to increase survivability. (See ATP 3-37.34 for information on survivability positions.)
3-67. Commanders have options for achieving dispersion. At the operational level, commanders maintain dispersion by employing multiple staging areas and multiple lines of communications. At the tactical level, commanders maintain dispersion by increasing the distance between subordinate formations and among the elements in those formations. In the attack, they use multiple routes and longer march intervals between formations to the objective and only concentrate forces enough to mass effects or generate favorable force ratios during close combat. In the defense, forces occupy areas away from prepared defensive positions until contact is imminent to prevent their detection and destruction by enemy deep fires. Defending forces also maximize dispersion by using terrain and employing the maximum supporting ranges and distances within acceptable risk criteria.
3-68. When concentrating forces is unavoidable or necessary, units remain concentrated at the lowest level and for the shortest time possible and then rapidly disperse. When the desired level of dispersion is not achievable, commanders place greater emphasis on imposing multiple, simultaneous dilemmas on enemy forces as they move within range of enemy weapons systems. This can reduce the risk of enemy forces efficiently massing their effects. Commanders also use speed and violence of action when dispersion is not possible to minimize exposure in high-risk areas.
During the six-week war, Azerbaijan exploited its technological advantage with lethal efficiency against Armenian forces. Azerbaijan used its UASs, in conjunction with Israeli loiter munitions and modified old Soviet AN-2 planes, to defeat Armenia’s older air defense systems. Azerbaijani forces flew the remotely piloted AN-2s to trigger engagements from Armenia’s air defense systems, while Azerbaijan’s UASs and loiter munitions remained at higher altitudes undetected or out of range. When the air defense systems engaged targets, Azerbaijan pinpointed the air defense systems locations and destroyed those systems with UASs, loiter munitions, or indirect fires. Azerbaijan’s tactics caused Armenia’s air defense network to collapse, and Azerbaijan gained local air superiority over the battlefield.
With air superiority, Azerbaijan placed Armenian forces under continuous surveillance with its UASs. In addition, Azerbaijani forces had infiltrated special operations forces to conduct surveillance of Armenian positions. Armenian forces were unable to remain hidden, and Azerbaijan began destroying Armenian tanks, artillery, and vehicles at a significant rate. Although battle damage assessments vary, multiple sources reported that Azerbaijan destroyed hundreds of Armenian tanks, armored fighting vehicles, artillery systems, multiple launch rocket systems, and air defense systems. The inability to hide and fear of destruction had a demoralizing effect on Armenian soldiers.
CREATE AND EXPLOIT RELATIVE PHYSICAL, INFORMATION, AND HUMAN ADVANTAGES IN PURSUIT OF DECISION DOMINANCE
3-69. The employment of lethal force is based on the premise that destruction and other physical consequences compels enemy forces to change their decision making and behavior, ultimately accepting defeat. The type, amount, and ways in which lethal force compels enemy forces varies, and this depends heavily on enemy forces, their capabilities, goals, and the will of relevant populations. Understanding the relationship between physical, information, and human factors enables leaders to take advantage of every opportunity and limit the negative effects of undesirable and unintended consequences.
3-70. Actions taken focused on one dimension can create advantages in the other dimensions. The physical dimension dominates tactical actions and the employment of destructive force to compel an outcome. Physical actions, particularly the employment of violence, usually generate cognitive effects in the human dimension. Information dimension factors inform and reflect the interaction between human and physical factors. The information dimension deals with how relevant actors and populations communicate what is happening in the physical and human dimensions. The human dimension is where perceptions, decision making, and behavior is determined, and is therefore the dimension that ultimately determines human will. Commanders combine, reinforce, and exploit advantages through all the dimensions, expanding them as they accrue over time. (See Chapter 1 for more information about physical, information, and human advantages.)
3-71. During competition and crisis, Army forces set conditions for armed conflict and physically exhibit combat readiness through training and exercises which is communicated by various means to create a deterrent effect in the human dimension. During armed conflict, tactical leaders typically focus on generating physical advantages and the immediate physical and cognitive effects they produce. However, leaders maintain awareness of the overall purpose of physical effects, ensuring they commit combat power to necessary objectives that produce advantageous results in all dimensions. At the strategic level, leaders focus more heavily on the information and human impacts of physical effects and how to convert them into desirable policy outcomes.
3-72. Successful military operations often depend on a commander’s ability to gain and maintain the operational initiative by achieving decision dominance—a desired state in which a force generates decisions, counters threat information warfare capabilities, strengthens friendly morale and will, and affects threat decision making more effectively than the opponent. Decision dominance requires developing a variety of information advantages relative to that of the threat and then exploiting those advantages to achieve objectives. Commanders employ relevant military capabilities from all warfighting functions to create and exploit decision dominance.
3-73. Decision dominance is aspirational, situationally dependent, and always relative to an opponent. The goal is to understand, decide, and act faster and more effectively than the threat. It is not absolute speed that matters, but speed relative to the threat. Commanders can achieve this by interfering with an enemy force’s C2 while enhancing, protecting, and sustaining their own C2. An advantage need not be large. A small advantage exploited repeatedly can contribute decisively to the success of Army forces. The ability and desire to generate a higher tempo does not mean commanders should act when the situation calls for waiting. The aim is meaningful—not merely rapid—action. A decision to act is meaningful only if the resulting actions by friendly forces create an advantage relative to the threat.
3-74. Adversaries and enemies pursue their own relative advantages, typically in asymmetric ways, while continually attempting to achieve decision dominance over friendly forces. Because threat forces adapt, and situations evolve, decision dominance is relative and transitory. Commanders therefore continuously make assessments to determine which forms of relative advantage are most important to pursue over time.
MAKE INITIAL CONTACT WITH THE SMALLEST ELEMENT POSSIBLE
3-75. Army forces are extremely vulnerable when they do not sufficiently understand the disposition of enemy forces and become decisively engaged on terms favorable to enemy forces. To avoid being surprised and incurring heavy losses, leaders must set conditions for making enemy contact on terms favorable to the friendly force. They anticipate when and where to make enemy contact, the probability and impact of making enemy contact, and actions to take on contact. Quickly applying multiple capabilities against enemy forces while preventing the bulk of the friendly force from being engaged itself requires an understanding of the forms of contact.
3-76. During armed conflict at the tactical level, commanders seek to gain and maintain contact with the enemy using the smallest element possible, enabling rapid development of situational understanding, and using maneuver and fires to attack enemy forces in the most advantageous way. Judicious employment of all available reconnaissance and security capabilities is the most effective way to make direct contact with the smallest possible friendly force. Friendly forces should attempt to make contact with sensors and unmanned systems first, incorporating them into their movement techniques. Employment of UAS and other platforms activates enemy systems and enables their detection without creating risks to manned friendly reconnaissance and maneuver forces. After detecting an enemy capability, Army forces cue intelligence platforms from other domains to improve their understanding of enemy force dispositions and engage those forces on advantageous terms.
3-77. Identifying enemy locations may not provide enough information for Army forces to discern enemy intentions. Commanders develop the situation through action when they deliberately place forces in contact. Small maneuver forces are often the most effective way to compel enemy forces to react and show their intentions. Leaders exercise tactical patience and set conditions for success. They synchronize maneuver with complementary and reinforcing capabilities through the depth of an operational environment to generate situational awareness and detect opportunities to exploit. By combining friendly speed with multiple dilemmas, it is possible to rapidly disintegrate the coherence of an enemy formation before it can effectively respond.
3-78. Using capabilities from multiple domains, such as air and ground, commanders cause threat systems to activate or emit electromagnetic signals that reveal their capabilities and the locations of their critical nodes, such as sensors, shooters, and command posts. During competition, commanders and staffs use this information to improve understanding, update target lists, and refine plans for attacking threat vulnerabilities. By doing this, commanders and staffs set conditions for success during armed conflict.
3-79. There are situations in which it is not advisable to make contact with the smallest possible element. When commanders are confident they have superior forces, have the element of surprise, and know the enemy’s disposition and course of action, they make contact with as much combat power as possible to maximize surprise and shock effect against enemy forces.
IMPOSE MULTIPLE DILEMMAS ON THE ENEMY
3-80. Imposing multiple dilemmas on enemy forces complicates their decision making and forces them to prioritize among competing options. It is a way of seizing the initiative and making enemy forces react to friendly operations. Simultaneous operations encompassing multiple domains—conducted in depth and supported by deception—present enemy forces with multiple dilemmas. Employing capabilities from multiple domains degrades enemy freedom of action, reduces enemy flexibility and endurance, and disrupts enemy plans and coordination. The application of capabilities in complementary and reinforcing ways creates more problems than an enemy commander can solve, which erodes both enemy effectiveness and the will to fight.
3-81. Deception contributes to creating multiple dilemmas, achieving operational surprise, and maintaining the initiative. Deception efforts by tactical formations seek to delay enemy decision making until it is too late to matter, or to cause an enemy commander to make the wrong decision. Deception requires an understanding of how to surprise enemy forces; time to plan, prepare, execute, and assess a deception operation; and the ability to properly resource the deception effort.
3-82. Deception inhibits effective enemy action by increasing the time, space, and resources necessary to understand friendly courses of action. Well-executed deception begins a cumulative effect on enemy decision-making cycles, and it can cause inaction, delay, misallocation of forces, and surprise as enemy forces react to multiple real and false dilemmas. Attempts to mislead enemy forces are fundamental to all courses of action development wherever possible. While commanders and staffs integrate deception as part of course of action development, they take operations security measures to obscure friendly intentions, make enemy forces account for multiple friendly courses of action for as long as possible, and ensure that enemy forces do not become aware of the deception effort. (See JP 3-13.4 and FM 3-13.4 for more information on military deception.)
3-83. Forcible entry operations and envelopments into locations offset from how enemy defenses are oriented can create multiple dilemmas by dislocating enemy forces’ prepared operational approach or exceeding their capability to respond. The capability to project power across operational distances presents enemy forces with difficult decisions about how to array their forces in time and space. Rapid tactical maneuver to exploit a penetration or envelopment defeats enemy attempts to reposition integrated fires networks or integrated air defense systems, which in turn are typically less effective when moving.
3-84. Creating multiple dilemmas requires recognizing exploitable opportunities. Understanding enemy dispositions, systems, and vulnerabilities, and the characteristics of the terrain and population, informs situational understanding and course of action development. Employing mutually supporting forces along different axes to strike from unexpected directions creates dilemmas, particularly when Army and joint forces simultaneously create effects against enemy forces in multiple domains. Commanders seek every opportunity to make enemy forces operate in different directions at the time and locations of their choosing. Commanders are not limited to destructive means for imposing multiple dilemmas on the enemy. For example, they can employ psychological operations and civil affairs capabilities to influence and garner the support of civilian populations. This creates a dilemma for enemy forces who must react and divert resources to counter passive or active resistance.
ANTICIPATE, PLAN, AND EXECUTE TRANSITIONS
3-85. Transitions mark a change of focus in an operation. Leaders plan transitions as part of the initial plan or parts of a branch or sequel. They can be unplanned and cause the force to react to unforeseen circumstances. Transitions can be part of progress towards mission accomplishment, or they can reflect a temporary setback. Common transitions are—
Between competition, crisis, and armed conflict.
Between operations dominated by offense, defense, and stability.
Between types of offense or defense.
Between phases of an operation.
Between branches and sequels of a campaign or major operation.
Between command posts during emplacement, movement, and displacement of one or more nodes.
Shifts of the main effort, supporting effort, and reserve between units.
Task organization changes.
Passing responsibility for enemy units crossing unit or echelon boundaries.
Passing terrain responsibility between units.
Transferring responsibility for security and governance to legitimate authorities.
Change in mission from combat operations to reconstitution.
Moving forces in and out of theater.
Changes in the environment that cause a reframe of the mission or change in the purpose of the operation.
3-86. Transitions are critical planning responsibilities for commanders. They anticipate key transitions and issue planning guidance to their staffs. Staffs in turn suggest to their commanders when transitions may be necessary. Staffs monitor current operations and track conditions that require transition. Transitions are typically points of friction or opportunities, and leaders assign subordinate leaders specific responsibilities wherever transitions occur, for example, during passage of lines, at wet gap crossings, at contact points, and along unit boundaries.
3-87. Effective transitions require planning and preparation well before their execution, so the force can maintain the momentum and tempo of operations. Risks increase during transitions, so commanders establish clear conditions for their execution. Commanders establish decision points to support successful transitions during operations. The ability of echelons below brigade to execute battle drills mitigates some of the risks higher echelons face during transitions.
3-88. A transition occurs for several reasons. An unexpected change in conditions may require commanders to direct an abrupt transition. In such cases, the overall composition of the force remains unchanged despite sudden changes in mission, task organization, and rules of engagement. Typically, task organization evolves to meet changing conditions; however, transition planning must also account for changes in mission. Commanders continuously assess the situation, re-task, re-organize, and cycle their forces in and out of close combat to retain operational initiative. Commanders seek to shift priorities or the main effort without necessitating operational pauses that make friendly forces more vulnerable to enemy action.
3-89. Commanders identify potential transitions during planning and account for them throughout execution. Transition planning and preparation should include—
Forecasting when and how to transition.
Arranging tasks to facilitate transitions.
Creating a task organization that anticipates transitions.
Rehearsing critical transitions, such as the transition from defense to offense.
Ensuring the force understands changes to rules of engagement during mission transitions.
Understanding potential unintended consequences and the risk they pose to successful transition.
3-90. Commanders and staffs account for the time required to plan, prepare, execute, and assess transitions, accounting for likely friction due to the environment, degraded communications, and enemy action. Assessment ensures that commanders measure progress toward such transitions and take appropriate actions to prepare for and execute them.
DESIGNATE, WEIGHT, AND SUSTAIN THE MAIN EFFORT
3-91. Commanders frequently face competing demands for limited resources. They resolve these competing demands by establishing priorities. One way in which commanders establish priorities is by designating, weighting, and sustaining the main effort. The main effort is a designated subordinate unit whose mission at a given point in time is most critical to overall mission success (ADP 3-0). Commanders provide the main effort with the appropriate resources and support necessary for its success. When designating a main effort, commanders consider augmenting a unit’s task organization and giving it priority of resources and support. The commander designates various priorities of support, such as for air and missile defense (AMD), close air support and other fires, information collection, mobility and countermobility, and sustainment. Commanders and staffs anticipate sustainment requirements of the main effort as it shifts throughout the operation, and they position supplies and capabilities according to the situation. Commanders must balance forward positioning of sustainment assets with the need for freedom of action and operational reach when weighting the main effort.
3-92. Commanders shift resources and priorities as circumstances require. While there can be only one main effort at any given time, commanders may shift the main effort several times during an operation to increase the endurance of the overall force. They should allow time for the shift of support priorities prior to designating a unit as the main effort, since shifting the main effort may require movement of resources and the positioning of supporting capabilities.
CONSOLIDATE GAINS CONTINUOUSLY
3-93. Leaders add depth to their operations in terms of time and purpose when they consolidate gains. Commanders consolidate gains at the operational and tactical levels as a strategically informed approach to current operations with the desired political outcome of the conflict in mind. During competition and crisis, commanders expand opportunities created from previous conflicts and activities to sustain enduring U.S. interests, while improving the credibility, readiness, and deterrent effect of Army forces. During large-scale combat operations, commanders consolidate gains continuously or as soon as possible, deciding whether to accept risk with a more moderate tempo during the present mission or in the future as large-scale combat operations conclude. (See paragraphs 6-98 through 6-105 for more information on consolidating gains during armed conflict.)
3-94. The multidomain aspects of an operational environment place increased strain on the ability of military forces to create enduring change, particularly in the human and information dimensions. The size, scale, and scope of an assigned area of operations (AO) may reduce the duration of effects, just as they dilute the potency of combat power. The speed and pervasiveness of enemy disinformation campaigns is a constant challenge that contests Army forces’ ability to change human will and behavior. The need to fix and bypass some enemy forces during operations designed to penetrate or envelop enemy echelons may leave significant enemy threats in rear areas and jeopardize gains made during offensive operations. Commanders therefore continuously assess when and how they will consolidate gains as they develop the situation.
3-95. Consolidating gains at every echelon leads to better transitions out of armed conflict and into post-conflict competition. It serves as a preventative against the rise of an insurgency by those wishing to prolong the conflict.
UNDERSTAND AND MANAGE THE EFFECTS OF OPERATIONS ON UNITS AND SOLDIERS
3-96. Continuous operations rapidly degrade the performance of people and the equipment they employ, particularly during combat. In battle, Soldiers and units are more likely to fail catastrophically than gradually. Commanders and staffs must be alert to small indicators of fatigue, fear, indiscipline, and reduced morale, and they must take measures to deal with these before their cumulative effects drive a unit to the threshold of collapse. Staffs and commanders at higher echelons must take into account the impact of prolonged combat on subordinate units, which causes efficiency to drop, even when physical losses are not great. Leaders consider the isolation Soldiers experience when not being able to remain connected with family and friends via social media and other platforms for extended periods. Well-trained, physically fit Soldiers in cohesive units retain the qualities of tenacity and aggressiveness longer than those who are not.
3-97. Although all units experience peaks and valleys in combat effectiveness, well-trained, cohesive units under effective leaders have increased endurance and higher effectiveness than units that lack training and effective leaders. Leaders develop resilient subordinates. Staffs and commanders need to take this variance in performance into account in their planning by matching units to missions, rotating units through difficult tasks to permit recuperation, and by basing their expectations of a unit’s performance on accurate awareness of its current capabilities. Historically, during conflicts where tactical units are in contact with enemy forces on a continuous basis for weeks or more at a time, commanders and staffs at echelons above brigade rotated subordinate units out of enemy contact to reorganize, rest, and train on a regular basis. Continuously assessing the combat effectiveness of subordinate formations is necessary to inform such decisions in the future.
SECTION III – OPERATIONAL APPROACH AND OPERATIONAL FRAMEWORK
3-98. The operational approach provides the logic for how tactical tasks ultimately achieve the desired end state. It provides a unifying purpose and focus to all operations. Sound operational approaches balance risk and uncertainty with friction and chance. The operational approach provides the basis for detailed planning, allows leaders to establish a logical operational framework, and helps produce an executable order. (See ADP 3-0 for more information on operational art. See ADP 5-0 for more information on planning.)
3-99. An operational framework organizes an area of geographic and operational responsibility for the commander and provides a way to describe the employment of forces. The framework illustrates the relationship between close operations, operations in depth, and other operations in time and space across domains. As a visualization tool, the operational framework bridges the gap between a unit’s conceptual understanding of the environment and its need to generate detailed orders that direct operations.
OPERATIONAL APPROACH
3-100. Through operational art, commanders develop their operational approach—a broad description of the mission, operational concepts, tasks, and actions required to accomplish the mission (JP 5-0). An operational approach is the result of the commander’s visualization of what needs to be done in broad terms to solve identified problems. It is the main idea that informs detailed planning. When describing an operational approach, commanders—
Consider ways to defeat enemy forces in detail and potential decisive points.
Employ combinations of defeat mechanisms to isolate and defeat enemy forces, functions, and capabilities.
Assess options for assuming risk.
DEFEATING ENEMY FORCES IN DETAIL
3-101. Armed conflict implies the need to defeat enemy forces. Defeat is to render a force incapable of achieving its objectives (ADP 3-0). When used as a task or effect in operations, defeat provides maximum flexibility to the commander in how to accomplish the mission. Senior leaders assign defeat as a task when the situation is still developing, or when the commander on the ground, by virtue of experience and proximity to the problem, is uniquely capable of deciding how to employ lethal force to accomplish objectives. As a task, defeat is appropriate for theater strategic and operational-level echelons, but it is often too vague for tactical echelons below corps level, where more specific outcomes or a higher level of destruction might be necessary to ensure the overall defeat of enemy forces. As a purpose or an effect, defeat is often used to describe the ultimate outcome of an operation.
3-102. Defeat inevitably leads to transition. Strategic defeat occurs when an enemy’s political leadership and national will acquiesce to the friendly political will, and the situation transitions to a more desirable form of competition below armed conflict. Operational defeat occurs when enemy forces no longer have the will or ability to pursue military objectives, and the friendly force has achieved most or all of its objectives. At the tactical level, an attacking force defeats an enemy defense when it causes enemy forces to transition to a retrograde and cease defending friendly objectives. A defending force defeats an enemy attack when it causes enemy forces to culminate and transition to the defense before achieving their objectives.
3-103. When U.S. forces possess overwhelming advantages across all domains, the JFC is able to attack all elements of the enemy force with a high degree of simultaneity. Simultaneity disrupts the enemy’s C2 system and rapidly disintegrates each component of the threat warfighting system at the same time. However, peer threats, by definition, possess a scale and quality of warfighting capability that is too extensive to attack at once. When fighting a peer threat, commanders identify weaknesses between enemy units or in enemy formations and warfighting systems that provide opportunities to defeat them in detail.
3-104. Defeat in detail is concentrating overwhelming combat power against separate parts of a force rather than defeating the entire force at once (ADP 3-90). Traditionally, commanders of a smaller force use this technique to achieve success against a larger enemy force. However, defeat in detail also applies to operations that focus effort on a specific enemy function, capability, echelon, domain, or dimension.
3-105. Defeat in detail requires leaders to evaluate enemy forces in the context of all the relevant domains and dimensions of an operational environment. Commanders must understand the various parts of an enemy force and its vulnerabilities, and then discern the best ways to project combat power against those vulnerabilities. By comparing enemy weaknesses to friendly advantages, leaders begin to see opportunities and formulate options. Sometimes enemy vulnerabilities and friendly advantages intersect at a single place and time in a way that is decisive to mission accomplishment. That single place and time is a decisive point— key terrain, key event, critical factor, or function that, when acted upon, enables commanders to gain a marked advantage over an enemy or contribute materially to achieving success (JP 5-0). Decisive points help commanders select clear, conclusive, attainable objectives that directly contribute to achieving an end state through convergence or other means.
DEFEAT AND STABILITY MECHANISMS
3-106. A defeat mechanism is a method through which friendly forces accomplish their mission against enemy opposition (ADP 3-0). Army forces at all echelons commonly use combinations of four defeat mechanisms: destroy, dislocate, disintegrate, and isolate. Applying more than one defeat mechanism simultaneously creates multiple dilemmas for enemy forces and complementary and reinforcing effects not attainable with a single mechanism. Commanders may have an overarching defeat mechanism or combination of mechanisms that accomplish the mission, with supporting defeat mechanisms for components of an enemy formation or warfighting system. Defeat mechanisms can guide subordinate development of tactical tasks, purposes, and effects in their operations, facilitating control and initiative.
3-107. During competition, commanders take actions that set conditions for the future application of defeat mechanisms and demonstrate the capability to impose the defeat mechanisms on enemy forces. These activities include posturing forces, penetrating enemy networks, and conducting exercises with allies and partners.
3-108. Commanders determine the speed and degree to which a defeat mechanism must impact an enemy force or warfighting system. Although rapid defeat is typically desirable, it may be more feasible or acceptable to take a gradual approach to completing a defeat. Rendering an enemy incapable of achieving its objectives does not usually require total annihilation. To determine the degree of impact on the enemy force, commanders consider causing only minor degradation to a threat warfighting system or unit when it is sufficient to prevent the enemy from achieving its objective. This preserves friendly combat power and applies the economy of force principle. In other cases, especially main efforts against determined peer threat forces, commanders typically require a significant portion of an enemy’s force be destroyed.
3-109. When commanders destroy, they apply lethal force against an enemy capability so that it can no longer perform its function. Destroy is a tactical mission task that physically renders an enemy force combatineffective until it is reconstituted. Alternatively, to destroy a combat system is to damage it so badly that it cannot perform any function or be restored to a usable condition without being entirely rebuilt (FM 3-90-1). Destruction and the threat of destruction lie at the core of all the defeat mechanisms and make them more compelling. The other mechanisms work when friendly action has caused enemy forces to face a grim reality: their ability to fight and relative advantages are degraded, and their options are to surrender, withdraw, or be destroyed.
3-110. Dislocate is to employ forces to obtain significant positional advantage in one or more domains, rendering the enemy’s dispositions less valuable, perhaps even irrelevant. Typically, the impact of dislocation increases when the friendly force exploits advantages in multiple domains. Commanders often achieve dislocation through deception and by placing forces in locations where enemy forces do not expect them. Achieving dislocation requires an understanding how enemy forces are oriented and how quickly they can shift. Envelopments and turning movements enable physical dislocation. Deception can create and enhance psychological effects of dislocation.
3-111. Isolate means to separate a force from its sources of support in order to reduce its effectiveness and increase its vulnerability to defeat (ADP 3-0). Isolation can encompass multiple domains and can have both physical and psychological effects detrimental to accomplishing a mission. Isolating an enemy force from the electromagnetic spectrum increases the effects of physical isolation by reducing its ability to communicate and degrading its situational awareness. The ability of an isolated unit to perform its intended mission generally degrades over time, decreasing its ability to interfere with an opposing force’s course of action. When commanders isolate, they deny enemy forces access to capabilities that enable them to maneuver at will in time and space.
3-112. Disintegrate means to disrupt the enemy’s command and control, degrading the synchronization and cohesion of its operations. Disintegration prevents enemy unity of effort and leads to a degradation of the enemy’s capabilities or will to fight. It attacks the cohesion of enemy formations and their ability to employ combined arms approaches and work effectively together. Commanders can achieve disintegration by targeting enemy functions essential to the threat’s ability to act as a whole. They often achieve disintegration by specifically targeting an enemy’s command structure, communications systems, the linkages between them, and the capabilities they control. Disintegration can be achieved through the employment of the other three defeat mechanisms in combination, particularly when directed toward systems like integrated fires commands and integrated air defense systems heavily dependent upon C2 and sensor nodes.
3-113. Cyberspace, space, and electromagnetic warfare capabilities can help disintegrate enemy formations by degrading communications and disrupting the quality of enemy information and decisions. Separating enemy reserves and follow-on echelons from the main body with maneuver forces or fires is a physical way to isolate echelons, achieve favorable force ratios, and destroy those echelons. This in turn disintegrates the coherence of an enemy’s attack or defense. Destroying enemy sustainment capability separates enemy fires and maneuver from fuel and ammunition and delays resupply operations.
3-114. A stability mechanism is the primary method through which friendly forces affect civilians in order to attain conditions that support establishing a lasting, stable peace (ADP 3-0). As with defeat mechanisms, combinations of stability mechanisms produce complementary and reinforcing effects that accomplish the mission more effectively and efficiently than single mechanisms do alone. The four stability mechanisms are compel, control, influence, and support:
Compel means to use, or threaten to use, lethal force to establish control and dominance, affect behavioral change, or enforce compliance with mandates, agreements, or civil authority.
Control involves imposing civil order.
Influence means to alter the opinions, attitudes, and ultimately the behavior of foreign, friendly, neutral, and threat audiences through messages, presence, and actions.
Support establishes, reinforces, or sets conditions necessary for the instruments of national power to function effectively.
RISK
3-115. Commanders accept risk on their own terms to create opportunities and apply judgment to manage those hazards they do not control. Risk is an inherent part of every operation and cannot be avoided. Commanders analyze risk in collaboration with subordinates to help determine what level and type of risk exists and how to mitigate it. When considering how much risk to accept with a course of action, commanders consider risk to the force against the probability of mission success during current and future operations. They assess options in terms of weighting the main effort, economy of force, and physical loss in the context of what they have been tasked to do.
3-116. Leaders consider risk across all domains. Accepting risk in one domain may create opportunities in other domains. For example, the risk of seizing an airfield puts ground forces at risk, but it creates an opportunity to receive reinforcements and supplies that extend operational reach. During combat against an enemy with capabilities comparable to that of the United States, the greatest opportunity may come from the course of action with the most risk. An example of this is committing significant forces to a potentially costly frontal attack that fixes the bulk of enemy forces in place to set the conditions for their envelopment by other forces. Another is taking a difficult but unexpected route to achieve surprise. Accepting significant risk is necessary when seeking to create an advantage where none exists otherwise.
3-117. The unrealistic expectation of avoiding all risk is detrimental to mission accomplishment. While each situation is different, commanders avoid undue caution or commitment of resources to guard against every perceived threat. Waiting for perfect intelligence and synchronization may increase risk or close a window of opportunity. Mission command requires that commanders and subordinates accept risk, exercise initiative, and act decisively, particularly when the outcome is uncertain.
3-118. Commanders determine how to impose risk on enemy forces. Viewing the situation through the enemy’s perspective, commanders seek to create multiple dilemmas and increase the number and severity of hazards with which enemy forces must contend. Leaders consider the human and information factors that govern the manner in which enemy forces assess costs and benefits and calculate risk. Commanders disrupt this risk calculation when they increase perceived costs to enemy forces and reduce the perception of potential benefits. Commanders do this by imposing dilemmas on enemy forces, not based on what a U.S. or allied leader views as a problem, but on what an enemy commander views as detrimental. Some dilemmas are universally accepted as costly, but others are cultural or personal. Commanders rely on military intelligence and experience to develop this level of situational understanding.
STRATEGIC FRAMEWORK
3-119. The strategic framework accounts for factors in the strategic environment and the connection of strategic capabilities to operational- and tactical-level operations. The strategic framework includes four areas:
Strategic support area.
Joint security area.
Extended deep area.
Assigned operational area.
(See figure 3-2 on page 3-23 for a depiction of the operational framework in the context of the strategic framework.)
STRATEGIC SUPPORT AREA
3-120. The strategic support area describes the area extending from a theater of operations to a base in the United States or another CCDR’s area of responsibility. It contains those organizations, lines of communications, and other agencies required to support deployed forces. It also includes the airports and seaports supporting the flow of forces and sustainment into a theater. Finally, a strategic support area may contain key operational capabilities, such as cyberspace assets, that are employed from outside an operational area but create effects inside it. Most friendly nuclear, space, and cyberspace capabilities and important network infrastructure are controlled and located in the strategic support area.
JOINT SECURITY AREA
3-121. A joint security area is a specific area to facilitate protection of joint bases and their connecting lines of communications that support joint operations (JP 3-10). The joint security area (JSA) is inside, or immediately adjacent to, an operational area where significant forces and sustainment from two or more services are positioned to conduct or support operations. Joint security on land includes bases, mission-essential assets, lines of communications, and convoy security. A senior Army commander is often designated with responsibility for joint security operations on land.
3-122. The size of a JSA varies considerably and is highly dependent on the size of the operational area, mission-essential assets, logistics support requirements, threats, or scope of the joint operation. The JSA may be included in, be separate from, or be adjacent to the rear areas of the joint force land component commander. During large-scale combat operations JSAs typically are separate from land component or field army rear areas and associated support areas. (See JP 3-10 for more information on JSAs.)
EXTENDED DEEP AREA
3-123. The extended deep area is comprised of operational and strategic deep areas. These areas typically do not fall within the land component command’s AO, but they are part of its area of interest because enemy capabilities and vulnerabilities in the extended deep area can have significant impacts on the outcomes of operations. Extended deep areas are typically the purview of the joint force headquarters or another combatant command. Typically, the joint force air component command (known as the JFACC) is the supported command in extended deep areas. Army forces may be tasked to support it with long-range precision fires.
3-124. Operational deep areas are generally inside the area of interest and immediately beyond the land component’s initially assigned AO. These areas may or may not be within the boundaries of a joint operations area (JOA) or a theater of operations. Operational deep areas are often beyond the feasible movement of conventional forces without significant support from the joint force.
3-125. Operational deep areas contain enemy supporting formations and capabilities for their main forces. Enemy forces can generate significant combat power from these areas, and the capabilities that reside there are often vital to their conduct of operations. In most campaign designs, operational objectives for friendly forces reside initially in the operational deep area.
3-126. Strategic deep areas are beyond the feasible range of movement for conventional ground forces or policy prohibits their operations. These areas are where the CCDR, other combatant commands, and national agencies can employ strategic intelligence capabilities, joint fires, special operations forces, and space and cyberspace capabilities. Many enemy space, cyberspace, and information warfare capabilities reside in strategic deep areas across international boundaries and outside the JOA, and they often comprise multiple areas of influence. (See figure 3-2 for a depiction of the operational framework.)

OPERATIONAL FRAMEWORK
3-127. The operational framework is a cognitive tool used to assist commanders and staffs in clearly visualizing and describing the application of combat power in time, space, purpose, and resources in the concept of operations (ADP 1-01). Commanders build their operational framework on their assessment of the operational environment, including all domains and dimensions. They may create new models to fit the circumstances, but they generally apply a combination of common models according to doctrine. The three models commonly used to build an operational framework are—
Assigned areas.
Deep, close, and rear operations.
Main effort, supporting effort, and reserve.
Note. Commanders may use any operational framework models they find useful, but they must remain synchronized with their higher echelon headquarters’ operational framework.
ASSIGNED AREAS
3-128. The JFC assigns land forces an operational area within a joint organizational construct. The land component or ARFOR commander subdivides their AO into subordinate assigned areas to best support the desired scheme of maneuver. Commanders assign areas to subordinates based on a range of factors, including the mission, friendly forces available, enemy situation, and terrain. An assigned area that is too large for a unit to effectively control or exceeds a unit’s area of influence increases risk, allows sanctuaries for enemy forces, and limits joint flexibility. An assigned area that is too small constrains maneuver, limits opportunities for dispersion, and creates congested lines of communication. Most operations involve a combination of contiguous and noncontiguous assigned areas. Large areas with small forces typically conduct noncontiguous operations which place greater demands on C2 and sustainment. Commanders retain responsibility for any area not assigned to a subordinate unit. Within their assigned area, units use control measures to assign responsibilities, prevent fratricide, facilitate C2, coordinate fires, control maneuver, and organize operations. To facilitate this integration and synchronization, commanders designate targeting priorities, effects, and timing within their assigned areas. There are three types of assigned areas that a land component or ARFOR commander uses:
Area of operations.
Zone.
Sector.
3-129. An area of operations is an operational area defined by a commander for the land or maritime force commander to accomplish their missions and protect their forces (JP 3-0). An area of operations is defined by its boundaries. Within their AO, units integrate assigned and supporting capabilities, synchronize warfighting functions, and generate combat power against enemy forces to accomplish the mission. Responsibilities for an AO include—
Terrain management.
Information collection, integration, and synchronization.
Civil affairs operations.
Movement control.
Clearance of fires.
Security.
Personnel recovery.
Airspace management.
Minimum-essential stability operations tasks which are—
Establish civil security.
Provide immediate needs (access to food, water, shelter, and medical treatment).
Commanders can add, remove, or adjust AO responsibilities based on the situation and mission variables.
Note. A land AO by definition does not include a volume of airspace to control. Airspace control authorities delegate airspace control to Army commanders based on the situation. All commanders must be prepared to enable or coordinate airspace management. (See JP 3-52 and FM 3-52 for more information on airspace control.)
3-130. A zone is an operational area assigned to a unit in the offense that only has rear and lateral boundaries. The non-bounded side of a zone is open towards enemy forces. A higher echelon headquarters uses fire support coordination and maneuver control measures such as a limit of advance and a coordinated fire line to synchronize its deep operations with those of a subordinate unit. Zones allow higher headquarters to adjust deep operations without having to change unit boundaries. This gives greater flexibility to the higher headquarters for controlling deep operations, allowing subordinate units to focus on close and rear operations. Units treat everything behind the forward line of troops as an AO with its associated responsibilities. Units can subdivide a zone into subordinate AOs, zones, or sectors.
3-131. A sector is an operational area assigned to a unit in the defense that has rear and lateral boundaries and interlocking fires. The non-bounded side of a sector is open towards the enemy. A higher echelon headquarters uses fire support coordination and maneuver control measures such as battle positions and trigger lines to synchronize subordinate units. Higher headquarters are responsible to synchronize employment of combat power forward of the main battle and security areas or coordinated fire line. Higher headquarters use sectors to synchronize and coordinate subordinate force engagement areas and allow for mutually supporting fields of fire, which do not require deconfliction between adjacent units. Units treat everything behind the forward line of troops as an AO with its associated responsibilities. Units can subdivide a sector into subordinate areas of operations, zones, or sectors.
3-132. While there are many other control measures that enable terrain management (for example, position areas for artillery or tactical assembly areas) only AOs, zones, and sectors are part of the assigned area model. Commanders and staffs use AOs when the operation requires a higher level of control. Zones are best for front line units conducting high tempo offensive operations characterized by direct fire contact with the enemy and a fluid forward line of troops. Sectors are best for front line units conducting a defense, making it easier for a higher headquarters to conduct deep operations and for subordinate units to have mutually supporting fires.
3-133. Commanders and staffs consider mutual support when considering how large an area to assign subordinates. Mutual Support is that support which units render each other against an enemy, because of their assigned tasks, their position relative to each other and to the enemy, and their inherent capabilities (JP 3-31). In Army doctrine, mutual support is a planning consideration related to force disposition, not a command relationship. Mutual support has two aspects: supporting range and supporting distance.
3-134. When two units are mutually supporting, their assigned areas are generally contiguous with each other. Units with non-contiguous areas are generally not mutually supporting. Supporting range is the distance one unit may be geographically separated from a second unit yet remain within the maximum range of the second unit’s weapons systems (ADP 3-0). Supporting range depends on available weapons systems, and it is normally the maximum range of the supporting unit’s indirect fire weapons, although certain capabilities employed via space and cyberspace can be used at much longer ranges. Terrain, visibility, and weather may limit the supporting range. If one unit cannot effectively or safely fire in support of another, the first may not be in supporting range even though its weapons have the required range. At higher echelons, communications are also a consideration. If two units cannot effectively coordinate the use of indirect fire, then they may not be considered in supporting range of each other. Figure 3-3 on page 3-26 illustrates a notional corps assigned area with noncontiguous AOs.
3-135. Supporting distance is the distance between two units that can be traveled in time for one to come to the aid of the other and prevent its defeat by an enemy or ensure it regains control of a civil situation (ADP 3-0). These factors affect supporting distance:
Terrain and mobility.
Distance.
Enemy capabilities, including those employed from the space, cyberspace, air, and maritime domains.
Friendly capabilities, including those employed from the space, cyberspace, air, and maritime domains. (See Chapter 6 for a greater discussion of mutual support.)
Note. Contiguous boundaries do not imply units are capable of mutual support or that their subordinate units have contiguous assigned areas. Therefore, mutual support between adjacent units and subordinate units must be part of commander dialogue to ensure the formation is assuming risk deliberately and at the right echelon.

3-136. Operational environments are larger than the associated assigned area. They influence and are influenced by factors outside unit boundaries. To account for these factors commanders typically consider areas of influence and areas of interest relative through all domains and dimensions.
3-137. An area of influence is an area inclusive of and extending beyond an operational area wherein a commander is capable of direct influence by maneuver, fire support, and information normally under the commander’s command or control (JP 3-0). The ranges of a unit’s maneuver and fires capabilities typically define its area of influence; however, commanders consider all forms of contact they can make with enemy forces when visualizing their area of influence. A unit’s area of influence contracts or expands based on the capabilities allocated by the higher headquarters and adjusts as the unit repositions its capabilities on the battlefield. An area of influence is normally larger than its associated assigned area, but it is smaller than its area of interest. Units typically have areas of influence that overlap with adjacent unit assigned areas. A unit might desire to collect information on or strike enemy forces traversing through an adjacent unit assigned area. This situation requires control measures to enable friendly forces to maintain pressure on enemy forces while mitigating the risk of fratricide. Understanding an area of influence helps commanders and staffs plan branches and sequels to the current operation in preparation for operations outside of the current assigned area.
3-138. An area of interest is that area of concern to the commander, including the area of influence, areas adjacent to it, and extending into enemy territory (JP 3-0). This visualization tool enables commanders and staffs to understand the impact of threats outside their assigned area and how their operation is progressing along with their adjacent and higher units. An area of interest includes those aspects of the domains from which enemy forces can employ capabilities that jeopardize the accomplishment of the mission. The area of interest can shift according to the situation. For example, Army forces track the location of enemy AMD, artillery, and armored formations outside the assigned area whose movement or employment may impact current and future operations. The area of interest also includes adjacent and other friendly forces whose actions or inactions of friendly forces could affect operations.
3-139. Commanders consider all forms of contact possible with enemy forces and update their area of interest as the situation develops, including the effects of enemy influence and disinformation. An area of interest surrounds an assigned area, extending forward and to the flanks of the assigned area, and overlapping with adjacent unit assigned areas. Depending on the operation, it may also extend rearwards, especially when enemy forces contest operational and strategic lines of communications. A unit’s area of interest is especially important for helping leaders assess risks and maintain situational awareness of factors that will become important as operations progress. It is particularly important that the area of interest account for human, information, and physical dimension factors across all domains.
DEEP, CLOSE, AND REAR OPERATIONS
3-140. Within assigned areas, commanders organize their operations in terms of time, space, and purpose by synchronizing deep, close, and rear operations. An echelon’s focus in time, space, and purpose—not necessarily their physical location—determines whether they are deep, close, or rear operations. This model assists commanders and staffs in synchronizing capabilities that reside outside of their unit’s assigned area, (for example, from air, space, and cyberspace) with operations inside their assigned areas. The degree of convergence that a corps can achieve to set conditions for its subordinate divisions depends on its ability to synchronize close, deep, and rear operations among its subordinate echelons and with the joint force.
3-141. Divisions and higher echelons typically align their deep, close, and rear operations to corresponding areas, due to the scale of forces and physical considerations involved. This facilitates their C2 of forces spread over wide distances whose physical locations do not correspond to the location and purpose of their effects. Typically, divisions and corps assign command posts to enable control of these areas. For example, a division may position an artillery battery in a position area for artillery located in the rear area but employ its fires in support of close operations. In this case, the rear command post might control the battery’s sustainment and protection, but the division main command post will control its priorities for providing indirect fire support. At brigade echelons and below, differentiating between close, deep, and rear may have less utility during large-scale combat operations because of the high tempo, narrow focus, and short planning horizons. At every echelon, however, commanders must understand the relationship among these operations and their combined impact on mission accomplishment. (See FM 3-94 for more information about deep, close, and rear areas.) Figure 3-4 on page 3-28 illustrates notional corps deep, close, and rear areas for a corps AO with contiguous divisions.
Note. The symmetry of figure 3-4 on page 3-28 provides the simplest way for understanding the operational framework which is a mental model. Applying the model to real situations results in significant variations.

3-142. Deep operations are tactical actions against enemy forces, typically out of direct contact with friendly forces, intended to shape future close operations and protect rear operations. At the operational level, deep operations influence the timing, location, and enemy forces involved in future battles. At the tactical level, deep operations set conditions for success during close operations and subsequent engagements.
3-143. At both the operational and tactical levels, the principal effects of deep operations focus on an enemy force’s freedom of action and the coherence and tempo of their operations. Deep operations strike enemy forces throughout their depth and prevent the effective employment of reserves, C2 nodes, logistics, and long-range fires. Deep operations are inherently joint, since many of the capabilities employed by or in support of Army formations are provided by a joint headquarters or Service component.
3-144. Several activities are typically conducted as part of deep operations. They include—
Deception.
ISR and target acquisition.
Interdiction (by ground or air fires, ground or aerial maneuver, cyberspace forces, special operations forces, or any combination of these).
Long-range fires against enemy integrated air defense systems, sustainment nodes, fires capabilities, and echeloned follow-on maneuver formations.
Electromagnetic warfare.
Offensive cyberspace operations and space operations.
Military information support operations.
3-145. Not all activities focused forward of the line of contact are deep operations. Counterfire, for example, primarily supports close operations, even though the targets attacked may be located at great distances from the forward line of troops.
3-146. Deep operations require detailed planning. Because of the relative scarcity of resources with which to perform these activities, deep operations focus on the enemy vulnerabilities and capabilities most dangerous to the next close operation. Attacks must employ enough combat power to achieve the desired result. This is critical when—as is frequently the case—maintaining momentum in close operations depends on successful prosecution of deep operations.
3-147. Close operations are tactical actions of subordinate maneuver forces and the forces providing immediate support to them, whose purpose is to employ maneuver and fires to close with and destroy enemy forces. Until enemy forces are defeated or destroyed in close operations, they retain the ability to fight and hold ground. At the operational level, close operations comprise the efforts of large tactical units—corps and divisions—to win current battles by closing with and defeating enemy forces after setting favorable terms to do so. At the tactical level, close operations comprise the efforts of smaller tactical units to win current engagements through movement combined with direct and indirect fires while physically in contact with the enemy forces they intend to destroy and defeat. Close operations concentrate overwhelming combat power at the right time and place to create and then exploit windows of opportunity to achieve assigned objectives.
3-148. Close operations include the deep, close, and rear operations of their subordinate maneuver formations. For example, divisions and separate brigades conduct corps close operations. Brigade combat teams (BCTs) are the primary forces conducting division close operations.
3-149. The positioning of assets and capabilities does not determine whether they are part of the close operation. For example, some reconnaissance and target acquisition units, while located forward near the line of contact, may have a purpose that supports deep operations.
3-150. Close operations are inherently lethal because they involve direct fire engagements at relatively short ranges with enemy forces seeking to mass direct, indirect, and aerial fires against friendly forces. Deep and rear operations set conditions for the success of close operations. The measure of success of deep and rear operations is their positive impact on increasing the effectiveness and reducing the cost of close operations.
3-151. Activities are part of close operations if their purpose contributes to defeating committed enemy forces that are or will be in direct physical contact with friendly forces. The activities that comprise close operations include—
Maneuver of subordinate formations (including counterattacks).
Close combat (including offensive and defensive operations).
Indirect fire support (including counterfire, close air support, electromagnetic attack, and offensive space and cyber operations against enemy forces in direct physical contact with friendly forces).
Information collection.
Sustainment support of committed units.
3-152. Rear operations are tactical actions behind major subordinate maneuver forces that facilitate movement, extend operational reach, and maintain desired tempo. This includes continuity of sustainment and C2. Rear operations support close and deep operations. At the operational level, rear operations sustain current operations and prepare for the next phase of the campaign or major operation. These operations are distributed, complex, and continuous. At the tactical level, rear operations enable the desired tempo of combat, assuring that friendly forces have the agility to exploit any opportunity.
3-153. Rear operations typically include five broad activities: positioning and moving reserves; positioning and repositioning aviation, fire support, and AMD units; conducting support area operations; securing sustainment and C2 nodes; and controlling tactical unit movement between the division or corps rear boundary and units conducting close operations. Rear operations typically include efforts that consolidate gains to make conditions created by deep and close operations more permanent. All of these activities compete for limited terrain and lines of communications. Division and corps rear command posts are generally responsible for rear operations.
3-154. There are several considerations for conducting rear operations. They include—
C2.
Information collection activities to detect enemy forces.
Establishment and maintenance of routes.
Terrain management.
Movement control.
Protection of critical friendly capabilities.
Information activities.
Infrastructure repair and improvement.
Defeating bypassed forces and continuing to consolidate gains.
Minimum-essential stability tasks which are—
Establish civil security.
Provide immediate needs (access to food, water, shelter, and medical treatment).
Coordination with host-nation and multinational governmental organizations.
Adjusting to shifts in the unit and subordinate rear boundaries.
Integration of new units into the division or corps.
3-155. Enemy deep operations often target friendly rear operations because they are often both vulnerable and essential to friendly mission success. Commanders commit combat power to protect rear operations, but they balance those requirements against those necessary for successful close and deep operations. Units involved in rear operations must protect themselves using both passive and active measures. Commanders and staffs must continuously reevaluate the possibility of more serious threats to rear operations and develop plans to meet them with minimum disruptions to ongoing close operations.
3-156. Support area operations are a critical part of rear operations. Support area operations are the tactical actions securing lines of communications, bases, and base clusters that enable an echelon’s sustainment and command and control.
3-157. A support area is where units position, employ, and protect base sustainment assets and lines of communications required to sustain, enable, and control operations. Support area operations include sustainment for the echelon and relevant security operations. Support area operations enable the tempo of deep and close operations. Support area operations require detailed planning to coordinate among the various units providing sustainment, protection, and security. A maneuver enhancement brigade or BCT typically provides C2 for support area operations for a division or corps due to the level of security, planning, and integration required.
3-158. Support area operations require detailed planning. Their security is often an economy of force effort. Commanders must balance their need to protect rear operations and tempo with the needs of main effort units committed to close and deep operations.
3-159. Commanders consider several items when conducting support area operations. They include—
Desired tempo.
Enemy maneuver and fires units that threaten current and future support area operations.
Additional forces required to protect the support area.
C2 nodes that will occupy the support area.
Command-support relationships between units in the support area.
Transportation networks (road, rail, inland waterways, and air) into and out of the area.
Protection from enemy indirect fire assets.
Survivability.
Dispersion, terrain management, and defensive responsibilities.
Displacement considerations based upon the overall operation.
Movement control into, through, and out of the support area.
3-160. C2 facilitates the freedom to operate, delegate authority, and lead from any point on the battlefield. Plans are the initial basis for action, but commanders must expect substantial changes in the course of an operation and periods of disrupted communications. Leaders allow their subordinates to react to unanticipated situations through the mission command approach to C2.
3-161. Commanders position command posts where they can best integrate capabilities and synchronize combat power without incurring too much risk from enemy interference. Commanders often position command posts and leaders in locations where they anticipate friction, and which are most vital to mission success. Specific mission requirements will dictate how commanders organize and array their command posts as well as the networks they establish to communicate during the conduct of operations. (See ATP 6-0.5 for a detailed discussion of command posts.)
3-162. Staffing, equipping, and organizational concerns vary among echelons of command. In every case, however, the purpose of C2 is to implement the commander’s will and synchronize operations in pursuit of the unit’s objectives. Army forces are equipped with a variety of command posts, including main command posts, tactical command posts or their equivalents, rear command posts, and mobile command groups. At the corps level and below, every echelon of command has a main command post and a tactical command post. Corps and divisions are also equipped with a rear command post, giving them the flexibility to delegate specific C2 responsibilities to nodes positioned to control deep, close, and rear areas.
MAIN EFFORT, SUPPORTING EFFORT, AND RESERVE
3-163. Commanders designate a subordinate unit as a main effort when its mission at a given point in time is most critical to overall mission success. Commanders weight the main effort with additional combat power. Typically, commanders shift the main effort one or more times during execution. When commanders designate a unit as the main effort, it receives priority of support and resources to maximize combat power. Commanders establish clear priorities of support, and they shift resources and priorities to the main effort as circumstances and the commander’s intent require. The unit that directly accomplishes the mission is usually the main effort when it conducts its mission. Commanders typically designate priority for sustainment to units that they anticipate to be the main effort. This helps maximize the combat power of a unit before it becomes the main effort. Shifting a priority of sustainment to the current main effort might be too late to be effective.
3-164. A supporting effort is a designated subordinate unit with a mission that supports the success of the main effort (ADP 3-0). Commanders resource supporting efforts with the minimum assets necessary to accomplish the mission. Forces often realize success of the main effort through success of supporting efforts. A main effort in an earlier phase can be a supporting effort for a main effort in a later phase.
3-165. A reserve is that portion of a body of troops that is withheld from action at the beginning of an engagement to be available for a decisive movement (ADP 3-90). A reserve is an uncommitted force, and it does not normally have a full suite of combat multipliers available to it until it is committed. It is the echelon’s main effort once it is committed. Commanders constitute a reserve and base the size of the reserve on the level of uncertainty in the current tactical situation. Commanders consider survivability, mobility, and the most likely mission when positioning their reserve. While commanders can assign their reserve a wide variety of tasks, through planning priorities, to perform on commitment, a reserve remains prepared to accomplish other missions. The primary purposes for a reserve are to—
Exploit success.
Counter tactical reverses that threaten the integrity of the friendly force’s operations.
Retain the initiative.
3-166. Once a reserve is committed, units reconstitute a new one whenever possible. When a commander assigns a unit the mission of being the reserve, the commander gives the unit a list of planning priorities. Typically a reserve has no more than three planning priorities because of the time it takes to adequately prepare for each priority.
Chapter 4 - Operations During Competition Below Armed Conflict
This chapter begins with an overview of how the Army contributes to competition below the threshold of armed conflict as part of the joint force. It describes methods employed by adversaries and how Army forces contest adversary activities by supporting combatant command campaign plans and preparing for large-scale combat operations with unified action partners. The chapter concludes by discussing how Army forces consolidate gains and transition to crisis or armed conflict as branches to joint campaigns.
OVERVIEW OF OPERATIONS DURING COMPETITION
4-1. Competition below armed conflict occurs when an adversary’s national interests are incompatible with U.S. interests, and that adversary is willing to actively pursue them short of open armed conflict. While neither side desires, at least initially, to use military force as the primary method to achieve its goal, the adversary is willing to employ national instruments of power, including military force, below the threshold of actual armed conflict to achieve its aims. The resulting tension between the two sides creates potential for violent escalation when one side challenges the status quo.
4-2. Operations during competition are intended to deter malign adversary action, set conditions for armed conflict on favorable terms when deterrence fails, and shape an operational environment with allies and partners in ways that support U.S. strategic interests and policy aims. Theater armies support combatant commanders (CCDRs) as they conduct operations to deter adversaries and achieve national objectives. Their operations, conducted as part of a combatant command campaign plan, are conducted over time and across broad areas without armed conflict. This may include cooperative training, support to local institutions, construction projects, and a range of other activities. In many cases, enduring engagement is necessary, especially given the tendency of adversaries to pursue strategic objectives over long periods of time that do not comport with the shorter political-strategic cycles found in the U.S. or among many of its allies and partners.
4-3. Army forces contribute to conventional deterrence during competition by preparing for armed conflict, including large-scale combat operations. This includes assisting allies and partners to improve their military capabilities and capacity. Preparation for combat operations and demonstrating the interoperability of the U.S. joint force with allies and partners presents the strongest deterrence to adversaries. Deliberate messaging that communicates the will and capability to conduct combat operations can amplify the deterrent effect of physical actions on the ground. Interoperability, coupled with the demonstrated capabilities and capacity of Army forces, reinforces a unified approach to defending mutual interests. Even a small contingent of forward-stationed U.S. Army forces are a challenge to defeat when operating with allies and partners. A force ready for large-scale combat operations contributes to the potency and integration of the other instruments of national power, provides CCDRs capabilities for graduated responses, and enables the Army to help the joint force achieve national strategic objectives through competition rather than armed conflict.
ADVERSARY METHODS DURING COMPETITION
4-4. To effectively plan, prepare, execute, and assess operations during competition requires a broad understanding of the strategic environment and common adversary methods and objectives. Adversaries use a range of techniques to hinder the United States from achieving its objectives during competition and further their own interests. Forward-positioned Army forces may be able to detect and assess such adversary activities. By understanding and effectively countering adversary techniques, Army forces can help the joint force and interagency partners achieve their objectives.
ACTIVITIES TO ACHIEVE STRATEGIC GOALS
4-5. Adversaries employ all of their instruments of national power in a combination of ways to pursue strategic interests without direct military confrontation with the United States. For example, Russia applies its elements of national power through an approach called “New-Type War” (also labeled “Russian New Generation Warfare”). This approach allows Russia to achieve many of its strategic goals below the level of armed conflict and with limited employment of military forces. If coercion through diplomatic, information, and economic instruments fails, Russia is prepared to employ its conventional military power and proxy forces as needed. China also relies on a comprehensive use of its instruments of national power. Like Russia, China seeks to achieve many of its strategic objectives with nonmilitary instruments of national power and keep military forces in a supporting role that reinforces facts established on the ground with other than overt military action.
4-6. By using all instruments of national power, an adversary is able to further its interests through a range of nonmilitary and military activities that may provide advantages over U.S. forces. Examples of nonmilitary activities include Russia and China’s diplomatic efforts to establish security cooperation agreements with neighboring countries as a way to expand regional influence. Another example is China’s use of infrastructure projects, as part of “The Belt and Road Initiative”, to grow its economic influence. In both examples, adversaries primarily use nonmilitary means to achieve strategic objectives while weakening U.S. influence and undermining political-military partnerships between the United States and other countries within these same regions.
4-7. Adversaries can pursue more aggressive options through military activities that safeguard their interests abroad, maintain regional stability, and exert influence regionally and globally. These activities may include controlling or reducing access to certain areas of the global commons, challenging the established borders of other nations, or using the threat of force to influence the decisions of neighboring countries. Adversaries may pursue these activities overtly with the use of conventional military forces or covertly through a combination of proxy forces, unconventional warfare, and information warfare.
4-8. Proxy forces are generally non-state actors aligned with respective state actors, and they perform activities on behalf of or in accordance with the state actor’s strategic objectives. Examples of proxies include paramilitary groups, criminal organizations, private civilian organizations, private companies, special interest groups, and religious groups. Covert methods, such as the use of proxy forces, provide adversaries with plausible deniability and cost savings in achieving strategic objectives.
ACTIVITIES TO COUNTER A UNITED STATES RESPONSE
4-9. While adversaries desire to further their interests and achieve their goals without U.S. involvement, they will be prepared to counter a response from the U.S. military. To do this, an adversary may attempt to prevent or constrain the United States’ ability to project forces to the region and limit U.S. response options by using the following methods:
Conduct information warfare activities to manipulate the acquisition, transmission, and presentation of information in such a way that legitimizes the adversary’s actions and portrays the United States as the aggressor.
Conduct preclusion activities through nonlethal means to undermine relationships, raise political stakes, manipulate public opinion, and erode resolve to constrain or eliminate basing rights, overflight corridors, logistics support, and concerted allied action.
Isolate the United States from allies and partners by fostering instability in critical areas and among relevant actors to increase U.S. operational requirements.
Create sanctuary from U.S. and partner forces through international law and treaty agreements, monitoring and attacking partner forces from across international borders, and using proxy forces.
Conduct systems warfare by executing cyberspace attacks against critical force projection and sustainment infrastructure nodes to delay or disrupt the United States’ ability to deploy forces. Systems warfare approaches include nonattributable attacks on domestic infrastructure and the employment of networked military capabilities that support isolation and preclusion efforts.
ACTIVITIES TO PRECLUDE UNITED STATES ACCESS TO A REGION
4-10. Adversaries seek to establish conditions that limit or prevent U.S. access to a region, typically in locations close to their borders. This includes forward positioning of layered and integrated air defenses, early warning surveillance radars, rocket artillery, electronic warfare capabilities, and counter-space capabilities. Additionally, adversaries may seek to position intermediate-range ballistic missiles, cruise missiles, fixed-wing aircraft, unmanned aircraft systems, and naval surface and subsurface forces to shape an operational environment in their favor. Positioning systems that support an antiaccess (A2) strategy allows adversaries to deny or disrupt U.S. access to a region in the event of hostilities while providing leverage against friendly partner nations with the potential use of force. Furthermore, the positioning of systems capable of delivering conventional and nuclear munitions creates additional challenges for the United States. An adversary’s ability to establish, maintain, and demonstrate robust A2 systems bolsters its domestic narratives while eroding partner nation trust and confidence.
4-11. Friendly forces must assume they are always under observation because of all the means available to a peer adversary, particularly those available in space and cyberspace. In addition to forward positioning capabilities that support A2 and area denial (AD) approaches, these adversaries seek understanding of the disposition, readiness, and activities of U.S. forces within a contested region. Adversary activities include reconnaissance of U.S. military installations, unit movements, ports of embarkation and debarkation, and staging areas to identify potential targets for ballistic missiles and long-range fires. Adversaries employ cyberspace tools to conduct reconnaissance of friendly networks to identify vulnerabilities for possible exploitation. An adversary may conduct probing actions in the air and maritime domains to test responses by U.S. and other friendly forces. The intelligence gained through these activities will prepare an adversary for hostilities in the event a situation escalates to armed conflict. (See the ATP 7-100 series for a detailed discussion on specific threat capabilities and employment strategies. See Chapters 6 and 7 for specific examples of how adversaries are likely to employ A2 and AD capabilities in the beginning of a conflict.)
PREPARATION FOR LARGE-SCALE COMBAT OPERATIONS
4-12. Army forces that cannot credibly execute operations during armed conflict neither deter adversaries nor assure allies and other unified action partners. Preparation for large-scale combat operations is therefore the primary focus of Army conventional forces during competition. While there are multiple forms of armed conflict, large-scale combat among state actors is the most complex and lethal form of armed conflict, and it demands significant focus along multiple lines of effort to prepare for it. Some of the activities Army forces execute to prepare for armed conflict include—
Setting the theater.
Building allied and partner capabilities and capacity.
Improving joint and multinational interoperability.
Protecting forward-stationed forces.
Preparing to transition and execute operation plans (OPLANs).
Training and developing leaders for operations in specific theaters.
SET THE THEATER
4-13. Setting the theater is the broad range of activities continuously conducted to establish conditions for the successful execution of operations in a theater. Setting the theater never ends. It is conducted to enhance an operational environment in ways favorable to friendly forces and occurs during competition, crisis, and armed conflict. While setting the theater occurs across each strategic context, its importance is greatest during competition because that is when the most time is available. Army forces must set the theater during competition to enable quick transitions during crisis and conflict, when time favors the aggressor. Army forces use military engagements, security cooperation, and other activities to assess and understand the current conditions within the theater and execute specific theater setting activities to enable joint forces and other unified action partners.
4-14. Setting the theater requires a comprehensive approach among unified action partners and bilateral or multilateral diplomatic agreements that allow U.S. forces access to ports, terminals, airfields, and bases in the area of responsibility (AOR) to support future operations. This includes but is not limited to theater opening; reception, staging, onward movement, and integration (RSOI); establishing networks; classifying routes; and other operational activities that set the conditions for operations in the AOR. Information activities are a significant part of setting the theater. They enable decision making, protect friendly information, inform domestic and international audiences, and influence foreign audiences, while helping to counter adversary information warfare.
4-15. Setting the theater is a continuous activity for all staff sections and warfighting functions. It involves significant sustainment, air and missile defense (AMD), engineering, information collection, intelligence, and communications focused on setting conditions to counter known or potential threats to U.S. interests across the AOR. All warfighting functions, functional areas, and branches that comprise staffs and commands conduct preparation of the operational environment to address unique considerations for setting the theater within their respective areas of expertise (for example, civil preparation of the environment and joint intelligence preparation of the operational environment). (For more information about the land component’s roles and responsibilities for setting the theater in conflict, refer to JP 3-31 and JP 3-35. For additional information about the subordinate Army tasks and activities associated with setting the theater, refer to ATP 3-93 and FM 4-0. See paragraphs 4-61 and 4-62 of this publication for considerations unique to theater armies and Chapter 7 for theater-setting considerations in a maritime environment.)
BUILD ALLIED AND PARTNER CAPABILITIES AND CAPACITY
4-16. Army forces fight as part of a joint and multinational force. The United States cannot achieve its security interests without the cooperation of treaty allies, partner nations, and other unified action partners. Helping partner nations build, rebuild, or maintain their national security institutions is a critical step in maintaining regional stability, and it is ultimately less expensive than requiring U.S. forces to do so. Additionally, by maintaining partner-nation security institutions, the Army helps add to the aggregate force that is available to potentially deter adversary forces or counter them if they choose to pursue their goals through armed conflict. Forward-stationed U.S. Army forces, by themselves, generally do not enjoy favorable combat power ratios with peer adversaries. Allies and other partners provide the bulk of forces initially able to conduct operations during armed conflict. This combined force capability enhances deterrence for both the partner nation and the United States. (See paragraphs 4-39 through 4-52 for more information on how Army forces help build allied and partner capabilities.)
4-17. Combined training and exercises with partners play a key role in building allied and partner capabilities and shaping an operational environment. Such events are the most overt and visible means of demonstrating friendly capabilities, interoperability, and will. Exercises also help set the theater. Multinational forces that maintain high levels of combat readiness provide the credibility essential to assure partners and deter adversaries. Combined exercises build relationships and mutual respect among allies and other multinational partners, identify systems and processes to employ partner capabilities effectively, and reveal shortfalls to be improved upon. Training exercises occur at all echelons of command, from tactical units to large, combined task forces. The application of lessons learned during these exercises is key to improving multinational interoperability during competition. An example of a failure to prepare for large-scale combat operations occurred in the Philippines in 1941.
During the summer of 1941 the United States Army took steps to prepare for potential armed conflict with Japan. The War Department created the United States Army Forces in the Far East (USAFFE) and recalled General Douglas MacArthur to active duty to serve as the commanding general. The War Department provided USAFFE with the priority for equipment and reinforcements within the Pacific Theater of Operations to support General MacArthur’s defensive plans.
By December 1941, USAFFE had made significant strides, but had not done enough to effectively prepare for armed conflict. When Japan’s forces attacked the Philippines on 8 December 1941, ten hours after their attack on Pearl Harbor, Hawaii, USAFFE was short personnel, supplies, and equipment. Aside from a provisional tank group, most forces were ill equipped and possessed obsolete weapons and vehicles. The Philippine armed forces, whose readiness was also a USAFFE responsibility, were even less prepared than U.S. forces. They lacked modern weapons, effective logistics systems, and training. The War Department and USAFFE attempted to make up for these shortcomings by distributing supplies from pre-positioned stocks on the islands of Corregidor and the Bataan Peninsula to both U.S. and Philippine units stationed throughout the archipelago.
The Far East Air Force was equally unprepared. It lacked early warning systems and anti-aircraft artillery. Planned survivability improvements to airfields were incomplete, leaving aircraft exposed on flight lines and parking aprons. As a result, the Far East Air Force lost over half of its aircraft by the conclusion of the first day of the war, most of which were destroyed on the ground.
Although the U.S. and Philippine forces mounted a fierce resistance for nearly six months, Japan eventually isolated the defenders in the Bataan Peninsula and on the island of Corregidor with naval and air forces. In the absence of friendly air and naval support, the U.S. and Philippine forces were unable to receive reinforcements, resupply, or conduct an evacuation. As a result, the U.S. and Philippine forces in the Bataan Peninsula fell to Japan’s forces in April 1942, and the remaining forces on Corregidor and the surrounding islands surrendered in May 1942.
INTEROPERABILITY
4-18. The ability of Army forces to fight as a cohesive whole, integrated with the joint force, allies, and partners, is vital to maximizing combat power and creating a deterrent effect in a theater. Interoperability is the ability to act together coherently, effectively, and efficiently to achieve tactical, operational, and strategic objectives (JP 3-0). An Army formation that is interoperable with joint and multinational partners is substantially more capable than one that is not. Interoperability with any unified action partner is essential to effective operations. Interoperability standards and procedures must be trained, tested, and refined during competition; it is too late to seek interoperability once a crisis or armed conflict begins.
4-19. Interoperability starts with mutual understanding across echelons throughout a multinational force. Effective interoperability includes understanding technical challenges and developing methods to bridge gaps, understanding the tactical capabilities of each member in the multinational force, and integrating partners into a unified operational approach. During competition, the theater army or a delegated command is responsible for building the infrastructure that enables this. Communication is primarily achieved through liaison teams, understanding staff processes, and ensuring adequate access to partner nation command and control (C2) systems (within the limits of national caveats). Understanding foundational interoperability requirements like NATO doctrine; American, British, Canadian, Australian, and New Zealand (known as ABCANZ) Armies Program interoperability standards; and Combined Forces Command (in the Republic of Korea) processes is critical to communicate and interoperate with allied forces. It is essential that these requirements and standards are incorporated into routine training and exercise planning at all echelons to build the required interoperable readiness needed in a time of crisis or conflict. (See FM 3-16 for more information on multinational operations and interoperability.)
PROTECT FORWARD-STATIONED FORCES
4-20. Peer threats possess reconnaissance and surveillance, fires; special operations forces; and other capabilities that can range forward-stationed Army forces and place them at risk. The protection of Army forces forward, under the assumption that deterrence is not guaranteed, is essential. Army forces implement procedures and conduct necessary activities to ensure they, and the elements of the joint or partner force they protect, can endure an initial attack with little early warning. This includes preparation for threat attacks from any domain that is informed by understanding what holds friendly forces at risk and how a threat may attack. An adversary could attack using capabilities from domains other than land, either to set conditions on the ground or as a means of escalation designed to limit friendly options. Preparation by Army forces therefore includes planning and integration with other elements of the joint force. Coordination for Army and joint capabilities that are able to protect friendly forces during armed conflict and enable them to endure until they can be supported is critical to establishing deterrence.
4-21. The demonstrated ability of Army forces to withstand an adversary’s initial attack adds to the integrated deterrence effect on adversaries and may dissuade them from escalation. Host-nation capabilities may constitute a significant part of force protection and forward defense, so they must be integrated into theater protective efforts. Forward deployed forces that cannot be adequately protected or quickly repositioned during adversary escalation to armed conflict should be relocated to more defensible locations.
PREPARE TO TRANSITION AND EXECUTE OPERATION PLANS
4-22. Army forces at every echelon prepare to execute OPLANs that they are expected or likely to support. The foundation for this is active, continuous information collection and intelligence analysis. Higher echelons, such as the theater army and corps, identify initial targets and the required Army and joint capabilities needed to attack those targets in the initial stages of an armed conflict. They likewise consider whether general defense plans that provide guidance for subordinate unit immediate action during the early stages of a conflict initiated with few indications or warnings are necessary or prudent.
4-23. Preparation to execute OPLANs must extend to all echelons and partners. Lower tactical echelons train tactical tasks related to the parts of an OPLAN they support or execute. Units conduct deployment rehearsals and emergency deployment readiness exercises to improve response times and validate plans. Rehearsals with unified action partners build mutual understanding and improve interoperability. Units conduct thorough reconnaissance of all lines of communications, infrastructure, avenues of approach, assembly areas, and potential firing points or battle positions. Leaders and Soldiers should walk the actual terrain that engagements and battles could be fought on and, when possible, they should use this terrain for rehearsals. A shared understanding of OPLANs, terrain, and adversaries down to the lowest tactical echelon will allow an effective transition to armed conflict.
TRAIN AND DEVELOP LEADERS
4-24. Leaders prepare themselves, their subordinates, and their organizations for operations in specific combatant command AORs. When developing expertise in specific regions, units become familiar with applicable OPLANS and coordinate with the theater army, the assigned military intelligence brigade-theater (MIB-T), and other theater army-assigned units as appropriate. This regionally specific readiness augments ongoing training and leader development activities conducted across the force. (See Chapter 8 for a detailed discussion on the role of leadership during operations.)
RELATIVE ADVANTAGES DURING COMPETITION
4-25. During competition, Army forces seek relative advantages at the theater strategic, operational, and tactical levels. Relative advantages are advantages that Army forces provide the joint force commander (JFC) in relation to a specific adversary, and they are always contextual. They are necessary to deter adversaries, assist the joint force in promoting U.S. interests, and set conditions to conduct operations during crisis and armed conflict. These advantages augment unified action partner activities, and they address Service-specific issues identified during combatant command campaign development. Identifying, achieving, and maintaining these advantages helps the Army employ combat power effectively during crisis and armed conflict. A relative advantage is temporary. Adversaries quickly adapt to counter advantages (especially technological ones) once they are created or employed, and they seek to reduce or eliminate their effectiveness.
4-26. Understanding advantage relative to an adversary requires understanding the adversary’s capabilities and will, friendly capabilities and will, and the operational environment within the theater. It further requires understanding of the interrelated influences of each dimension in an operational environment, including how physical, human, and information factors affect each other in a specific context. Changes in one dimension often have outcomes in the other two and in more than one physical domain.
PHYSICAL ADVANTAGES DURING COMPETITION
4-27. Due to the expected tempo of operations, a sufficient number of Army forces comprised of the right capabilities must be forward stationed to provide CCDRs with a credible deterrent force and the ability to respond, when necessary, to adversary actions. Physical advantage encompasses combat power and the correlation of forces: the ability to deliver effects, superior range, and the ability to concentrate superior capabilities at the right places and times. Examples of activities that create physical advantages during competition include—
Working with allies to conduct a deployment exercise of a theater-tailored unit to improve its OPLAN integration and interoperability.
Surveying a potential assembly area with a forward engineer support team to determine if the area is of sufficient size to accommodate a properly dispersed Army formation.
Hardening facilities against attack and rehearsing drills in response to potential adversary courses of action.
Maintaining stocks of key supplies and equipment (Army pre-positioned stocks [APS]) in or near areas of concern to accelerate deployment of forces during crises or armed conflict.
INFORMATION ADVANTAGES DURING COMPETITION
4-28. Information activities play a key role during competition. They include Army support to the combatant command and unified action partner strategic messaging. Coordinating with interagency and other unified action partners helps to develop and deliver coherent messages that counter adversary disinformation. Army forces reinforce strategic messaging by maintaining and demonstrating U.S. Army readiness for operations. Examples of relative information advantages are—
Identifying targets and conducting target development on threat capabilities.
Setting the conditions for convergence by developing methods to penetrate adversary computer networks.
Discrediting adversary disinformation by helping the JFC inform domestic and international audiences through Army and joint information activities.
Promoting the purpose and outcomes of multinational exercises and training events.
Continuously monitoring the operational environment to detect changes to adversary methods or narratives.
HUMAN ADVANTAGES DURING COMPETITION
4-29. The institutional depth and professionalism of U.S. Army personnel contribute to the morale and will of partner security forces as Army forces interact across all ranks and echelons. Army formations serve as a professional force operating under the rule of law as guests in a specific region to facilitate the accomplishment of mutual military training goals. This can be a powerful advantage over adversaries who seek to extract concessions, including financial and informational gains, from other countries or groups. This bond of trust forms the foundation of the U.S. alliance system, and it is the primary means to ensure the security of the United States and its partners. Examples of activities that help achieve human advantages include—
Training U.S. and partner nation forces in multinational exercises at combat training centers.
Routine interaction with allies and other unified action partners that builds and maintains human, technical, and procedural interoperability through agreed-to standards.
Hosting international officers at U.S. professional military education programs and sending U.S. officers to international military schools.
Sustained presence by theater-aligned advisor teams that builds relationships and promotes interoperability over time.
INTERAGENCY COORDINATION
4-30. Military engagement, security cooperation, and deterrence activities usually involve a combination of military forces and capabilities separate from, but integrated with, the efforts of interagency participants. These actions are coordinated by diplomatic chiefs of mission and country teams. Understanding their roles and relationships is critically important. The Department of State is responsible for the diplomatic instrument of national power. Chiefs of mission are the final approval authorities for all U.S. military activities that occur in the nation they are responsible for, and they have the authority to modify the execution of planned activities during competition. (See JP 5-0 for more information on country-specific plans.)
4-31. Activities that occur during competition encompass a wide range of actions where the military instrument of national power supports and is subordinate to the other instruments of national power. Competition overseas generally requires cooperation with international organizations (for example, the United Nations) and government entities in other countries to protect and enhance mutual national security interests, deter conflict, and set conditions for future contingency operations.
UNITED STATES DIPLOMATIC MISSION
4-32. U.S. diplomatic missions include representatives of all U.S. departments and agencies physically present in the country. Chiefs of missions are the principal officers in charge of diplomatic missions. They are often, but not always, ambassadors. They oversee all U.S. government programs and interactions with and in a host nation. The chief of mission is the personal representative of the President and reports through the Secretary of State, ensuring all in-country activities serve U.S. interests and regional and international objectives.
4-33. The United States maintains different types of diplomatic missions in different countries. Some countries have only a consulate, many have only an embassy, and others have an embassy and a number of consulates. Typically, Army elements conducting security cooperation activities coordinate with diplomatic mission officials, even in nations with only a consulate. Relationships with consular offices are determined on a case-by-case basis. The same entities and offices existing in an embassy are present or liaised at consulates. (See FM 3-22 for a detailed explanation of this role in relation to Army operations.)
COUNTRY TEAM
4-34. The country team is the point of coordination within the host country for the diplomatic mission. The members of the country team vary depending on the levels of coordination needed and the conditions within that country. The country team is made up of the senior member of each represented U.S. department or agency, as directed by the chief of mission. The team may include the senior defense official or defense attaché, the political and economic officers, and any other embassy personnel desired by the ambassador.
4-35. The country team informs various organizations of operations, coordinates elements, and ensures unity of effort. Military engagement with a host country is coordinated through the Defense Attaché Office or Office of Security Cooperation at the embassy or consulate. However, several other attachés and offices may also be integral to security cooperation activities, programs, and missions. The country team provides the foundation of local knowledge and interaction with the host-country government and population. As permanently established interagency organizations, country teams represent the single point of coordination, integration, and synchronization of security cooperation activities supported by combatant commands and the theater army. It is incumbent upon the theater army, with the approval of the combatant command, to work with and inform the country team of recommendations for military engagement, security cooperation, and deterrence activities that involve Army forces across all domains.
COMPETITION ACTIVITIES
4-36. Competition involves activities conducted under numerous programs within a combatant command. The CCDR uses these activities to improve security within partner nations, enhance international legitimacy, gain multinational cooperation, and influence adversary decision making. Competition activities include obtaining access for U.S. forces, maintaining sufficient forward-based presence within a theater to influence conditions in the strategic environment, and mitigating conditions that could lead to a crisis or armed conflict. At any time during competition, but especially during times of heightened tension, leaders must take great care to ensure Army forces avoid activities that accidently provoke crisis or armed conflict. Army forces, as directed by the theater army, must stay within an activity level that meets the CCDR’s intent for readiness without unintentionally increasing tensions.
4-37. Activities that occur during competition are directly tied to authorities provided in various titles of the United States Code and approved programs, and they are integrated and synchronized with the Department of State, other government agencies, country teams, and ambassadors’ plans and objectives. The Department of State and the United States Agency for International Development (USAID) help produce the joint regional strategy to address regional goals, management, and operational considerations. Each country team develops both an integrated country strategy and a country development cooperation strategy to address joint mission goals and coordinated strategies for development, cooperation, security, and diplomatic activities. Working with the Department of State and various country teams, the CCDR develops country-specific security cooperation plans, which are codified in the country-specific security cooperation section of the combatant command campaign plan (CCP). Some CCPs include regional country plans, posture plans, and theater distribution plans that facilitate synchronization of resources, authorities, processes, and timelines to favorably affect conditions within the CCDRs’ AORs.
4-38. Army forces execute activities during competition that support joint force campaigning goals, satisfy interagency requirements, and set the necessary conditions to employ Army combat power during crisis and armed conflict. The theater army works with the CCDR to develop objectives for the employment of Army forces in theater and develops support plans to address Army-specific activities. Army forces provide security cooperation capabilities across any given theater of operations by conducting military engagement, security cooperation, nuclear deterrence, counter-weapons of mass destruction activities, and humanitarian assistance.
MILITARY ENGAGEMENT
4-39. Military engagement is contact and interaction between individuals or elements of the Armed Forces of the United States and those of another nation’s armed forces, or foreign and domestic civilian authorities or agencies, to build trust and confidence, share information, coordinate mutual activities, and maintain influence (JP 3-0). Military engagement occurs as part of security cooperation, but it also extends to interaction with domestic civilian authorities. Army forces will also routinely communicate with nongovernmental organizations, either directly or indirectly, to ensure expectations and roles are understood.
4-40. CCDRs and Army senior leaders seek out partners and communicate with adversaries to discover areas of common interest and tension. This increases the knowledge base for subsequent decisions and resource allocation. Such military engagements can reduce tensions and may prevent conflict, or, if conflict is unavoidable, they may allow the United States to enter into conflict with greater access and stronger alliances or coalitions. Army forces support military engagement through deliberate interactions with unified action partners at the junior Soldier through senior leader levels. The State Partnership Program provides a good example of how powerful military engagement can be.
The State Partnership Program supports the security cooperation objectives of CCDRs by developing enduring relationships with partner countries and carrying out activities to build partner capacity, improve interoperability, and enhance U.S. access and influence while increasing the readiness of U.S. and partner forces to meet emerging challenges. The program links a state’s National Guard with the partner nation’s military, security forces, and disaster response organizations in a cooperative relationship.
Since the program’s inception in 1993 with the three Baltic Republics, it has expanded to encompass partnerships with 89 nations. Most of the earliest State Partnership Program partner countries in Europe have gone on to become U.S. allies in NATO, and many of them credit the State Partnership Program and their National Guard partners with helping make that possible. By building enduring relationships based on mutual trust and support, the State Partnership Program has expanded the pool of aligned global security providers and improved the capabilities of both U.S. Army units and partner nation militaries across the world.
SECURITY COOPERATION
4-41. Security cooperation is all Department of Defense interactions with foreign security establishments to build security relationships that promote specific United States security interests, develop allied and partner nation military and security capabilities for self-defense and multinational operations, and provide United States forces with peacetime and contingency access to allied and partner nations (JP 3-20). These efforts may include Army forces participating in joint and multinational exercises and employing regionally aligned forces. Conducting security cooperation is one of the Army’s primary stability tasks.
4-42. Security cooperation is governed by the Foreign Assistance Act (22 United States Code [USC], 2151) and the Arms Export Control Act (22 USC, 2751) addressing DOD interactions with other nations. The Department of State is the lead agency for security sector assistance. All DOD security cooperation programs must nest with Department of State security sector guidance. (See JP 3-20 for more information on joint security cooperation and FM 3-22 for additional details on Army support to security cooperation.)
4-43. Commanders and staffs conduct security cooperation to develop allied and other friendly military capabilities for self-defense and multinational operations, to improve information exchange and intelligence sharing, to provide U.S. forces with peacetime and contingency access, and to mitigate conditions that could lead to a crisis. Multiple types of security cooperation activities can often occur simultaneously with overlapping purposes. These activities include security assistance, security force assistance (SFA), foreign internal defense (FID), and support to security sector reform efforts.
4-44. Security assistance is a group of programs the U.S. Government uses to provide defense articles, military training, and other defense-related services by grant, lease, loan, credit, or cash sales. Security assistance programs are typically focused on the transfer of defense articles and services to eligible foreign governments, the provision of training and education to foreign military personnel, and the sale of construction services in support of partner nations’ military establishments. Military education and training exchanges are invaluable for building interoperability and fostering trust over time between U.S. Army and partner personnel.
4-45. Security force assistance is the Department of Defense activities that support the development of the capacity and capability of foreign security forces and their supporting institutions (JP 3-20). Security forces are duly constituted military, paramilitary, police, and constabulary forces of a state (JP 3-22). Consistent with Department of Defense (DOD) policy for SFA, the Army develops, maintains, and institutionalizes the capabilities of its personnel to support efforts to organize, train, equip, rebuild or build, and advise foreign security forces and relevant supporting institutions. SFA activities are conducted primarily to assist partner nations to build their capacity to defend against external and transnational threat actors. Security force assistance brigades (SFABs) are Army organizations focused specifically on this mission. (See paragraphs 4-88 through 4-89 and ATP 3-96.1 for information on SFABs.)
4-46. SFA and security assistance are different. Security assistance is a broader set of programs that includes training, but also includes equipment transfers, sales, and other programs. SFA works in conjunction with security assistance programs while focusing specifically on building the capacity and capability of foreign security forces and their supporting institutions.
4-47. Foreign internal defense is participation by civilian agencies and military forces of a government or international organizations in any of the programs and activities undertaken by a host nation government to free and protect its society from subversion, lawlessness, insurgency, terrorism, and other threats to its security (JP 3-22). FID includes the actions of both nonmilitary organizations and military forces.
4-48. FID is a comprehensive approach that supports partner development towards democratic governance and military deference to civilian rule. These activities may employ the indirect use of military forces along with diplomatic, informational, and economic means. FID involves the support of a standing host-nation government and its military or paramilitary forces. The focus of all U.S. FID efforts is to support the host-nation’s internal defense and development program to build the capability and capacity of the host nation to achieve self-sufficiency. FID is an Army special operations forces core activity. (See JP 3-22 and ATP 3-05.2 for a detailed discussion of foreign internal defense.)
4-49. SFA and FID have much in common because both enable friendly partners’ capacity to provide for their own defense. While there can be overlap, FID activities are aimed at strengthening a wide range of functions including both military and civilian governmental institutions against internal threats. SFA activities improve military and other security forces against both internal and external threats, and they do not include activities that primarily support other government institutions.
4-50. Security sector reform is a comprehensive set of programs and activities undertaken by a host nation to improve the way it provides safety, security, and justice (JP 3-07). The overall objective is to provide these services in a way that promotes an effective and legitimate public service that is transparent, accountable to civilian authority, and responsive to the needs of the public.
4-51. Security sector reform is an umbrella term that includes integrated activities in support of defense and armed forces reform; civilian management and oversight; justice, police, corrections, and intelligence reform; national security planning and strategy support; border management; disarmament; demobilizations and reintegration; and reduction of armed violence. The Army’s primary role is supporting the reform, restructuring or re-establishing the armed forces and the defense sector across the competition continuum.
4-52. U.S. and partner military forces collaborate with interagency representatives and other civilian organizations to design and implement security sector reform strategies, plans, programs, and activities. The Department of State leads and provides oversight for these efforts through the integrated country strategy. The desired outcome of security sector reform programs is an effective and legitimate security sector firmly rooted within the rule of law.
NUCLEAR DETERRENCE AND COUNTERING WEAPONS OF MASS DESTRUCTION
4-53. U.S. nuclear capabilities are foundational to the deterrence of adversary weapons of mass destruction use. To ensure the credibility of this deterrent, joint and Army forces must integrate the planning and operations of nuclear and conventional forces. Further, Army forces must plan, train, and exercise to conduct operations under the adversary threat or use of weapons of mass destruction in order to deny the adversary any perceived advantage that might result from employing weapons of mass destruction. To do so, commanders and staffs must continuously assess, protect, and mitigate the effects of adversary chemical, biological, radiological, and nuclear (CBRN) weapons use and contamination hazards. They must train under simulated weapons of mass destruction conditions. When under threat of nuclear attack, commanders must balance the risk of dispersing forces to mitigate the impact of nuclear effects across their AO against the ability to concentrate sufficient combat power to achieve objectives. In a chemically contaminated environment, a commander’s decision-making ability is complicated by the effects on Soldier stamina, reaction times, and sustainment. Each of these environments requires unique actions to ensure a formation’s ability to maneuver, fight, and sustain operations. (See ATP 3-90.40 for more information on countering weapons of mass destruction.)
HUMANITARIAN ASSISTANCE
4-54. USAID is the lead U.S. government agency, responsible to the Secretary of State, for administering civilian foreign aid and providing humanitarian assistance and disaster relief. USAID often works in concert with Army forces when Soldiers are tasked to provide assistance. It can supplement forces conducting civil affairs operations that the DOD conducts to build relationships and win the trust, confidence, and support of local populations. One example of a successful humanitarian assistance operation occurred during an Ebola outbreak in Liberia in 2014.
In October 2014, a joint force comprised of 3,000 Soldiers, Sailors, Airmen, and Marines deployed to Liberia to help contain and eradicate the Ebola virus. The 101st Airborne Division (Air Assault) served as the joint task force (JTF) headquarters during this operation. The 101st worked with the government of Liberia, the U.S. Embassy, United States Army Africa, USAID, the U.S. Centers for Disease Control and Prevention, and the U.S. Public Health Service. USAID was the lead federal agency. Army units helped build and supported 17 Ebola treatment centers across Liberia. Army forces trained 1,500 health care workers, and a logistic system was established that provided medical supplies and building materials. As a result of the rapid response and achieving unity of effort, Liberia went from 80 new cases of Ebola a day to being declared Ebola-free within seven months.
ROLES OF ARMY ECHELONS DURING COMPETITION
4-55. Theater armies, including their assigned theater-echelon commands and brigades, perform essential functions during competition to achieve national objectives while deterring adversary malign action. Corps, divisions, and brigade combat teams (BCTs) are crucial to the execution of operations, activities, and tasks during competition. These forces may support SFA or FID by participating in multinational exercises and conducting humanitarian and other civil-military operations, development assistance, and training exchanges. Army forces at corps and lower echelons directly engage with partner forces, governmental and nongovernmental organizations, and civilian populations to accomplish missions, build rapport, and improve conditions that promote stability.
Note. The organizations listed in paragraphs 4-56 through 4-96 have critical roles during competition. Numerous other organizations also provide important contributions.
THEATER ARMY ROLES DURING COMPETITION
4-56. The theater army is the primary Army organization that plans, prepares, and oversees the execution of activities conducted by Army forces during competition and assesses the results of these activities. It supports and enables the CCDR’s pursuit and maintenance of operational access critical to achieving advantages throughout an AOR while improving the security capabilities of partner nations. Gaining relative advantages during competition requires intelligence about the adversary’s capabilities and intent relative to friendly forces. While adversary intent is more difficult to ascertain, both factors are equally important since capability plus malign intent represent a larger immediate threat than either factor on its own. This understanding allows theater army commanders to recommend actions to the CCDR that impede adversary goals or convince adversaries to seek alternative courses of action more favorable to U.S. interests.
4-57. The theater army integrates Army forces and capabilities with the other instruments of national power on behalf of the CCDR. It fulfills CCDR requirements while simultaneously fulfilling Service-specific requirements for Army forces to prepare for large-scale combat operations. It achieves its support to both the joint force and Army by concentrating on seven functions and by providing oversight or C2 to subordinate Army organizations during competition. Within each theater army function, there are multiple tasks the theater army might fulfill to achieve its mission. (See FM 3-94 and ATP 3-93 for an expanded discussion of each function listed in paragraph 4-58 and the subordinate tasks within each function.)
4-58. During competition, the theater army focuses on enabling the United States, its allies, and other unified action partners to compete effectively below the threshold of armed conflict in ways directed by the CCDR. These persistent and regular activities provide assurance to partner nations and deter adversaries. The theater army does this by focusing on the following functions:
Execute the CCDR’s daily operational requirements.
Provide administrative control (ADCON) of Army forces.
Set and maintain the theater.
Set and support operational areas.
Exercise C2 over Army forces in the theater.
Perform joint roles limited in scope, scale, and duration.
Conduct contingency planning for crisis and armed conflict.
4-59. The theater army translates the CCDR’s plans and requirements into concrete actions by Army forces. This includes, but is not limited to, the following activities and tasks:
Provide Army support to other Services (ASOS).
Conduct theater security cooperation.
Assess and develop infrastructure.
Develop concept plans and OPLANS.
Maintain threat models and provide intelligence on significant changes in the operational environment.
4-60. Administrative control is the direction or exercise of authority over subordinate or other organizations in respect to administration and support. The exercise of ADCON fulfills a military department’s statutory responsibilities. ADCON is synonymous with administration and support responsibilities identified in Title 10, USC. ADCON includes organization of Service forces, control of resources and equipment, personnel management, unit logistics, individual and unit training, readiness, mobilization, demobilization, discipline, and other matters not included in the operational missions. The theater army headquarters is responsible for ADCON of all Army forces in the AOR in both peacetime and wartime. (See AR 10-87 for more information on ADCON.)
4-61. In addition to the broad requirements in setting a theater, including contributions from all warfighting functions (outlined in paragraphs 4-13 through 4-15), theater armies have unique requirements for theater setting met by conducting sustainment preparation of the operational environment. Sustainment preparation of the operational environment is a continuous shaping activity involving analysis to determine infrastructure, environmental, or resource factors in the operational environment that impact the Army’s ability to sustain a commander’s OPLAN. Analysis products cover such topics as host-nation support, selection of lines of communications, determination of operational stock assets, replacement operations, and design of a distribution network and information technology infrastructure for the theater. In most cases these resources (including host-nation labor and services) will be shared with partners of other nations in accordance with negotiated agreements. (See FM 4-0 for more information on sustainment preparation of an operational environment.)
4-62. The theater army continually analyzes, evaluates, and, when directed, expands APS to rapidly provide JFCs with needed Army capabilities. APS augment allocated Army rotational forces already serving in a theater and theater-assigned forces. The tempo and intensity of operations during crisis or armed conflict may not allow for the timely deployment of all of an apportioned force’s equipment sets from the United States via strategic airlift or sealift. Depending on the theater, this may require a large and dispersed equipment force posture based at multiple hardened sites. If needed, a high operational readiness rate will be maintained for APS that allows Army forces to fall in on the equipment and employ it within a few days of arriving in theater. The theater army coordinates with Army Materiel Command to maintain and optimize APS. (For additional information on APS, refer to ATP 3-35.1.)
4-63. Setting and supporting operational areas for the joint force occurs at operational and tactical echelons. During competition, the theater army helps identify likely joint operations areas (JOAs) for ground forces. The theater army ensures that the JOA includes bases and base camps needed by forces that primarily operate in the land domain. (See ATP 3-37.10 for a discussion on base and base camp planning.) Planners must take a holistic approach to understand the needs of the other Services and address Army requirements. Due to the large amount of information needed at the tactical echelon to properly set and support JOAs, the theater army usually needs to develop a multi-year plan that examines potential areas of operations (AOs). The theater army relies on a large number of low density and high demand units to conduct this tactical level of analysis. Many of these capabilities reside in the United States Army National Guard or the United States Army Reserve.
4-64. The theater army is the Army Service component command (ASCC), and it has the responsibility to control attached and assigned Army forces within the AOR through ADCON and operational control (OPCON) or tactical control (TACON). As the Army component of the combatant command, the ASCC is the ARFOR for the theater. When a subordinate JTF is established containing Army forces, the senior Army headquarters in that JTF is normally designated as its ARFOR. (See Appendix B for details on command and support relationships.)
4-65. The theater army initially maintains control of all Army forces assigned to an AOR until control is passed to a subordinate JTF in a JOA. This control is usually passed from the theater army to the JTF when the Army force is ready for onward movement and integration into the JTF. As part of controlling Army forces, the theater army (or other headquarters designated as the ARFOR) maintains ADCON of Army forces and addresses Service responsibilities such as coordinating ASOS.
4-66. While serving as the ASCC, the theater army has the capability to perform three joint roles for the CCDR. With augmentation, the theater army can be the theater joint force land component command, a JTF, or the joint force land component command to a JTF in a JOA. However, these roles can only be performed in limited scope, scale, and duration, unless the JFC provides significant augmentation.
4-67. A key aspect of combatant command and Service component planning during competition or crisis is the development of contingency plans. A contingency plan is a branch of a campaign plan that is planned based on hypothetical situations for designated threats, catastrophic events, and contingent missions outside of crisis conditions (JP 5-0). Contingency plans are branches to global, regional, functional, and combatant campaign plans that address potential threats that put one or more national interests at risk in ways that warrant military operations. Contingency plans anticipate the possibility that campaign activities during competition could fail to prevent aggression, a need to respond to instability in a key state or region, or response to natural disasters. (See JP 5-0 for more information on contingency planning.)
4-68. The theater army commander and staff assist the combatant command in developing contingency plans, including developing subordinate plans for Army forces as required. Theater army planners routinely review and update contingency plans to ensure they remain feasible. This includes a review of Army force structure and its relation to joint time-phased force and deployment data (TPFDD). This relationship is covered in detail under force tailoring in paragraph 4-71. Army corps and divisions that are regionally aligned to a specific combatant command may develop subordinate plans as directed. Army corps and divisions train for and rehearse these plans in Joint Chiefs of Staff-directed exercises, Army Mission Command Training Program exercises, and other training events. (See ADP 5-0 for doctrine on Army planning.)
4-69. Theater army and select subordinate organizations prepare for operations that could occur in the rear areas identified during OPLAN development. Planning and preparing for rear area operations facilitates consolidation of gains during armed conflict. Where possible, the theater army should involve the rear area command posts of regionally aligned corps and divisions in the development and refinement of plans dealing with rear areas likely to be part of those units’ AOs. Regionally aligned units that primarily operate in the rear area must be included in planning and exercises whenever possible.
4-70. Army formations coordinate, rehearse, and support host-nation execution of stability and security missions. These efforts help minimize the diversion of combat power from other priorities. Civil affairs units have expertise for analyzing potential civil networks to execute these missions. They identify potential civil networks through civil preparation of the environment and the civil network development and engagement process. Civil preparation of the environment is the continuous development of civil knowledge within an area of operations to help commanders identify capabilities within civil society that can be integrated with operations for stability and security activities (FM 3-57). This minimizes the requirement for Army forces in the rear area and facilitates the maintenance or restoration of host-nation governance and legitimacy.
4-71. Force tailoring is the process of determining the right mix of forces and the sequence of their deployment in support of a joint force commander (ADP 3-0). It involves selecting the right force structure for a joint operation from available units within a combatant command and from the Army force pool. Commanders then sequence forces into an AO as part of force projection. JFCs request and receive forces for each campaign phase, adjusting the quantity of Service component forces to match the effort required. TPFDD documents contain both force composition and force flow requirements, and they are the primary method by which JFCs tailor their inbound forces. Theater armies tailor forces to meet land force requirements as determined by JFCs, and they recommend a deployment sequence to meet those requirements. Force tailoring is continuous. (See JP 3-35 for more information on force tailoring and TPFDD development.)
THEATER ARMY ASSIGNED FORCES
4-72. Each theater army has assigned or allocated theater-level forces that provide additional support across the CCDR’s AOR and help the theater army achieve its objectives. Different theaters have different subordinate forces with distinct command and support relationships based on theater requirements and force availability. The units listed in paragraphs 4-73 through 4-87 are common theater-level formations that facilitate operations during competition.
4-73. The Theater Sustainment Command (TSC) is the Army’s organization for the integration and synchronization of sustainment in a theater. The TSC connects strategic enablers to tactical formations. It is a theater-committed asset to each theater army, and it focuses on Title 10, USC support of Army forces for theater security cooperation and the CCDR’s daily operational requirements.
4-74. TSCs execute sustainment operations through their assigned and attached units while integrating and synchronizing sustainment operations across an AOR. They have four operational responsibilities to forces in theater: theater opening, theater distribution, sustainment, and theater closing. The task-organized TSC is tailored to provide operational-level sustainment support within an assigned AOR. It integrates and synchronizes sustainment operations for the theater army, including all Army forces forward stationed, transiting, or operating within an AOR. The TSC coordinates Title 10, USC; ASOS; DOD executive agency; and lead Service responsibilities across the entire theater. (See ATP 4-94 for more information on the TSC.)
4-75. The MIB-T is usually assigned to the combatant command with OPCON delegated to the theater army. It provides mission command for the theater army’s information collection and intelligence analysis capabilities across all intelligence disciplines, integrating theater and national architectures and data to support the theater army’s daily operations requirements and preparation for contingency operations. The theater army headquarters specifically relies on the MIB-T for threat characteristics, intelligence estimates, threat and civil considerations, data services, intelligence architecture development and maintenance, and all-source intelligence products. These efforts support theater army planning requirements, including development of Army plans supporting the CCP and maintenance of OPLANs and contingency plans.
4-76. The MIB-T serves as the intelligence anchor point for deploying forces, providing theater-specific expertise and support. It maintains a regional intelligence architecture that deploying and theater-aligned units can access. This allows units to tailor mission planning and training and effectively leverage the broader intelligence enterprise. The MIB-T’s regional focus provides continuity and cultural context to its analytic intelligence products. The brigade can collect, analyze, and track the threat characteristics and doctrine of theater state and non-state actors over many years, providing indications and warnings of changes in an operational environment. This allows it to create and maintain a valuable database of intelligence regarding persons of interest and the evolving doctrine and capabilities of regional military forces. (See FM 2-0 for more information on the MIB-T.)
4-77. Theater aviation support is executed by theater aviation brigades, theater airfield operations groups, and theater aviation sustainment maintenance groups. Each theater aviation brigade can conduct assault or general support aviation tasks in support of the theater and its subordinate commands, but it requires augmentation with attack aviation or unmanned aircraft system (UAS) units to conduct attack, reconnaissance, and security operations. Combat aviation brigades may also support theater aviation operations with lift, attack, and UAS capabilities. Theater airfield operations groups provide air traffic services, conduct airfield management operations, and support RSOI requirements for aviation assets. The theater aviation sustainment group is resourced to provide aviation sustainment maintenance and limited depot sustainment support throughout the theater AO. (See FM 3-04 for more information on aviation brigades and groups.)
4-78. The Army air and missile defense command (AAMDC) is the highest echelon for air defense artillery units. It is usually under OPCON of the theater army, or land component command if designated, with the AAMDC commander serving as the theater Army AMD coordinator. The AAMDC is also usually in direct support of the theater air force, or air component command if designated, with the AAMDC commander serving as the theater deputy area air defense commander. The AAMDC participates in theater exercises and integrates with joint and multinational partners in all aspects of AMD operations. It provides assets and coordinates coverage to protect forward-positioned joint and Army forces, and critical infrastructure, from air, missile, and rocket attack. This protection includes early warning, surveillance, tracking, and defense against tactical short-range targets through intermediate-range ballistic missiles. (See FM 3-01 and ATP 3-01.94 for more information on AAMDC planning and execution.)
4-79. The theater army is the designated DOD executive agent for setting and supporting the theater communications and network infrastructure in all AORs. The theater army executes these responsibilities either through a signal command (theater) or strategic signal brigade assigned to support the AOR. Either unit provides connectivity to Defense Information Systems Network services up to secret classification. This connectivity includes establishing and operating the theater network architecture to support all joint and Army forces operating in an AOR.
4-80. The signal command (theater) or strategic signal brigade provides oversight, leadership, and technical direction over the theater network and spectrum management support for all Army units across the theater. It also provides—
Centralized management of data, voice, and video networks, including interfaces with joint, interorganizational, and multinational systems in the theater.
Enforcement of global cybersecurity policies to support the CCDR and theater army commander.
Oversight of units installing, operating, maintaining, and securing signal support systems and network interfaces to joint and multinational partner systems in theater.
Establishment of mission priorities to ensure network capabilities are available to meet commanders’ information requirements.
4-81. The theater engineer command (TEC) supports the theater army by organizing and directing Army combat, general, and geospatial engineer assets to improve mobility, enhance survivability, enable force projection and logistics, build partner capacity, and develop infrastructure. The primary focus of the TEC during competition is to determine and build the needed infrastructure to facilitate deployment of U.S. forces, protect forward-stationed U.S. forces, and, where possible, build up the capabilities of allied and partner nations to withstand an initial assault by a peer threat. Examples of engineer activities the TEC directs are conducting route analysis and terrain analysis of potential assembly areas for large Army units like BCTs and identifying needed assets to construct dispersed base clusters in the rear areas to support logistics operations in the close area. When directed, the TEC also provides C2 for engineers from other Services and multinational organizations and provides technical oversight (quality assurance and surveillance) assistance for contracted construction engineers according to the relationships established by the JFC. (See FM 3-34 for more information on theater engineer commands.)
4-82. A battlefield coordination detachment (BCD) is a specialized, regionally focused Army element that serves as the senior Army operational commander’s liaison with the air component. A BCD is co-located with the joint air operations center (JAOC), combined air operations center, or the Air Force air operations center.
4-83. The BCD is the Army’s interface for systems connectivity to the JAOC and for personnel integration with their JAOC counterparts. The BCD supports the land component command during large-scale combat operations. Army corps relay requirements and requests to the land component, who, in turn, relays land component requirements and requests for joint force air component support through the BCD. The BCD represents the joint force land component commander throughout the joint air tasking cycle in the JAOC. (See ATP 3-09.13 for doctrine on the BCD.)
4-84. An Army theater fires command or theater fires element provides C2 of assigned fires capabilities, serves as the senior organization assigned to a theater army to integrate allocated or assigned fires capabilities, and executes critical fire support functions. It develops and nominates joint targets across the theater. This support to joint targeting supports the continuous setting of the theater and coalition forces land component commander (CFLCC), field army (when constituted), and corps operations. The theater fires command or element ensures the Army’s contribution to the joint targeting process is effectively planned and executed during competition and crisis and can quickly transition to large-scale combat operations in accordance with the ground force commander’s priorities. (See FM 3-09 for additional information on theater fires commands and elements.)
4-85. The Army field support brigade links strategic resources to tactical units, and it can be assigned in support of a theater army or a corps. It provides APS readiness, ensuring stocks are maintained for use by arriving forces during crisis or armed conflict. The execution of APS equipment configuration and handoff operations are exercised as individual events and also as part of larger exercises, including the DEFENDER exercise series. Army field support brigades also run logistics civil augmentation programs. These can be used to provide resources to emerging needs, including theater-wide contract and other support to theater setting and opening requirements. The relationships developed during competition with potential contract support organizations can be leveraged to meet sustainment requirements using organizations already in theater. These and other functions are integral to building and maintaining combat power for large-scale combat operations by enabling the rapid and effective arrival and employment of Army forces. (See ATP 4-98 for additional details on the Army field support brigade.)
4-86. The multi-domain task force (MDTF) provides the joint force with a formation capable of employing long-range precision fires and other effects from multiple domains in support of the commander’s objectives. It is designed to defeat complex enemy systems through the collection of information and different forms of lethal and non-lethal fires. When required, it can be task-organized to provide capabilities to the JTF or component commander. During competition, the MDTF may be forward stationed in a CCDR’s AOR to employ joint and Army capabilities in support of target development. The MDTF headquarters coordinates and synchronizes the information collection operations of its assigned formations with other theater and national assets.
4-87. The MDTF is capable of coordinating and integrating cyberspace electromagnetic activities and space capabilities with long-range surface fires to deceive, neutralize, or disrupt enemy formations, C2 nodes, and cyberspace electromagnetic activities. It does so to enable Army and joint forces to penetrate and disintegrate enemy A2 and AD enabling C2 systems and exploit the resulting freedom of maneuver. The MDTF is designed to operate in a distributed fashion while retaining the ability to deliver effects that create opportunities for joint force exploitation. Based upon specific mission variables, the MDTF may be augmented with capabilities from across the warfighting functions.
4-88. Security force assistance brigades (SFABs) provide advisors to conduct worldwide SFA operations to develop the capacity and capability of foreign security forces and their supporting institutions in support of theater security cooperation objectives. Advisors shape an operational environment by strengthening allies and building lasting partnerships. Advisors increase host-nation capability through joint exercises, and they remain ready to support the partnered force’s operations and modernization in conjunction with other instruments of national power. An SFAB improves interoperability by providing teams to advise partnernation forces across all warfighting functions. It advises at the battalion, brigade, division, and corps levels. When the SFAB is consistently employed with a partner nation, it can improve a partner-nation security force.
4-89. SFABs are regionally aligned to a specified geographic area to cultivate an in-depth knowledge and experience base capable of addressing the unique concerns of a given theater. The advisors in SFABs, in conjunction with civil affairs and theater information collection assets, enhance the common intelligence picture for a CCDR since they have direct knowledge of a partner’s force capabilities and have experience with their population. When directed, they conduct liaison and support activities to enable multinational operations during armed conflict. SFABs are uniquely manned and equipped to provide enduring presence in regions of strategic competition to promote interoperability, build partner conventional warfighting capacity, and set conditions for contingency operations. (See ATP 3-96.1 for additional details on the SFAB.)
CORPS ROLES DURING COMPETITION
4-90. When a corps is present in a CCDR’s AOR, it provides the C2 linkage between subordinate tactical echelons and theater strategic echelons. For example, V Corps oversees theater-assigned units such as the 2nd Cavalry Regiment, 12th Combat Aviation Brigade, and the 41st Field Artillery Brigade, and it oversees the employment of the MDTF assigned to U.S. European Command. During competition, it is also normal for the corps to have an expeditionary sustainment command, operational fires command, expeditionary military intelligence brigade, and a medical brigade in general support.
4-91. During exercises to prepare for large-scale combat operations, the corps fills one of three roles. The corps can be designated as tactical land headquarters employing multiple divisions. It may also assume the role of a joint task force headquarters or land component command headquarters during a contingency operation or training event, after it undergoes the necessary training and joint augmentation. When the corps is the land component command headquarters, it also serves as the ARFOR. (See FM 3-94 and ATP 3-92 for more information on the corps.)
DIVISION ROLES DURING COMPETITION
4-92. Divisions are often the primary interface with various unified action partners during competition. When regionally aligned, a division with a tailored package of subordinate brigades and other enablers—both Regular Army and Reserve Component—is allocated to a CCDR to help execute the CCP. Examples of additional enablers include maneuver enhancement brigades and civil affairs, military intelligence, military police, CBRN, psychological operations, explosive ordnance disposal, and engineer units.
4-93. A regionally aligned division normally works with multinational partners to conduct security cooperation over extended periods. By establishing habitual relationships, divisions help assure allies, build trust with partner nations, and build interoperability with them and other unified action partners. Divisions help partners build shared situational understanding and partner capacity. They also deter conflict through the conduct of various activities such as exercises, training, equipping, education, conferences, and military staff talks. Division support to security cooperation helps shape regional stability by—
Building defense relationships that promote U.S. security interests.
Developing friendly military capabilities for self-defense and multinational operations.
Providing the division and other U.S. forces with peacetime and contingency access to host nations to prevent and deter conflict.
Improving readiness to incorporate allied or partner formations.
4-94. Division headquarters provide direct C2 of the brigades tasked to conduct specific operations supporting security cooperation and interoperability development with partners. They provide training resources and oversight to brigades at home station. Division headquarters are responsible for leader development down to the battalion level. They continuously improve the readiness of Army forces over which they have influence, protecting their time and ensuring that demanding, realistic training is the first priority.
4-95. Division headquarters provide subject matter expertise to assist brigades as they prepare for missions or capstone training exercises, to include awareness of NATO or American, British, Canadian, Australian, and New Zealand (known as ABCANZ) interoperability standards when forces from those nations are involved. Low density military occupation specialties or specialized units may benefit from the division consolidation of training events. Divisions have subject matter experts in low density specialties who develop, implement, execute, and evaluate training programs across several echelons. (See FM 3-94 and ATP 3-91 for a further discussion of division roles and responsibilities.)
BRIGADE COMBAT TEAMS DURING COMPETITION
4-96. BCTs provide CCDRs with a combined-arms, close combat force that can operate as part of a division or a joint task force. During competition, they focus on perfecting tactical tasks in preparation to execute OPLANs for large-scale combat operations. Forward deployed BCTs assess and improve protection measures against adversary capabilities and promote interoperability with host-nation tactical units. While most of a rotational brigade’s training occurs in the continental United States and does not involve partnernation forces, brigades anticipate and plan how to integrate with host-nation forces. Familiarity with agreedto coalition or bilateral interoperability standards helps increase alliance or coalition capability and minimizes the time necessary for learning during execution. (See FM 3-96 for information on BCTs and FM 3-16 for information about multinational operations.)
CONSOLIDATING GAINS DURING COMPETITION
4-97. Army forces continuously consolidate gains to maintain an operational environment that is advantageous to U.S. strategic interests. Experience proves that what Army forces do during competition helps ensure stability and reduces the potential for manmade crises or armed conflict throughout a region, even in locations where no previous combat has occurred. Examples of consolidating gains during competition range from transportation system improvements (including port, airfield, and rail lines of communications), increasing theater supply stocks, intelligence cooperation, and providing Army medical personnel to support a combatant command’s humanitarian and civic assistance activities. Army forces contributing to humanitarian relief efforts with allies and partners help cement existing international relationships or set conditions for new ones in other places.
4-98. Army forces consolidate gains most effectively by maintaining a persistent or permanent presence in a theater of operations. This presence enables the cultivation of relationships on a predictable and reliable basis and provides Army forces a high degree of regular access to allies and partners. The enduring results of these activities help ambassadors, country teams, and JFCs gain a greater degree of influence with allies and partners as they pursue mutually beneficial objectives. In addition to this increased influence, Army consolidating gains activities contribute to joint efforts to support deterrence.
4-99. Consolidation of gains during competition following armed conflict or crisis is significantly different than during steady-state competition. In areas that have not seen recent armed conflict or a disruptive crisis, Army forces consolidate gains by reinforcing the success of steady-state competition activities. They do this by following through on what was begun earlier in consistent ways that provide predictability to allies and partners. In most cases, these activities will be indistinguishable from other competition activities designed to build partner capabilities and improve other advantages relative to threat forces.
4-100. Consolidating gains following armed conflict requires significant operations that, if not properly conducted, could result in a return to crisis or conflict. These efforts include information collection and intelligence analysis to understand threats, their support from the population, and what options are available to defeat them. Consolidating gains also includes stability tasks related to providing security, food, water, shelter, and medical treatment to the population. When appropriate, Army forces then work to restore or rebuild civil institutions and to transition security and stability tasks to those institutions. (See FM 3-07 and FM 3-57 for additional details on stability operations and governance.)
4-101. When immediate concerns are addressed after a crisis or armed conflict, the theater army and supporting forces focus most of their efforts on theater strategic consolidation of gains. They work with the theater’s other components, the combatant command, interagency partners (primarily the Department of State), partner nations, and other unified action partners to develop and achieve long-term objectives. In general, these consolidation of gains activities are less intense and occur over longer periods of time. Army forces build on the success of past conflicts by conducting targeted engagements with unified action partners. Examples of this include routine engagements with Republic of Korea, Japanese, and NATO forces by forward-positioned and rotational units. (See ATP 3-93 for a detailed overview of routine theater army activities to consolidate gains during competition.)
4-102. Peace operations are a means of consolidating gains. Peace operations are multiagency and multinational crisis response and limited contingency operations involving all instruments of national power with military missions to contain conflict, redress the peace, and shape the environment to support reconciliation and rebuilding and facilitate the transition to legitimate governance (JP 3-07.3). They usually occur under agreements brokered through organizations like the United Nations or through regional bodies like the African Union. (See JP 3-07.3 and ATP 3-07.31 for additional details on peace operations.)
TRANSITION TO CRISIS AND ARMED CONFLICT
4-103. Transitions are inherently complex and unpredictable because anticipated environmental conditions can quickly change and alter the perception of strategic leaders who do not have all the information necessary for clear understanding. A response by one side can result in the perception of escalation by the other, leading to increased tensions. A crisis requiring a response can also occur because of unforeseen environmental changes. Transition from competition to crisis or armed conflict is often based on four types of decisions, resulting actions, and the follow-on associated effects from the initial action. Examples include—
A decision by national command authorities to escalate or initiate armed conflict. Examples include the 2003 invasion of Iraq, the 2011 Libya strike, and the 2020 strike against Iranian General Qasem Soleimani.
A decision by adversaries to escalate or initiate armed conflict. Examples include Hezbollah’s rocket strikes against Israel in 2006, the Russo-Georgia War in 2008, and the Russian invasions of Ukraine in 2014 and 2022.
A decision by allied nations to escalate or initiate an armed conflict. An example of this is the 1967 Six-Day War that occurred between Egypt, Syria, Jordan, Iraq, and Israel.
Decisions made in response to a rapid environmental change that neither side planned for but causes tensions to rise. An example is the change brought to the strategic environment by the 2020 pandemic.
4-104. Army forces and leaders anticipate the potential for conflict in their operational environment. This is informed by input from the intelligence community and direction from strategic-level leaders. SFABs and other regionally aligned units have access to sensitive areas and ally and partner leaders. Their access and robust communications enable them to gain insight on actual conditions on the ground and provide real-time updates to decision makers during fluid situations. Decisions made before and during the initial stages of a crisis or armed conflict have significant impact on the decisions made by adversaries and the ultimate outcome of a particular situation.
4-105. Once a crisis or armed conflict starts, adversaries use all capabilities at their disposal to disrupt the deployment of Army forces. They will attempt to prevent the Army and the joint force from obtaining the needed time to deploy and build combat power. This chaos, with its resultant frictions, is the environment into which Army forces will respond.
CONFLICT TYPE DETERMINATION
4-106. Army forces and leaders need to anticipate the type of conflict the Nation will fight. This is informed by input from the intelligence community and direction from strategic-level leaders. Decisions made before and during the initial stages of a crisis or armed conflict have significant impact on the decisions made by adversaries and the ultimate outcome of a particular situation. The initial decisions or recommendations by Army strategic leaders impact the ability of the Army to project force in a timely manner.
FORCE PROTECTION
4-107. Indications and warnings in a theater may prompt a decision to mobilize and deploy Army forces in anticipation of a crisis or armed conflict. Army forces anticipate and react to adversary actions targeting them where they are located during the initial stages of an operation, whether in the United States or forward deployed. Adversaries seek to degrade and disrupt the ability of Army forces to deploy. Adversaries may employ cyberspace attacks to inflict power outages at home station, target transportation networks to delay shipment of unit equipment, conduct social media attacks on Service or family members, and instigate protests that lower popular support for Army forces. Insider threats and proxies can conduct acts of terror, sabotage, subterfuge, and other activities against U.S. forces stationed in the United States and abroad. Adversaries may immediately employ lethal capabilities against Army forces using their air-, sea-, cyber-, and space-based capabilities to exploit surprise. Forward stationed forces should be prepared to deploy from garrison to dispersed locations to prepare a defense against an enemy attack. Force protection during transition will include physical security measures, operations security, and active information efforts to counter adversary efforts to misinform and otherwise influence Soldiers, Family members, and supporting organizations and communities.
NONCOMBATANT EVACUATION OPERATIONS
4-108. A transition to crisis or armed conflict may require a noncombatant evacuation operation (NEO). Army forces conduct NEOs under a wide range of conditions. They may be conducted under relatively stable conditions or under unstable conditions that involve enemy combatants. Ideally, leaders anticipate a NEO requirement and are able to execute it prior to crisis or armed conflict. Uncertain adversary intentions and the threat of violence often create desperation amongst evacuees and local populations and increase the complexity and risk for forces conducting NEOs.
4-109. Once a NEO is requested, approved, and directed, the CCDR directs forces to conduct evacuation operations in support of the Department of State and Chief of Mission. NEOs, especially those of significant scale, will require Army forces that would otherwise be dedicated to other missions. (See JP 3-68 for more information on NEOs.)
INITIAL EMPLOYMENT OF FORWARD-STATIONED FORCES
4-110. A key strategic decision during competition or crisis is whether forward-stationed units will defend forward to hold terrain or displace to more advantageous positions. This decision should occur during competition unless a crisis unfolds in unanticipated ways and forces a decision point. During transition, forward-stationed Army forces have three courses of action. The JFC can integrate Army forces with host-nation land component forces as part of a mobile or area defense, assign U.S. Army forces a theater reserve role, or implement a plan that combines both courses of action. A theater reserve role allows the JFC to preserve Army combat power for future offensive operations. Army forces may be required to defend key terrain and infrastructure to allow for receiving deploying forces. Army leaders advise the JFC on the best ways to use forward-stationed forces based on current conditions in the AO.
Chapter 5 - Operations During Crisis
This chapter begins with a discussion of the broad trends that occur in the strategic environment and adversary actions during crisis. It discusses how Army forces provide options to joint force commanders (JFCs) seeking to obtain relative advantages during crisis, and how the Army projects forces. It then describes the roles of theater armies, corps, divisions, and brigades. The chapter concludes with a discussion of consolidating gains and transitioning back to competition or to armed conflict.
OVERVIEW OF OPERATIONS DURING CRISIS
5-1. A crisis is an incident or situation involving a threat to the United States, its citizens, military forces, or vital interests that develops rapidly and creates a condition of such diplomatic, economic, or military importance that commitment of military forces and resources is contemplated to achieve national objectives (JP 3-0). A crisis may be the result of adversary actions or indicators of imminent action, or it may be the result of natural or human disasters. During a crisis, opponents are not yet using lethal force as the primary means for achieving their objectives, but the situation potentially requires a rapid response by forces prepared to fight to deter further aggression. When directed, the Army provides a JFC with capabilities to help deter further provocation and sufficient combat power to maintain or reestablish conventional deterrence. The introduction of significant land forces demonstrates the will to impose costs, provides options to joint force and national leaders, and signals a high level of national commitment. The effects of a persistent presence on the ground among allied or partner forces cannot be easily replicated with air or maritime power alone.
5-2. Crisis response operations are characterized by high degrees of volatility and uncertainty. A crisis may erupt with no warning, or it may be well anticipated. Its duration is unpredictable. Additionally, adversaries may perceive themselves in a different context or state of conflict than U.S., allied, and partner forces. What is seen by one side as a crisis might be perceived by the other as armed conflict or competition. Army leaders must demonstrate flexibility, anticipate changes in an operational environment, and provide JFCs with credible, effective options. This requires trained forces agile enough to adapt quickly to new situations and commanders and staffs adept at linking tactical actions to attaining policy objectives.
5-3. Regardless of the capabilities employed, there are generally two broad outcomes from a crisis. Either deterrence is maintained, and de-escalation occurs, or armed conflict begins. While this requires that Army forces be prepared for either type of transition, forces deploying during crisis always assume they are deploying to fight. While Army forces prepare for armed conflict, they avoid sending signals that armed conflict is inevitable, regardless of what the adversary does, to avoid inadvertent escalation. Generally, senior leaders at the corps and higher echelons influence those perceptions through public communications in support of the JFC and national leaders.
Note. Army forces also respond to crises related to disaster response, humanitarian assistance, and defense support to civil authorities when tasked. These crisis contexts and response options are covered in separate doctrinal publications. See JP 3-28, JP 3-29, ADP 3-07, ADP 3-28, FM 3-07, and ATP 3-57.20 for more information on these types of crises and associated response options.
ADVERSARY METHODS DURING CRISIS
5-4. A crisis is frequently caused by an adversary acting aggressively to coerce and intimidate its opponents with the threat of force. Once an adversary crosses a U.S., allied, or partner crisis threshold, it attempts to shape and control the crisis to limit or prevent a U.S. military response. An adversary’s attempts to control the situation involves escalating or de-escalating its activities based on an assessment of the situation, which includes a calculation of risk. Adversary forces conduct a detailed analysis of their available capabilities, capacity, and operational reach within a theater relative to friendly forces; their overall desired end state; and their willingness to achieve that end state before deciding to escalate. Even after careful analysis, the way a situation develops can be unpredictable. Some peer adversaries view conflict as a continuous condition in which heightened or reduced periods of violence occur and recur. Changing the intensity of their actions, even when that reduces tension, does not end their campaign to oppose U.S. interests.
ADVERSARY ACTIVITIES TO SHAPE A CRISIS
5-5. As a crisis develops, peer adversaries will attempt to shape the situation to their benefit through information warfare and preclusion focused on the U.S. joint force. They may use diplomatic, economic, and information means to divide an opponent’s political leadership from its civilian population. They create separation by introducing or exacerbating distrust and division between different groups to weaken an opponent’s political leadership and to create dissatisfaction among an opponent’s civilian population. Adversaries position military forces in ways to increase uncertainty for opponents and to complicate their decision making. These activities create conditions for the adversary to exploit situations with minimal interference from the U.S., allied, or partner military forces.
5-6. Adversaries may use proxy forces to conduct information warfare, unconventional warfare, and criminal activities, although the balance and utility of these forces in crisis differs from their use during competition. Proxy forces, whether they are a militant separatist group, private military company, or criminal network, bring different capabilities to a situation, and the employment of their capabilities shifts as the strategic context changes. For example, while criminal networks can still accomplish useful tasks in environments marked by increased levels of violence, they do not have the same level of utility that they did during competition. Similarly, separatist groups cannot typically operate without significant support from their sponsor’s military or security services, and that support is likely to be focused elsewhere at the beginning of a crisis. Despite their limitations, proxy forces provide adversaries with another tool to shape a crisis situation.
ACTIVITIES TO CONTROL ESCALATION
5-7. Peer adversaries may attempt to control the escalation of a crisis to avoid armed conflict with the United States by initiating actions to prevent or counter a U.S. response. These actions may focus on allies or partners using diplomatic, information, military, and economic instruments. Adversary measures include setting fait accompli conditions on the ground designed to make military responses either too expensive to employ or too late to affect the political situation. An adversary also has other options to control escalation, which include accelerating its operational timelines, employing information warfare, increasing support to proxy forces, and increasing the number of forward deployed units in the region. Adversary forces may also initiate crises in other theaters to distract U.S. forces and diffuse their response in the area of greatest interest. In extreme cases, an adversary may conduct a limited attack in response to U.S. reactions to the activities that precipitated the original crisis.
ACTIVITIES TO MITIGATE UNITED STATES DETERRENCE
5-8. As adversary forces plan for operations during a crisis, they consider several key actions to mitigate U.S. deterrence efforts and to ensure these operations do not interfere significantly with their interests. These actions may include—
Conducting limited attacks to expose friendly force vulnerabilities. These attacks may also degrade the deterrence value of deployed forces and destroy credibility among current and potential partners.
Disrupting or delaying the deployment of Army and joint forces through cyberspace attacks and denial of space capabilities.
Exploiting gaps in national interests among the United States, partner nations, and potential partners by attacking weaker countries with whom the United States has no treaty obligations to defend.
Conducting deception operations to conceal their real intent.
Increasing the use of proxy forces to coopt, coerce, or influence the local population, organizations, and governments within a crisis region.
Creating multiple dilemmas for the United States by attacking or threatening the use of force against potential partner nations in regions outside of the crisis region.
Impacting the will of the public through information warfare, including cyberspace attacks.
Threatening the use of nuclear weapons to prevent intervention by the United States, allies, and partners.
OPERATIONS SECURITY
5-9. Operations security is vital to the success of operations during crisis. Continuously employing the operations security process generates measures and countermeasures to limit an adversary’s ability to discern friendly intent, knowing that friendly forces are always under observation and at risk of detection. Operations security is a function of how tasks and activities are conducted and how individual Soldiers and units are successful in meeting the directed standards. Army units in a joint operations area (JOA) exercise strict operations security to protect friendly information and protect the network against cyberspace attacks. They do this by ensuring no use of personal electronic devices, minimizing electromagnetic emissions, and limiting communications on command and control (C2) information systems to the maximum possible extent. This protects Soldiers from social media and other information-related attacks and limits the information available to adversaries that can be used to target family members. It also makes it more difficult for adversaries to identify units and their locations and reduces the incentive for adversary forces to strike targets they view as lucrative enough to risk conflict to destroy. Stress caused by adversary social media attacks during crisis is potentially circumvented by avoiding social media altogether, since the combined effects of a disinformation campaign could degrade Soldier performance and morale far more than not having access to personal devices and media accounts. Operations security is a continuous activity at every echelon down to the individual Soldier level.
RELATIVE ADVANTAGES
5-10. During crisis, Army forces capitalize on the knowledge and experiences gained and use the systems, processes, and infrastructure developed while setting the theater to respond to adversary aggressions or threats. While this preparation and experience provide Army forces, allies, and other coalition forces with a good starting point in mature theaters, the transition into crisis will most likely be chaotic, and it will present Army leaders with unforeseen challenges that require rapid response. Army forces therefore build upon the information, human, and physical advantages gained during competition to mitigate friction, deter adversaries, and when necessary, transition into armed conflict.
PHYSICAL ADVANTAGES DURING CRISIS
5-11. Achieving physical advantage during crisis consists of working with host-nation forces to form a credible defense and ensuring the survivability of allied forces in theater. If there is key or decisive terrain, Army forces and host-nation partners may seek to deter adversaries by setting a defense of that ground early in a crisis. Army forces in theater assume conflict is imminent and take all available measures to protect against attack in every domain where an attack could occur.
5-12. During crisis, Army combat power will likely be limited initially to a small number of forwardstationed forces, those forces that can draw Army pre-positioned stocks (APS) rapidly, and forces used to threaten adversary forces with forcible entry into their area of operations (AO). This combat power will most likely be used in a defensive posture until the JFC receives enough land forces to make offensive operations feasible. The intent should be to increase the combat power of Army forces to a point where they can credibly threaten adversary forces with offensive operations. Ideally, this will deter further enemy action. If, however, deterrence fails, this force facilitates armed conflict that will terminate on terms favorable to U.S. interests. In well-developed theaters, Army combat power will likely be forward stationed and integrated with partner forces as a key part of their defensive plans. This credible land force, capable of disrupting or significantly degrading an adversary’s initial attack, maximizes the deterrent potential of Army forces.
INFORMATION ADVANTAGES DURING CRISIS
5-13. Two key information activities are protecting friendly information and degrading the threat’s ability to communicate, sense, make effective decisions, and maintain influence with relevant actors and populations. An example is the use of strategic messaging to undermine the credibility of an adversary by exposing violations of international law and showing that adversary narratives are false. Achieving information advantages is a commander-driven, combined arms activity that employs capabilities from every warfighting function. During crisis, commanders lead their staffs to refine information activities based upon plans and processes developed during competition. Examples include commanders and staffs focusing on the challenges and tasks of establishing a mission-partner environment, building or modifying an intelligence architecture, and creating or refining common operating procedures with allies and other partners.
HUMAN ADVANTAGES DURING CRISIS
5-14. While enduring relationships with alliance and coalition partners may be in place at the theater strategic level as a crisis develops, at the operational and tactical levels it is likely that units have less experience operating with one another. Forces deploying into a theater may have experience working with the security forces of partner nations if they were regionally aligned or worked together in a professional military education or training setting, but most will not have such experience. This requires leaders who have worked with joint and multinational partners to focus their staffs on the most critical interoperability tasks necessary for effective coalition operations. It also requires awareness of the difficulty in fully understanding situations when dealing with other cultures. Employing the liaison networks built by the theater army during competition will enable simultaneous in-theater training exercises with the deployment of Army forces. This facilitates early shared understanding, helping leaders and subordinate units integrate with allied and partner forces in the most expeditious and efficient manner possible while also signaling determination to adversaries. Demonstrated readiness for combat operations and interoperability among U.S., allied, and partner forces helps to upset adversary risk calculations and deter further aggression.
ARMY SUPPORT TO THE JOINT FORCE DURING CRISIS
5-15. The military supports unified action partners during crisis by providing flexible deterrent and response options. A flexible deterrent option (FDO) is a planning construct intended to facilitate early decision making by developing a wide range of interrelated responses that begin with deterrent-oriented actions carefully tailored to create a desired effect. A flexible response option (FRO) is a military capability specifically taskorganized for effective reaction to an enemy threat or attack and adaptable to the existing circumstances of a crisis. FDOs and FROs occur across the diplomatic, informational, military, and economic (known as DIME) instruments of national power, and they are not just confined to the military. They are most effective when integrated and implemented in a nearly simultaneous manner. Examples of simultaneous FDO and FRO actions are shown in figure 5-1. (See JP 5-0 for additional examples of diplomatic, economic, information, and joint force FDOs and FROs.)

5-16. Determining what threat and enemy forces perceive as important will inform U.S. understanding of their desired end state, associated courses of action, and employment of forces. This allows strategic leaders to determine the appropriate amount of military force to apply in concert with diplomatic, information, and economic activities to prevent adversaries from achieving their objectives. Examples of Army contributions that can deploy rapidly to support joint flexible deterrent and response options are contained in table 5-1 on page 5-6.
| Command and control headquarters—establishment of a field army or deployment of a corps or division. |
| Air defense to protect key infrastructure and population centers from theater ballistic missiles. |
| Additional personnel to expand the capability of theater-assigned headquarters. |
| Intelligence assets to support situational understanding, targeting, and information activities. |
| Deploying a security force assistance brigade to establish liaison capability or conduct security force assistance. |
| Building or expanding infrastructure and increasing sustainment capacity to facilitate reception, staging, onward movement, and integration. |
| Airborne or air assault units positioned to conduct joint forcible entry. |
| A brigade combat team drawing Army pre-positioned stocks. |
| Port opening to receive the joint force. |
| Multi-domain task force to respond to adversary antiaccess and area denial activities. |
| Special operations forces to conduct foreign internal defense, direct action, or special reconnaissance. |
| Civil affairs to enable civil-military operations and interorganizational cooperation. |
| Chemical, biological, radiological, and nuclear units for response to weapons of mass destruction employment. |
5-17. While FDOs are primarily intended to prevent a crisis from developing or worsening, FROs are designed to preempt or respond to attacks against U.S. interests. FDOs are preplanned, deterrence-oriented actions carefully tailored to bring an issue to early resolution without armed conflict, and they can be initiated before or after unambiguous warning of threat action. In comparison, FROs can be employed in response to aggression by adversaries, and they are intended to facilitate early decision making by developing a wide range of actions carefully tailored to produce desired effects. FDOs and FROs must be deliberately tailored in terms of timing, efficiency, and effectiveness to avoid undesired effects, such as eliciting an armed response should adversary leaders perceive that friendly FDOs or FROs are being used as preparation for a preemptive attack.
5-18. FDOs and FROs serve three basic purposes. First, they provide a visible and credible message to adversaries about U.S. will and capability to resist aggression. Second, they position U.S. forces in a manner that facilitates implementation of the operations or contingency plan should armed conflict occur. Third, they provide options for joint and national senior leaders. They allow for measured increases in pressure to avoid unintentionally provoking combat operations, and they enable decision makers to develop the situation to gain a better understanding of adversary capabilities and intentions. FDOs and FROs are elements of contingency plans executed to increase deterrence in addition to, but outside the scope of, the ongoing joint operations. The key goals of FDOs and FROs are—
Communicate the strength of U.S. commitment to treaty obligations and regional peace and stability.
Confront adversaries with unacceptable costs for their possible aggression.
Isolate adversaries from regional neighbors and attempt to split adversary coalitions.
Rapidly improve the military balance of power in the theater of operations without precipitating an armed response from adversaries.
Develop the situation and better understand adversary capabilities and intentions.
5-19. Leaders exercise restraint and carefully calculate risk before recommending an increase in Army forces to address a crisis. Peer adversaries have global capabilities, and they can create multiple dilemmas for U.S. forces by escalating a crisis horizontally in a different theater. Surging forces in one region may address a crisis, but it potentially creates opportunities for adversaries or enemies in another region. Leaders must anticipate second- and third-order effects on other combatant commands and the risk to the homeland when forces are committed to address a specific crisis. An example of an effective response operation occurred in Korea in 1976.
On 18 August 1976, a North Korean platoon-sized force attacked a small element of U.S. and South Korean Army forces conducting a routine tree trimming detail in the Joint Security Area, a location set aside for military talks and jointly secured by forces from both the U.S.-led United Nations Command and North Korea. The North Koreans murdered two U.S. officers and wounded five South Korean soldiers, escalating the already tense security arrangement.
Leaders assessed that the act was an attempt to dissuade American support for the U.S. military presence in South Korea. U.S. leaders considered multiple response options. Although some advocated for a swift and lethal response, the U.S.-led alliance implemented a course of action designed to avoid escalation but demonstrate allied cohesion and resolve.
Three days after the attack, dozens of U.S. and South Korean forces reoccupied the same site where the unprovoked attack occurred and cut down the tree. As a show of force and coalition readiness, hundreds of U.S. and South Korean soldiers provided overwatch for the work detail. Army forces also deployed attack helicopters and prepared artillery for use if necessary. This show of force was part of a larger joint response option. President Ford ordered U.S. forces to Defense Condition Three, deployed strategic bombers, and deployed a U.S. aircraft carrier.
The operation de-escalated the situation while bringing attention to North Korea’s malign activity, further isolating North Korea from the international community. The operation compelled the North Koreans to admit they regretted the incident, and they agreed to separate forces in the joint security area. The response resolved the incident with stronger international support for the United Nations’ mission and a stronger bond between U.S. and South Korean forces.
FORCE PROJECTION
5-20. The demonstrated ability to project Army forces into an operational area is an essential element of conventional deterrence. Army forces depend almost entirely upon joint lift capabilities for deployment. Force projection is the ability to project the military instrument of national power from the United States, or another theater in response to requirements for military operations (JP 3-0).
5-21. During a crisis, ground forces provide a JFC with more enduring options than forces primarily concentrated in or transiting other domains. Army forces are capable of occupying ground indefinitely. They must be sustained just like other Services, but the Army’s ability to maintain persistent presence is far greater because of the nature of operations on land. The potentially close physical proximity of ground forces to adversary forces provides the JFC with greater understanding and can help the JFC dictate the tempo of operations.
5-22. Army forces achieve persistent presence by deploying forces into a theater to support forward-stationed U.S. forces, or those of allies or partners. These forces are likely already executing operations directed in response to provocations, indications, or warnings that hostile activities may commence. At the direction of the JFC, Army forces execute tasks, activities, and operations designed to deter further malign activity and set conditions for success should deterrence fail. The forward presence or projection of Army formations into a theater provides capabilities that create tactical and operational dilemmas for threat forces, enabling the JFC to seize and retain the initiative. Prompt deployment of land forces in the initial phase of a crisis can preclude the need to deploy larger forces later, and it assures allies and other partners. Effective early intervention can also deny adversaries the time necessary for them to set conditions in their favor.
5-23. Deployment alone does not guarantee success. Achieving successful deterrence involves convincing adversaries that the deployed force is able to markedly reduce the adversary force’s chance of success during armed conflict. Adversaries measure the ability of Army forces to conduct operations during armed conflict through careful observation of how well those forces are prepared to conduct large-scale combat operations and the capabilities those forces introduce into a specific context as part of the overall joint response.
5-24. As Army forces prepare to respond to a crisis, the JFC conducts a final review of deploying forces, ensuring they are deployed in the proper sequence and are able to be task-organized effectively for the anticipated mission. Threat forces are likely to detect force projection activities using space and cyberspace capabilities, human intelligence, and open-source collection efforts. Planners should anticipate adversary forces using all available means to contest the deployment of forces, beginning from home station, during transit, and upon arrival in theater. Therefore, operations security, dispersion of forces, deception operations, and physical security are critical planning considerations. Senior commanders and planners must understand the risks and shape deployments to satisfy both speed and operational readiness. (See Chapter 3 for more information on force tailoring and Appendix C for further discussion on contested deployments.)
5-25. Force projection is particularly important during crisis, as Army forces have an unknown amount of time to shape a developing situation. It can occur, however, in any context. Forces projected forward during competition to conduct exercises, bolster allies and partners, and conduct other activities are under observation. Adversaries assess the speed and efficiency of these routine deployments, which can have a deterrent effect. Given the fluid nature of a crisis, force projection may continue well after a crisis has transitioned to armed conflict. Sound force projection planning encompasses—
Opening the theater.
Mobilization.
Deployment.
Protection during transit.
Reception, staging, onward movement, and integration (RSOI).
Initial employment of forces.
Sustainment.
Redeployment.
OPENING THE THEATER
5-26. During the transition to crisis or armed conflict, Army forces open the theater to receive deploying forces. Army forces execute existing plans to establish and open air, sea, and rail terminals. Distribution systems and intermediate staging bases may be established where required. Higher echelon (including theater, corps, and division enablers) and rapidly deployable C2 elements begin to integrate with host-nation forces as quickly as possible to set the conditions for RSOI of follow-on tactical forces. This includes coordination with the forces of other supporting nations to assure effective distribution of services, facilities, and supplies to all deploying units across the alliance or coalition. During theater opening, designated arriving forces draw available APS. This provides the JFC with increased capacity and capability during the initial stages of a crisis or armed conflict. Army forces must be prepared for combat while conducting theater opening operations. The first deploying units require the capability to defend themselves while they provide reaction time and maneuver space for follow-on forces.
MOBILIZATION
5-27. Mobilization is the process by which the Armed Forces of the United States, or part of them, are brought to a state of readiness for war or other national emergency (JP 4-05). During mobilization, the Army focuses its efforts on filling joint manning documents to augment combined and joint task force (JTF) headquarters, land component headquarters, and Army units designated for deployment. During crisis, strategic leaders may decide to mobilize select portions of the U.S. Army National Guard and U.S. Army Reserve to provide key capabilities to JFCs. During armed conflict, it is likely that strategic leaders will remove some or all mobilization limitations, enhancing the Army’s ability to respond to an aggressive act by an enemy with the necessary capabilities. An example of a limitation that is lifted for armed conflict would be ordering a full mobilization of the Army National Guard or Army Reserve in lieu of a selected reserve call up or partial mobilization.
5-28. Despite the rapid response and expeditionary capabilities of the joint force, no amount of expeditionary capability can overcome the challenges posed by physical distance. Most Army forces tasked to respond to a crisis have a delay between notification and the time they assemble at the location from which to deploy. For active-duty formations this time period is generally days or weeks, and for Army National Guard or Army Reserve forces this time period is generally weeks to months. The mobilization process takes longer for units with large amounts of equipment and personnel.
5-29. Some units are directed to maintain higher levels of readiness or maintain a prepared-to-deploy status. This higher state of readiness primarily includes units in the immediate response force. The immediate response force provides the Army with the ability to provide combatant commanders (CCDRs) with land capabilities of limited capacity to rapidly respond to a crisis.
5-30. For most Army forces, mobilization operations begin at home station. As a general rule, once mobilized, it takes at least 30 to 45 days for most Army forces stationed within the United States to deploy to a theater when their equipment is shipped via strategic sealift. This planning timeline is the same whether the United States is involved in a crisis or armed conflict due to the fixed speed of moving Army equipment over civilian transportation infrastructure. However, if a threat force inflicts significant damage across the strategic support area during armed conflict, these timelines may be further extended. This timeframe does not include RSOI upon arrival overseas. Additional time may also be required if the joint force is not able to provide sufficient capacity to protect land, sea, and air lines of communications or sufficient sea and airlift is not available for simultaneous movement of multiple large units. (See Appendix C for more information on deployments contested by threat forces.)
DEPLOYMENT
5-31. Deployment is the movement of forces into and out of an operational area (JP 3-35). Proper planning establishes what, where, and when forces are needed to achieve objectives. How the JFC intends to employ forces is the foundation of the deployment structure and timing. For example, a JFC may deploy a combatready brigade combat team (BCT) or division early in a crisis to stabilize a situation or secure ports for follow-on forces, accepting risks to the movement efficiency of follow-on forces. Corps and division staffs examine all deployment possibilities and conduct parallel planning.
5-32. Most Army equipment travels via strategic sealift. It will take weeks or months for the equipment to arrive in theater. Commanders and planners must not underestimate the joint deployment challenges of operating against peer adversary forces with robust air, maritime, space, and cyberspace capabilities. Commanders and planners must envision what they want the force to look like upon arrival in theater and then backwards plan with the assumption that some of it may not arrive as planned or even at all. The objective of deployment planning is to synchronize deployment activities to facilitate effective execution of operations in an operational area. Successful deployment planning requires knowledge of a unit’s deployment responsibilities, an understanding of deployment, and an appreciation of the link between deployment and employment. (See ATP 3-35 for a discussion of these deployment phases and planning in detail.) The steps used in deployment planning are—
Analyze the mission.
Structure forces.
Refine deployment data.
Prepare the force.
Schedule movement.
An example of deployment friction and unit actions to overcome it occurred in 2003.
In 2003, Task Force Ironhorse initially shipped its unit equipment sets to Turkey as called for in the initial invasion operations order. However, the equipment sets had to be rerouted through the Suez Canal and Kuwait after Turkey did not allow the use of its territory for the invasion of Iraq. The task force concept of operations called for tailored force packages that would allow rapid employment upon arrival in Turkey. However, tailoring the force packages precluded the ability of U.S. Transportation Command to maximize the available square footage of strategic sealift ships. This degraded the ability of the JFC to receive additional assets. Additionally, the refusal of Turkey forced the task force commander, Major General Odierno, to rapidly develop new courses of action for forces tailored for an operation that was no longer feasible. Though friction occurred due to the extreme change in conditions, the unit adapted. It did this while constantly interfacing with organizations at the strategic and theater strategic levels. Major General Odierno also ensured that all leaders of his task force were integrated into the plan as it changed. As a result of these efforts, Task Force Ironhorse had personnel staged in Kuwait, prepared for the new conditions facing them when their equipment finally arrived in Kuwait.
PROTECTION DURING TRANSIT
5-33. The U.S. Army Installation Management Command is a critical protection enabler during unit predeployment activities through the fort-to-port movement of Army forces. This command manages most Army installations, and garrison commanders ensure the protection of forces as they deploy. Installation provost marshals protect deploying unit assets as they prepare to deploy with police and security guards. In addition, installation safety, medical, and information management personnel protect the force during deployment preparation and execution. Corps and division staffs coordinate closely with installation staffs to identify information and assets that need protection, and they apply appropriate protection and security measures consistent with their collective threat analysis.
5-34. Threats may attempt to impede or prevent unit deployments. This creates a requirement for coordination of the physical security of deploying unit personnel and equipment as they move to ports of embarkation. Physical security is required for personnel and equipment while awaiting transport at ports of embarkation, during movement, and after arrival at ports of debarkation. Planning for physical security remains a focus in unit staging areas, along routes upon which units and supplies move, and for tactical assembly areas prior to onward movement into AOs.
5-35. U.S. Transportation Command and the Military Surface Deployment and Distribution Command administer a defense transportation security program to provide standardized transportation security measures and procedures, constant oversight, and central direction in coordination with other Department of Defense (DOD) activities and port authorities. Commanders plan for protection measures for their units and equipment from home station to the port of embarkation, while Military Surface Deployment and Distribution Command coordinates for security within the port.
5-36. Corps and division staffs ensure that all contract processes for transportation movements meet DOD security requirements. They coordinate with the installation transportation officer in the continental United States at home station or the movement control team outside the continental United States and authorized railroad or commercial truck carriers on guard and escort matters. Some government and commercial carriers provide limited security measures to protect in-transit equipment and supplies. These measures include the use of contract security personnel and secure transfer facilities to safeguard unit assets.
5-37. If the corps or division staff determines that carrier security measures are insufficient given the threat, corps and division headquarters have a number of options for increasing the protection and security of deploying units and their associated equipment and supplies. These options include directing subordinate units to provide Soldiers to guard equipment and supplies throughout the deployment process. Commanders can also direct units to have Soldiers carry certain sensitive items as part of their individual loads throughout the deployment process.
5-38. Corps and division commanders submit protection plans before their arrival overseas through the respective ARFOR or the theater army headquarters to the CCDR responsible for all military forces in the AOR within which deploying forces will operate. These plans should align with the guidance developed by the CCDR, who coordinates and approves various deploying unit protection plans.
RECEPTION, STAGING, ONWARD MOVEMENT, AND INTEGRATION
5-39. RSOI is the process that delivers combat power to the JFC in a theater of operations or a JOA. RSOI is the responsibility of the theater army and its associated theater sustainment command (TSC). During crises involving a peer adversary, RSOI must occur rapidly in as many dispersed locations as possible to complicate adversary targeting. It is a theater-level process, with careful coordination required between units, theater sustainment personnel, host-nation support, and commercial entities. Effective RSOI matches personnel with their equipment, minimizes staging and sustainment requirements while transiting these ports of debarkation, and begins onward movement as quickly as possible. Deploying units need to understand and implement previously developed plans to accomplish integration and maintain combat readiness upon their arrival. (See JP 3-35 and ATP 3-35 for a discussion of factors and considerations associated with the conduct of RSOI.)
5-40. Reception is the process of receiving, offloading, marshalling, accounting for, and transporting of personnel, equipment, and materiel from the strategic and/or intratheater deployment phase to a sea, air, or surface transportation point of debarkation to the marshalling area (JP 3-35). As the initial step of introducing combat power on the ground, reception determines success or failure of the RSOI operation. Efficiency imparts speed, which requires well-understood plans flexible enough to overcome friction.
5-41. The theater army or a designated sustainment unit (typically the assigned TSC) implements reception from strategic lift activities at or near designated air and seaports of debarkation. While the reception plan for each theater varies, reception capacity should at least equal planned strategic lift delivery capability. At a minimum, the theater army considers the impact of joint C2, movement control, and port operations while planning. Additionally, commanders and their staffs consider dispersion, air and missile defense (AMD), and other security measures when planning and conducting reception operations based on the vulnerability to enemy special-purpose forces and long-range fires.
5-42. Staging is assembling, holding, and organizing arriving personnel, equipment, and sustaining materiel in preparation for onward movement (JP 3-35). Staging is the part of the RSOI operation that unites unit personnel with their equipment and prepares them for onward movement and employment by the JFC. During staging, deploying forces have limited mission capability and are generally not self-sustainable. Most units require extensive maintenance, supply, protection, and life support while staging. In some cases, their equipment must be reconfigured following transport on ships or aircraft.
5-43. Onward movement is the process of moving forces and sustainment from reception facilities and marshalling or staging areas to tactical assembly areas or other operating areas. Many external factors influence onward movement. They include the availability of transportation assets and the requirements of their future higher echelon headquarters. These factors determine the sequence in which units move from their staging areas onward to their respective AOs. Plans for the movement of a corps or division headquarters and its attached and supporting divisions or brigades into an AO maintain a balance between security and flexibility.
5-44. Corps and division commanders rely heavily on their staffs and integrating cells to finish coordinating their movement plans to their projected AOs with all necessary military and civilian agencies. The logistics distribution network may be operated by the U.S. military, the host nation, or by a combination of military and civilian agencies. The appropriate staff cells and elements consider the number of suitable routes and lift assets available to meet the movement requirements of subordinate units. Other considerations include—
Construction of routes.
Road and route improvement and maintenance.
Repair of bridges and culverts.
Clearance of obstacles, including explosive hazards.
Bridging rivers or dry gaps.
Establishment of security along routes.
Placement of convoy support centers.
Traffic control to permit freedom of or restriction of civilian movement along routes.
Communications architecture.
Requirements of allies and other partners moving at the same time as U.S. forces.
5-45. In the context of RSOI, integration is the coordinated transfer of units into an operational commander’s force prior to mission execution. It can start as soon as the JFC and the new unit are aware of the mission. The JFC may provide initial and periodic situational updates to the inbound unit throughout the force projection process. The JFC may have training requirements for the deploying unit that it must accomplish before and upon arrival in the theater. Integration occurs across all warfighting functions. Generally, the more time a unit has to integrate before conducting operations, the better the unit will perform. However, the situation may require rapid integration. Therefore, commanders balance the risks to mission and force when determining the tempo of unit integration.
5-46. When a deploying unit replaces another unit, a relief in place occurs during integration. During crisis integration of deploying forces will probably involve augmentation of U.S. and host-nation forces already in position, and not require a relief in place, although establishing liaison with units on the flanks is required. Regardless of the circumstance, the command of combat-ready units is transferred to the receiving commander during integration. Integration is complete when the CCDR, other JFC, or land component commander establishes positive control over arriving units. This usually occurs in forward assembly areas when those units are capable of performing missions.
5-47. If the deploying division or brigade is the first U.S. force into a JOA, there may be a need to deploy an advance party task-organized with security, protection, logistics, and engineering support capabilities. As part of the unit movement preparations, the advance party is resourced from the division, brigade, attached assets, or it is provided by outside units. This is particularly true if the predeployment site survey determines that the AO does not have sufficient infrastructure to support division or brigade operations. Changes in the number of available forces as deployment proceeds will also increase the number of units present and change disposition of units and the dimensions of AOs. In circumstances demanding more experienced leadership, it may be necessary for the deputy commander and a select staff to lead this advance party. They set the groundwork for the rest of the unit by performing face-to-face coordination with local military or civilian leaders.
5-48. Unit deployment operations end when all deploying elements complete their RSOI within the assigned JOA. The specifics of RSOI reflect the specific circumstances of the operational and mission variables prevailing in that JOA. (See JP 3-35 for information on joint RSOI requirements.)
INITIAL EMPLOYMENT OF FORCES
5-49. The initial employment of Army forces during a crisis will most likely be as part of FDOs or FROs. This employment may represent the opening stages of a joint operation or a show of force demonstration. The objective of this early employment is to deter an adversary from further aggression, expand the theater to receive follow-on Army and joint forces, and form a credible defense with host-nation forces to prevent adversary gains. Without a robust theater infrastructure, a large number of forward-stationed forces, or a robust APS inventory that enables rapid deployment, Army forces can only provide limited support to partner forces. While immediate support may be limited, even limited support could prove decisive when it is obvious that additional capabilities are quickly moving into the theater to address initial shortfalls.
SUSTAINMENT
5-50. Sustainment is central to force projection, and sustainment preparation of an operational environment is the basis for sustainment planning. Corps, division, and brigade planners focus on identifying the resources available in an operational area for use by friendly forces and ensuring access to them. The theater army is a key partner in providing this information to deploying units. A detailed estimate of requirements allows planners to advise the commander of the most effective method of providing adequate and responsive support, while minimizing the vulnerable sustainment footprint. There is no fundamental difference in sustainment preparation of an operational environment during competition, crisis, or armed conflict, except that sustainment activities intensify as Army forces respond to crisis and prepare for armed conflict, since time available decreases and requirements from risks to units on the ground increase exponentially. Proper sustainment permits the Army to project force over time and through the necessary depth of an AO. (See FM 4-0 for more information on sustainment.)
REDEPLOYMENT
5-51. Redeployment is the transfer or rotation of forces and materiel to support another commander’s operational requirements, or to return personnel, equipment, and materiel to the home and/or demobilization stations for reintegration and/or out-processing (JP 3-35). National strategic leaders determine the appropriate time for the redeployment of Army forces. Usually, redeployment of Army forces does not occur until tensions reduce and conditions permit the transition of security and stability responsibilities to other legitimate authorities.
ARMY ECHELONS DURING CRISIS
5-52. All Army echelons have considerable responsibilities when responding to a crisis. Each conducts reconnaissance, liaison, and troop preparation. As units deploy, they may send leaders and staffs to other headquarters and to ports and airfields to refine their understanding of requirements and the situation on the ground. Deploying units can expect their leaders to be called to outside planning meetings early in the process and for special training needs to emerge even as units are busy with other preparations for movement. Units can expect to receive individual replacements or augmentees and a number of attachments based on task organization.
THEATER ARMY ROLES DURING CRISIS
5-53. The theater army commands all Army forces in the AOR until the CCDR attaches selected Army forces to a subordinate JTF. Until another organization can assume the role, the theater army initially divides its responsibilities between the Army component (the ARFOR) in the JOA or theater of operations and Army forces operating in other parts of the AOR. This may require force tailoring by the theater army to develop the initial request for forces, followed by additional task organization as forces arrive in the AOR. The theater army is able to perform as a JTF or combined forces land component command headquarters for limited contingency operations and during the initial period of a crisis. It requires rapid augmentation to conduct continuous operations in either case.
5-54. As the Service component command, the theater army remains responsible to Headquarters, Department of the Army for service-specific requirements within the AOR during a crisis. This falls under the ADCON chain of authority. This authority establishes a hierarchy for Army support to deployed forces without modifying the operational chain of command that runs from the CCDR through subordinate JFCs. For example, theater army commanders may—
Lead RSOI operations for arriving forces.
Complete collective training, theater orientation, and theater acclimation.
Manage force modernization of Army forces before their employment in the JOA.
5-55. During joint operations sustainment is a Service responsibility except as specified by executive agency requirements, DOD directives, CCDRs’ lead Service designations, or inter-Service support agreements. CCDRs direct theater army commanders to provide Army support to other Services (ASOS) to agencies or multinational forces when required. However, shared sustainment responsibility or common-user logistics is more effective, especially for joint operations. Directive authority for logistics is the additional authority available to CCDRs to eliminate duplicative or overlapping sustainment responsibilities. The theater army coordinates with the combatant command staff to determine joint sustainment requirements, identify responsibilities, and enable commanders to exercise sustainment C2. (See ATP 3-93 for additional details on the theater army.)
CORPS ROLES DURING CRISIS
5-56. During crisis, the corps headquarters may deploy into an operational area as a tactical headquarters with subordinate divisions and brigades. Corps typically deploy an early entry command post, comprising selected personnel from within the headquarters, to provide C2 of arriving forces. Should crisis become armed conflict, large-scale combat operations may require the corps headquarters to function under the command of a multinational force land component or become subordinate to a field army equivalent established as part of a multinational coalition.
5-57. Corps headquarters plan for all phases of an operation from mobilization to redeployment. Corps operations require planners to consider all functions and capabilities required to gain and maintain positions of relative advantage and the capabilities threat forces can use against friendly forces. Understanding the planning and execution timelines of various capabilities is critical when considering the integration of those capabilities into the overall plan. The corps headquarters is responsible for—
Understanding the threat.
Integrating information collection and intelligence analysis into the next higher echelon’s - processes and systems.
Establishing liaison with its higher headquarters and planning reconnaissance of its initial - assembly areas, routes, and forward assembly areas.
Assigning subordinate units areas of operations.
Identifying multiple routes from the points of debarkation through assembly areas to staging areas.
Establishing an initial concept of operations.
Planning to consolidate gains.
Coordinating cyberspace attack mitigation, including distributed denial of service, malicious - software, or system intrusion.
Planning and preparing for communication denial and degradation.
Planning for dispersion of subordinate units along routes and within assembly areas.
5-58. Per the deployment order and operation plan (OPLAN) or operation order, the corps staff plans task organization and employment of subordinate units, integration and synchronization of operations, massing of effects, allocation of resources, and determination of priorities. The corps staff provides the primary Army interface to manage the time-phased force and deployment list for all its assigned forces. The corps determines when its command posts will arrive at a port of debarkation in relation to the arrival of protection, sustainment, and maneuver units.
5-59. A corps commander can influence, but not dictate, the tailoring of subordinate units. The CCDR, theater army, supporting combatant commands, U.S. Transportation Command, and U.S. Army Forces Command all make decisions concerning the composition and deployment sequence of the corps. A corps commander can, however, organize and prepare the corps command posts for efficient and effective movement throughout a deployment. By selecting personnel with the right skill sets and providing them the right mix of equipment, the commander, chief of staff, and assistant chief of staff, operations, match corps C2 capabilities with mission requirements.
5-60. Assigning initial staging areas, movement routes, and subsequent assembly areas in uncertain threat conditions requires a calculated balance between force protection and building combat power. Staging areas for subordinate division and separate brigade elements should be large enough for divisions and separate brigades to disperse elements into company-sized tactical formations while they are performing maintenance checks, loading munitions, ensuring crew readiness, and preparing to move to forward positions. These plans may change frequently as new forces arrive, and they will need to be modified for every stage of deployment. (See ATP 3-92 for additional details on corps operations.)
DIVISION
5-61. The division headquarters performs many of the same activities as the corps headquarters. The division headquarters fulfills its primary role as a tactical headquarters staffed, trained, and equipped to command two to five BCTs and other subordinate brigades and battalions. One or more of these brigades may be allied formations. Upon deployment into a theater, a division may undergo significant task organization in preparation for its assigned roles during operations. Initially, during crisis, a division conducts defensive, security, and stability tasks in support of joint operations. The primary role of a division during crisis is to demonstrate credible coercive force as a combined arms formation. Divisions should expect to conduct short notice training exercises with multinational partners and perform other activities that demonstrate capabilities as part of crisis response. In an immature theater, a division headquarters should be prepared to accommodate the command structure of the next higher echelon until that echelon’s systems are in place. (See ATP 3-91 for additional details on division operations.)
BRIGADES
5-62. During crisis, brigades provide strategic leaders and JFCs with an alternative to deploying a corps or division. If strategic leaders or the joint force require a credible and rapidly deployable deterrent during an escalating crisis, they may decide to deploy a BCT, functional brigade, multifunctional brigade, or a combination thereof as part of a FDO or FRO. To conduct an effective FDO or FRO a brigade could be given prepare-to-deploy orders or conduct emergency deployment readiness exercises. Other options include moving brigades operating in a theater to dispersed locations with improved survivability that are advantageous for defense or integrating these forces into the area or mobile defensive plans of partner nations. If there is no corps or division present in the theater, the theater army provides C2 of the brigade. An example of a BCT rapidly deployed as an FRO occurred in 2019 in Iraq.
On 31 December 2019, during a time of heightened tensions with Iran, an initial wave of 750 paratroopers from the 82d Airborne division assigned to the immediate response force deployed to Baghdad to provide additional security. This deployment was in response to an attack that occurred on the U.S. embassy 18 hours earlier. The remainder of the Soldiers in the brigade deployed within days. In total, 3,000 Soldiers provided additional security at the embassy for almost two months. While forward deployed, the Soldiers continued training to demonstrate readiness, and they were postured to rapidly respond at the CCDR’s direction.
CONSOLIDATING GAINS
5-63. During and after crisis response, Army forces consolidate gains to deny adversary forces the means to extend the crisis or create a similar crisis in the future. This will often entail maintaining an enhanced force posture in a JOA for a period of time to demonstrate U.S. willingness to defend allies and partners. Army forces continue to support improvements to host-nation capabilities through a security cooperation plan designed to make them less vulnerable to future crisis. If an adversary directly targets partner forces, or acts through a proxy, the United States must be prepared to reconstitute the partner’s forces as quickly as possible. The ability of Army forces to reconstitute partner nation forces is especially important to JFCs since, in many areas, only the Army has the capacity to conduct a comprehensive security cooperation program. Many allies and partners rely primarily on their armies and do not have robust navies or air forces. Consolidating gains during and after crisis response creates enduring change that reinforces deterrence against adversaries and improves relative advantages for U.S., allied, and partner forces.
TRANSITION TO COMPETITION OR ARMED CONFLICT
5-64. There are two outcomes of a crisis—a de-escalation to competition or an escalation to armed conflict. Transitions are typically points of friction. Commanders emphasize information collection prior to and during transitions to maintain a detailed understanding of the threat and continuously assess the situation in order to position their forces to retain the initiative.
TRANSITION BACK TO COMPETITION
5-65. During a crisis, partner nation security forces and government institutions may suffer losses that reduce capability and capacity due to the actions of adversary or proxy forces. Army forces may be tasked to execute security cooperation programs to help restore or maintain partner nation capabilities and capacity as a means to consolidate gains. Army forces seek to restore partner security forces and government institutions as quickly as possible to maintain popular support. Doing so reduces the need for large numbers of U.S. forces to deploy in the future or be maintained in theater to support or enable a partner nation’s security. A quick recovery also highlights the strength of the alliance or bilateral relationship of a partner nation with the United States. (See Chapter 4 for more information on partner nation capabilities and capacity.)
5-66. Army forces use products developed from the civil preparation of the environment to help rebuild partner-nation security forces. Army forces work with partner nations to do this and do not act unilaterally. The security force assistance brigade (SFAB) and civil affairs units are the ideal core for this effort, but all types of Army units may contribute. When the effort is large and there is a need for additional subject matter expertise, or there is a need to reconstitute host-nation conventional forces, additional Army forces may be required. (See JP 3-20 and FM 3-57 for more details on security cooperation and civil affairs operations.)
5-67. Army forces may help the JFC exploit favorably resolved crises to establish new patterns of behavior for a theater. While crises are generally uncertain and volatile, their resolution and resulting transition back to competition provide opportunities to capitalize on changes in an operational environment. Army forces support joint efforts to create and reinforce changes that benefit the United States and its allies and partners in competition and provide improved relative advantages that assist in deterring future adversary malign behavior.
TRANSITION TO ARMED CONFLICT
5-68. Army forces responding to a crisis are prepared for and expect to fight. This saves time during the transition and requires an understanding of the OPLAN or likely concept of operations as early as possible. Forward-positioned forces reposition into battle positions or tactical assembly areas and take all available measures to protect themselves from attack in every domain as they prepare for combat. When located with allied or partner units, Army forces synchronize their activities to ensure unity of purpose and mutual support. Depending upon the enemy and distance from the United States, Army forces should expect to receive little support in the opening stages of a conflict and plan accordingly.
Chapter 6 - Operations During Armed Conflict
Section I of this chapter introduces large-scale combat operations and the ways in which they vary. It addresses topics applicable to both offensive and defensive operations, including enemy methods, relative advantages, integrating with the joint force, defeat mechanisms, and enabling operations. Section II describes defensive operations. Section III describes offensive operations. Section IV describes transition to post-conflict competition and stability operations.
SECTION I – ARMED CONFLICT AND LARGE-SCALE COMBAT OPERATIONS
6-1. Armed conflict encompasses the conditions of a strategic relationship in which opponents use lethal force as the primary means for achieving objectives and imposing their will on the other. The employment of lethal force is the defining characteristic of armed conflict, and it is the primary function of the Army. Lethality’s immediate effect is in the physical dimension—reducing the enemy’s capability and capacity to fight. However, the utility of lethal force extends into the information and human dimensions where it, along with the other instruments of national power, influence enemy behavior, decision making, and will to fight.
6-2. During armed conflict, operations usually reflect combinations of conventional and irregular warfare approaches. Leaders apply doctrine for large-scale combat operations during limited contingencies that require conventional warfare approaches. Irregular warfare includes counterinsurgency and unconventional warfare, which other publications specifically address. The initial actions of large-scale combat operations will likely overlap with actions initiated during competition and crisis. For example, while some units are engaged in offensive or defensive operations, other units may be completing non-combat evacuations while in contact with enemy forces. (See FM 3-24 for detailed information about counterinsurgency. See ATP 3-05.1 for more information about unconventional warfare.)
6-3. Large-scale combat operations are extensive joint combat operations in terms of scope and size of forces committed, conducted as campaigns aimed at achieving operational and strategic objectives through the application of force. Large-scale combat on land occurs within the framework of a larger joint campaign, usually with an Army headquarters forming the base of a joint force headquarters. These operations typically entail high tempo, high resource consumption, and high casualty rates. Large-scale combat introduces levels of complexity, lethality, ambiguity, and speed to military activities not common in other operations.
6-4. Large-scale combat operations occur in circumstances usually associated with state-on-state conflict, and they encompass divisions and corps employing joint and Army capabilities from multiple domains in a combined arms manner. Irregular warfare activities often complement large-scale combat operations, with conventional, irregular, and special operations forces conducting operations close to each other. This proximity requires cooperation between friendly forces of all types to ensure success. In other cases, irregular warfare occurs largely in a secondary joint operations area (JOA) or another theater of operations. When this occurs, the combatant commander (CCDR) ensures sufficient coordination of operations to support unity of purpose at the national level.
6-5. Successful large-scale combat operations defeat enemy armed forces while establishing control over land and populations to achieve operational and strategic objectives. They may capitalize on superior military capability to quickly overwhelm a weaker enemy and consolidate gains as part of a rapid campaign. Large scale combat operations against more capable enemy forces are likely to be of longer duration, lasting months or longer.
6-6. Army forces may execute large-scale combat operations in a supporting, enabling, or advisory role, instead of constituting the bulk of ground maneuver forces. One example was OPERATION INHERENT RESOLVE, beginning in 2014, during which a U.S.-led combined joint task force supported Iraqi Security Forces and Syrian Democratic Forces in defeating the Islamic State of Iraq and Syria. In these cases, U.S. forces applied large-scale combat operations tactics in support of a partner force.
6-7. The characteristics of large-scale combat operations vary based on many factors, including the enemy. When fighting against a less capable enemy, the U.S. joint force may have significant advantages in most domains. The principal concerns during such operations include how to win rapidly at minimal cost, consolidate gains, and transition responsibility for an area to legitimate authorities. When fighting against a peer enemy, able to contest the joint force in all domains, the operational environment becomes much more difficult. Integrated air defense and long-range fires systems; cyberspace and electronic warfare capabilities; chemical, biological, radiological, and nuclear capabilities (CBRN); and global reconnaissance and surveillance networks can create parity or significant enemy advantages in one or more domains, particularly early during a conflict and when operating close to its own borders. To succeed, the U.S. joint force must create its own relative advantages, preserve combat power, and rapidly exploit what opportunities it creates. Commanders must assume risk to create opportunity and sequence their operations because they cannot defeat enemy forces in a single decisive battle.
ENEMY APPROACHES TO ARMED CONFLICT
6-8. Although peer enemies mainly seek to obtain their strategic objectives during competition, they will engage in armed conflict if they view that the rewards are worth the risk. Once engaged in armed conflict, peer enemies employ combinations of threat methods to render U.S. military power irrelevant whenever possible and inflict unacceptable losses on the United States, its allies, and its partners. Russia and China employ their instruments of national power and military capabilities in distinct ways.
RUSSIA
6-9. The Russian view of war is that it is often undeclared, fought for relatively limited policy objectives, and occurs across all domains. Russian leaders assess that modern conflicts are characterized by a destructive and rapid initial period of war that is more decisive than in the past. Additionally, Russia considers that non-nuclear strategic precision-guided weapons can achieve strategic effects on par with nuclear weapons. Doctrinally, Russia plans to employ nuclear weapons in response to non-nuclear attacks when those attacks threaten Russian sovereignty.
6-10. During armed conflict, Russia seeks to exert simultaneous pressure in all domains. Russian strategies intend to increase the costs of confrontation and make the objectives of the United States and its allies politically and economically unsupportable. Russia’s objective is to weaken U.S. national will to continue a conflict by inflicting highly visible and embarrassing losses on U.S. forces.
6-11. Russian forces intend to win conflicts with massed and precision fires. Russian forces will attempt to set the operational conditions so that deployment of U.S. forces is ultimately counter to U.S. interests. If the U.S. does deploy forces, Russian goals are centered on creating constraints that prevent success of the United States’ campaign. Russian methodologies focus on four key areas:
Disrupt or prevent understanding of the operational environment. Russian information warfare activities manipulate the acquisition, transmission, and presentation of information in a way that suits Russia’s preferred outcomes.
Target stability. Russia may foster instability in key areas and among key groups so that regional security conditions do not support U.S. operational requirements.
Disaggregate partnerships. Russia acts upon U.S. allies and partners to reduce the ability of the United States to operate in its preferred combined, joint, and interagency manner.
Prevent access. Russia employs pre-conflict activities to deny access to U.S. forces, using nonlethal means initially and transitioning to lethal means if necessary. It seeks to undermine relationships, raise political stakes, manipulate public opinion, and attack resolve to constrain or deny basing rights, overflight corridors, logistics support, and concerted allied action.
6-12. As it applies instruments of national power, Russia integrates military forces and other means at selected times and locations to achieve desired objectives as part of its overall campaign. It uses offensive and defensive tactics and techniques that include acts of crime and terrorism. These actions can also be employed to manipulate population perceptions and dissuade support to U.S. military forces or other institutions. When necessary, Russia uses acts of physical violence, psychological operations, and different means of manipulating information to gain influence and develop voluntary or coerced cooperation in a target population. Concurrently, it uses indirect means to progressively degrade U.S. combat power and infrastructure resources and to otherwise psychologically influence the political, social, economic, military, and information variables of the operational environment.
6-13. Russian tactical-level units operate as combined arms forces to exploit the effects of both precision strikes and massed fires. Against lesser opponents, Russian forces employ deep maneuver when possible to defeat an enemy’s will to resist early in a conflict. In other cases, they mass capabilities in pursuit of more limited objectives while fixing their adversary along a broad front. Regardless of the situation, a basic principle of Russian military actions is to use the effects of strike actions to create the conditions for military success.
6-14. Russia prefers to employ all available national elements of power prior to using maneuver forces, and after force-on-force operations begin, it will continue to employ these integrated national capabilities to support tactical maneuver. Russian forces also employ denial and deception (maskirovka) to mask the true intent of their operation. To execute tactics, Russian units apply intelligence methods and decision making, that are scientifically based, to—
Understand the conditions of an operational environment that will impact operations.
Determine the tactical functions required and calculate the required allocation of combat power needed to accomplish a mission in a specific time and location.
Understand the psychological and cognitive issues among competing friendly forces, aggressor forces, the local population, and other actors in an operational environment.
CHINA
6-15. China considers three aspects in the country’s view of conflict: comprehensive national power, deception, and the Three Warfares. Comprehensive national power is made up of hard power and soft power. Hard power includes military capability and capacity, defense industry capability, intelligence capability, and related diplomatic actions such as threats and coercion. Soft power includes such things as economic power, diplomatic efforts, foreign development, global image, and international prestige. China views comprehensive national power as a vital measure of its global status. Ultimately, all forms of conflict— military, diplomatic, or other—must enhance China’s comprehensive national power. (For more information on China’s comprehensive national power, see ATP 7-100.3.)
6-16. Deception plays a critical role in every part of the Chinese approach to conflict. People’s Liberation Army planners employ stratagems to achieve their deception goals. Stratagems describe the enemy’s mindset, focusing on how to achieve the desired perceptions by the opponent, and then they prescribe ways to exploit those perceptions.
6-17. China’s strategic approach to conflict employs Three Warfares designed to support and reinforce the People’s Liberation Army’s traditional military operations. Though these approaches are called warfares, they are universally nonlethal and do not involve direct combat operations. If a battle must be fought, the Three Warfares are designed to unbalance, deceive, and coerce opponents to influence their perceptions in ways that create advantage. The Three Warfares are—
Public opinion warfare.
Psychological warfare.
Legal warfare.
6-18. Public opinion warfare is China’s high-level information campaign designed to set the terms of political discussion. China views this effort as capable of seizing the initiative in a conflict before any shots are fired by shaping public discourse, influencing political positions, and building international acceptance of Chinese interests.
6-19. China’s psychological warfare is broadly similar to U.S. military information support operations in that it is intended to influence the behavior of a given audience. Psychological warfare is the deliberate manipulation of psychological reactions in target audiences, designed to create and reinforce attitudes and behaviors favorable to China’s objectives and guide adversary behavior towards China’s preferred outcomes.
6-20. Legal warfare for China is the setting of legal conditions for victory—both domestically and internationally. Legal warfare seeks to unbalance potential opponents by exploiting international or domestic law to hinder their military operations, to create legal justification for People’s Liberation Army operations worldwide, and to support Chinese interests through a valid legal framework. It guides how the People’s Liberation Army trains to treat prisoners of war, detainees, and civilians, and it guides how the People’s Liberation Army abides by international legal conventions, codes, and laws.
6-21. During armed conflict, China employs systems warfare in combination with the other threat methods, such as preclusion, isolation, and sanctuary. China employs these threat methods throughout all domains and at all levels of warfare. Systems warfare involves—
Bypassing enemy systems’ areas of strength, thus gaining a combat advantage by approaching them asymmetrically.
Developing systems that excel at exploiting perceived weaknesses in enemy systems, thereby offsetting their strengths by undermining the systems’ ability to perform assigned missions.
Undermining international alliances through diplomatic efforts.
Conducting cyberspace attacks to disable air or seaports.
Using special operations forces to undermine civilian morale through covert operations.
Note. China uses the term “special operations forces” to identify their special forces units per ATP 7-100.3. Russian doctrine uses the term “special purpose forces” for their special forces units. For brevity, this manual uses “special operations forces” to describe special forces units employed by an adversary or enemy.
6-22. Although many actors on the world stage have embraced the concepts of systems warfare, including Russia, China has woven the idea into every aspect of their warfighting capabilities and methods. The systems warfare concept consists of two basic ideas: creating purpose-built operational systems that combine key capabilities under a single command, and the use of these operational systems to asymmetrically target and exploit vulnerable components of an opponent’s system. The People’s Liberation Army believes that by effectively destroying, isolating, neutralizing, or offsetting key capabilities, it can degrade the enemy’s will and ability to resist enough to achieve victory.
6-23. At the tactical level, systems warfare centers largely on targeting high-value battlefield systems such as radars, command and communications nodes, field artillery and air defense systems, and critical logistics support means. China relies on heavy employment of long-range fires at maximum standoff distance to target friendly joint enablers and command and control (C2) nodes. Examples of tactical system warfare include using heavy rocket artillery to defeat or destroy enemy radars and artillery systems, electronic warfare to suppress or neutralize enemy command and communications networks, and deception operations to target enemy leaders’ situational understanding.
RELATIVE ADVANTAGES DURING ARMED CONFLICT
6-24. Army leaders must anticipate enemy advantages and have a plan to overcome them. Army forces avoid attacking directly into enemy strengths. They best overcome enemy advantages by creating their own advantages to exploit in pursuit of assigned objectives. Army formations most effectively achieve overmatch through the integration and synchronization of joint and multinational capabilities employed from positions in multiple domains that create cascading dilemmas and defeat the enemy’s operational approach.
PHYSICAL ADVANTAGES
6-25. Friendly forces require physical advantages to defeat enemy forces and occupy land areas, exert control over lines of communications, and protect the physical infrastructure used to attain information and human advantages. Throughout armed conflict, leaders seek physical advantages that include—
Position.
Range.
Speed of movement.
Technologically superior capabilities.
Terrain and weather.
6-26. Positional advantage occurs when one force’s location facilitates its ability to exploit an enemy weakness. For example, a force positioned to attack the flank of an enemy defense oriented in a different direction is an advantage because it causes enemy forces to reposition and negates some of the benefits of a prepared defense. Gaining this advantage typically requires maneuver and involves assuming risk to a formation or in another part of the assigned area.
6-27. Friendly forces may enjoy a range advantage, particularly when employing joint capabilities. Superior range can enable the delivery of effects for which an enemy force has no immediate answer. Range advantage can also apply to distances friendly forces can move relative to enemy forces, particularly when friendly forces can do so quickly.
6-28. A higher speed of movement relative to enemy forces creates an advantage when leaders exploit it to move faster than enemy forces can effectively react or reposition. Speed of movement enables most other physical advantages—when employed with judgment. Speed mitigates risk and affords protection when units are closing with enemy forces while in range of enemy fires capabilities. The faster a unit closes with the enemy, the shorter the exposure. However, focusing on speed without applying judgment can cause units to blunder into enemy engagement areas and suffer heavy losses.
6-29. Leaders exploit technological advantages while directing course of action development and schemes of maneuver. New technological advantages do not always have to be new pieces of equipment. Using old technology or combining Army and joint capabilities in new and novel ways is often effective in gaining advantages.
6-30. Terrain and weather often provide advantages, especially in terms of mobility and countermobility. Leaders use high-speed avenues of approach to increase the speed of movement. They use severely restrictive terrain to reduce the mobility of enemy armored formations. In the offense, leaders use terrain to conceal their movement. In the defense, they use reverse slopes to provide cover and concealment. In the offense or defense, rain helps infantry reduce the noise of dismounted movement through wooded areas. Limited visibility periods help conceal battle positions and friendly movements from enemy reconnaissance efforts.
INFORMATION ADVANTAGES
6-31. Information advantages invariably overlap with and emanate from physical and human advantages. To gain an information advantage, units first require a physical or human advantage. Army forces create and exploit information advantages by acting through the physical and human dimensions of an operational environment. Leaders combine information advantages with other advantages to understand the situation, decide, and act faster than enemy forces. Examples of information advantages during armed conflict include—
The ability to access enemy C2 systems to disrupt, degrade, or exploit enemy information.
Opportunities created by deception operations to achieve surprise and thwart enemy targeting.
The ability to mask electromagnetic signatures.
The ability to integrate and synchronize friendly forces in denied or degraded environments through use of redundant communications.
The ability to rapidly share information with domestic and international audiences to counter enemy malign narratives.
The ability to inform a wide range of audiences to maintain legitimacy and promote the friendly narrative.
The ability to rapidly share and analyze information among commanders and staffs to facilitate decisions and orders.
HUMAN ADVANTAGES
6-32. Because war is a clash between opposing human wills, the human dimension is central to war. Army formations are principally designed to achieve objectives through the threat or employment of lethal force, which has a psychological effect. Understanding an enemy force’s tolerance for casualties and the political and social will to endure them is important to understanding the level of effort required to prevail against enemy forces in large-scale combat operations. Leaders do everything possible in the physical and information dimensions to reduce the enemy’s will to fight. During armed conflict, human advantages include—
Political and national will that supports strategic objectives.
Experienced, well-trained formations.
Leadership well versed in the mission command approach to C2.
Adherence to the law of war.
Unit cohesion and Soldiers with the mental and physical stamina for combat.
The trust of the host-nation population.
Confidence in a sustainment system that provides the best possible medical treatment and adequate supplies.
Interoperability and mutual trust between allies and host-nation partners.
OPERATING AS PART OF THE JOINT FORCE
6-33. The Army always fights as part of a joint force, and usually as part of a multinational coalition during large-scale combat operations. Because combatant commanders (CCDRs) often assign the senior Army commander as the joint force land component commander (JFLCC), it is imperative that Army leaders from the JFLCC to brigade level understand the integration of operations on land with those in the other domains for the joint force.
6-34. The Army supports the joint force by providing the capabilities and capacity to apply sustained combined arms landpower through movement, close combat, and fires at whatever scale is necessary to defeat enemies on land. It does this by employing capabilities from the land, maritime, air, space, and cyberspace domains in support of ground operations on land and employing ground-based capabilities to enable operations in the other domains.
6-35. Army forces’ contributions to the joint force extend well beyond Army support to other Services (ASOS) through a variety of actions. They include—
Establish C2 on land.
Counter air and missile threats that deny air and maritime freedom of action with land-based systems.
Defend and control key terrain.
Defeat components of enemy antiaccess (A2) and area denial (AD).
Conduct large-scale combat operations.
Sustain large-scale combat operations.
Consolidate gains.
ESTABLISH COMMAND AND CONTROL ON LAND
6-36. Establishing C2 on land requires a land component command that assigns land areas and properly defines command and support relationships between subordinate forces. A commander assigns land areas and command and support relationships based on the mission and the commander’s concept of operations. A commander also considers the level of joint support available when assigning land areas and task-organizing forces. Army forces establish C2 of land areas at the direction of the joint force commander (JFC), normally the JFLCC. A JFLCC is the commander within a unified command, subordinate unified command, or joint task force (JTF) responsible to the establishing commander for recommending the proper employment of assigned, attached, or other available land forces; planning and coordinating land operations; and accomplishing assigned missions. C2 across the width and depth of the land component commander’s assigned areas requires access to strategic communications. Therefore, commanders plan for the movement and placement of strategic communications systems in C2 nodes. (See JP 3-31 and FM 3-94 for more information on the JFLCC.)
6-37. In addition to their assigned missions, Army forces generally consider four key issues. They are the assignment of subordinate land areas, the concept of mutual support between subordinates, the integration of echelons in terms of time, space, and purpose, and the proper task organization of the land force.
6-38. The JFC typically assigns a land area of operations (AO) to the land component command. A land AO does not typically encompass the entire land operational area of the JFC’s joint operations area (JOA), but the size, shape, and positioning should be adequate for the JFLCC to accomplish the mission and protect the forces under the JFLCC’s control. In the assigned land AO, the JFLCC establishes an operational framework for the AO that assigns responsibilities to subordinate ground force commanders and allocates capabilities to fulfill those responsibilities. Based on the situation, the land component command assigns areas (AO, zone, or sector) to subordinate tactical echelons. Figure 6-1 on page 6-8 reflects a baseline doctrinal template for depths and frontages by echelon. (See Chapter 2 for more information on considerations for how to assign areas to subordinate echelons.)
Note. Political constraints, geography, ally and partner dynamics, forces available, the types of operations being conducted, and the enemy all influence the appropriate AO size for each echelon.

6-39. Commanders consider mutual support when task-organizing forces, assigning land areas, and positioning units. A high degree of mutual support between units provides flexibility and options to commanders and creates multiple dilemmas for enemy forces. When units can support each other, commanders have more options to combine capabilities from all warfighting functions and across all domains. Commanders and staffs assess supporting range of capabilities between units to understand their options with respect to mutual support and reducing the vulnerability of friendly forces to defeat in detail. Air capabilities and indirect fires have long ranges that provide options for increasing the supporting range between units.
6-40. Supporting distance depends on the mobility of the formation, the terrain, and the enemy situation. When units operate outside weapons ranges, they may be able to maneuver from supporting distances to enable each other. Infantry units may be able to maneuver a short supporting distance to enable an armored formation in severely restrictive terrain. A combat aviation brigade may be in supporting distance to aid an infantry brigade isolated from the rest of the division. When units must operate in a widely distributed manner, commanders and staffs position reserves so that they can maneuver in support of multiple formations depending on the situation.
6-41. Units are not within supporting distance regardless of their proximity to each other if they cannot communicate or are fixed by enemy forces. When units share a common operational picture (COP), relative proximity is less important than the ability to coordinate maneuver and fires. Exploiting the advantage of mutual support requires that units synchronize maneuver and fires more effectively than enemy forces do.
6-42. Large-scale operations involving both conventional and special operations forces require the integration and synchronization of conventional and special operations efforts. The JTF commander must consider the different capabilities and limitations of both conventional and special operations forces, particularly in the areas of C2 and sustainment. Exchanging liaison elements between conventional and special operations staffs further integrates efforts of all forces concerned. (For more information on coordinating conventional and special operations forces, see FM 6-05.)
6-43. Commanders assign subordinate units noncontiguous areas when the situation requires, either because the intent is to move along dispersed axes of advance or to minimize detection in locations like rear areas. When this occurs, the higher headquarters retains responsibility for the risk associated with the unassigned areas and mitigates that risk with capabilities it controls. As long as friendly forces have the initiative and can force the enemy to react, large units operating in non-contiguous areas are able to protect their lines of communication and can provide advantages at acceptable risk. However, risk to non-contiguous forces increases quickly the longer they become static, particularly in their rear areas. Large AOs with limited numbers of forces, and maritime environments where operations occur across groups of small islands are conditions that require non-contiguous assigned areas.
6-44. Joint capabilities can mitigate risk when subordinate units operate in noncontiguous areas of operations beyond supporting range or supporting distance of other ground forces. However, depending on joint capabilities outside an Army commander’s direct control entails the risk that those capabilities may not be available due to enemy activity, weather, or higher JFC priorities. (See Chapter 3 for more information on mutual support. See Chapter 8 for more information on non-contiguous assigned areas in maritime environments.)
6-45. Describing echelon roles and responsibilities in time, space, and purpose makes operations more cohesive through the depth of an operational area where enemy formations and irregular forces are intermingled with friendly forces. Intermingling of forces increases complexity and make it difficult to retain unity of effort between echelons. Commanders and staffs integrate the operations of all echelons to ensure that they accrue advantages and accomplish objectives.
6-46. Echelons maneuver subordinate formations to defeat enemy forces. Mission success demands that higher echelons provide support to subordinate operations. During large-scale combat operations, brigade combat teams (BCTs) and divisions generally focus on defeating enemy maneuver formations. Corps and higher echelons generally focus on defeating enemy integrated air defense systems and portions of the enemy’s integrated fires command according to the JFC plan and priorities.
6-47. BCTs need the time and space to defeat lead enemy security operations and maneuver echelons. Divisions provide time and protection for subordinate formations by disintegrating the cohesion of followon forces, reserves, and short- and mid-range fires that threaten close and rear operations. Divisions maneuver brigades in close operations against enemy maneuver forces. Divisions employ attack aviation and close air support to enable their operations and employ rear operations to sustain tempo and operational reach. Focusing on enemy maneuver forces does not prevent BCTs and divisions from attacking components of the enemy’s integrated air defense or fires capabilities. Corps routinely require divisions to attack priority enemy capabilities that are in the division’s assigned area or area of influence.
6-48. Corps maneuver divisions and set conditions by employing joint capabilities, including space and cyberspace effects, to defeat enemy mid- and long-range fires, air and missile defense capabilities, and their associated networks and sensors. Additionally, corps disrupt the movement of subsequent maneuver formations. Corps ensure division rear areas do not expand beyond their capacity to control, and they continue to expand division initial efforts to consolidate gains. The land component command provides mutual support to other components and maintains unity of effort on land with unified action partners. Land component command assessments ensure that tactical actions are having the desired effects in the physical, information, and human dimensions. They ensure that command narratives match the tactical situation, and that tactical actions reinforce command narratives. (See Figure 6-2 for a notional depiction of echelon roles and responsibilities in terms of time, space, and purpose.)
6-49. Higher headquarters actively aid their subordinate formations in their fights, not merely attaching or assigning them with additional capabilities. Commanders and staffs actively avoid becoming so narrowly focused on their echelon’s roles and responsibilities that they allow their subordinate formations to fail.

6-50. Commanders task organize their forces to ensure they are capable of fulfilling their roles, responsibilities, and purpose. Task-organizing is the act of designing a force, support staff, or sustainment package of specific size and composition to meet a unique task or mission (ADP 3-0). Considerations when task-organizing a force include the mission, training, experience, unit capabilities, sustainability, the operational environment, and the enemy threat. Task-organizing allocates assets to subordinate commanders and establishes command and support relationships. Task-organizing can be continuous, as commanders reorganize units for subsequent missions during the course of operations. The ability of Army forces to task-organize increases agility of formations. It lets commanders configure their units to best use available resources. It also allows Army forces to match unit capabilities to tasks. The ability of sustainment forces to tailor and task-organize ensures commanders have freedom of action to change with mission requirements.
6-51. The task organization of a formation supports C2 and formalizes command and support relationships between units. An effective task organization—
Facilitates the commander’s intent and concept of operations.
Ensures unity of command and synchronization of efforts through proper use of command and support relationships.
Retains flexibility with the concept of operations.
Ensures flexibility to meet unforeseen events and support future operations.
Weights the main effort.
Exploits enemy vulnerabilities.
Allocates resources with minimum restrictions on their employment.
Adapts to conditions imposed by changing variables.
Maintains or creates effective combined arms teams.
Offsets limitations and maximizes the potential of all available forces.
Provides mutual support among subordinate units to the greatest extent possible.
6-52. Units organize and reorganize their forces based on the tasks their higher headquarters assign throughout the course of an operation. Commanders ensure that each subordinate echelon has sufficient combat power assigned, attached, or in support to accomplish its missions. The allocation of supporting joint and Army capabilities takes into account main and supporting efforts by phase of an operation and other factors, like where to accept risk with economy of force efforts to create opportunities elsewhere.
6-53. Task organization changes place burdens on subordinate units, no matter how agile they may be. Before changing task organization, leaders consider less disruptive options, such as changes in support relationships and priorities of support.
COUNTER AIR AND MISSILE THREATS
6-54. Enemy air and missile capabilities are a significant threat to Army forces. They increase risk to formations building combat power in assembly areas, to forces transiting lines of communications, and forces conducting rear operations. While able to attack friendly forces during offensive operations, they are particularly dangerous to command posts and any units detected while in static positions. Defeating enemy air and missile threats is necessary to create opportunities for offensive maneuver. However, the employment of maneuver forces that cause forward-positioned enemy air and missile capabilities to displace can complement counter-air operations.
6-55. Counter-air is a theater mission that integrates offensive and defensive operations to establish and maintain a desired degree of control of the air by neutralizing or destroying enemy aircraft and missiles, both on the ground and in the air. These operations may include the use of Army manned or unmanned aircraft and long-range fires, maneuver forces, special operations, space operations, cyberspace operations, and electromagnetic warfare capabilities.
6-56. Defensive counter-air operations are all defensive measures within the theater designed to neutralize or destroy enemy forces attempting to penetrate or attack through friendly airspace. Defensive counter-air encompasses active and passive defensive actions taken to destroy, nullify, or reduce the effectiveness of hostile air and missile threats against friendly forces and assets. The goal of defensive counter-air operations, in concert with offensive counter-air operations, is to provide an area from which forces can operate while protected from air and missile threats. Defensive counter-air operations must be integrated and synchronized with offensive counter-air operations and all other joint force operations. The area air defense commander, when established by the JFC, is responsible for defensive counter-air planning and operations.
6-57. The JFC designates an area air defense command with the authority to plan, coordinate, and integrate overall joint force defensive counter-air operations through the joint air operations center. Together they establish an integrated air defense system. With the support of the component commanders, the area air defense command develops, integrates, and distributes a JFC-approved joint area air defense plan.
6-58. Friendly forces conduct air and missile engagements in accordance with guidelines and rules established by the area air defense commander, who is normally the joint force air component commander. A joint force air component commander is from the service with the most air assets and the capability to plan, task, and control joint air operations in an AO, typically the Air Force or Navy.
6-59. The Army air and missile defense command (AAMDC) is the Army’s lead organization for Army air and missile defense (AMD) forces in a theater. The AAMDC commander, as the theater army AMD coordinator, assists the ARFOR commander and the area air defense commander in the planning and coordination of the critical asset list and the creation of the defended asset list.
6-60. Army air defense artillery (ADA) forces conduct AMD operations for the joint force. Army forces may attack to seize key terrain for the emplacement and employment of theater air and missile defense systems by the JFC to defeat portions of the enemy air and missile capabilities. Forward deployed or early entry ADA forces defend critical assets against air attack while the JFC builds combat power.
6-61. The critical asset list identifies the most critical assets requiring protection, and it serves as the foundation for a defended asset list, which allocates available ADA forces. Integration with joint or multinational AMD components in the JOA can mitigate some shortages of AMD systems. Short-range air defense (SHORAD) provides air defense against low-altitude air threats for key joint and Army assets, primarily amphibious landing sites, ports, airfields, command posts, and crossing sites. Integrated C2 across all ADA echelons enables the most efficient allocation of limited SHORAD and early warning assets. High-to-medium altitude AMD forces defend joint and Army forces against ballistic missile threats.
6-62. When planning, positioning, and determining how often ADA units are required to conduct survivability moves, units take into account the range of enemy indirect fires and the ability of enemy forces to identify ADA unit signatures. Maneuver units may be required to defend ADA units against ground attack. (See JP 3-01 for more information on countering air and missile threats. See FM 3-01 for more information about Army AMD operations.)
DEFEND AND CONTROL KEY TERRAIN
6-63. The joint force has enduring requirements that include defending allies with forward-stationed forces, controlling strategic lines of communications to enable the deployment of combat power, and controlling the key terrain required during joint forcible entry operations. The contributions of Army forces both protect and enable the other members of the joint force, which in turn enable greater freedom of action and opportunities for operations on land. (See Section II of this chapter for information on defense during large-scale combat operations.)
6-64. Armed conflict often occurs after a long period of competition and is likely to begin with some form of enemy aggression against a U.S. ally or partner, an attack on forward-stationed U.S. forces, or both. Forward-stationed forces whose combat mission involves defending as part of an allied effort may be required to conduct mobile or area defenses or retrogrades or reposition to tactical assembly areas where they can prepare for their role in future operations. Advisor teams from the theater-aligned security force assistance brigade (SFAB) may embed alongside threatened partners, providing real-time tactical intelligence and access to U.S. capabilities. Commanders and staffs ensure defending forces have the appropriate priority for Army and joint fires. Operation plans (OPLANs) and supporting subordinate plans identify main defensive positions, security areas, force requirements, the locations of tactical assembly areas, and other planned locations. Building on preparations made during competition, units occupy these positions and, when able, they make improvements to overhead cover, concealment, communications, and fields of fire. Friendly forces hinder enemy detection efforts by combining real preparations with preparations of fake positions. Defensive preparations during competition, particularly the establishment of survivability positions, preserve combat power when enemy preparatory fires commence with little or no warning.
6-65. Forward-stationed forces that have a mission to reposition at the outset of armed conflict require familiarization and understanding of routes and future positions. They acquire this during competition. As part of rehearsals, units exercise alert and recall procedures, load plans, ammunition draws and distributions, tactical road marches, and passages of lines with the actual units that they would pass through. Leaders ensure rehearsals reflect combat conditions as much as possible, and they pay attention to details such as limited visibility movements, secure radio communications with allies, and in-transit maintenance plans.
6-66. Army forces, especially those stationed in forward locations or tasked to protect critical joint capabilities, continuously improve the survivability of their positions. Whenever possible, leaders ensure that key capabilities are mobile, and they take active measures to complicate their targeting during competition and crisis by moving them irregularly, using camouflage, digging in when stationary, and maintaining dispersion. Unit standards and discipline, inculcated and habituated with a protection mindset during training, determine success or failure during the opening phases of a conflict.
6-67. Depending upon what a specific OPLAN says or a situation dictates, some forward-stationed forces may reposition to tactical assembly areas to conduct specific tasks or preserve combat power. They may conduct these operations in or out of contact, and leaders must plan and rehearse them to be successful. When they involve rearward passage of lines through allied forces, units participate in rehearsals using the same procedures and secure communications planned for actual execution to maintain operations security.
6-68. When bypassed by enemy maneuver forces, commanders of forward-positioned forces take the initiative to stay in the fight. They seek to defeat elements of enemy follow-on forces. They make every attempt to disrupt enemy sustainment and long-range fires capabilities conducting deep strikes against friendly forces. These operations are most successful when supported by local populations. (See paragraphs 6-159 through 6-161 for more information on passages of lines. See paragraph 6-190 for more information on retrograde operations.)
6-69. Controlling strategic lines of communications and key terrain is essential to the joint force’s ability to project sustain combat power. Russia and China can contest joint operations across the globe, from the strategic support area in the continental U.S., along air, land, and maritime shipping lanes, to intermediate staging bases, and forward to tactical assembly areas. Because strategic lines of communications usually include key land areas, Army forces play a critical role in defending them.
6-70. Enemies integrate conventional and irregular warfare capabilities to disrupt lines of communications from the strategic support area to the close area. Enemy air, space, cyberspace, and missile capabilities are able to range targets anywhere in the world. Enemies can employ espionage or surrogates to attack infrastructure and populations in the continental United States. Enemy surface and subsurface maritime capabilities, in conjunction with unconventional approaches, will disrupt maritime lines of communications. Enemy medium- and long-range fires will contest the ability of Army forces to move combat power into forward tactical assembly areas.
6-71. Army forces control key staging areas such as airfields, railheads, and ports. They employ survivability methods and techniques appropriate to the situation to harden their positions. Depending on the operational and mission variables, these areas may be vulnerable to enemy cyberspace attacks and other methods of information warfare, espionage, terrorist attacks, special operations forces, ballistic missile attacks, and weapons of mass destruction.
6-72. Although the other Services are responsible to secure the air and maritime lines of communications, Army forces may secure some land areas, especially in vicinity of airfields and ports. Aircraft and ships must displace at irregular intervals to complicate enemy targeting, which in turn complicates planning requirements when Army forces are required to provide protection or other forms of support. Securing key terrain for use by other Services is important, even when it initially reduces combat power available for other purposes. Enabling other Services helps ensure the flow of Army forces into theater.
6-73. During armed conflict, joint operations to enforce sanctions or conduct blockades may require Army forces to control critical maritime choke points from land. Army capabilities, such as unmanned aircraft systems (UASs), long-range precision fires, AMD, attack aviation, electromagnetic warfare, inform and influence activities, security force assistance, and area security provide the joint force with options. (See JP 3-32 for more information on sea control.)
6-74. During offensive operations, commanders economize security of rear areas and protection of lines of communications to weight the main effort. To mitigate risk, commanders cooperate within the joint force and with multinational and other unified action partners for support. Allies and partners, in particular, can provide security capacity, situational awareness, and expertise in interacting with local populations, relieving Army forces of area security operations better suited to host-nation forces.
DEFEAT COMPONENTS OF ENEMY ANTIACCESS AND AREA DENIAL
6-75. Enemy A2 and AD approaches deny friendly force protection and freedom of action. Enemies pursue A2 and AD approaches with lethal means that significantly increase the risk to forward-stationed forces and the ability to deploy and stage additional forces into tactical assembly areas. Understanding the structure and function of the enemy’s integrated fires command helps friendly forces disintegrate the cohesion of enemy A2 and AD approaches and create exploitable opportunities for the joint force to conduct offensive operations.
6-76. An integrated fires command is a dedicated combination of C2 structures and organic and attached joint fire support units. The integrated fires command exercises centralized C2 of all allocated, dedicated fire support assets retained by its level of command. This can include aviation, artillery, naval gunfire, and surface-to-surface missile units from different commands and services. It also exercises C2 over all reconnaissance, intelligence, surveillance, and target acquisition assets dedicated to its support. An integrated fires command is tasked to engage designated operational and strategic targets. Integrated fires commands are typically associated with campaign-level headquarters. However, there are circumstances where an integrated fires command may be formed at the theater level. For example, the theater could have two separate campaigns, requiring a centralization of critical fire support assets at theater level to achieve the strategic or theater campaign objectives. Enemy forces integrate air and missile defense capabilities with the integrated fires command in different ways depending on their capabilities and the situation. Figure 6-3 on page 6-16 illustrates a notional theater-level integrated fires command.

6-77. The integrated fires command executes all fire support tasks for the supported command. The integrated fires command is designed to—
Exploit precision and massed fires through carefully integrated ground and air fire support.
Minimize the amount of time from target acquisition to engagement.
6-78. An integrated fires command and its component systems have key vulnerabilities that Army forces can target when supporting joint force operations. Like any military system, it requires sustainment capabilities and other support that Army forces can detect and attack. It has electromagnetic signatures that enable detection from friendly joint intelligence, surveillance, and reconnaissance (ISR) from all domains. Enemy networks depend on C2 nodes Army forces can target. Perhaps most importantly, systems within an integrated fires command are comprised of land-based capabilities, including sensors, fires capabilities, and C2 nodes, all of which Army forces can attack.
6-79. Defeating enemy A2 and AD approaches requires continuous effort, best facilitated by forward-stationed forces positioned and protected before hostilities commence. This allows air and naval capabilities to stage closer to joint force targets, increasing the number of sorties they conduct. It allows Army forces and the rest of the forward-postured joint force to retain the terrain and facilities necessary for the introduction of additional friendly forces into theater. Preserving forward-stationed forces and retaining critical terrain inside a theater during the opening stages of a conflict provides depth and operational reach of the joint force.
6-80. A2 and AD are two different enemy approaches that the joint force typically expects to encounter. The joint force often considers them as part of the same challenge because retaining or regaining access to geographic areas requires a cohesive joint approach through all domains. Defeating A2 and AD requires a multidomain approach that includes Army forces retaining or seizing critical terrain to establish the depth necessary for defeating enemy forces.
6-81. Commanders defeat enemy A2 and AD approaches by employing multiple attacks through multiple domains. Complementary and reinforcing networked A2 and AD capabilities are resilient against a single line of attack. An enemy operating near its border is able to reconstitute forces and capabilities from homeland sanctuaries. Maneuvering the right capabilities within range to attack critical vulnerabilities might incur too much risk when all threat systems are operating at full capability. Therefore, leaders destroy or isolate the most exposed parts of the enemy’s systems over time, degrading them enough to support maneuver and create other opportunities to exploit. Destruction, isolation, and dislocation of various parts of an enemy integrated fires complex or air defense system can all contribute to its disintegration.
6-82. The main physical components of enemy A2 and AD systems are sensors, firing platforms, networks, C2, sustainment, and the forces securing them. Army forces attack these components as part of a joint operation that integrates all available capabilities. The JFLCC requests joint effects to support Army forces. The JFLCC may request space capabilities to detect enemy systems, offensive space operations for specific effects, and offensive cyberspace operations or electromagnetic capabilities to attack an enemy’s networks (See FM 3-12 for information on offensive cyberspace operations.)
6-83. The JFLCC is responsible for integrating joint capabilities and synchronizing their employment and effects to achieve convergence in order to enable subordinate maneuver. Achieving convergence is a key part of the approach to defeating enemy A2 and AD.
6-84. Army forces request space and cyberspace effects to disrupt A2 and AD C2 networks and create other effects. Army formations synchronize cyberspace and electromagnetic warfare effects against the enemy’s network, disrupting human and automated communications between sensors, firing units, and command posts. When Army planners identify a requirement, they request space and cyberspace effects according to unit procedures. They must understand the planning and preparation timelines required for the effects they are requesting. For example, initiating cyberspace effects takes time, and it should be part of initial OPLAN development and revisions. Many cyberspace effects can take months to generate, even though they can be delivered rapidly once developed. This is a challenge for Army echelons whose planning horizons during combat are measured in terms of hours and days. Therefore, it is important that Army leaders anticipate desired cyberspace effects well in advance of when they will need to integrate them. (See FM 3-12 for more information on requesting cyberspace effects. See FM 3-14 for more information on space operations.)
6-85. Army forces employ combinations of defeat mechanisms to attack components of an enemy’s A2 and AD system within the overall intent of degrading and ultimately defeating its ability to function cohesively. Subordinate echelons align their operations and objectives with conditions set by the land component command and act rapidly to exploit them. This combination of attacks and objectives ultimately defeats the enemy’s preferred operational approach and renders the enemy force vulnerable to follow-on operations by the JFC. Commanders use deliberate and dynamic targeting to create opportunities to attack the enemy and create redundancies for friendly forces. (See JP 3-60 and ATP 3-60 for more information on dynamic and deliberate targeting processes.)
6-86. Commanders must account for the possibility that enemy forces are able to regenerate some or all of their capabilities, in some cases by repositioning forces from elsewhere. Commanders and staffs continually assess enemy A2 and AD systems and maintain enough combat power to defeat enemy regeneration efforts to avoid surprise and preserve friendly freedom of action. Defeating enemy A2 and AD approaches typically enables joint forcible entry operations and the movement of friendly forces from aerial ports of debarkation and seaports of debarkation to their tactical assembly areas.
JOINT FORCIBLE ENTRY OPERATIONS
6-87. Forcible entry is the seizing and holding of a military lodgment in the face of armed opposition or forcing access into a denied area to allow movement and maneuver to accomplish the mission (JP 3-18). A forcible entry operation may be the JFC’s opening move to seize the initiative. Forcible entry operations may be used to conduct operational movement and maneuver to attain positional advantage or as part of a deception.
6-88. Commanders design their forcible entry operations to seize and hold a lodgment against armed opposition. A lodgment is a designated area in a hostile or potentially hostile operational area that, when seized and held, makes the continuous landing of troops and materiel possible and provides maneuver space for subsequent operations (JP 3-18). This requires friendly forces to be combat loaded and prepared for immediate combat operations prior to their arrival on the ground in the lodgment area. A force defends the perimeter of a lodgment until it has sufficient forces to break out and conduct offensive operations.
CONDUCT LARGE-SCALE COMBAT OPERATIONS
6-89. During large-scale combat operations, Army forces conduct offensive, defensive, and stability operations to defeat enemy forces. Defeat of enemy forces in close combat is normally required to achieve campaign objectives and national strategic goals after the commencement of hostilities. Divisions and corps are the formations central to the conduct of large-scale combat operations, as they are organized, trained, and equipped for the deep, rear, and support operations that enable subordinate success during close combat. The ability to prevail in ground combat is a decisive factor in breaking an enemy’s will to continue a conflict. Conflict resolution requires the Army to conduct sustained operations with unified action partners as long as necessary to achieve national objectives. Section II and Section III of chapter 6 describe how Army forces, as part of a joint force, conduct defensive and offensive operations during large-scale combat.
SUSTAIN LARGE-SCALE COMBAT OPERATIONS
6-90. Large-scale combat operations require greater sustainment than other types of operations. Their high tempo and lethality significantly increase maintenance requirements and expenditure of supplies, ammunition, and equipment. Large-scale combat incurs the risk of mass casualties, which increase requirements for health service support, mortuary affairs, and large-scale personnel and equipment replacements. Large-scale combat operations demand a sustainment system to move and distribute a tremendous volume of supplies, personnel, and equipment. (See FM 4-0 for more information on sustainment.)
6-91. Army sustainment is a key enabler of the joint force on land. Army forces provide sustainment to other elements in the joint force according to the direction of the JFC. The JFC has the overall responsibility for sustainment throughout a theater, but the JFC headquarters executes many of its sustainment responsibilities through the TSC. When directed, Army sustainment capabilities provide the bulk of Army support to other services through executive agency, common-user logistics, lead Service, and other common sustainment resources. (See JP 4-0 for more information on joint sustainment. See ADP 4-0 for more information on the Army sustainment roles and responsibilities.)
6-92. Capabilities from other domains enable sustainment of Army forces. Air sustainment capabilities provide responsive sustainment for high priority requirements. Maritime-enabled sustainment supports largescale requirements. Space- and cyberspace-enabled networks facilitate rapid communication of sustainment requirements and precise distribution.
6-93. Successful sustainment operations strike a balance between protecting sustainment capabilities and providing responsive support close to the forward line of troops. A well-planned and executed logistics operation permits flexibility, endurance, and application of combat power. Plans must anticipate and mitigate the risk posed by enemy forces detecting and attacking friendly sustainment capabilities. Sustainment formations pursue operations security, survivability, and protection with the same level of commitment as all other forces. While most rear and support operations are economy of force endeavors when allocating combat power in divisions and corps, the continuity and survivability of those operations are vital to deep and close operations.
6-94. Dispersion of assets and redundancy help protect sustainment formations. Dispersing sustainment formations makes it less likely that enemy long-range fires can destroy large quantities of material. Dispersion also creates flexibility, as several nodes can execute the sustainment concept without a single point of failure. However, dispersed sustainment operations complicate C2 and can be less efficient than a massed and centralized approach. Commanders balance the risk between dispersion and efficiency to minimize exposure to enemy fires while maintaining the ability to enable the supported formation’s tempo, endurance, and operational reach.
6-95. Commanders must plan for the possibility of heavy losses to personnel, supplies, and equipment. Even with continuous and effective sustainment support, units may rapidly become combat ineffective due to enemy action. Commanders at all levels must be prepared to conduct reconstitution efforts to return ineffective units to a level of effectiveness that allows the reconstituted unit to perform its future mission. Reconstitution is an operation that commanders plan and implement to restore units to a desired level of combat effectiveness commensurate with mission requirements and available resources (ATP 3-94.4).
6-96. Reconstitution is a significant combined arms operation, and the actions involved in reconstitution transcend normal day-to-day force sustainment actions. Reconstitution is a command decision, typically made two echelons above the unit being reconstituted, and it is conducted across all warfighting functions, using existing systems and units to accomplish. No resources exist solely to perform reconstitution. Reconstitution requires the full support of commanders and staffs at all echelons to achieve the necessary results commensurate with future mission success. Reconstitution efforts following a CBRN attack present even greater challenges. If units cannot decontaminate equipment, commanders must assess the risk to the mission and personnel in continuing operations with or without contaminated equipment. (See ATP 3-94.4 for more information on reconstitution.)
6-97. Maneuver commanders, at the combatant command, ASCC, field armies, corps, or division echelons, direct reconstitution as an operation. Command guidance should address the timing, location, degree to which the unit is reconstituted, and the training required before the reconstituted unit resumes operations. As a general consideration, the more degraded or combat ineffective a unit becomes, the greater the sustainment effort and amount of individual and collective training the unit will require to return it to combat effectiveness. (See FM 4-0 for more information on supplying reconstitution.)
CONSOLIDATE GAINS DURING ARMED CONFLICT
6-98. Army forces consolidate gains for the joint force by making temporary advantages more enduring. Consolidating gains is not a phase, but rather an imperative that achieves the ultimate purpose of campaigns and operations. Army forces consolidate gains continuously during the conduct of operations, with varying emphasis by each echelon over time. Consolidating gains initially focuses on the exploitation of tactical success to ensure enemy forces cannot reconstitute any form of resistance in areas where they were initially defeated. A small unit consolidating on an objective and preparing for enemy counterattacks can be the first part of a larger effort to consolidate gains.
6-99. Unity of purpose for consolidating gains starts at the theater strategic level, where leaders plan and coordinate the resources necessary to achieve the JFC’s desired end state. They provide subordinate echelons a shared visualization of the security conditions necessary for the desired political or strategic end state. Achieving the desired end state generally requires a whole-of-government effort with unified action partners within and outside of the theater of operations. At the operational and tactical levels, land component commands and corps exploit division tactical success by maintaining contact with enemy remnants, bypassed forces, and the capabilities that enemy forces could militarize to protract the conflict. Friendly forces employ lethal and nonlethal capabilities to defeat remaining enemy forces in detail. Commanders direct information activities to reduce the will of those forces to resist and the local population to support them.
6-100. Conducting detainee operations plays a significant role in consolidating gains. Failure to secure defeated enemy forces quickly gives them the opportunity to break contact, recover the will to fight, and then reorganize resistance with whatever means remaining available to them. Capture of defeated enemy units and individuals separated or disorganized by friendly action is therefore critical. Large numbers of detainees may place a tremendous burden on operational forces as tactical forces divert combat power to process and secure them. Additionally, friendly forces must account for the detention of irregular forces and criminal actors that take advantage of a lack of civil security and civil control. Leaders assess the threat posed by irregular forces and criminal actors to determine whether or not these groups warrant detention by friendly forces. (See FM 3-63 for more information on detainee operations.)
6-101. Army forces must deliberately plan and prepare for consolidating gains because it is resource intensive and requires significant coordination with unified action partners. Planning for consolidating gains includes an assessment of operational risk, available combat power, changes to task organization, and additional assets required to achieve the desired end state. Assets might include—
Additional forces to provide area security tasks.
Host-nation, partner, and allied security forces.
ISR assets.
Engineers.
Military police.
Explosive ordnance disposal units.
Medical units.
Logistics units.
Civil affairs units.
Psychological operations units.
CBRN units.
6-102. Operations to consolidate gains can take many forms. These operations can include—
Offensive operations. Forces conduct offensive operations to complete the defeat of fixed or bypassed enemy forces.
Area security. Forces conduct security tasks to defeat enemy remnants, proxy or insurgent forces, and terrorists; control populations and key terrain; and secure routes, critical infrastructure, populations, and activities within an assigned area.
Stability operations. Forces execute minimum-essential stability operations tasks and ensure the provision of essential governmental services (in support of host nation or in place of the host nation), emergency infrastructure reconstruction, and humanitarian relief. These may include military governance.
Influence local and regional audiences. Commanders communicate credible messaging to specific audiences to prevent interference and generate support for operations or the host nation.
Defensive operations. Establish security from external threats. Commanders ensure sufficient combat power is employed to prevent physical disruption from threats across the various domains seeking to reverse or subvert the military gains made by friendly forces.
Detainee operations. Commanders and staffs must consider detainee operations prior to a conflict, during, and after large-scale combat operations have ceased. Detainee operations have long-lasting operational and strategic impacts.
6-103. Determining when and how to consolidate gains at the operational level and applying the necessary resources at the tactical level requires clear understanding about where to accept risk during an operation. Failure to consolidate gains generally leads to failure in achieving the desired end state, since it represents a failure to follow through on initial tactical successes and cedes the initiative to determined enemies seeking to prolong a conflict. Security is necessary for transition of responsibility to a legitimate governing authority and the successful completion of combat operations. Army forces integrate the capabilities of all unified action partners and synchronize their employment as they consolidate gains.
6-104. Although operations to consolidate gains may at times be economy of force efforts, they are critical to the long-term success of the joint force’s operation. Enemy forces will continue to challenge Army gains even after their forces are defeated to gain time for a favorable political settlement, set conditions for a protracted resistance, and alter the nature of the conflict to gain relative advantages. Enemy forces will execute information warfare, exploit cultural seams, challenge security, encourage competition for resources, promote conflicting narratives, support religious divides, and create alternatives to legitimate authority. As long as enemy forces have a will to resist, they will continue to attempt to undermine friendly gains.
6-105. Consolidating gains requires a significant commitment of combat power in addition to the combat power being employed to maintain tempo and pressure on enemy main body forces. When available, Army forces rely on host-nation forces better suited for operations that involve close interaction with local populations. When a host nation or an ally is unable to provide support, Army forces are responsible for consolidating gains. During large-scale combat operations, corps should plan for a division and a division should plan for a BCT to conduct operations with the purpose of consolidating gains.
APPLYING DEFEAT MECHANISMS
6-106. As described in Chapter 2, defeat mechanisms are broad means by which commanders visualize and describe how they plan to defeat enemy forces. Defeat mechanisms have interactive and dynamic relationships constrained only by the resources available and imagination. Defeat mechanisms are most useful for commanders at the division-level and above to develop operational and strategic approaches to defeat enemy forces. For commanders at the brigade combat team-level and below, the defeat mechanisms may offer limited utility. Defeat mechanisms are not tactical tasks, and commanders at the lower tactical echelons do not develop or employ defeat or stability mechanisms.
6-107. Once developed, defeat mechanisms help commanders and staffs determine tactical options for defeating enemy forces in detail. Commanders translate defeat mechanisms into tactics and describe them in the concept of operations. Commanders use tactics to apply friendly capabilities against enemy forces in the most advantageous ways from as many domains as possible. Understanding how tactics support each of the defeat mechanisms improves tactical judgment. (See ADP 3-90 for more information on tactics.)
DESTROY
6-108. Destruction and the threat of destruction lies at the core of all the defeat mechanisms and makes them compelling in a specific context. It is the defeat mechanism with the most enduring effect. A commander can achieve the destruction of smaller units with massed fires. However, destruction is the most resource-intensive outcome to achieve on a large scale. Commanders use destruction as a defeat mechanism when—
Enemy forces are not vulnerable to other means.
The tactical situation requires the use of overwhelming combat power.
The risk of loss is acceptable.
It is necessary to set conditions for other defeat mechanisms.
6-109. The physical effects of destruction have significant implications in the information and human dimensions. The destruction of enemy capabilities sends the message that enemy forces may be overmatched, and defeat is imminent. Casualties and the loss of life have negative psychological impacts that can either embolden or degrade enemy morale and will to fight. Typically, significant death and destruction degrade enemy morale and will. The joint force can sometimes achieve similar results with modest and precise applications of combat power. However, modest applications of combat power may prolong the joint force’s ability to achieve a decisive outcome. Excessive destruction of infrastructure can create a humanitarian crisis and create civilian casualties or suffering that undermines domestic and international support for military operations, so commanders must exercise judgment appropriate to each operational context. For moral, legal, and pragmatic reasons, commanders should take precautions to avoid death and destruction unnecessary for operational success, and they must always comply with the law of armed conflict.
6-110. At the operational level, physical destruction is rarely feasible or acceptable as the overarching defeat mechanism. Operational-level commanders choose elements of enemy forces that must be destroyed to enable the other defeat mechanisms. They synchronize Army, joint, and unified action partner capabilities to destroy critical components of enemy warfighting systems, such as sensors, long-range fires capabilities, C2 nodes, supply depots, and critical infrastructure.
6-111. At the tactical level, the lower the echelon the more central destruction is to its operation. Corps and divisions destroy enemy formations and critical capabilities to enable tactical success. They destroy enemy surveillance, reconnaissance, C2, fires, maneuver, protection, and sustainment capabilities. They destroy these capabilities to limit the effectiveness of enemy offensive or defensive schemes and preserve friendly combat power. At brigade echelons and below, units close with and destroy weapon systems, combat platforms, and personnel to render enemy forces incapable of resistance.
DISLOCATE
6-112. Dislocate as a defeat mechanism renders an enemy’s position ineffective and, ideally, irrelevant. Dislocation can enable surprise. It forces enemy forces to react to the unexpected, and it imposes new dilemmas on enemy decision makers. If the dislocation that occurs is great enough, enemy forces may reconsider their risk assessment and conclude that they must surrender or reposition because their position no longer offers a reasonable expectation of success. More commonly, dislocation will force an enemy to make major changes to its dispositions and give up considerable ground.
6-113. The challenge of dislocation is that enemy leaders likely understand the value of the position desired by the friendly force, and they have made efforts to protect it. Therefore, to maneuver forces into positions that are so advantageous they render the enemy dispositions ineffective, commanders must often make use of deception and assume considerable risk.
6-114. Dislocation extends into the human and information dimensions. Combinations of physical maneuver and information activities can undermine the confidence of decision makers and their forces. Deception operations that enable surprise can present enemy forces with dilemmas they did not expect, and they may incite them to question other assumptions they made about friendly courses of action. For example, an enemy force preparing a defense that believes terrain and weather will protect its flank is surprised when friendly forces maneuver there during an attack. Not only is the geographic position and orientation of the enemy defense rendered ineffective, but so too is the confidence of the force. The force may begin to question its leadership while it adjusts its dispositions under the pressures of time and friendly contact.
6-115. At the operational level, commanders dislocate the enemy by posturing friendly forces in multiple assembly areas that do not make any single course of action obvious, and then they threaten maneuver along multiple axes of advance that exceed the enemy force’s ability to mass effects. While dislocation alone is unlikely to cause enemy forces to lose the will to fight, it creates favorable conditions for the combination of other defeat mechanisms. It can overwhelm enemy networked air defense and integrated fires systems, and it can enable a tempo of offensive operations from which enemy defenses cannot recover.
6-116. At the tactical level, vertical and horizontal envelopments and turning movements are common forms of maneuver that can precipitate dislocation. While these tactics can create rapid success, they may come with significant risk to rear areas and flanks, operational reach, and maintaining the momentum required to achieve objectives in accordance with a specific timeline. These tactics are most often successful against enemy units operating at or beyond the limit of their supporting capabilities, adjacent units, or reserves. Essentially, the friendly force assesses that it can achieve an advantageous position and exploit it faster than supporting enemy forces can react. The defeat of North Korean forces in 1950 illustrates the relationship between the defeat mechanisms of destroy and dislocate.
In early August 1950, the North Korean People’s Army (NKPA) advance had driven U.S. and Republic of Korea forces back into the southeastern portion of the Korean peninsula and threatened to push them into the sea. To stop the advance of the NKPA, U.S. and Republic of Korea forces held a defensive perimeter, approximately 140 miles wide, along the Naktong and Nam Rivers. Over the next few weeks, NKPA and friendly forces engaged in heavy fighting with attacks and counterattacks occurring along the entire perimeter, as the NKPA attempted to break through the defensive line. Throughout this period of the war, the NKPA held the initiative against U.S. and Republic of Korea forces, but by mid-September the initiative shifted to friendly forces.
On 15 September, while United Nations and NKPA forces were decisively engaged in the south, the U.S. X Corps conducted a two-division amphibious landing at Inchon, on the west coast of Korea, north of Seoul. This operational-level turning movement, code-named OPERATION CHROMITE, occurred 150 miles behind enemy lines and caught the NKPA completely by surprise. In the following days, X Corps captured the Seoul-Suwon area and severed NKPA lines of communications.
In conjunction with the amphibious landing, the U.S. Eighth Army launched a major counteroffensive against the twelve NKPA divisions opposing it in the south. With the support of United Nations’ air power, the Eighth Army penetrated the enemy’s forward defenses at multiple places and advanced northwest to link up with the X Corps. The combined actions by X Corps and Eighth Army left an estimated force of eight NKPA divisions isolated in southwestern Korea. Outflanked, unable to resupply or reinforce, and facing strong pressure in its close and rear areas, the NKPA began to collapse. Some NKPA units and individuals began to retreat, and their initial retreat quickly turned into a rout. Those NKPA units unable to retreat were destroyed or captured by friendly forces. By the end of September, the NKPA ceased to exist as an organized fighting force in South Korea.
ISOLATE
6-117. Isolating an enemy force separates it from its physical, information, or human sources of support. It involves denying the enemy force access to resupply of personnel and equipment, access to intelligence, and shared understanding with adjacent units and higher echelon headquarters. Isolation denies enemy ground forces access to capabilities from other domains, forcing them to operate only in a limited area of the land domain with the resources they have on hand.
6-118. At the operational level, it is difficult to achieve complete isolation of an enemy force not already physically separated from the enemy main body. Even limited access to air, ground, and maritime lines of communications can sustain a prepared and determined enemy force for long periods. However, operational-level commands can employ capabilities to temporarily isolate units or critical capabilities from the rest of an enemy formation in one or more domains. This enables defeat of the enemy in detail, or it sets conditions for operations in other domains. Operational headquarters conduct activities that physically and psychologically isolate enemy leaders from their formations and other sources of support. This may include disrupting communications networks or access to space and cyberspace capabilities for a specific enemy echelon or conducting influence activities to lessen local support for national objectives. When an enemy force includes elements from different nations, it is possible to isolate one or more of them physically or by informational means. Exploiting differences in national aims or cultural divisions degrades the enemy’s overall effectiveness.
6-119. At the tactical level, physically blocking lines of communications, controlling key terrain, fixing supporting units, and encircling an enemy force are tactics that support the achievement of isolation. Electromagnetic attack capabilities help tactical leaders deny enemy forces access to reliable communications, and they can play a major role in creating psychological isolation. Destroying enemy command posts at one echelon can isolate that echelon’s subordinate formations from the next higher echelon, temporarily causing significant disruption to coherent C2.
6-120. While isolation on its own may not cause defeat, it increases the vulnerability of enemy forces to destruction, dislocation, and disintegration. It can also reduce the will to fight and increase the probability of uninformed decision making, which then amplifies the effects of the other defeat mechanisms.
DISINTEGRATE
6-121. To disintegrate is to attack the cohesion of the whole and involves preventing components of an enemy formation or capability from fulfilling their role as part of the overall effort. Disintegration causes the formation or capability to function less effectively, creating vulnerabilities that the friendly force can exploit. Disintegration is most effective when created by a combination of the other three defeat mechanisms, and it includes both physical and cognitive effects on enemy forces. Disintegration is typically temporary and causes enemy forces to adapt. Creating more lasting effects requires forces that are ready to exploit the opportunity provided by disintegration. Commanders ensure they have sufficient combat power for exploitation, and they synchronize their exploitation efforts with the temporal effects of disintegration.
6-122. Disintegration sets conditions for achieving operational level objectives. Destruction, isolation, and dislocation all focus on relatively limited parts of a larger enemy force in specific geographic areas, whereas the effects of disintegration can have repercussions throughout the depth and breadth of the enemy’s echelons. Effective disintegration can cause collapse of coherent organized resistance for operationally significant periods.
6-123. To disintegrate an enemy formation or capability, commanders need only to disrupt or desynchronize enemy forces to the degree required for achieving the desired end state. In this sense, disintegration provides a measure of economy the other defeat mechanisms do not. Commanders do not need to create decisive effects at a single point in space, time, or domain. Even modest impacts on a combination of objectives across multiple domains can produce the necessary effects over time.
6-124. Operational-level echelons disintegrate large enemy formations and their capabilities by attacking their individual components. Attacking operational-level C2 infrastructure impacts all enemy functions, and it is the most direct way to cause disintegration. Degrading enemy communications using a combination of lethal fires, electromagnetic attack, and joint-enabled offensive cyberspace operations disrupts an enemy force’s ability to synchronize operations. Deception compounds and accelerates the effects the other defeat mechanisms contribute towards disintegration.
6-125. Army forces disintegrate the components of integrated air defenses, long-range fires systems, and C2 networks to enable friendly freedom of action. The requirement to disintegrate these systems does not end with forcible entry operations or the start of offensive operations. Because these systems are resilient, disintegrating them relies on assessing them throughout the duration of a campaign.
6-126. Enemy systems that enable A2 and AD approaches have vulnerabilities that include sensors, communications links to firing platforms, and dependencies on space-based global navigation satellite systems and the electromagnetic spectrum. The data and processors that facilitate detection and fire mission transmission can be an exploitable vulnerability. Commanders can employ joint fires capabilities to destroy enemy long-range surface-to-surface and surface-to-air systems, which are difficult to replace. Friendly forces that have penetrated enemy defensive echelons can further disintegrate enemy integrated fires systems with direct fire or the threat of being overrun. While enemy forces reposition, their effectiveness is degraded.
6-127. Army forces can disintegrate enemy maneuver formations by converging joint capabilities in ways that interdict main supply routes, mobility corridors, and transportation infrastructure such as bridges, rail heads, airfields, ferries, and tunnels. These actions affect enemy repositioning and rapid reaction to friendly operations. Commanders can focus on the destruction of the best-trained and equipped enemy forces in a particular formation, which may disrupt the cohesion of the larger formation and lower its morale.
6-128. Enemy operations depend on sustainment systems in the same way friendly operations do. Destroying or disrupting supply depots, logistics convoys, fuel facilities, and sustainment units can render the enemy formations they sustain incapable of achieving their intended objectives. Even limited attacks on enemy sustainment capabilities can delay their operations, degrade their combat power, and make them vulnerable to early culmination.
6-129. Senior tactical echelons disintegrate enemy forces by attacking vulnerabilities that make them less able to employ a combined-arms approach to operations. Disrupting enemy communications with electromagnetic attacks or physical attacks against C2 nodes are means of doing this. Commanders use deception to create uncertainty and slow enemy decisions. They conduct reconnaissance and security operations and maintain operations security to prevent enemy forces from developing an accurate picture of friendly dispositions and courses of action.
6-130. Army forces employ forms of maneuver that avoid the enemy force’s main effort and enable friendly forces to decisively engage enemy forces without becoming fixed targets for long-range fires. Seeking or creating assailable flanks creates opportunities for exploitation in depth, forcing enemy forces to fight from unfavorable terrain or in directions they did not anticipate. Penetrations, envelopments, and turning movements are forms of maneuver well suited for doing this. Because enemy forces can anticipate the most favorable friendly forms of maneuver, their preparations focus on denying them. Therefore, friendly courses of action require sufficient combat power employed with a combination of stealth, speed, deception, and risk acceptance to be successful.
6-131. Disrupt, degrade, neutralize, reduce, isolate, delay, suppress, deny, fix, bypass, and deceive are examples of common tasks and effects that leaders combine to disintegrate enemy tactical echelons. Leaders use these tasks to limit enemy freedom of maneuver, impose friction on enemy operations, and disrupt enemy synchronization.
6-132. A combined-arms approach helps retain sufficient combat power and the mobility necessary to exploit the opportunities disintegration provides. The 1973 Arab-Israeli War illustrates the importance of a combined-arms approach to achieving disintegration.
After the destruction of its air force and defeat of its ground forces by Israel in the 1967 Six Day War, Egypt reorganized its armed forces in preparation for what it saw as the inevitable next conflict. With help from the Soviet Union, it acquired a modern integrated air defense system and anti-tank guided missile systems to counter the Israeli air and armor forces that had been a large factor in its defeats in three previous wars. These new capabilities gave the Egyptian army the opportunity to surprise the potent Israeli Defense Forces air-ground team, which it exploited in 1973.
In a well-planned and rehearsed operation, Egyptian forces rapidly assaulted across the Suez Canal, penetrated Israeli Defense Force defensive positions, and established a deliberate defense after a short advance. The Israeli counterattack with aircraft and an armored brigade was defeated with heavy losses from surface-to-air missiles and anti-tank guided missile systems, respectively. The losses were a shock to the previously undefeated Israeli air and armor forces, which needed to quickly reconstitute and adapt to a very different operational environment than 1967. The Israeli Army recognized that a mounted, tank-only approach was not going to defeat well-trained infantry with modern long-range anti-tank missiles. Only a combined arms approach to close combat would be effective, so it quickly task-organized infantry units into the armored brigades.
Once the task-organized brigades penetrated Egyptian first echelon defenses and cleared key objectives, the Israeli Army was able to disrupt and ultimately defeat the integrated air defense system by destroying vulnerable launchers and radars with direct fire. The Israeli action forced the remaining integrated air defense systems to displace further into Egypt. With the integrated air defense system effectively defeated, the Israeli air force maneuvered unimpeded in support of its ground forces and contributed to the complete tactical defeat of the Egyptian army.
The success of the Israeli Defense Force combined approach to operations later in the war sharply contrasts with the failure of its hasty and unbalanced initial counterattack. The Israeli Defense Force’s success is also an example of how ground forces enabled operations in the air domain, which in turn were able to enable the ground forces. Lastly, the Israeli Defense Force operational approach took advantage of the integrated air defense system’s critical vulnerabilities, which included dependence upon relatively fixed positions. Disintegration of the integrated air defense system did not occur until the Israeli Defense Force was able to create and then exploit opportunities on the ground through hard fought close combat.
ENABLING OPERATIONS
6-133. Enabling operations set friendly conditions required for most operations. Commanders direct enabling operations to support the conduct of offensive, defensive, and stability operations and defense support to civil authorities tasks. The execution of enabling operations alone does not directly accomplish the commander’s end state, but enabling operations must occur to complete the mission. Examples of enabling operations are—
Reconnaissance.
Security.
Troop movement.
Relief in place.
Passage of lines.
Countermobility.
Mobility.
RECONNAISSANCE
6-134. Reconnaissance is a mission undertaken to obtain, by visual observation or other detection methods, information about the activities and resources of an enemy or adversary, or to secure data concerning the meteorological, hydrographic, or geographic characteristics of a particular area (JP 2-0). Reconnaissance occurs continuously in all domains. Reconnaissance identifies terrain characteristics, obstacles to mobility, the disposition of enemy forces, and the relevant characteristics of the civilian population. It facilitates mobility and prevents surprise. Reconnaissance prior to unit movements and occupation of assembly areas is critical to protecting friendly forces and preserving combat power. Units perform reconnaissance to make contact with enemy forces on favorable terms. Leaders at every echelon emphasize the importance of reporting and rapidly updating digital and analog systems. (See ADP 3-90 for more information on reconnaissance.)
6-135. There are seven fundamentals of successful reconnaissance operations. They are—
Ensure continuous reconnaissance.
Do not keep reconnaissance assets in reserve.
Orient on reconnaissance objectives.
Report all required information rapidly and accurately.
Retain freedom of maneuver.
Gain and maintain enemy contact.
Develop the situation rapidly.
6-136. There are five types of reconnaissance operations. They are—
Zone reconnaissance.
Area reconnaissance.
Route reconnaissance.
Reconnaissance in force.
Special reconnaissance.
6-137. Zone reconnaissance is a type of reconnaissance operation that involves a directed effort to obtain detailed information on all routes, obstacles, terrain, and enemy forces within a zone defined by boundaries (ADP 3-90). Commanders assign a zone reconnaissance when they need additional information on a zone before committing other forces.
6-138. Area reconnaissance is a type of reconnaissance operation that focuses on obtaining detailed information about the terrain or enemy activity within a prescribed area (ADP 3-90). This area may consist of a single location, such as a town, a ridgeline, a forest, an airhead, a bridge, an installation, or any other critical operational feature such as obstacles. (See ADP 3-90 for more information on area reconnaissance.)
6-139. Route reconnaissance is a type of reconnaissance operation to obtain detailed information of a specified route and all terrain from which the enemy could influence movement along that route (ADP 3-90). The route may be a road, highway, trail, mobility corridor, avenue of approach, or axis of advance. The reconnaissance effort provides new or updated information on route conditions, such as obstacles and bridge classifications, and enemy, adversary, and civilian activity along the route. (See ATP 3-34.81 for more information on route reconnaissance, route classification, and the classification of features along routes.)
6-140. A reconnaissance in force is a type of reconnaissance operation designed to discover or test the enemy’s strength, dispositions, and reactions or to obtain other information (ADP 3-90). Battalion-sized task forces or larger organizations usually conduct a reconnaissance in force. Commanders assign this operation when an enemy force is operating within an area, and they cannot obtain adequate information about the enemy force by other means.
6-141. Special reconnaissance is reconnaissance and surveillance actions conducted as a special operation in hostile, denied, or diplomatically and/or politically sensitive environments to collect or verify information of strategic or operational significance, employing military capabilities not normally found in conventional forces (JP 3-05). Special reconnaissance provides an additional capability for commanders and supplements other conventional reconnaissance and surveillance actions.
6-142. During the conduct of any variation of reconnaissance, the commander may require information about a specific aspect of the area of operations (AO). To obtain this information the commander may direct a specific focus task which typically requires the use of an organization uniquely trained and equipped for the mission. Focus tasks include electromagnetic, engineer, CBRN, and civil reconnaissance.
6-143. Electromagnetic reconnaissance is the detection, location, identification, and evaluation of foreign electromagnetic radiations (energy) (JP 3-85). Electromagnetic reconnaissance supports information collection at brigade and higher echelons using assigned electromagnetic warfare personnel and capabilities. Information obtained through electromagnetic reconnaissance assists the commander with situational understanding and can support signals intelligence activities. Electromagnetic reconnaissance may result in electromagnetic protection modifications or lead to an electromagnetic attack against enemy capabilities. (For more information on electromagnetic reconnaissance see FM 3-12.)
6-144. Engineer reconnaissance obtains information about the infrastructure, terrain, or threat. This may include data on obstacles, gap crossing sites, airfields, bridges, tunnels, roads, and trails. Engineer units do not have designated reconnaissance teams. Engineer reconnaissance is directed and task-organized based on mission requirements using assets that would otherwise support other engineer missions. (For more on engineer reconnaissance see ATP 3-34.81.)
6-145. CBRN reconnaissance includes missions to obtain information on suspected or confirmed chemical, biological, radiological, or nuclear threats and hazards in an assigned area. CBRN reconnaissance identifies indicators of enemy CBRN production or employment and indicators related to civilian or industrial facilities that could be weaponized or produce hazards when damaged or destroyed. (For more on CBRN reconnaissance see ATP 3-11.37.)
6-146. Civil reconnaissance is a targeted, planned, and coordinated observation and evaluation of specific civil aspects of the environment such as areas, structures, capabilities, organizations, people, or events (JP 3 57). Civil reconnaissance verifies or refutes civil information, supports operational environment assessments, and detects and monitors changes in the civil component. It is conducted over time through routine engagement and patterned civil observance using active and passive sensors, virtual sensors, and other means. (For more information on civil reconnaissance see FM 3-57.)
SECURITY OPERATIONS
6-147. Units may perform security tasks to the front, flanks, or rear of their main body, and they must be aware of enemy threats in all domains relevant to their assigned area. The main difference between the performance of security and reconnaissance tasks is that security tasks orient on the force, area, or facility being secured, while reconnaissance tasks orient on enemy forces and terrain. Security tasks are supporting efforts. The ultimate goal of security operations is to protect main body forces from surprise and deny enemy freedom of action to collect on friendly forces. The protected force may not always be a military force; it can also be the civilian population, civil institutions, and civilian infrastructure in the unit’s assigned area.
6-148. There are a number of general considerations when performing security operations. These apply to all security tasks, but they are most applicable to the performance of screen, guard, and cover tasks. The screen, guard, and cover tasks share many common control measures, starting with boundaries defining the security area. The main body unit establishes the security area. For a security force operating to the front of the main body, the lateral boundaries of the security area are normally an extension of the lateral boundaries of the main body. The security force’s rear boundary is normally the battle handover line. (See ADP 3-90 for additional information on common security control measures for security operations.)
6-149. Security operations are those operations performed by commanders to provide early and accurate warning of enemy operations, to provide the forces being protected with time and maneuver space within which to react to the enemy, and to develop the situation to allow commanders to effectively use their protected forces (ADP 3-90). The four types of security operations are area security, cover, guard, and screen.
6-150. Area security is a type of security operation conducted to protect friendly forces, lines of communications, and activities within a specific area (ADP 3-90). The security force may be protecting the civilian population, civil institutions, and civilian infrastructure with a unit’s assigned area.
6-151. Cover is a type of security operation done independent of the main body to protect them by fighting to gain time while preventing enemy ground observation of and direct fire against the main body (ADP 3-90). A force tasked to cover may do so offensively or defensively.
6-152. Guard is a type of security operation done to protect the main body by fighting to gain time while preventing enemy ground observation of and direct fire against the main body (ADP 3-90). Units performing a guard cannot operate independently. They rely on fires and functional and multifunctional support assets of the main body. A force tasked to guard may do so offensively and defensively.
6-153. Screen is a type of security operation that primarily provides early warning to the protected force (ADP 3-90). Screens provide less protection than guards or covers. Screen missions are defensive in nature and accomplished by establishing a series of observation posts and patrols to ensure observation of the assigned area. The screen force gains and maintains enemy contact consistent with the operation order and destroys or repels enemy reconnaissance units by conducting counter-reconnaissance.
6-154. The screen, guard, and cover security operations provide increasing levels of combat power and increasing levels of security for the main body. Area security preserves freedom to move reserves, position fire support means, protect C2 systems, and conduct sustainment operations. Commanders balance the combat power employed for security against the requirements of the main and supporting efforts.
6-155. All maneuver forces are capable of conducting security operations. All Army BCTs conduct security operations as part of their mission-essential task list, while maneuver enhancement brigades, when properly task-organized, support theater army, corps, and divisions by conducting screens and area security throughout its assigned area of operations. Habitual support relationships with attachments and established standard operating procedures facilitate unity of effort and efficiency during security operations spanning multiple echelons of divisions and corps.
6-156. Successful security operations in any domain depend on properly applying five fundamentals. These fundamentals are—
Provide early and accurate warning.
Provide reaction time and maneuver space.
Orient on the protected force, area, or facility.
Perform continuous reconnaissance.
Maintain enemy contact.
(See ADP 3-90 for additional information on the conduct of security operations.)
TROOP MOVEMENT
6-157. Troop movement is the movement of Soldiers and units from one place to another by any available means (ADP 3-90). Units perform troop movements using different methods, such as dismounted foot marches, mounted marches using tactical vehicles, or air, rail, and water means in various combinations. The method employed depends on the situation, the size and composition of the moving unit, the distance the unit must cover, the urgency of execution, and the condition of the troops. It also depends on the availability, suitability, and capacity of the different means of transportation. Troop movements over extended distances have extensive sustainment considerations.
RELIEF IN PLACE
6-158. A relief in place is an operation in which, by direction of higher authority, all or part of a unit is replaced in an area by the incoming unit and the responsibilities of the replaced elements for the mission and the assigned zone of operations are transferred to the incoming unit (JP 3-07.3). Units have three techniques for conducting a relief: sequentially, simultaneously, or staggered. A sequential relief occurs when each element in the relieved unit is relieved in succession, from right to left, left to right, front to rear, or rear to front. A simultaneous relief occurs when all elements are relieved at the same time. A staggered relief occurs when each element is relieved in a sequence determined by the tactical situation, not its geographical orientation. Simultaneous relief takes the least time to execute but is more easily detected by enemy forces. Sequential or staggered reliefs can occur over a significant amount of time. These three relief techniques can occur regardless of the operational theme in which the unit is participating. (See ADP 3-90 for more information about relief in place.)
PASSAGE OF LINES
6-159. A passage of lines is an operation in which a force moves forward or rearward through another force’s combat positions with the intention of moving into or out of contact with the enemy (JP 3-18). There are two types: a forward passage of lines and a rearward passage of lines. A forward passage of lines occurs when a unit passes through another unit’s positions while moving toward the enemy (ADP 3-90). A rearward passage of lines occurs when a unit passes through another unit’s positions while moving away from the enemy (ADP 3-90).
6-160. Units perform a passage of lines to continue their attacks or perform counterattack, retrograde, and security tasks that involve advancing or withdrawing through other units’ positions. A passage of lines potentially involves close combat. It involves transferring the responsibility for an AO between two units. That transfer of authority usually occurs when roughly two thirds of the passing force have moved through one or more passage points. The headquarters directing the passage of lines is responsible for determining when the passage of lines starts and ends. If not directed by higher authority, the stationary unit commander and the passing unit commanders determine—by mutual agreement—the time to pass responsibility for an area. They disseminate this information to the lowest levels of both organizations.
6-161. Units have several reasons for conducting a passage of lines. These reasons include to—
Sustain offensive tempo and avoid culmination.
Maintain the viability of the defense by transferring responsibility from one unit to another.
Transition from the performance of delay or security tasks by one force to a defending unit.
Relieve a unit for another mission or task.
(See ADP 3-90 for more information on passage of lines.)
COUNTERMOBILITY OPERATIONS
6-162. Countermobility is a set of combined arms activities that use or enhance the effects of natural and man-made obstacles to prevent the enemy freedom of movement and maneuver (ATP 3-90.8). The primary purposes of countermobility are to shape enemy movement and maneuver and to prevent the enemy from gaining a position of advantage. Countermobility is conducted to support forces operating along the range of military operations. Countermobility directly supports offensive and defensive operations.
6-163. In support of offensive operations, countermobility activities isolate objectives and prevent enemy forces from repositioning, reinforcing, and counterattacking. They enable flank protection as operations progress into the depth of enemy defenses or as an integrated economy-of-force effort to provide general flank security. In support of defensive operations, countermobility activities disrupt enemy attack formations and assist friendly forces in defeating the enemy in detail, to channel attacking enemy forces into an engagement area or areas throughout the depth of the defense, and to protect the flanks of friendly counterattack forces.
6-164. The conduct of countermobility activities typically requires engineers and includes proper obstacle integration with the maneuver plan, adherence to obstacle emplacement authority, and positive obstacle control. Combined arms obstacle integration synchronizes countermobility into the concept of operations. Because most obstacles have the potential to prevent the freedom of movement and maneuver to both friendly and enemy forces, it is critical that commanders weigh the risks and evaluate the trade-offs of employing different types of obstacles. Countermobility activities include—
Siting obstacles.
Constructing, emplacing, or detonating obstacles.
Marking, reporting, and recording obstacles.
Maintaining obstacle integration.
(See ATP 3-90.8 for more information on countermobility.)
MOBILITY OPERATIONS
6-165. Freedom to move and maneuver within an operational area is essential to applying combat power. Most operational environments and enemy forces present numerous challenges to movement and maneuver. Leaders overcome these challenges through the integration of combined arms mobility.
6-166. Mobility tasks are those combined arms activities that mitigate the effects of obstacles to enable freedom of movement and maneuver (ATP 3-90.4). There are six primary mobility tasks:
Conduct breaching.
Conduct clearing (of areas and routes).
Conduct gap crossing.
Construct and maintain combat roads and trails.
Construct and maintain forward airfields and landing zones.
Conduct traffic management and enforcement.
6-167. Mobility tasks enable friendly forces to move and maneuver freely on the battlefield. Effective execution of mobility tasks depends on information collection and intelligence. Breaching and gap crossing in support of maneuver are primarily conducted using combat engineer units, often during close combat.
6-168. Gap crossing, clearing, and the construction of combat roads and trails, forward airfields, and landing zones primarily support movement and require combat and general engineering units. Mobility tasks in support of movement are not normally conducted under fire, although the threat of fire is always present.
6-169. A breach is a synchronized combined arms activity under the control of the maneuver commander conducted to allow maneuver through an obstacle (ATP 3-90.4). A successful obstacle breach is a synchronized and rehearsed combined arms activity under the control of the maneuver unit. Breaching is a mission undertaken to penetrate an obstacle. Breaching facilitates penetrations through enemy reinforcing obstacles covered with direct and indirect fire.
6-170. Clearing is a mobility task that involves the total elimination or neutralization of an obstacle that is usually performed by follow-on engineers and is not done under fire (ATP 3-90.4). It is generally accomplished by destroying, altering, or removing obstacles.
6-171. A gap is a ravine, mountain pass, river, or other terrain feature that presents an obstacle that may be bridged (ATP 3-90.4). Gaps will exist in an operational environment and present a significant challenge to movement and maneuver. A gap crossing is the projection of combat power across a linear obstacle (a wet or dry gap).
SECTION II – DEFENSIVE OPERATIONS
6-172. Defensive operations defeat an enemy attack, buy time, economize forces, hold key terrain, or develop conditions favorable for offensive operations. Although offensive operations are usually required to achieve decisive results, it is often necessary, even advisable, to defend. Defensive operations alone do not normally achieve a decision unless they are sufficient to achieve the overall political goal, such as protecting an international border.
PURPOSE AND CONDITIONS FOR THE DEFENSE
6-173. One purpose of defending is to create conditions for the offense that allows Army forces to regain the initiative. Other reasons for conducting the defense include—
Retaining decisive terrain or denying a vital area to an enemy force.
Attritting or fixing an enemy force as a prelude to the offense.
Countering enemy action.
Accepting risk in one area to create offensive opportunities elsewhere.
6-174. There are many potential conditions for defensive operations. They include—
Enemy aggression initiating armed conflict requires forward-stationed friendly forces to defend to buy time and conserve combat power until reinforced.
Offensive operations culminate and the commander needs to build combat power while countering enemy offensive operations.
A unit is assigned an economy of force defensive role as a supporting effort.
The higher echelon headquarters directs a mission to defend an area, population, key infrastructure, or other key terrain in support of the overall course of action.
U.S. forces accomplish all objectives and transition to a defense to deter future enemy aggression.
6-175. The key to a successful corps or division defense is a concept of operations that allows defensive forces to break the enemy’s momentum and seize the initiative. Surprise is as important in defense as in offense, and the defensive concept should avoid obvious dispositions and techniques. When executing a defense, commanders orchestrate combat power from all available domains to synchronize effects at a decisive place and time that results in the enemy’s defeat. Commanders decide where to concentrate combat power and where to accept risk. Success may require that a defending unit exploit opportunities to seize the initiative, such as a spoiling attack or counterattack.
6-176. Time is often the most important resource for defending forces. The enemy chooses the time and location for its attack, so the amount of time friendly units have to prepare a defense is often unknown and usually inadequate. Defending corps and divisions must have a sense of urgency to complete their planning, coordinating, rehearsing, and conducting information collection. Their subordinate units need time to develop engagement areas by preparing battle positions, pre-positioning sustainment assets, and emplacing obstacles. Taken together this means that strict adherence to priorities of work and priorities of effort is critical to time management.
6-177. Defending commanders seek to create more time to prepare an effective defense. A corps or division commander may task-organize and resource a security force for employment in the security area to guard or cover main battle area forces as a means to create additional preparation time and prevent surprise. Commanders may also launch spoiling attacks, raids, or feints to disorganize enemy preparations and gain more time to prepare. A defender continually attacks enemy forces in depth with joint and Army fires and aviation to attrit the enemy force and disrupt its scheme of maneuver. Friendly conventional and special operations forces can slow an enemy attack by complicating the enemy force’s movements and supply. Uncertainty as to when or where enemy forces will attack requires a commander to maintain a larger reserve.
6-178. A successful defense requires the integration and synchronization of all available assets. The defending commander assigns missions, allocates forces (including the reserve), and apportions functional and multifunctional support and sustainment resources within the construct of main and supporting efforts. The commander determines where to concentrate defensive efforts and where to accept risks based on the results of intelligence preparation of the battlefield. This determination includes accounting for the enemy’s reconnaissance and surveillance efforts and the vulnerability of friendly troop concentrations to massed enemy fires. Commanders strive to counter enemy attacks by accounting for its capabilities in each domain that can influence friendly forces.
CHARACTERISTICS OF THE DEFENSE
6-179. Successful defenses share some important characteristics. They include—
Disruption—deceiving or destroying enemy reconnaissance forces, breaking up combat formations, separating echelons, and impeding an enemy force’s ability to synchronize its combined arms.
Flexibility—developing plans that anticipate a range of enemy actions and allocate resources accordingly.
Maneuver—achieving and exploiting a position of physical advantage over an enemy force.
Mass and concentration—creating overwhelming combat power at specific locations to support the main effort.
Depth—engaging multiple enemy echelons, enemy long-range fires, sustainment, and C2.
Preparation—preparing the defense before attacking enemy forces arrive.
Security—conducting security, protection, information activities, operations security, and cyberspace and electromagnetic warfare tasks.
(See ADP 3-90 for more information on the characteristics of the defense.)
ENEMY OFFENSE
6-180. Enemy tactics, capabilities, and probable courses of action all inform defensive planning. Defending commanders must see the terrain and their own forces from the enemy perspective in all relevant domains to anticipate both threat courses of action and friendly weaknesses that an enemy force could exploit. Defending commanders identify probable enemy objectives and possible enemy avenues of approach to achieve them. Understanding enemy capabilities in all domains is critical to devising the most effective friendly defensive schemes. Identifying enemy limitations helps determine opportunities to exploit friendly advantages.
6-181. At the initiation of offensive operations, enemy forces seek to disrupt and destroy friendly C2, apply overwhelming firepower, and rapidly penetrate friendly rear areas. They use information warfare to attack information systems, deceive, and protect their own information systems. Enemy forces use electronic attack and long-range strikes against C2 systems, information collection systems, air defense systems, and aircraft. The enemy’s goal is to weaken or destroy the joint force’s decision-making, air and missile defense, and air combat capabilities, which creates opportunities for enemy forces to achieve early decisive success.
6-182. A key to an enemy force’s ability to achieve early dominance is to strike first. General considerations that influence the enemy force’s decision to initiate offensive operations include when the enemy determines the joint force is unprepared for an attack, when the enemy identifies a weakness in the joint force that it can exploit, or when the enemy is fully prepared and can commit to operations at any time. The enemy’s decision is tied to factors that provide them with the greatest opportunity to win the first battle, which they believe greatly improves their chances for success in later operations.
6-183. An enemy force seeks to establish early advantages in the air, space, and cyberspace domains to set conditions for dominance in the maritime and land domains. An enemy force aims to prevent the joint force from introducing additional forces into the conflict region and to disrupt the friendly logistics systems enabling forward-positioned forces. Enemy forces concentrate their long-range attacks on C2 nodes, logistics bases, and assembly areas to disrupt the joint force’s defensive operations and to degrade the joint force’s ability to prepare for offensive operations.
6-184. When enemy leaders commit forces into ground combat during offensive operations, they typically attempt to conceal the location of their main effort with multiple fixing attacks on the ground, allowing them to isolate friendly forward units. Enemy forces use fires and electronic attack to disrupt critical friendly command posts, radars, and fire direction centers.
6-185. Generally, enemy forces seek to reinforce success, massing capabilities at a vulnerable point to achieve large force-ratio advantages to enable a rapid penetration of friendly defenses. Enemy leaders use mobile forces to exploit a penetration rapidly to the maximum possible depth to make the overall friendly defensive position untenable. Enemy forces seek advantages in both volume and range of fires to simultaneously mass fires at the point of penetration to enable rapid closure and breakthrough, fix other friendly elements along the forward line of own troops, and target key friendly C2 and logistics nodes along the depth of the defense. Enemy forces prefer to use fires to fix, move around friendly battle positions when possible, and move through destroyed units when necessary. Enemy forces seek to maneuver tactically to a depth that achieves operational objectives in support of their overall strategic purpose. Enemy forces employ reconnaissance, electronic warfare, information warfare, and other capabilities at their disposal to both enable and exploit initial tactical gains. These are likely to include chemical weapons. (See figure 6-4 on page 6-34 for an illustration of a notional enemy offensive operation.)

TYPES OF DEFENSIVE OPERATIONS
6-186. There are three types of defensive operations. These operations have significantly different concepts and present different problems. Units consider each independently when planning and executing the defense. Although the names of these types convey the overall aim of a selected operation, most defenses at division and higher echelons combine elements of all three types. The types of defensive operations are—
Area defense.
Mobile defense.
Retrograde.
AREA DEFENSE
6-187. An area defense is a type of defensive operation that concentrates on denying enemy forces access to designated terrain for a specific time rather than destroying the enemy outright (ADP 3-90). The variations of an area defense include defense of a linear obstacle, perimeter defense, and reverse slope defense. The purpose of an area defense is to retain the terrain where the bulk of the defending force positions itself in mutually supporting prepared positions. Units maintain their positions and control the terrain between these positions and focus their fires into engagement areas. Units may supplement these fires with a possible counterattack. Units at all echelons can conduct an area defense, and Army forces may have maritime engagement areas. They may use an area defense to transition to offensive operations, retrograde operations, or stability operations. (See ADP 3-90 for more information on area defense.)
MOBILE DEFENSE
6-188. A mobile defense is a type of defensive operation that concentrates on the destruction or defeat of the enemy through a decisive attack by a striking force (ADP 3-90). The mobile defense focuses on defeating or destroying enemy forces by allowing them to advance to a point where they are exposed to a decisive counterattack by a striking force. The striking force is a dedicated counterattack force in a mobile defense constituted with the bulk of available combat power (ADP 3-90). A fixing force is a force designated to supplement the striking force by preventing the enemy from moving from a specific area for a specific time (ADP 3-90). The fixing force is used to hold attacking enemy forces in position, to turn attacking enemy forces into ambush areas, and to retain areas from which to launch the striking force.
6-189. A mobile defense requires assigned areas of considerable depth. Units shape the battlefield causing an enemy force to overextend its lines of communications, expose its flanks, and dissipate its combat power. Likewise, units must be able to move their forces into a position where they can defeat an attacking force. Divisions and larger formations normally execute mobile defenses. (See ADP 3-90 for more information on mobile defense.)
RETROGRADE
6-190. A retrograde is a type of defensive operation that involves organized movement away from the enemy (ADP 3-90). The three variations of the retrograde are delay, withdraw, and retirement. An enemy force may compel these operations, or units may execute them voluntarily, such as when a security force executes a rearward passage of lines through a main battle area. In either case, the higher echelon headquarters executing the retrograde must approve the operation before its initiation. A retrograde is not conducted in isolation; it is a transitional operation. It is part of a larger maneuver scheme designed to preserve combat power for future operations. Forward-stationed forces should be prepared to execute retrograde operations as part of a multinational force when outnumbered during the early part of a conflict.
DEFENSIVE OPERATIONAL FRAMEWORK CONSIDERATIONS
6-191. In the defense, commanders typically retain the deep and rear areas, but they divide the close area into two distinct portions: the security area and main battle area. Commanders use this approach to synchronize operations, including those in air, space and cyberspace, to defeat an enemy force throughout its depth. Figure 6-5 on page 6-36 depicts friendly defensive operations across a notional operational framework.

EXTENDED DEEP OPERATIONS
6-192. Operational- and strategic-level deep operations are typically outside an assigned land AO for a corps or division, but parts fall within the senior Army formation’s area of interest and area of influence. During defensive operations, Army forces may request JFC or other strategic effects against strategic infrastructure or sanctuary areas that are enabling enemy offensive operations.
6-193. Strategic leaders may task Army long-range fires, cyberspace, space, and other global capabilities to support attacking targets in the extended deep area to set conditions for friendly defensive operations. Long-range artillery and ground-based missile capabilities can range enemy long-range missile batteries, manufacturing and economic nodes, critical infrastructure such as airfields and ports, strategic communications nodes, and strategic sustainment and reserve locations. Special operations forces, either unilaterally or combined with indigenous forces, can attack vulnerable targets, influence populations, and motivate or support established networks, such as local militias and resistance groups, to gather valuable information, oppose enemy forces, and weaken popular support to enemy offensive operations. Friendly-backed indigenous forces, or guerilla forces, can also damage or degrade critical infrastructure to disrupt enemy sustainment activities.
DEEP OPERATIONS DURING DEFENSIVE OPERATIONS
6-194. Deep operations are essential to the effectiveness of the defense. The commander uses them to attrit, isolate, disrupt, and disorganize attacking formations and to create windows of opportunity in which to act decisively against lead enemy echelons. Deep operations are the commander’s means of ensuring success in the main battle area by limiting the enemy’s options, disrupting the enemy’s ability to mass fires against friendly battle positions and denying the ability of subsequent echelons to support the lead echelon. Commanders use rocket artillery, rotary-wing aviation, UASs, special operations forces, space and cyberspace capabilities, electromagnetic warfare, and influence activities to conduct deep operations. Commanders request joint fires to divert, disrupt, delay, or destroy the enemy’s long-range capabilities before they are in direct contact with Army forces. The battlefield coordination detachment, as the senior Army operational commander’s liaison with the air component, serves a central role in relaying requests for joint fires to the joint air operations center. (See JP 3-03 for information on interdiction.)
6-195. Deep operations begin to disrupt the cohesion of the enemy attack as early as possible, before the enemy closes with maneuver forces in the security area. Psychological effects degrade the will of enemy forces to fight, interfere with enemy decision making, and disrupt enemy attacks as they begin, especially when combined with attacking C2 nodes, fires, and other key capabilities. Deception to conceal the location and disposition of defending forces and limit the effectiveness of enemy fires delays the enemy’s ability to mass effects. Army forces in the defense conduct deep operations to—
Isolate enemy forces in the security area and main battle area from follow-on echelons.
Disrupt the enemy’s ability to support committed forces with fires and logistics.
Guard against interference with the commitment of friendly reserves.
Attrit sufficient enemy combat power to achieve favorable force ratios in the main battle area.
Transition to the offense.
6-196. As part of conducting deep operations, corps and division commanders maintain a current intelligence picture of enemy forces throughout their area of interest. They coordinate for and integrate effects created by special operations core activities to achieve operational and strategic objectives and disrupt enemy forces, capabilities, and infrastructure that support enemy offensive operations. Commanders also ensure that deep operations remain focused on setting conditions for forces in the security and main battle areas while avoiding becoming overly fixated on close operations.
6-197. As enemy formations approach the forward line of troops, leaders monitor enemy movements, determine which elements of the enemy force are most threatening, and attack high-payoff targets, including enemy long-range fires, air defense systems, logistics assets, and C2 nodes. The commander uses reconnaissance and security forces and fires to disrupt the enemy approach and delay enemy second echelon forces and reserves in ways that desynchronize the enemy attack. When available, commanders employ offensive space and cyberspace capabilities in combination with electromagnetic attacks to disrupt enemy communications and hinder the enemy’s ability to adapt. Deep operations in the defense may also seek to suppress enemy air defenses to enable friendly air capabilities, including air interdiction and close air support, to operate in the security area and main battle area.
6-198. Commanders synchronize deep operations among subordinate echelons through the use of fire support coordination measures. Coordinated fire lines are permissive fire support coordination measures that commanders can use for rapid engagement of targets while simultaneously providing flexibility for friendly forces. In the defense, the corps establishes a coordinated fire line with subordinate divisions, so that the corps can target critical enemy capabilities with surface-to-surface fires beyond where the divisions need to focus in their own close and deep areas.
SECURITY AREA OPERATIONS
6-199. During the defense, the security force occupies an assigned area far enough forward of the forward edge of the battle area to protect main battle area units from surprise. Security forces provide early warning to give main battle area units time to reposition forces against enemy maneuver and to mitigate the effects of enemy medium-range fires.
6-200. Commanders have the option of employing a screen, guard, or cover in a security area, depending on the mission variables. When deciding which option to use, commanders consider the following:
The depth, breadth, and terrain of the security area relative to number of forces available.
The capabilities of the security force relative to the threat it faces, particularly its mobility.
The amount of time the commander needs the security force to provide forces in the main battle area.
6-201. Commanders determine the location, orientation, and depth of the security area based on the terrain available and the purpose of the defense. Units identify enemy avenues of approach and named areas of interest. The depth of the security area determines the time available to react to approaching enemy forces. Occupying a deep security area allows the security force to destroy enemy reconnaissance assets without compromising critical observation posts or positions. It prevents enemy forces from easily penetrating the security area and prevents gaps when observation posts or units displace or are lost. Security forces cover less depth along a broad front because they have fewer resources to position in depth and potentially fewer opportunities to exploit terrain. Shallow security areas may require units to task-organize and resource their security forces to perform guard operations that provide more reaction time for the main body.
6-202. The task organization of the security force depends on its role in the overall concept for defense. Covering forces and guard forces require more reinforcement than screening forces. Fires, engineers, aviation, and other attachments increase the ability of guard or covering forces to slow and disorganize the enemy, degrade the enemy’s security forces, and gain additional time for the defending commander.
6-203. Commanders determine when to occupy security areas based on their assessment of all possible enemy courses of action and the preparation required in the main battle area. They allow enough time for their security force to move and establish its positions. The mission variables influence how these security forces deploy and occupy positions. Commanders may push forward to establish a security area, or they may establish one along a current forward line of troops while preparing the main battle area further to the rear, depending upon the favorability of the terrain and enemy dispositions.
6-204. Information collection capabilities enable the performance of security tasks. Commanders focus their collection on named areas of interest to detect and track enemy forces. Data and reporting from UASs, intelligence operations, ground sensors, and national assets can expand the areas under surveillance, provide early warning, and cue security forces. Rotary-wing aircraft detect and report enemy forces at extended ranges with sensors. This permits security force units on the ground to concentrate their forces on likely enemy avenues of approach, named areas of interest, targeted areas of interest, and restrictive terrain that degrades sensor performance. Commanders employ their information collection assets to detect enemy force movements, which provides time to reposition security forces and employ assets to counter enemy actions.
6-205. The security force’s rear boundary is normally the battle handover line. Handover of the battle from forces in the security area to forces in the main battle area requires close coordination to avoid confusion and fratricide. The security force must retain freedom to maneuver to conduct a rearward passage of lines. Main battle area forces establish contact points, passage lanes, and routes through the main battle area. Control of indirect fires passes to main battle area units as the security force moves through the passage lanes. Typically, battalion-sized units of a security force hand the battle over to the brigades through which they pass. Regardless of size or echelon, they must be able to alert the main battle area commander that the enemy is approaching on particular avenues of approach and keep the enemy’s leading units under observation. After passage, security area forces move where directed and begin preparing for subsequent operations.
MAIN BATTLE AREA OPERATIONS
6-206. The main battle area is where the commander intends to deploy the bulk of the unit’s combat power and defeat an attacking enemy force. The commander positions forces in the main battle area to block enemy penetrations, choosing terrain that puts enemy forces at the greatest possible disadvantage. Commanders assign sectors to subordinate forces in the main battle area as a means of controlling subordinate maneuver unit operations. Defensive sectors should align with major enemy avenues of approach. The force responsible for the most dangerous sector is typically the main effort. Commanders employ their reserves in the main battle area to halt an enemy attack, to destroy penetrating enemy formations, or to counterattack to regain the initiative.
6-207. Restrictive terrain, choke points, and natural obstacles such as rivers usually favor an area defense oriented on key terrain and avenues of approach. Open, less restrictive terrain usually favors a mobile defense, which orients on the enemy. Most defenses at the division and corps levels offer opportunities for a combination of mobile and area defense. Corps and division commanders maintain situational awareness about close operations in the main battle area while maintaining focus on deep operations to prevent enemy forces from reinforcing or effectively supporting their forward echelons.
6-208. Spoiling attacks and counterattacks can be used to disrupt enemy forces and prevent them from massing combat power or exploiting success in the main battle area. Future operations cells conduct contingency branch and sequel planning to counter potential enemy penetrations of the main battle area, typically by repositioning forces and establishing decision points for committing the reserve.
RESERVE
6-209. Commanders base the size of their reserve on the level of uncertainty about the enemy force’s capabilities and intentions. A commander’s concept of operations describes the size, composition, location, and priorities of planning for the reserve. The more uncertainty that exists, the larger the reserve is. The purpose of the reserve during the defense is to maintain a hedge against uncertainty and counter enemy success, usually by blocking a penetration or enveloping it from a flank. When planning a defense, commanders cannot typically be strong everywhere, and therefore they accept risk about unlikely enemy courses of action. A reserve mitigates the risk the commander assumes. Commanders may use reserves to counterattack enemy vulnerabilities, such as exposed flanks or support units, or to defeat isolated parts of the enemy forward echelon. In some cases, a commander must use the reserve to reinforce battle positions in the main battle area to hold critical terrain, block penetrating enemy forces, or to react to threats against the division or corps rear area. Units position their reserve force for maximum flexibility.
6-210. Commanders determine the reserve’s planning priorities based on their estimate of the situation. Commanders of brigades or larger formations normally retain about one quarter of their force in reserve, though the percentage depends on the scheme of maneuver and the commander’s level of uncertainty. Higher levels of uncertainty require a larger reserve.
6-211. Timing is critical to counterattacks. Commanders must anticipate the circumstances requiring commitment of their reserve and rehearse its commitment to the main battle area. Rehearsals help validate the reserve’s response plan and increase the speed with which it can respond. Commanders make the decision to commit a reserve promptly, with sound understanding of the movement and deployment timelines from its assembly area to the main battle area in existing terrain and weather conditions. If committed too soon, reserves may not have the desired effect or be in a good position for commitment against a more dangerous situation later. Committed too late, the reserve may not be able to influence the situation enough to meet the overall intent. Movement control and air defense in the rear area is vital to getting the reserve into the battle on time and in good order.
6-212. Reserves may be air or ground maneuver units or a combination of the two. They should be task-organized with combined arms capabilities and given priority for the employment of joint capabilities. Commanders take the strengths and weaknesses of the reserve into account and plan accordingly. For example, employing an air assault force provides a formation that can respond rapidly to a threatened area or rapidly threaten an enemy flank after seizing key terrain. Once committed, however, it has limited mobility and sustainment capabilities.
6-213. The mobility and lethality of attack aviation makes it one of the most responsive and effective types of reserves. It can rapidly counterattack enemy armored penetrations. Despite its effectiveness, attack aviation should never be the only reserve element due to the potential impacts of weather and the risk incurred by not having enough aviation available for other critical roles, such as enabling security area operations.
6-214. Once commanders commit a reserve, they immediately begin to constitute another one from uncommitted forces or from forces in less threatened areas. When selecting the new reserve, commanders consider what capabilities would be most effective in the situation and the likely locations where it would be employed.
REAR OPERATIONS DURING DEFENSIVE OPERATIONS
6-215. Rear operations maintain freedom of action in the security and main battle areas and prevent culmination. The rear command post enables this freedom of action by planning and directing sustainment, conducting terrain management, providing movement control, and providing area security of the rear area. Rear operations ensure prompt delivery of commodities in high demand during defensive operations, particularly ammunition. Depending on the enemy situation, commanders commit maneuver units to secure rear operations, although all forces conducting rear operations must maintain local security and conduct survivability tasks. Leaders must consider the terrain, protection, and sustainment requirements for higher headquarters or joint enablers that may be located in the rear area. (See FM 3-94 for more information on the rear command posts.)
6-216. Because rear operations divert combat power from other priorities, commanders must weigh the need for this diversion against other potential consequences, and they must be prepared to assume risk based upon both mission analysis and running estimates. Assuming risk may be as simple as suspending all but critical operations in the rear area for a time, so that units operating in the rear area can concentrate on selfdefense at critical junctures.
6-217. Leaders mitigate vulnerabilities associated with command posts, support areas, staging areas, and transportation operations by doing everything possible to limit enemy detection, harden critical nodes, and counter enemy attacks before they can inflict significant losses. Effective counter-UAS operations are critical to countering enemy reconnaissance attempting to identify high-payoff friendly targets. Electromagnetic protection, limited offensive space control operations, dispersion, and repositioning capabilities within the rear area to complicate enemy targeting, particularly of critical C2 nodes, is very important during the defense when a division or corps is relatively static for extended periods of time. (See ATP 3-01.81 for more information on counter-UAS operations.)
TRANSITION TO OFFENSE
6-218. The ultimate goal of defensive operations is to defeat the enemy’s attacks and transition, or threaten to transition, to the offense. Units must deliberately plan for transitions to identify and establish the necessary friendly and enemy conditions for a successful transition. As friendly forces meet their defensive objectives, forces consolidate and reorganize for offensive operations or prepare to facilitate forward passages of lines for fresh formations. Units should do everything possible to prevent enemy forces from reinforcing their forward echelons, consolidating, or reorganizing while friendly forces prepare for follow-on operations.
6-219. Commanders transition to the offense when they assess they have enough combat power to maintain pressure on the enemy. They do not wait for perfect conditions, and they sometimes must push tired formations to attack because the opportunity to complete the defeat of enemy formations reduces the risk of future casualties fighting the same enemy formations after they have recovered. Commanders continuously assess the effects of battle on their formations relative to their opponents, and they let that assessment guide how hard they pursue enemy forces and how high of a tempo they sustain. (See ADP 3-90 for additional information on the defense.)
SECTION III – OFFENSIVE OPERATIONS
6-220. The key to successful offensive operations is to achieve all desired objectives prior to culmination. This requires the force in the offense to have some combination of relative advantage in the physical, information, or human dimensions. Typically, offensive operations require advantages in multiple domains, but commanders may achieve those advantages through deception operations and surprise rather than the physical means of combat power alone.
PURPOSE AND CONDITIONS FOR THE OFFENSE
6-221. The purpose of the offense is to defeat or destroy enemy forces and to gain control of terrain, resources, or population centers. Offensive operations take something from an enemy force. They are characterized by aggressive initiative on the part of subordinate commanders, by rapid shifts of the main effort to create and exploit opportunity, by momentum, and by the deepest, most rapid possible destruction of enemy defensive schemes and the capabilities that enable them.
CHARACTERISTICS OF THE OFFENSE
6-222. The high risk, tempo, and physical toll of offensive operations require high levels of unit training, morale, and cohesion. Successful offenses share these characteristics:
Audacity—the ability to assume risk to create opportunity with bold action.
Concentration—orchestrating forces or effects to create and exploit opportunity. (Concentrating effects is called “mass.”)
Surprise—taking action that catches enemy forces off guard.
Tempo—maintaining a pace of operations that is faster than the enemy’s, but not so fast that it cannot be sustained for as long as necessary to achieve all assigned objectives.
(See ADP 3-90 for more information on the characteristics of the offense.)
ENEMY DEFENSE
6-223. The purposes of enemy defensive operations are to set military conditions to resume offensive operations or defend until the enemy achieves a favorable political outcome. The enemy employs two types of defenses generally, a maneuver defense and an area defense. A maneuver defense trades terrain for the opportunity to destroy portions of an opponent’s formation and render the opponent’s combat system ineffective. In an area defense, the enemy denies key areas to friendly forces. In most situations against a peer or superior opponent, enemy forces are willing to surrender terrain to preserve their major combat forces, since the loss of those forces threatens the survival of the enemy’s state or regime. Figure 6-6 on page 6-42 depicts a notional enemy maneuver defense.
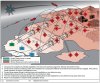
6-224. The enemy establishes a defensive system on favorable terrain and employs capabilities throughout the depth of the battlefield. The enemy’s goal is to resist the joint force’s ability to attack in depth by creating layered standoff that makes integrated action between ground forces and the rest of the U.S. joint force impossible. In the disruption zone, enemy forces attack the joint force with long-range fires and limited objective attacks by ground forces to preempt or disrupt the joint force’s planned attack. Enemy forces employ aviation, artillery, and ballistic missiles in long-range attacks against the joint force’s C2 systems, long-range fires capabilities, attack helicopters, logistics bases, and assembly areas. The enemy uses special operations forces, guerilla forces, and proxy forces in limited objective attacks to harass and disrupt the friendly forces’ preparations for offensive operations.
6-225. In the main battle zone, the enemy force designs its defensive system to defeat penetrations of its main defensive lines and envelopments by the joint force’s ground, airborne, or air assault forces. Along its defensive lines, the enemy attempts to slow and disrupt friendly forces with a combination of obstacles, prepared positions, electronic warfare, and favorable terrain. The enemy’s basic goal is to fix friendly forces with maneuver units and destroy them with massed fires in a layered defensive approach. The layered approach starts with identifying friendly units with long-range air, space, and cyberspace capabilities and then targeting them with fires before they are in range to maneuver during close combat. Ideally, they would attrit friendly forces to the point that they lack the combat power to exploit any initial successes they achieve.
6-226. Enemy forces continuously improve positions in ways that make attacks against them more costly and allow enemy forces to commit the minimum amount of ground combat power forward. Enemy forces use deception, dispersion, and repositioning to avoid easy acquisition by friendly information collection systems. Enemy forces typically employ significant reserves to counterattack penetrations and attempted envelopments. Integrated air defense systems arrayed in depth provide protection and freedom of movement for enemy maneuver units and fires systems.
6-227. Forward-positioned enemy forces focus on providing observed fires for long-range surface-to-surface systems and fixing friendly forces long enough to be engaged effectively by those systems. Enemy forces are likely to conduct a maneuver defense, whenever they are able, by using a series of subsequent battle positions to achieve depth. An enemy commander seeks to use fires and obstacles to prevent decisive engagement of the defending ground forces as they reposition, while causing friendly forces to move as slowly as possible under continuous fire. An enemy force can be expected to employ significant electronic warfare, reconnaissance, surveillance (including UASs), and cyberspace capabilities as part of this defensive effort. Peer enemies can employ chemical weapons, and some can employ tactical nuclear weapons, to prevent the culmination of their defending forces.
TYPES OF OFFENSIVE OPERATIONS
6-228. The types of offensive operations describe the general sequence of the offense and recommended formations. The purpose discriminates one from another. The four types of offensive operations are—
Movement to contact.
Attack.
Exploitation.
Pursuit.
MOVEMENT TO CONTACT
6-229. Movement to contact is a type of offensive operation designed to develop the situation and to establish or regain contact (ADP 3-90). It creates favorable conditions for subsequent tactical actions. Units conduct a movement to contact when the enemy situation is vague or not specific enough to conduct an attack. Forces conducting a movement to contact seek to make contact with the smallest friendly force feasible. A movement to contact may result in a meeting engagement. A meeting engagement is a combat action that occurs when a moving force, incompletely deployed for battle, engages an enemy at an unexpected time and place (ADP 3-90). If friendly forces make contact with an enemy force, they have five options: attack, defend, bypass, delay, or withdraw.
ATTACK
6-230. An attack is a type of offensive operation that destroys or defeats enemy forces, seizes and secures terrain, or both (ADP 3-90). Attacks incorporate coordinated maneuver. An attack is different from a movement to contact since knowledge of the enemy’s disposition enables units to synchronize and employ combat power more effectively. There are four variations of attacks:
Ambush.
Counterattack.
Raid.
Spoiling attack.
EXPLOITATION
6-231. An exploitation is a type of offensive operation that usually follows a successful attack and is designed to disorganize the enemy in depth (ADP 3-90). Exploitations seek to disintegrate enemy forces to the extent that they have no alternative but surrender or retreat. Division and higher echelon headquarters normally plan exploitations as branches or sequels to current operations.
PURSUIT
6-232. A pursuit is a type of offensive operation designed to catch or cut off a hostile force attempting to escape, with the aim of destroying it (ADP 3-90). Pursuits entail rapid movement and decentralized control. Any offensive operation can transition into a pursuit if enemy resistance breaks down and enemy forces flee. Generally, a pursuit normally follows a successful exploitation. There are two types of pursuits:
Frontal.
Combination.
OFFENSIVE OPERATIONAL FRAMEWORK CONSIDERATIONS
6-233. Within the context of the higher echelon commander’s operational framework and the general phasing scheme, commanders must design attacks that defeat enemy forces across all echelons, while enabling subordinate disciplined initiative. When designing attacks, commanders divide the task of defeating an enemy force and maintain an integrated approach through deep, close, and rear operations. Commanders account for air, space, cyberspace, and when relevant, maritime capabilities across the operational framework. Figure 6-7 illustrates friendly offensive operations across a notional operational framework.

EXTENDED DEEP AREA DURING OFFENSIVE OPERATIONS
6-234. The extended deep area is an important part of any formation’s area of interest because it contains enemy capabilities that can inflict damage on friendly forces and affect friendly forces’ operational reach and endurance. Enemy strategic C2 nodes and long-range fires capabilities, including ground-based missiles and aviation assets, are generally located in the extended deep area out of the corps or division’s AO. The situation in the extended deep area influences future operations, and it may become part of an assigned area when offensive operations progress, forward boundaries advance, and units move around the battlefield. Commanders integrate the effects and activities of special operations forces and partner irregular forces in extended deep areas. Army forces request joint effects in the deep area, and they may be tasked by the JFC to employ long-range fires against targets in the extended deep area. Disrupting enemy decision making or destroying enemy long-range fires capabilities limits the enemy’s ability to mount a coordinated defense and can destroy enemy forces reconstituting or preparing for counterattacks.
DEEP OPERATIONS DURING OFFENSIVE OPERATIONS
6-235. Deep operations focus on parts of an assigned area that are not in direct fire contact with the main body of the formation but may be in the future. At division and corps, which have assigned and attached long-range fires capabilities, the deep area extends beyond the forward line of troops to a distance that corresponds with the ability of Army and joint capabilities to reach. Divisions and corps integrate special operations forces, depending on C2 relationships, with deep operations to degrade the enemy’s will to fight, destroy high-payoff targets, and disrupt enemy defensive infrastructure and sustainment. Special operations forces operating in deep areas require control measures to synchronize actions and mitigate risk.
6-236. Commanders use graphic control measures in the deep area to delineate responsibility for targets, employment of fires, axes of advance, and future ground objectives. Forward boundaries, coordinated fire lines, fire support coordination lines, kill boxes, and restricted fire areas are all coordination measures that commanders use to integrate deep operations among echelons.
6-237. Commanders synchronize joint and organic lethal and nonlethal effects in the deep area to disrupt enemy echelons, neutralize reserves, and destroy key capabilities including counterbattery radars and fires systems that can impact close operations. For example, a commander may combine massed fires against the enemy reserve with military information support operations, attacking that unit’s resupply operations to psychologically isolate it from the main body and erode its will to fight.
6-238. Corps and divisions may use their indirect fires capabilities to support close operations and to conduct deep operations. Commanders employ reconnaissance and security forces, both air and ground, to make initial contact, detect targets, and facilitate fires in support of deep operations. They may shift priority of fires from deep to close operations in support of the main effort.
6-239. Commanders may also employ reconnaissance and security forces to conduct deep operations. Commanders may task-organize dedicated security forces to make contact with the smallest possible ground formations and to develop the situation before the main body can be decisively engaged. Normally an attacking unit does not need extensive forward security forces; most attacks are launched from positions already in contact with the enemy, which reduces the usefulness of a separate forward security force. An exception occurs when the attacking unit is transitioning from the defense to an attack, and it had previously established a forward security area as part of the defense.
CLOSE OPERATIONS
6-240. Close operations occur where forces at divisions and lower echelons maneuver and where forces at the BCT and lower echelons conduct most direct fire engagements. BCTs and lower echelon formations destroy or render enemy forces combat ineffective through movement and fires during close operations. Close combat at the BCT-level and below relies heavily on the warfighting skill and determination of leaders and small-unit teams. Battle drills and creating effects from massed indirect fire play a critical role in success during close combat, since immediate action or reaction can determine success and failure.
6-241. When commanders achieve their initial objectives in the close area, they transition to the next phase of the operation, or they execute a branch or sequel should the situation require a change to the original plan. A branch may require friendly forces to defeat a counterattacking enemy force on the division’s flank with joint capabilities or reserves. When commanders defeat most enemy defensive forces, they may transition some of their focus to consolidating gains. For example, when lead friendly echelons fix and bypass enemy forces to maintain momentum, follow-on friendly forces must defeat the bypassed enemy forces to prevent them from disrupting friendly lines of communications, negatively influencing local populations, or breaking out. Commanders initiate operations to consolidate gains as early as possible, while still in close proximity to enemy units, to mitigate the risks those enemy units breaking contact could generate later.
6-242. Close operations require graphic control measures to synchronize the application of combat power, to ensure integration of subordinate units, to maintain maximum pressure on the enemy, and to mitigate the risk of fratricide within the friendly force. There is no arbitrary benefit to minimizing or maximizing the number of graphic control measures for a particular operation. The optimum number of graphics depends on the mission variables. Having many graphics provides options and agility to the plan, and this can be especially helpful in air-ground coordination or facilitating rapid changes of direction. Leaders balance the complexity of control measures. They should be simple enough for bold execution and detailed enough to enable agility and adaptation based on the situation. The best approach for employing control measures is to ensure they maximize subordinate unit freedom of action and prevent subordinate units from having more tasks than they can reasonably accomplish.
6-243. Commanders adjust the employment of graphic control measures according to the situation, but they always consider the range and speed of subordinate unit capabilities and their overall operational tempo. As units move forward, rear boundaries typically require corresponding shifts to ensure the unit’s assigned area does not exceed its area of influence. BCTs have limited ability to control long lines of communication, and their tempo and endurance is affected by time and distance of resupply, casualty evacuation, and other sustainment considerations. Division boundaries require similar considerations, with the added complexity of displacing division C2 nodes to support operations. Moving a division C2 node requires careful planning to maintain continuous C2 of subordinate formations and avoid unnecessary tactical pauses.
6-244. Commanders and staffs maintain situational awareness about adjacent friendly and enemy units in their area of interest. Although commanders and staffs have a plan for where a zone of attack will be and can use it to create initial boundaries and other graphic control measures, enemy forces operate independently of them. This means that while friendly forces have some constraints or restrictions in terms of employing capabilities outside of their assigned area, enemy forces do not. This requires friendly forces to understand what enemy capabilities outside their assigned area can influence friendly operations and closely coordinate responses with friendly units to the flanks and rear.
REAR OPERATIONS DURING THE OFFENSE
6-245. Rear operations encompass a wide range of activities directly controlled through the rear command post of a corps or division. Rear operations include sustainment operations, support area security, risk mitigation of areas not assigned to subordinate units, terrain management, movement control, coordinating and synchronizing protection capabilities, consolidating gains, and conducting stability operations as required. Corps and division reserves typically occupy positions in the rear area before their commitment, and they must receive priority of movement through the rear area when they are repositioned or committed. Rear operations contribute to the operational reach, tempo, freedom of action, endurance, and momentum of the whole formation.
6-246. Rear operations must adapt to the forward progress of the attacking divisions or BCTs. This may require moving support units, the rear command post, and sustainment activities forward as an attack progresses. The rear command post typically assumes responsibility for much of the new land area gained by the attacking forces. The division rear command post must be prepared to assume responsibility for the land areas left by forward-moving forces. In particular, it must be ready to control and repair routes, manage terrain for follow-on support units, and assure that the division reserve can move without obstruction. These activities may also require the rear command post to direct the reduction of explosive ordnance threatening critical infrastructure or key resources.
6-247. Tactical units move through rear areas on their way to being integrated into corps or division operations. These units report through the rear command post and occupy assembly areas designated by the rear command post until they are able to integrate with the main command post, should they be employed as part of close or deep operations. Long-range fires, ADA, CBRN decontamination, aviation, and reserve units occupy assembly areas and other positions in the rear area. Their requests for fires and other enablers, their use of ground and airspace, and their other operations are coordinated through the rear command post, unless otherwise directed by the main command post.
6-248. Commanders typically economize combat power reserved to protect their rear operations. Bypassed enemy forces, enemy special operations forces, and irregular forces pose a significant threat to rear operations. Typically, divisions assign a BCT to provide security and consolidate gains in rear areas. Maneuver enhancement brigades, with augmentation, employ a tactical combat force to defeat Level III threats throughout the support areas, including major sustainment nodes and main supply routes. (See JP 3-10 for more information on threat levels.)
6-249. Rear operations play a key role during transitions. For example, a transition between defense and offense increases the amount of fuel, maintenance, and movement support required for operations. A transition to stability operations requires greater humanitarian aid supplies, force protection and construction material, and contract support.
6-250. When required, commanders conduct reconstitution operations in the rear area, where enemy direct fire contact is unlikely. While reconstitution operations are dominated by sustainment factors, they are not the exclusive responsibility of sustainment units. All warfighting functions contribute to an effective reconstitution.
6-251. As stability becomes a greater focus of operations, commanders must assess the resources available against the mission to determine how best to conduct the minimum-essential stability operations tasks and what risk they can accept. The land component commander can establish a civil affairs task force to operate in the rear area and form a transitional military authority or support civil administration that facilitates the ultimate consolidation of gains in support of the desired strategic end state. The purpose of the civil affairs task force is to concentrate stability operations in an AO under a commander’s main effort. Additionally, commanders may require Soldiers from all branches to conduct civil security related tasks such as transitional public security tasks until local security forces are able to conduct these tasks. The speed with which transition from U.S. forces to local authorities occurs is dependent on the ability to plan and control elements aimed at developing and legitimizing governance at the tactical and operational levels. (See FM 3-57 for more information regarding the civil affairs task force.)
TRANSITION TO DEFENSE AND STABILITY
6-252. When offensive operations culminate before enemy forces are defeated, friendly forces rapidly transition to the defense. Commanders may deliberately transition to the defense when enemy forces are incapable of fully exploiting an opportunity, or when they believe they can build combat power to resume the offense before enemy forces can react effectively. Depending on where culmination occurs, friendly forces may have to reposition forces on defensible terrain and develop a form of defense and scheme of maneuver based on an assessment of the mission variables.
6-253. Successful offensive operations end because Army forces have achieved their assigned objectives. A successful offense can also require a transition to a defensive posture dominated by stability operations and a strategic environment moving toward post-conflict political goals. These operations have the goal of transitioning responsibility for security and governance to legitimate authorities other than U.S. forces.
6-254. As a transition to stability operations occurs, leaders focus on stability tasks and information activities to inform and influence populations and conduct security force assistance. Effective collaboration with diplomatic and humanitarian organizations enhances the ability to achieve stability mechanisms. Army forces play a key role in enabling the joint force to establish and conduct military governance until a civilian authority or government is given control of their assigned areas.
TRANSITION TO POST-CONFLICT COMPETITION
6-255. Army forces conclude armed conflict by establishing conditions that are favorable to the United States on the ground. Army forces support these conditions throughout armed conflict by consolidating gains and prosecuting operations with desired end state in mind. As hostilities end, stability tasks dominate operations with the purpose of transitioning responsibilities to legitimate authorities in a secure environment. Army forces provide the joint force with the option of establishing a military transitional government before transitioning full governing responsibility to host-nation or other provisional governments.
6-256. Standards for transitioning governance responsibility depend on the credibility, capability, and capacity of the governing organization to maintain the favorable conditions established during armed conflict. Strategic leaders determine the broad conditions for transition at the outset of operations and refine them based on how the situation changes. Army forces play a key role in understanding the host-nation culture, understanding critical infrastructure, assisting strategic leaders in the development of realistic transition goals and timings, and determining the duration and scale of U.S. commitments required to maintain stability.
THEATER ARMIES DURING TRANSITION TO POST-CONFLICT COMPETITION
6-257. Theater armies play a key role in transition to post-conflict competition. Unlike JTFs that are created for limited durations, theater armies maintain a continuous, long-term focus on theater strategy and relevant national interests. A theater army anticipates and requests the additional forces, functional capabilities, and resources required to support transition. Theater requirements will change as combat operations reduce and focus on stability tasks increase. Theater armies refine logistic estimates, update security cooperation plans, request engineer units capable of infrastructure development, refocus civil affairs requirements, improve communications infrastructure, and address any other critical requirements.
6-258. Enabling legitimate authorities requires coordination with unified action partners, as well as a favorable attitude among the population towards friendly forces supporting the effort. The theater army’s goal is to replace U.S. combat forces with host-nation or other provisional authorities.
6-259. Security force assistance (SFA) is a key component of any plan to transition. SFA requires trained, educated professional officers and noncommissioned officers as trusted advisors to partner-nation security forces. A theater army supports JFCs in integrating conventional forces and special operations forces into SFA plans that support transition and sustainable political outcomes.
6-260. The theater army engages other regional actors to assist in promoting the stability of the region and managing the transition. In most cases, successful transition requires the theater army to retrograde equipment, close the JOA, coordinate for the redeployment of Army forces, and manage a long-term security cooperation plan. Relationships with regional leaders help to facilitate these requirements and provide stability for local populations.
CORPS DURING TRANSITION TO POST-CONFLICT COMPETITION
6-261. Corps play a key role in transitioning from combat to stability-focused operations. As part of this, consolidate gains activities may require the Army corps to employ forces to perform these tasks:
Establish area security throughout the entire corps AO. This includes offense and defense tasks to destroy or neutralize remaining threats and protect the civilian population and infrastructure.
Conduct stability tasks necessary to create conditions that allow for the eventual transition to a legitimate authority.
Conduct security force assistance to build the capability and capacity of foreign security forces.
Dissuade enemies and adversaries from reinitiating hostile or disruptive operations and persuading them to abide by sanctions, laws, or international dictates.
Coordinate and influence the assumption of responsibility by host-nation or other authorities.
Synchronize psychological actions aligned with friendly unit activities (including deeds, words, and images) to favorably influence civilian attitudes toward friendly security forces and the eventual transition to legitimate authority.
6-262. As large-scale combat operations conclude in a corps AO, the corps continues to adjust its operational framework to meet the increasing demand on stability tasks, while maintaining a posture that prevents enemy forces from reconstituting their forces and operations. Operations primarily focus on providing area security in high threat areas, followed by the performance of stability tasks in lower threat areas. During transition, corps will likely conduct simultaneous offense, defense, and stability operations.
DIVISIONS DURING TRANSITION TO POST-CONFLICT COMPETITION
6-263. During transition, divisions will likely conduct simultaneous offense, defense, and stability operations. Divisions must sustain those forces in combat operations concurrently with stability operations. In addition, division support assets must be prepared to displace from established support areas, through areas where security may not yet be established, to new support areas to better support those forces in combat operations prior to area security being established.
6-264. Divisions perform the stability tasks necessary to create conditions within an AO that allow for transition to a legitimate civilian authority or a unified action partner to act as a transitional authority. Divisions also manage brigades as they conduct SFA to build the capability and capacity of foreign security forces. Finally, divisions dissuade adversaries from reinitiating hostile or disruptive operations and persuade them to abide by sanctions, laws, or international dictates.
BRIGADES DURING TRANSITION TO POST-CONFLICT COMPETITION
6-265. Task-organized BCTs perform most area security tasks, and they facilitate the accomplishment of most stability tasks in concert with unified action partners. Army forces take specific actions upon culmination of large-scale combat operations. These actions include—
Consolidation.
Establishing area security.
Conducting stability tasks.
6-266. The transition from large-scale combat operations to area security tasks entails risk. Units shifting focus from combat to consolidation are vulnerable to counterattack. Historical evidence suggests a force is most vulnerable after a hard-fought win. Commanders and staffs should plan for a quick transition and stress the importance of local security. (See FM 3-90-1 for additional information on consolidation.)
6-267. Forces first perform minimum-essential stability tasks, and then they maintain or reestablish a stable operational environment and provide essential governmental services, emergency infrastructure reconstruction, and humanitarian relief. BCTs further develop and reassess situations, perceptions, and opportunities through continuous information collection to maintain positive momentum to achieve additional gains.
Chapter 7 - Army Operations in Maritime Environments
This chapter describes Army operations in a predominantly maritime environment. It begins with a discussion of the unique characteristics and challenges posed by maritime regions. It continues with a discussion of maritime planning considerations, and it concludes with a description of a potential operational approach for a maritime environment.
SECTION I – OVERVIEW OF THE MARITIME ENVIRONMENT
7-1. Previous conflicts have proven the critical role of land forces in maritime theaters. In almost all cases it is land that makes a maritime area important to a combatant commander. Land masses near or surrounded by water create maritime choke points, enable force projection in and out of maritime areas, and contain the majority of the world’s population. The ultimate objective of conflict is typically not control over vast expanses of open water, but rather the land and people who control it. Planning and training for the unique considerations of operations in these environments is critical, as is an integrated planning approach with the rest of the joint force. A maritime operational environment adds coordination and synchronization requirements for Army echelons that typically operate and train in land operational environments. Army and joint force planning must reflect an understanding of the dynamic nature of the threats and constraints to land forces in maritime regions. Army movement and maneuver between land masses is almost entirely dependent on joint capabilities. Control of critical land masses is essential to the sustainment and protection of joint operations in a maritime operational environment. This interdependence has been historically crucial to success during armed conflicts against peer threats in maritime theaters, and it continues to be crucial in the foreseeable future.
PHYSICAL CHARACTERISTICS OF THE MARITIME ENVIRONMENT
7-2. Habitable land masses vary in size and geology. They include land masses as large as Australia to small islets that make up larger atoll systems, such as the Marianas islands in Micronesia or Alaska’s Aleutian Islands chain. Regardless of their size, not all islands are suitable for extended occupation without externally provided water and other supplies. While most islands are natural, formed by tectonic or volcanic action, manmade islands created for military and other purposes are also found within certain regions, such as the South China Sea. Maritime land masses include a variety of environmental conditions. Islands throughout Southeast Asia are predominantly jungle and savanna regions. Islands throughout the Baltic, Arctic, and subArctic regions may experience prolonged periods of extreme cold weather. Mountainous terrain can be found on jungle, Arctic, and desert islands. Each island can contain unique environmental planning considerations that can affect the way Army forces are resourced and employed. (See ATP 3-90.97 for more information on cold weather environments. See ATP 3-90.98 for more information on operations in jungle environments. See ATP 3-90.99 for more information on operations in desert environments.)
7-3. Currently, 22 nations in the world are recognized as archipelagic states, and these unique maritime nations can include several cultures, religions, languages, and geopolitical histories within their own territorial boundaries. Regional influences, littoral urbanization, external actors, regional geopolitical perspectives, and local economic conditions may change from island to island, even when those islands comprise a single country. Commanders and staffs must understand these complex factors to influence outcomes in the human and information dimensions of an operational environment. Corps, divisions, or even brigades may have an area of operations (AO) that spans several islands, each with a unique culture and history.
7-4. In a predominantly maritime environment, any land that can be occupied to attain a physical position of relative advantage by friendly or enemy forces can become key terrain. The largely maritime domains challenge planners to account for operational reach and the impact of space and time on reinforcement of existing forward-stationed forces and allies. The distance between bases throughout the maritime regions hinders mutually supporting operations and sustainment from supporting echelons in the theater. Remoteness and distance increases vulnerability to amphibious raids by enemy special operations forces and attacks from long-range aircraft or missiles, and it increases the risk of physical isolation by air and naval forces.
LITTORAL REGIONS
7-5. Maritime environments include littoral regions, divided into two segments: seaward and landward. Seaward segments include the area from open ocean to the shore, which must be controlled to support operations ashore. Landward segments are those areas inland from the shore that can be supported and defended directly from the sea. Maritime littoral regions are divided into five categories:
Enclosed and semi-enclosed seas—bodies of water surrounded by a landmass and connected to either an ocean or another enclosed sea by a connecting body of water, such as a strait.
Islands—single land masses surrounded by a body of water.
Archipelagoes—groups of islands.
Open seas—unenclosed bodies of water, typically outside of territorial boundaries.
Marginal seas—portions of open seas or oceans that bound land masses such as peninsulas, islands, and archipelagos.
7-6. Operations in these environments require information concerning tides in the local area, average wave heights, and daily wind forecasts, as tides and winds may unexpectedly impact wave heights. Tidal flow and currents impact operations for small or shallow draft vessels. Tidal changes can also affect vehicle mobility when crossing unimproved beachheads or operations without causeways or engineer support. Extreme weather plus the corrosive effects of salt water can rapidly degrade the maintenance readiness of equipment already at the extent of long logistics lines of communications.
ARCTIC REGION
7-7. The Arctic region is significantly influenced by maritime considerations. The Artic encompasses part of the areas of responsibility of three different geographic combatant commands, eight countries, and all time zones. There are two primary transit routes through the Arctic: the Northwest Passage and the Northern Sea Route. The Arctic is a geopolitically competitive region and a potential area for armed conflict. There are various international partnerships and alliances within the region, with overlapping relationships complicated by international disputes about maritime boundaries. The Arctic presents a harsh and demanding maritime, land, and air environment for military operations. Extreme temperatures, long periods of darkness and extended daylight, high latitudes, seasonally changing terrain, and rapidly changing weather patterns define Arctic conditions, and they all have impacts on the operational and mission variables. The variability of the physical terrain and weather exposes military forces and capabilities to increased levels of risk.
7-8. The Arctic is not challenging solely due to extreme cold temperatures. Ground mobility is typically most favorable during the winter months. Summer poses significant challenges for most vehicles moving off road, while the most challenging period is the spring thaw when ground movement becomes impossible across large swaths of territory. Regardless of season, air and sea mobility are critical enablers for military operations. Thawing permafrost affects infrastructure across the region. Lacking the climate moderating effect of the warm Gulf Stream, the North American Arctic hosts a much harsher environment than the European Arctic. The warming of the Arctic has led to longer windows of reduced ice conditions over a larger area. Long-term trends indicate a more consistently navigable Arctic, potentially affecting the mobility of Army and threat forces during armed conflict.
7-9. Operations in the Arctic region get more complicated when roadways, seaports, and airfields can become unusable depending on seasons. The loss or change of sea ice can open new waterways and increase transit through the region. This could require additional forces, equipment capability, and infrastructure investments to secure the U.S. homeland, allied partners and infrastructure, or the northern avenues of approach during armed conflict.
CONSIDERATIONS UNIQUE TO THE MARITIME ENVIRONMENT
7-10. Threats to Army forces in a maritime theater include those in any other type of theater. Additionally, commanders and staffs must take into account unique joint and enemy courses of action in planning and executing operations in a maritime environment.
JOINT FORCE CONSIDERATIONS IN A MARITIME ENVIRONMENT
7-11. The heavily interdependent nature of joint operations means that the defeat of one part of the joint force puts the other parts at significant risk. The failure of Army forces to retain key terrain or protect air and naval bases while preserving their own combat power could result in the loss of air and maritime superiority, which in turn could lead to the ultimate defeat in detail of unsupported Army forces in an entire area of responsibility (AOR).
7-12. Army forces require a joint common operational picture (COP) of friendly forces and their operations, including those of allies and partners, in all domains. An inaccurate joint or partner COP could cause flawed assumptions and situational understanding that decreases effective decision making.
7-13. As with other environments, planning land operations in maritime environments should address relevant factors affecting friendly and enemy operations. The products and tools typically gathered to plan and portray the unique characteristics of a maritime environment include riverine and coastal navigation charts or tidal reports and observations from local fishing communities. Additional characteristics to consider include—
Coastal terrain and soil compositions.
Commerce and trade along navigable waterways.
Maritime-specific infrastructure.
Navigable bodies of water.
Population densities and variations along shores and near navigable waterways.
Tidal flow, surf conditions, and current directions.
Natural obstacles adjacent to terrain (including sandbars, shoals, mud flats, and dunes).
ENEMY COURSES OF ACTION UNIQUE TO THE MARITIME ENVIRONMENT
7-14. Enemy forces have the ability to take multiple actions unique to the maritime environment to hinder joint operations. They use capabilities from all domains to interdict lines of communications between the strategic support area and forward-positioned Army forces, putting forces at risk of isolation and beyond the supporting distance from other joint force elements. Enemy forces target shipping that carries the bulk of Army heavy equipment into theater and the pre-positioned equipment already in theater as part of their preclusion and isolation approaches. While Army forces can take measures to protect equipment already in theater, they are dependent upon the other Services for the protection of people, equipment, and supplies in transit.
7-15. Threats may employ asymmetric tactics to reinforce their area denial (AD) approaches throughout a region, capitalizing on the vulnerability of isolated friendly locations lacking adequate protection. Locations that cannot be reinforced or supported by other elements of the joint force are particularly vulnerable. Attacks by enemy special operations and naval forces are difficult for Army forces to detect and counter without proper positioning and preparation. Anticipating possible enemy courses of action in one region that would support a broad theater-wide outcome should drive friendly priorities of planning and preparation.
7-16. Enemy forces may use proxy forces to destabilize regional partners, further delaying Army forces from safely accessing basing and lines of communications. Proxy forces can facilitate enemy reconnaissance, surveillance, and disruption of joint operations. They can also affect access to sea-lanes and airports for transportation, hindering the resupply of island bases, and limiting the ability to reinforce forward-positioned friendly forces through attacks on bases and base clusters.
7-17. Enemy surface-to-surface and surface-to-air fires systems are critical to the layered defense and early warning systems necessary to attack forward-positioned friendly forces with little warning. These systems simultaneously prevent reinforcement or support of those friendly forces. Enemies position robust and integrated air and missile defenses, early warning surveillance radars, and electronic warfare capabilities that range elements of the U.S. joint force put them at risk during competition, crisis, and conflict. Enemy medium range ballistic missiles, cruise missiles, anti-ship missiles, and air and naval forces also put friendly forces at risk. This combination of systems warfare approaches threatens land-based forces even when they do not directly target them, since land-based forces require the support of air and maritime forces for sustainment, early warning, and protection.
ARMY-SPECIFIC CONSIDERATIONS
7-18. Commanders and staffs account for multiple considerations when planning and executing operations in a maritime environment. Counter-reconnaissance by Army forces on an island requires a 360-degree approach to avoid surprise. Responding to threats requires highly mobile capabilities that mass effects against enemy forces quickly. Although threats can approach from any direction to achieve surprise, there are constraints in terms of where enemy forces are able to land during an amphibious or air assault and range constraints that might cause aircraft to favor certain approaches. Intelligence preparation of the battlefield requires an understanding of air and maritime avenues of approach and their relationship to a particular land mass or grouping of land masses.
7-19. Army forces positioned at existing bases within the range of adversary long-range fires establish primary and alternate survivability positions for themselves while providing air and missile defense (AMD) and local security to airbases and ports. They may also be required to defend against amphibious assaults, and airborne or air assault operations by enemy forces seeking to control a particular land area or destroy critical infrastructure. Army forces operating on islands with austere infrastructure and resources require significant sustainment during prolonged operations.
7-20. Land areas able to accommodate significant military forces in strategically or operationally important areas are scarce in maritime environments, and what is available is already a known point for enemy planners. This makes surveillance of friendly activities simpler, affecting the ability to achieve surprise or avoid being surprised. It also makes the process of enemy observation, information collection, and subsequent targeting faster and more effective. The implications, with regard to friendly forces concealing and protecting themselves, are significant.
7-21. The British defeat in Malaya is a historical example of a poorly executed defense at both the operational and tactical levels. It also is an example of a peer threat exploiting superior planning, leadership, and aggressive action across multiple domains to overcome numerical inferiority against a defending force.
On 8 December 1941, Imperial Japanese forces launched the invasion of Malaya from their strongholds in French Indochina. Japanese intelligence suggested that General Yamashita’s 70,000 troops were outnumbered nearly 2 to 1, so he concluded that only a bold, rapidly executed attack with aggressive, well-trained troops would ensure victory. The British Empire was decisively engaged in North Africa, the battle of the Atlantic, and the defense of the home islands. While it deployed additional ground, naval, and air units to Singapore, the combination of time, distance, and demands in other theaters made further reinforcement unlikely. Those forces that arrived before the commencement of hostilities had little time to train or prepare for operations against an opponent of unknown quality in an unfamiliar environment.
The allied defense of Malaya rested on several false assumptions. First, allied forces assumed there would be sufficient warning of an attack, which in turn, would allow for adequate air and naval reinforcements. The few major naval reinforcements (the battleship Prince of Wales and battle cruiser Repulse) were sunk, and the aircraft rapidly lost against a qualitatively superior Japanese air arm. The Allies assumed that the dense jungle terrain would impede enemy ground movement and simplify defense of the peninsula; but it actually hindered the defenders more than the Japanese. They assumed the enemy main effort would come from the sea, which was the most heavily fortified part of their defense. It did not. They assumed their air force to be superior to that of the Japanese. It was not. They also assumed that the British and Commonwealth troops were better trained than the Japanese Army. They were not. These beliefs cost the Allies and provided an opportunity for the Japanese forces.
The Japanese launched a successful night amphibious assault on the northern coasts of Malaya and advanced south along the eastern coast. They also made simultaneous landings in Thailand, just north of the Malaya border, and sent units south into the interior and along the west coast. The Allies attempted to slow the Japanese advance with prepared positions along the roads and by destroying bridges, but the Japanese repeatedly bypassed or enveloped static positions by moving off the roads and conducting amphibious landings. On 10 December, Japan sank the last major allied naval units and achieved air supremacy.
By 27 January 1942, allied forces had retreated across the strait onto the island of Singapore. Japan subsequently invaded Singapore on 7 February and completed its conquest on the 15th. In just over two months, Yamashita’s 25th Army of 70,000 troops decisively defeated a defending force of over 140,000 soldiers at the cost of just under 10,000 casualties. Yamashita’s use of speed, maneuver, and surprise allowed him to dictate the operational tempo of the invasion. He ably exploited opportunities provided by the Japanese air and naval forces while generating his own with aggressive maneuver on the ground. The simultaneous presentation of multiple dilemmas across the air, maritime, and land domains led to the largest surrender of British forces in history. (See figure 7-1 for a map of operations in Malaya.)

SECTION II – MARITIME ENVIRONMENT PLANNING AND OPERATIONAL FRAMEWORK
7-22. Planning for operations in maritime environments requires commanders and staffs carefully consider the operational environment. Commanders and staffs need to consider that applying an operational framework in a maritime environment is significantly different than applying an operational framework to a land operation.
PLANNING CONSIDERATIONS FOR A MARITIME ENVIRONMENT
7-23. Planning for operations on land in maritime environments requires a high level of complex detail to coordinate the movement and landing of troops, equipment, and supplies by air and surface means. The success of Army operations in the maritime environment are uniquely dependent on unity of effort and integrated, collaborative planning with joint headquarters and subordinate echelons.
7-24. The joint force commander (JFC) for major maritime operations is typically a senior naval officer. The JFC ensures unity of effort across the joint force and ensures the task and purpose of Army operations nest with the overall joint operational concept. Despite the physical distances and relative isolation typically associated with land operations in a largely maritime environment, Army commanders must maintain situational understanding through joint collaboration to ensure their operations or activities do not have a negative effect on other operations or units. This includes maintaining situational awareness during movement, which requires direct and continuous integration of Army personnel into the command and control (C2) nodes of Marine Corps, Navy, and Air Force units. This may also include integration with multinational amphibious or maritime units.
7-25. Army corps, divisions, and brigades supporting or reporting to JFCs must understand the joint planning process and contribute to it even as they conduct parallel planning using Army processes with their subordinate echelons. This directly contributes to the successful execution of operations across an extended battlefield, where long distances and sporadic network connectivity affect the situational awareness and synchronization of forces. (See JP 5-0 for additional information on planning and execution of the joint planning process.)
7-26. Planning for operations in maritime environments requires collaboration between Army forces and other relevant components of the joint force command and integration across warfighting and joint functions at each echelon. Ideally, planning should be conducted by commanders and their staffs in the same location, which in some cases may be aboard a ship or in the air. When this is not practical, the exchange of liaison officers facilitates planning functions. Planning efforts—particularly in crisis situations—are conducted in parallel and collaboratively across the involved echelons and Services. This is crucial for any assault operation conducted across extended maritime distances. Integrated planning is facilitated by using operational planning teams formed around planners from functional areas that include subordinate and supporting command liaison officers. Aligning Army warfighting function cells with the joint functions enables integrated planning.
APPLYING THE OPERATIONAL FRAMEWORK
7-27. Applying the operational framework in maritime environments requires commanders and staffs to consider the impacts of maritime surface areas and integration with maritime forces. It also requires a different appreciation about what constitutes deep, close, and rear operations in relation to each other. The physical separation of forces by bodies of water affects considerations of mutual support since many operations are likely to involve noncontiguous AOs. Army echelons may have responsibilities for information collection of maritime surface areas and for providing fires into maritime and littoral regions in support of other Services. Army forces may be required to defend against enemy amphibious assaults, requiring tactical level coordination with Navy and Marine Corps forces. Army forces may also conduct amphibious landings or airborne and air assault operations over water in support of joint operations. Operations that were previously considered close, such as forcible entry, can extend into a deep area based on distance between islands or sea bases. Tactical support areas may be separated by extended distances and require the use of watercraft or other joint capabilities to support tactical level sustainment or tactical maneuver forces to secure sea lines of communications.
ASSIGNING A JOINT OPERATIONS AREA WITHIN AN AREA OF RESPONSIBILITY
7-28. The Unified Command Plan designates the AOR. Within that AOR, a larger maritime environment might have several joint operations areas to facilitate C2 and resource prioritization. For example, United States Indo-Pacific Command may designate a JOA for operations in the South China Sea and a JOA for operations in Korea. Both JOAs require unique C2, movement and maneuver, sustainment, intelligence, fires, and protection planning and resources. This also includes the designation of an appropriate land component headquarters and staff to facilitate joint integration specific to that JOA and the particular Army operations within it. A JOA is established for operations within an AOR that is specialized or limited in its scope or duration, and a JFC directs military operations as a joint task force (JTF).
DESIGNATING A JOINT SECURITY AREA
7-29. Within the JOA, the JFC designates numerous joint security areas (JSAs). In a maritime environment, JSAs can be separated by considerable distances, and they probably will not be with areas that are actively engaged in combat. A theater army headquarters or theater sustainment command (TSC) may be required to conduct theater sustainment operations from a single designated JSA or from multiple locations, depending on mission requirements. Army forces may also be designated to secure the JSA and critical intermediate staging bases. (See JP 3-10 for additional information on planning and execution of operations in the JSA.)
ASSIGNING AN AREA OF OPERATIONS
7-30. An AO is the operational area defined by a commander for land and maritime forces. The JFC assigns land areas of operations. The designation of subordinate AOs in a maritime environment enables freedom of action, maintains tempo, and maximizes available combat power. Larger island land masses may allow Army forces to operate with a contiguous AO, with the unit boundaries directly adjacent to each other. Smaller archipelagic island chains may require a noncontiguous AO and may even leave some islands within a designated AO completely unoccupied by friendly forces depending on the operational requirements and threat. Figure 7-2 illustrates a notional corps area of operations with significant maritime aspects.

Deep Operations in Maritime Environments
7-31. Deep operations in a maritime environment may focus on defeating enemy antiaccess (A2) and AD capabilities to set conditions for joint offensive operations using information collection, special operations forces, and fires. They may also focus on reconnaissance and security activities in support of joint defensive operations using the same capabilities. In either situation, Army intelligence capabilities support operations in the extended deep area, enabling the JFC to understand and visualize the operational environment before shaping with fires or maneuver forces in subsequent operations. Army fires assets may also be designated in a support role to other component commands, providing suppression of enemy air defense for aerial attack of island-based enemy forces or surface fires to defeat enemy naval forces. Joint forcible entry operations, to include the amphibious landing of Army forces, may seize key terrain to begin or exploit the disintegration of an enemy A2 or AD approach in a specific joint operations area (JOA).
Close Operations in Maritime Environments
7-32. Close operations in a maritime environment may appear much the same as a traditional land-based approach discussed in Chapter 6. Seizing key terrain requires Army forces to conduct offensive operations, which can include airborne, air assault, and amphibious assaults. Close operations also include defense of islands and island-based nodes that facilitate joint operations, such as airfields and ports. Given the isolated nature of some forward-deployed Army forces critical to the success of joint operations, those forces may be required to conduct defensive operations for extended periods until additional forces arrive. Sustainment planning should assume isolation for periods of several weeks or more.
Rear Operations in Maritime Environments
7-33. Rear operations in a maritime environment include those necessary to set and sustain the theater and facilitate combat operations for the joint force. These operations include conducting protected reception, staging, onward movement, and integration (RSOI) and conducting theater sustainment. RSOI could occur thousands of miles away from where a unit would be employed in combat. These operations require increased joint integration during the planning process to ensure prioritization of critical joint resources and to mitigate risk to vulnerable and extended air and sea lines of communications.
7-34. Sustainment and protection operations are associated with support areas, enabling the building and preservation of combat power. While forces positioned on land masses have their own support areas, large expanses of water may require waterborne or airborne transportation for the staging and movement of personnel and equipment between various echeloned support areas. Support areas may be sea based or land based on islands, connected by sea or air lines of communications. These strategic and tactical support areas are critical assets that can be vulnerable to enemy attack, and they typically require increased security considerations, such as anti-submarine and theater AMD.
SECTION III – OPERATIONAL CONSIDERATIONS FOR A MARITIME ENVIRONMENT
7-35. In a predominantly maritime JOA, naval and air components are typically the key components of the JFC’s operational approach. Army forces develop a nested operational approach that reflects and supports the JFC plan. This section details what Army forces consider to successfully nest their operational approach with the joint force. (See ATP 5-0.1 for a more detailed discussion on the Army’s recommendations for developing operational approaches. See JP 5-0 for a more detailed discussion of the joint operations planning processes.)
ESTABLISH COMMAND AND CONTROL
7-36. Given the size of an AOR for most maritime environments and the distance between land areas, there may be multiple active JOAs, each with separate headquarters. Maritime environments impose significant challenges for theater army signal and sustainment architecture. Subordinate ARFORs rely on maritime and space capabilities to overcome these challenges.
DEFEND AND CONTROL KEY TERRAIN
7-37. Friendly forces are stationed or positioned in dispersed forward positions in maritime theaters, and often have been there for decades to facilitate joint operations throughout a maritime theater. Their locations are typically key or even decisive terrain, which requires that Army forces must also be able to defend and control that terrain. Their ability to do so is a function of survivability that depends on active and passive defense measures, reinforcement with critical weapons systems, hardening and camouflaging of command posts, securing critical C2 networks, sustainment, and the employment of protection-oriented land forces. Providing active and passive AMD, to include early warning, reduces the effectiveness of enemy long-range fires or attack. Forward-positioned forces must be prepared to fight outnumbered and from exposed terrain, specifically islands, for as long as is required. This increases the need for security throughout the AOR and forward-positioned sustainment capabilities. Army forces enhance the protection of their own less mobile assets by continually improving the survivability of their positions.
7-38. Retaining critical island terrain through an effective defense, one that includes counterreconnaissance and security operations, is vital for the success of the JFC’s objectives to deny enemy forces a relative advantage. Retaining key land masses enables joint freedom of action for operations in the air and maritime domains, since land-based capabilities can maintain a persistent physical presence that lessens requirements on air and naval forces to secure avenues of approach. Defeating enemy C2 systems is key to defeating layered standoff, A2 weapons, early warning, and enemy reconnaissance and surveillance capabilities. The ability to maintain key terrain for access and security enables the JFC to employ key long-range fires and protection capabilities. This enables regional access during armed conflict critical for maritime freedom of navigation and air superiority. Denying enemy access to limited terrain, sea channels, airspace, and cyberspace by occupying key terrain is crucial to creating an advantage. As there is no easy exfiltration from an exposed island base or maneuver to positions outside of enemy fires ranges, the physical reinforcement of bases may be critical to the success of Army forces in enabling joint force success.
PROTECTION SUPPORT TO THE DEFENSE
7-39. The ability to protect and augment the security of the other Services is critical in maritime theaters because of the relative isolation of the forces they position forward and the exposure of those forces to threat capabilities that could be employed with few indications or warnings. The following tasks directly support theater setting and are critical to the success of joint maritime operations:
AMD, to include counter-unmanned aircraft systems (UASs).
Littoral defense.
Area security (base and base cluster defense).
Chemical, biological, radiological, and nuclear (CBRN) defense.
Explosive ordnance disposal support.
General, combat, and geospatial engineering support.
7-40. Ground-based theater-level AMD assets are typically operational control (OPCON) to the Army air and missile defense command (AAMDC) for the JOA. The AAMDC is assigned to the theater army and generally placed in support of the area air defense commander. Army short-range air defense (SHORAD) units are assigned or attached to theater, corps, or division commands, and are OPCON to air defense artillery (ADA) commanders at these echelons. Army forces provide security for designated high priority assets, including layering SHORAD assets into the security plan as part of a defended asset list. The JFC normally delegates authority to the joint force air component commander, as the area air defense commander, for engagements of air and missile threats. When the JFC organizes the joint force, in addition to a joint force air component commander, the JFC also normally designates an area air defense commander for defensive counterair and an airspace control authority for joint airspace control. Normally, the JFC designates the air component commander as the area air defense commander and airspace control authority, because the three functions are so integral to one another. Coordination and integration with the surface combatants of the joint maritime component commander performing AMD roles for critical joint bases is also required. With the support of the component commanders, the area air defense commander develops, integrates, and distributes a JFC-approved joint area air defense plan. (See to FM 3-01 or ATP 3-01.15 for detailed information about the planning and integration of AMD.)
7-41. Theater and tactical ADA units provide early warning by employing sensors to detect air and missile threats and disseminating air defense warnings to U.S. forces, allied or partnered forces, and civilian populations. C2 elements disseminate air defense early warnings through various communication networks and nodes, to include submitting an incoming threat or an all-clear message to the network. (See FM 3-01 for more detailed information on early warning tasks associated with AMD operations.)
7-42. Army forces in maritime environments should assume their land operations are being observed by the enemy and not assume that AMD protection extends to their AO, especially when separated by extended distances and vast bodies of water. Larger air threats entering friendly space can be detected early, and identified, processed, and defeated as part of the air component’s roles and responsibilities to the JFC. There remains a requirement to find (including detect, identify, and be prepared to defeat) UASs, which could be launched from naval or commercial vessels or other land masses. Sensors, which include long-range and short-range radars, optical devices, wireless, and audible alert systems face challenges detecting smaller tactical UASs at sufficient ranges to mitigate effects. (See ATP 3-01.81 for more information regarding counter-UAS planning and execution.)
7-43. The JFC normally designate JSAs and designates forces to provide the security of base, base clusters, and lines of communications. Various types of security forces can secure the JSA and lines of communications, including dedicated Army forces, coalition partners, and host-nation forces. Bases and base clusters can be noncontiguous with each other even on relatively small islands, and they may be separated by extended distances and vast bodies of water.
7-44. Army commanders can be assigned roles as an area commander, base cluster commander, or base commander, all of which facilitate base defense in support of land and other Service forces. Base threats may include special operations forces, naval gunfire, long-range surface-to-surface fires, and manned and unmanned aircraft. Security forces should be able to coordinate for indirect and joint fire support, have a high degree of tactical mobility, and a reasonable span of C2. (See JP 3-10 for more information on the joint requirements for base defense and securing lines of communication. See ATP 3-37.10 for more information on the techniques of establishing and securing bases.)
7-45. Threat employment of CBRN weapons can deny access to key terrain containing ports, airfields, or staging areas for either friendly or enemy forces until decontamination is complete or until the land component commander assumes the risk of operating in a contaminated environment. Army forces should understand the threat’s intent, weapons capabilities, and weapons effects. The threat may range from artillery or rockets to theater ballistic missiles. Delivery tactics could include overt or covert means (for example, special operations forces), state-sponsored terrorism, or other asymmetric methods. Contamination mitigation minimizes the time required to return personnel and mission-essential equipment to a mission-capable state as part of an overall contamination mitigation plan for the JOA. (See ATP 3-11.32 for more detailed information about CBRN and contamination mitigation techniques during security operations.)
7-46. Explosive ordnance disposal (EOD) units detect, identify, conduct onsite evaluations, render safe, and conduct exploitation, disposal, or other disposition of explosive ordnance, including weapons of mass destruction. They advise commanders on improvised explosive devices and other explosive hazard threats, including the most effective way to defeat the devices. They also directly support requirements to render safe explosive hazards that put the use of ports, airfields, and other critical infrastructure at risk. EOD units can support remediation of areas that ensure access to clear aerial ports of debarkation and seaports of debarkation facilities and other facilities that support seaports. (See JP 3-42 for a more detailed discussion on the joint integration and Army roles for ordnance. See ATP 4-32 for detailed information on the techniques of EOD.)
7-47. Islands identified as key terrain for operations typically require additional engineer support to harden existing key infrastructure or construct new infrastructure to meet the JFC’s requirements for airfields, ports, and survivability positions. Construction equipment, personnel, and supplies often require specific transportation coordination and prioritization as critical assets for movement by air or sea. Remote locations that do not have immediate access to organic engineer support require either locally procured or contracted construction capabilities or manually constructed survivability positions that are concealed as best as possible from enemy observation as part of survivability measures. (See FM 3-34 for fundamentals and planning considerations on the employment of general and combat engineer capabilities. See ATP 3-37.34 for specific techniques and considerations on protective positions, camouflage, and enhancing survivability.)
SECURITY OPERATIONS IN MARITIME ENVIRONMENTS
7-48. The JFC designates the area commander for base and lines of communication security, and most of the security tasks are typically the responsibility of land force commanders. Collaborative planning and integration between ground forces providing base security and naval and air forces providing sea lines of communications security is crucial to maintaining freedom of navigation for combat operations. Army forces provide security support to all bases within their designated JOA. Brigade combat teams (BCTs), military police brigades, and maneuver enhancement brigades are suitable for this function. This responsibility can include bases commanded by organizations that are not part of the area commander’s forces, such as multinational allies or other joint services. The JFC may institute standard force protection policies for all commands and bases within an AOR to ensure unity of effort.
7-49. A joint force land component commander (JFLCC) may be designated as the joint security coordinator by the JFC, with other unified action partner forces assigned to support security plans for the JOA. The joint security coordinator coordinates the overall protection of the joint security area in accordance with JFC directives and priorities. This ensures the requirements and priorities are coordinated with the area air defense commander. The joint security coordinator typically establishes a joint security coordination center. The staff of this center may be part of the JFLCC headquarters, or this function may be delegated to a subordinate unit, and it normally includes representatives from all components operating in the JSA to assist in meeting joint security requirements.
7-50. Every island with a base, regardless of size, requires the same level of comprehensive planning to ensure sufficient protection in the event there are no reinforcements immediately available when conflict commences. Army forces should anticipate direct enemy attacks by small units or special operations ground forces, attack aircraft, and indirect fires. Commanders must ensure that base defense measures are adequate to detect and defeat small-unit operations (including Level I or Level II threats) well before crisis or conflict. Dispersion mitigates effects of long-range fires and attack aircraft, but dispersion on small islands is not always possible. Construction, reinforcement, and caching supplies may be the primary option to offset this vulnerability, but they are necessary everywhere within range of threat capabilities.
7-51. Successful security of key terrain and infrastructure depends on an integrated and aggressive plan consisting of dedicated security forces and responsive sustainment and protection forces (including medical, ADA, and engineer). The theater army synchronizes the base security plans, integrates them into the overall JFC’s intent, and allocates additional forces for securing sustainment nodes and command posts, key terrain, or critical infrastructure necessary for combat operations. Remote island bases have the same security planning considerations, but they vary in their tactical application based on the environment. These considerations include, but are not limited to—
Defense against sea-based attacks, such as enemy special operations forces or naval fires.
The integration and application of coastal-based indirect fire systems and fire support planning.
Integrated planning for aviation support, including movement and protection of forward arming and refueling points.
Coastal and harbor security support and integration of host-nation or local security forces.
Integration of coastal barrier systems, sea-based obstacles, and sea-based or harbor mines.
(See JP 3-10 for more information on joint security coordination command posts. See ADP 3-37 for more information regarding the fundamentals of protection and protection planning.)
DEFEAT COMPONENTS OF ENEMY ANTIACCESS AND AREA DENIAL AND ENABLE JOINT OFFENSIVE OPERATIONS
7-52. Army forces support joint defeat of enemy integrated air defense, fires and strike complexes, surveillance, and reconnaissance, and integrated C2 networks to enable success during joint operations. AMD and fire support are two of the Army’s critical contributions to these efforts, enabling ground, naval, and air forces to maintain access to the various regions of an operational environment.
PROVIDE THEATER AIR AND MISSILE DEFENSE
7-53. Friendly ADA forces may protect maritime access points, such as shipping channels or ports, to enable the flow of combat power and theater sustainment. Considerations for employing ADA capabilities during AMD operations in a maritime environment are—
Defeat enemy air and missile threats encountered in strategic and tactical operations, including medium-range, short-range, and close-range ballistic missiles; cruise missiles; UASs; rockets, artillery, and mortars; tactical air-to-surface missiles; and fixed-wing and rotary-wing aircraft.
Integrate and maintain tactical data linkages to other Service and multinational forces conducting AMD operations in the JOA, weapons systems, sensors, effectors, and C2 nodes at each echelon.
Provide early warning for air and missile attacks and disseminate attack warnings.
Provide extended-range surveillance of the airspace and detect, acquire, track, classify, discriminate, and identify aerial objects from near-ground level to high altitudes in difficult terrain and in adverse weather conditions.
Contribute to airspace management and control functions by identifying, coordinating, integrating, and deconflicting Army assets in the JOA airspace.
7-54. The number and dispersion of critical assets across numerous islands may exceed the ability of available ADA forces to defend against the air and missile threats. The employment of passive AMD measures by tactical formations is critical to their survivability, particularly on remote islands that may not have access to sufficient active ADA capabilities or reinforcement from a neighboring island chain. Access to early warning networks with over-the-horizon and redundant communications increases reaction time and further mitigates risks for remote locations primarily using passive defense measures. (See FM 3-01 for more detailed information on planning considerations associated with AMD operations.)
FORCIBLE ENTRY OPERATIONS
7-55. In a maritime environment, Army forces are likely to conduct two complex forms of forcible entry operations: airborne or air assault and amphibious landing. Forcible entry operations seize and hold lodgments against armed opposition to set conditions for follow on operations. To set favorable conditions for success during forcible entry, commanders and staffs must—
Visualize the entry location and understand the impact of other domains on forcible entry operations.
Control air and maritime areas to protect the force and preserve lines of communications leading up to and during the entry.
Disrupt enemy influence during entry.
Isolate the lodgment from reinforcement by enemy forces.
Maintain access to the lodgment throughout the duration of operations to build and sustain combat power.
Manage the lodgment to integrate other supporting operations.
Seize and maintain the initiative to achieve surprise throughout the entry operations.
7-56. The JFC decides whether to conduct the forcible entry as a concurrent or integrated operation. Concurrent forcible entry operations occur when a combination of amphibious assault, airborne, air, or ground assault forcible entry operations are conducted simultaneously, but as distinct operations with separate AOs and objectives. Integrated forcible entry operations occur when amphibious assault, airborne assault, air assault, and ground forcible entries are conducted simultaneously within the same AO against mutually supporting objectives. Large island land masses would likely involve integrated forcible entry involving U.S. Marines and potentially allied or partner forces. Smaller archipelagic island chains could require concurrent forcible entries that enable security operations or subsequent main and supporting efforts against larger objectives.
7-57. Forcible entry operations by ground, sea, or air all use the same phasing model to facilitate coordination and synchronization. These phases are preparation and deployment, assault, stabilization of the lodgment, introduction of follow-on forces, and termination or transition operations. Planning for forcible entry also includes planning for—
Movement planning over extended lines of communications over water.
Information collection against an enemy with layered and integrated early warning.
Management of transitions when lines of communications and networks are extended over water.
Insertion of special operations forces.
Ensuring air superiority over the joint landing area.
Coordination for initial and reinforcing entry forces for the initial assault and main assault.
Establishment and operation of any potential intermediate staging bases.
Lodgment security, organization, and expansion from shore to an island interior.
(See JP 3-18 for more detailed discussion and information about Army forces roles, responsibilities, and planning considerations for joint forcible entry operations.)
AMPHIBIOUS OPERATIONS
7-58. Planning for an amphibious operation is continuous, and it requires collaborative, parallel, and detailed planning by all participating forces. The organization of any amphibious operation should be sufficiently flexible to meet the planned objectives in each phase of the operation and account for unforeseen developments. Sound planning provides for unity of effort through unity of command, centralized planning and direction, and decentralized execution. JFCs may decide to establish a functional component command to integrate planning and reduce JFC span of control. This improves the efficiency of information flow, weapons systems management, component interaction, unity of effort, or control over the scheme of maneuver. Regardless of approach, the JFC designates command relationships for the commanders of the amphibious task force and landing forces. The designation of the supported and supporting role of the amphibious force commanders is important, as it establishes main and supporting efforts and prioritizes resources.
7-59. Opposed landings in a maritime environment are one of the most difficult and dangerous military operations, so achieving the element of surprise should be pursued by all available means. Overt activities that threaten the element of surprise should be kept to a minimum and conducted as close as practical to the arrival of joint fire support assets in the JOA. Deception operations may facilitate surprise if they portray a course of action the enemy expects or a timeline for execution different than planned. Deception operations are a necessity during assault breaching of a defended beachhead. Large lane sizes demand large numbers of weapons and multiple aircraft passes to clear zones prior to the assault. This may draw immediate attention to the landing force unless alternate lanes are brought under fire as well
7-60. The landing force typically consists of maneuver, protection, and tactical echelon sustainment forces. The JFC designates the landing forces commander. If Army forces are part of the landing force, they must be task-organized with appropriate combat and sustainment capabilities to support the landing force. Army forces also provide intra-theater ship-to-shore transport, including landing craft, cargo handling, logistics, traffic control, and engineering capabilities.
Note. If the JFC organizes planning along functional lines, functional component commanders normally exercise OPCON over their parent Services’ forces and tactical control (TACON) over other Services’ forces attached or made available for tasking.
7-61. Setting conditions prior to the execution of any amphibious operation is critical. Enabling operations that set conditions include supporting and pre-landing operations. These require detailed integration at all echelons and highly synchronized employment of Army and joint capabilities that can reinforce success and ensure landing force survivability under conditions where reinforcement or support may not be readily available. Planning for forcible entry also includes planning for—
Force concealment as part of a larger joint military deception operation.
Maritime clearance of mines in the vicinity of transportation lanes, landing beaches, and shorebased sustainment nodes.
Maritime and hydrographic reconnaissance for landing beaches and sea approach lanes.
Accurate prediction of weather and tidal conditions.
Seabasing of supporting aviation resources, such as aeromedical evacuation or attack aviation.
Assault breaching and beach clearance of anti-landing obstacles, which may include mines.
Status of civil and local national inhabited areas, to both conceal landing forces and prevent civilian casualties.
7-62. Pre-landing operations take place between the commencement of the action phase (arrival of the amphibious force into the operational area) and the ship-to-shore movement. There is rarely a clear transition between support and pre-landing operations, and this must be planned for and clearly communicated across echelons prior to execution. Some planning considerations during this phase include—
Obstacle clearance (including perimeter and main barrier minefields and the engineer and beach barriers that canalize landing forces) and marking usable sea and shore channels for follow-on forces.
Integration of naval fire support.
Integration of air support, including electromagnetic warfare and airspace between the landing force and amphibious task force.
Clearance of fires on landing areas.
Ammunition and fuel expenditure prior to landing.
Loss and recovery of equipment prior to landing.
Loss of personnel and recovery of casualties prior to landing.
Resupply and rearming schedule for amphibious and landing forces.
Landing force requirements to support other forces prior to and after the landing assault.
Organization and location of reserve in a similar manner as the assault force.
7-63. During an amphibious operation, a subsidiary landing outside the designated landing area is normally conducted by elements of the amphibious task force to support the main landing. Subsidiary landings should be planned and executed by commanders with the same precision as the main landing. Amphibious re-embarkation for follow-on operations may require additional support from specialized units or other Service forces and additional logistics support to replace lost or damaged equipment and depleted supplies. For tactical echelons, combat rubber raiding craft can provide flexibility to amphibious operations, including movement to reconnaissance objectives and subsidiary landings sites, movement of forces inland from a coast along waterways, or recovery of casualties to support vessels. Additionally, Army planning must account for casualties and the continued medical treatment of patients, potential for CBRN decontamination, requirement to transport remains or provide mortuary services, transportation and transfer of enemy detainees, and logistics to support basic sustenance ashore. (See JP 3-02 for more information about the fundamentals of planning and executing joint amphibious operations. See MCTP 13-10M for more detailed information and considerations on amphibious embarkation. See ATP 3-17.2 for tactical considerations on movement from ship to shore and the C2 of shore and beach parties.)
SUSTAIN LARGE-SCALE COMBAT OPERATIONS IN MARITIME ENVIRONMENTS
7-64. Setting and sustaining a maritime theater includes RSOI of personnel and equipment and the protection of forward-positioned forces critical to the security of key strategic assets, such as theater AMD, airfields, ports, and sea lanes. Army watercraft are essential to sustainment in maritime environments as they are designed to perform missions specifically related to intratheater movement of combat power and sustainment. While capable of deploying over strategic distances, Army watercraft are not strategic lift platforms, but they are a critical link between strategic lift and land-oriented tactical movements. Army and Navy engineering assets are critical to the establishment and maintenance of port facilities.
ESTABLISH PROTECTED RECEPTION, STAGING, ONWARD MOVEMENT, AND INTEGRATION
7-65. During armed conflict in a maritime operational environment, theater opening and RSOI vary to meet mission requirements of the JFC. The theater engineer command is responsible for developing and maintaining the necessary infrastructure (including ports and roadways) that support RSOI and follow-on operations. Multiple islands requiring multiple ports will increase the demand for specialized engineer and sustainment formations to construct, develop, maintain, and operate them.
7-66. Rather than gaining efficiencies from a consolidated location, the theater army may be required to support multiple JSAs and RSOI sites. Using multiple RSOI locations increases the overall signal, sustainment, protection, and maneuver requirements for the theater. An often-overlooked component of RSOI is the mandatory combat training that needs to be conducted. TSC personnel do not conduct this training; a maneuver force must provide the personnel. More RSOI locations require more trainers.
7-67. Multiple JSAs and JOAs will likely require the theater army to request additional signal assets to support the theater signal brigade as they develop the necessary C2 architecture to support operations. Both the strategic signal brigade and the tactical signal brigade will require significant augmentation to support the theater and JOA communications network. Army forces maintain coastal, harbor, and inland waterway defense while accounting for extended deployment times. Critical protection, firepower, and mobility assets may also be disbursed across numerous islands in the AOR and in the JOA, requiring detailed coordination and reconfiguration of loads prior to embarkation.
Note. Given the varying nature of islands and maritime environments where Army forces may operate, there are many scenarios where RSOI take place outside the JOA, and onward movement for Army forces may occur just prior to the execution of a forcible entry operation to an island. This may also change from island to island, depending on the enemy situation.
7-68. In a maritime environment, reception, staging, and integration activities may need to occur prior to onward movement into a JOA. The process of securing and uploading unit basic loads, addressing life support for personnel, or reconfiguring underway must occur prior to debarking directly into combat. Units that require extensive support for staging, including maintenance or cross-loading of supplies critical to survivability (Class IV and Class V items), may require an intermediate staging base outside the JOA before continuing on to their debarkation point. Additionally, units may execute onward movement out of sequence from reception, staging, and integration. Units may need to conduct integration during embarkation or during a reconfiguration at an intermediate base outside the JOA.
7-69. RSOI may occur from sea bases. Seabasing is the deployment, assembly, command, projection, sustainment, reconstitution, and reemployment of joint power from the sea without reliance on land bases within the operational area (JP 3-02). Seabasing provides Army forces with the ability to conduct certain functions and tasks at sea without dependence on infrastructure ashore, and it minimizes the need for stockpiles ashore while positioning joint forces for immediate employment. Seabasing requires detailed collaborative planning between joint forces, but it can provide a secure base of operations with C2 capability, and it minimizes the requirements ashore for an initial port and airfield to support missions. (See JP 3-02 for more information on considerations for planning and executing staging operations from sea bases.)
CONDUCT THEATER SUSTAINMENT OPERATIONS
7-70. Theater sustainment in a maritime environment is a highly collaborative process. When directed to provide management of common sustainment functions that include other Services, the TSC leads the joint sustainment planning board. Army forces provide theater and port opening functions for joint forces to maintain strategic and operational reach. Theater sustainment plans must account for—
Maritime movement of Army pre-positioned stocks (APS).
Joint logistics over-the-shore (JLOTS).
Intertheater transportation by joint assets.
Intratheater transportation for personnel during and after RSOI.
Classes of supply and access to field services.
Field and sustainment maintenance in remote locations.
Distribution.
Operational contract support.
General engineering (ports and airfields).
Sustaining and mitigating impact of limited island infrastructure.
Mortuary affairs.
7-71. Bringing APS ashore requires detailed planning as part of the movement control and sustainment planning boards at the TSC and Army field support battalions. APS are positioned strategically, and they are not designated to any specific unit. Floating stocks may be discharged in support of armed conflict and require detailed early planning. In a maritime environment, the sustainment demands and maintenance footprint for an APS download operation may quickly exceed the capabilities of a small island port. The APS download has significant considerations for suitable, deep draft port facilities and infrastructure, support equipment, host-nation and coalition approval for port access, maintenance personal, and detailed force protection and security plans. The demand for maintenance and support personnel and security forces is significant, and it requires additional sustainment planning. APS download operations typically require a TSC or division-level C2 node and additional protection assets to mitigate their vulnerability to enemy attacks. (See ATP 3-35.1 for more information on planning for APS stocks in combat operations.)
7-72. JLOTS is a key enabler to combat operations in maritime environments. It is typically coordinated and controlled by the TSC. JLOTS allows heavy forces to be moved from ship to shore when there are no modern deep-water ports available, such as on various smaller atolls or when ports are not available due to combat damage or volume of shipping. The strategic flexibility provided by JLOTS requires detailed coordination and frequent training as a Navy and Army warfighting skill set before conflict occurs. This family of systems includes vulnerable assets that facilitate the ship-to-shore movement of necessary supplies and the administration of personnel supporting JLOTS. The offshore petroleum distribution system, elevated causeway system, pier systems, roll on/roll off discharge facilities, and the administration architecture associated with JLOTS employment are highly vulnerable, lack protection or early warning systems, and are unable to quickly displace in the event of enemy attack. If a JFC is considering using a JLOTS, the command should take measures to reduce its vulnerability. (See JP 4-01.6 for more detailed information about JLOTS.)
7-73. Because of the constraints imposed on ground movement in maritime operational environments, it is critical that the TSC integrates into the JFC’s transportation board and working groups to prioritize and execute transportation operations during armed conflict. This board and working group direct the planning and coordination of modal operations, intermodal operations, movement control, and theater distribution. Surface transportation normally requires a pre-planned transition from watercraft to motor transport at the shoreline for the movement of supplies and personnel in-shore. Naval forces provide essential causeway, sealift, and logistics over-the-shore support to land forces when ports may be austere, damaged, or nonexistent. Naval forces may be responsible for downloading supplies from vessels and delivering them to port operations for release to Army forces. Commanders may task Army forces to assist with downloading and uploading equipment and supplies from ships and boats. Naval construction capabilities provide port construction such as warehouses, storage facilities and explosive ordnance disposal to locate and dispose of mines along ports and channels.
7-74. Army watercraft provide additional sealift and sustainment capabilities to the JFC and JFLCC as part of inter-island transportation support. Given the limited availability of these critical assets, most of which are highly vulnerable to attack from enemy antiship systems, some Army equipment and forces may be prioritized lower than other Service equipment and forces for transportation into and around the AOR. Army watercraft operations depend on host-nation access and infrastructure improvement to enable both maneuver forces and follow-on sustainment. Army units assigned to maritime environments with organic tactical combat rubber raiding craft can also provide a tactical means of intra-island and possibly inter-island resupply. This can reduce the burden for operational assets, providing increased access to restrictive littoral terrain, a reduced signature for targeting, and flexibility to operational and tactical commanders. (See FM 4-01 for more information about Army transportation planning, command relationships, and overall capabilities to the joint force. See ATP 4-15 for more a more detailed discussion about the techniques of planning for and employing Army watercraft.)
7-75. Commercial shipping organizations may provide movement assets, but they require increased planning and support due to a lack of organic protection systems. The theater army’s contribution to transportation during combat operations in a maritime environment may be to protect lighterage operations. Lighterage is the process in which small craft are used to transport cargo or personnel from ship-to-shore using amphibians, landing craft, discharge lighters, causeways, and barges (JP 4-01.6). It can also transfer equipment and personnel between ships or for intratheater transport. Lighterage includes landing craft and modular causeway systems, such as ferries. To facilitate port operations at joint intermediate staging bases, Army forces provide and operate float utility watercraft, such as harbor and ocean-going tugs, pusher tugs, floating cranes, barges, floating causeways, and roll-on/roll-off discharge facilities. Once sustainment assets are positioned to support specific tactical operations, it is difficult and time consuming to reposition them when priorities shift.
7-76. For inter-theater and intra-theater air transportation operations by fixed-wing assets, the TSC is responsible for consolidating, prioritizing, and processing aerial resupply requests. A division or corps aviation officer determines consolidation and synchronization of rotary-wing movement based on the commander’s priorities. Intra-theater rotary-wing movement in a JOA requires aircrews trained and equipped for deck landing and overwater flight operations.
7-77. Army forces provide operational medical support to the joint force. Although military medical forces are afforded protection under the law of armed conflict from being directly targeted, the geographic constraints associated with providing medical support to forces on islands, in likely proximity to combatant forces or key terrain, coupled with the effects of long-range fires, increases risks to medical forces and facilities. Hardening of medical care facilities in exposed locations, like on small or remote islands, is crucial to maintaining hospital survival. Additionally, threats from nonstate actors upon medical facilities and capabilities may require increased protection measures. Units may need to rely on ship-based medical facilities during initial operations, which requires joint planning and coordination. Higher-level care facilities also place an increased demand on certain classes of supply, which may be difficult to transport, have special storage requirements (for example, refrigeration), and be difficult to off-load in remote island locations. (See FM 4-0 for more information on the Army’s operational medical support to the joint force.)
7-78. The lethality of large-scale combat operations can devastate both the social fabric and the economic viability of small islands where construction assets may be limited even before conflict occurs. Early establishment of base security and maintaining viable governance may largely depend on the repair of critical port and airfield infrastructure. A JTF commander may use either operational contract support or request military engineers to repair facilities during combat operations (or improve their survivability prior to combat operations).
7-79. In the Arctic, base infrastructure materials across the region need to have high thermal efficiency, long-term durability, tolerance to repeated freeze and thaw cycles, and resistance to permafrost degradation. Infrastructure in many austere locations has already deteriorated due to extreme environmental factors. It can also complicate force sustainment operations as roadways, seaports, and airfields are potentially rendered inoperable by ice, snow, seasonal thaws, and freeze cycles. Class IV construction material resupply for arctic use may have long lead times. Therefore, infrastructure to be used by military units deployed to arctic areas should be inspected as soon as possible to identify deterioration and inadequate systems.
Chapter 8 - Leadership During Operations
This chapter describes basic doctrine for combat leadership. It begins with a discussion of the art of command, and it describes the impact of a commander’s competence, presence, decision making during operations, and risk acceptance. It then describes the role of commanders in driving the operations process. The chapter concludes with a discussion on how leaders adapt their formations for missions while developing junior leaders and teams.
THE ART OF COMMAND AND THE COMMANDER
8-1. The commander’s chief responsibilities during operations are to develop effective tactics and to lead and direct the unit in executing them. Soldiers want and willingly follow leaders who win. The most important quality for commanders or other leaders, however, is competence. Good leaders understand tactics, the abilities of their own and enemy units, what is possible in any situation. Combined arms competence is the combat commander’s greatest contribution to winning. Effective commanders lead and inspire their subordinates to fight and win based upon that competence, while ensuring unity of purpose and unity of effort. They do this through a combination of processes, the staffs and subordinate leaders they empower, and their personal example and influence. While the commander is the primary leader of a formation, all leaders play an important role in carrying out their higher echelon commander’s intent as they provide command and control (C2) to their own subordinates during operations.
8-2. Commanders and their subordinate leaders determine success or failure through the decisions they make, the examples they set, the actions they inspire, and their will to win. The commander is the focal point for the employment of staff processes that inform the judgment critical for rapid, effective decision making. Commanders must possess the confidence and skill to rapidly make difficult decisions, accepting risk to create and exploit fleeting opportunities. They conceive and implement sound operational and tactical solutions with the speed and force necessary to win. They also seek staff officers and subordinates who are proficient at their specialties and use them to make the unit tactically effective.
8-3. Commanders have a moral responsibility to ensure their units are prepared for combat. They prepare them through realistic training that reinforces individual and small-unit task and battle drill proficiency, collective proficiency in the execution of mission essential tasks under the most demanding conditions, and the development of staffs able to integrate the warfighting functions and joint capabilities in combined arms approaches against enemy forces. Commanders resource training and protect subordinates’ training time. They establish the command climate within their unit, direct staff and subordinates during operations, and continually assess all aspects of their performance. They build trust, develop their subordinates’ competence and confidence, encourage subordinate commanders to think critically, and demand that they demonstrate initiative within the commander’s intent. Lastly, they prepare subordinates to assume responsibility one and two echelons above their current assignment so that they can effectively assume control of the larger formation when required to because of casualties or lost communications.
8-4. Commanders make decisions informed by judgment grounded in their experience, expertise, intuition, and self-awareness. Judgment is the single most important leadership attribute applicable to selecting the critical time and place to act, assigning missions, prioritizing, managing risk, and allocating resources. Thorough knowledge of military science, a strong ethical sense, and an understanding of enemy and friendly capabilities across domains form the basis of the judgment required of commanders. Judgment becomes more refined as commanders become more experienced, and good judgment becomes even more essential in ambiguous or uncertain operational environments. Self-awareness and experience help commanders become more expert about assessing situations and receiving assistance from their staffs. Self-awareness is required to assess one’s self and to earn the trust of those one commands. Judgment allows commanders to distinguish between risk acceptance essential to successful operations and potentially disastrous rashness. The commander’s judgment and experience help shape information requirements and staff priorities during operations. Subordinate commanders and staffs collaborate to provide the most relevant information in the most effective format for the commander to make sound decisions.
APPLYING THE ART OF COMMAND
8-5. Command is more art than science because it requires commanders exercise their judgment, leverage their experience, and use their intuition when leading their units. Commanders apply the art of command by providing leadership, delegating authority, allocating resources, and making decisions. Subordinates operating within the commander’s intent facilitate unity of effort to create and exploit relative advantages. Higher echelon leaders provide subordinate echelons access to information and the authority to use Army and joint multidomain capabilities through delegation. Leaders delegate appropriate authority to subordinates based on an assessment of their competence, talents, and experience.
COMMANDER PRESENCE ON THE BATTLEFIELD
8-6. Commanders provide leadership in combat to inspire their Soldiers, especially in challenging situations. Command presence is the influence commanders have on those around them, through their physical presence, communications, demeanor, and personal example. Commanders establish command presence through personal interaction with subordinates, either physically or virtually through C2 systems, and demonstrating their character, competence, dignity, strength of conviction, and empathy prior to and throughout operations.
8-7. Commanders go where they can best influence operations, assess units, and improve unity of effort. Where commanders place themselves on the battlefield is one of the most important decisions they can make. Commanding forward allows commanders to effectively assess and manage the effects of operations on their formations through face-to-face interactions. It allows them to gather information about actual combat conditions, but it must be balanced against the requirement to be where the best overall situational awareness can be maintained for the entire formation. As far as operational conditions allow, leadership should be exercised up front at critical times and places without interfering with subordinate leader prerogatives, becoming unreachable by other elements of the unit, or making it simpler for the enemy to target multiple echelons of leadership in one place.
8-8. At the battalion level and below, commanders lead by personal example, acquire much information themselves, and communicate face to face with those they direct. Typically, they position themselves well forward to influence the main effort during different phases of an operation. However, even at these levels, commanders cannot provide direct leadership for their whole unit given the challenges of maintaining continuous communications when units are dispersed or in contested electromagnetic environments.
8-9. At higher levels, echeloned command posts are central to effective C2. During operations, commanders must assess the situation up front as often as possible without being disruptive to the focus of subordinate commanders. They deliberately plan and organize their C2 approach to mitigate their loss of broad situational understanding during battlefield circulation by the development of subordinate commanders, and staff officers empowered to make decisions on the commander’s behalf to exploit opportunities and respond to changing circumstances without needing to ask permission.
8-10. Commanders convey importance and focus the efforts of the command by how they communicate, regardless of where they are physically located. A calm and authoritative tone of voice generates a sense of presence, as does a crisp and efficient manner of providing guidance; both require practice to master. No matter their location, effective commanders encourage their troops, sense their morale, and inspire through personal example. Commanders balance the risk of commanding forward with necessity to build trust by depending upon subordinates to accurately report and demonstrate initiative in their portion of an area of operations (AO). Lieutenant General Eichelberger’s actions to identify and address problems faced by the 32d Infantry Division in Buna in 1942 provide an effective example of commanding forward.
In autumn 1942, U.S. forces were attempting to establish positions from which to drive the Japanese from New Guinea and the adjacent islands. The 32d Infantry Division was to eliminate Japanese positions near the village of Buna. By the end of November, however, the division had made little progress, and General Douglas MacArthur sent Lieutenant General Robert Eichelberger, I Corps commander, there to correct the situation. Eichelberger’s instructions were to “remove all officers who won’t fight [and]… if necessary, put sergeants in charge of battalions and corporals in charge of companies.”
Eichelberger and his staff arrived on 2 December and were disturbed by what they observed: Soldiers were suffering from a number of tropical diseases. Rations were scant. There was little discipline or military courtesy. Morale was low. Organization was very poor. Only a few Soldiers were at the front line; many were in the rear areas, sent there initially to recover from illness or injury, but now under no one’s effective control. Fearing the jungle, Soldiers were afraid to patrol and, consequently, did not know the location of Japanese positions. Leadership at all levels was ineffective.
Eichelberger moved quickly to address these problems. He had supplies flown in and distributed so that Soldiers became better fed, clothed, and medically treated. He stopped offensive operations for two days to reestablish effective C2. Patrols were sent out nightly, and Japanese positions identified. Several commanders, including the division commander, were replaced with officers who could instill a more disciplined and aggressive attitude. Eichelberger was frequently near the front, wearing his rank openly to show his Soldiers their commander was present. In addition to demonstrating to his men that he was willing to share the same risks, Eichelberger was able to observe battlefield conditions personally, leading to better commander’s visualization.
By 3 January 1943, after a series of resolute—albeit costly—attacks, the 32d Infantry Division had overcome organized resistance at Buna. Eichelberger’s actions reversed the tide of battle in the theater. From a collection of demoralized units, he created a fighting force that stopped the Japanese advance.
8-11. Physical presence allows commanders to gain firsthand appreciation for the situation that they can rarely gain any other way. Face-to-face discussions in their own or subordinate command posts and forward presence allow commanders to see things that may not be conveyed by C2 systems. Forward presence demonstrates a willingness to share danger and hardship, and it provides an opportunity to motivate subordinates. Commanders should avoid putting their subordinates at additional risk when they are forward, however, since the enemy is likely to quickly target senior commanders when their location becomes obvious. The same consideration applies to their own command posts, which should disperse their footprint and reposition often enough to complicate enemy targeting. The following factors, common to all levels of command, may influence where commanders position themselves:
The need to understand the situation.
The need to make decisions.
The need to communicate.
The need to motivate subordinates.
8-12. Commanders delegate authorities to subordinate leaders for the conduct of operations based upon their judgment of their capabilities. This allows the commander to be elsewhere, potentially in a location that permits broader perspective and understanding. It also enables faster decision making in contested environments than if both leaders were in the same location, and it prevents the need for continuous communication. Continuous communication allows enemy forces to detect and target commanders, subordinates, and command posts. It should be avoided whenever possible. Exercising a mission command approach to C2 and delegating the broadest possible authorities to subordinate leaders empowers them to exploit opportunities and conduct more effective distributed operations.
COMMANDER’S INTENT
8-13. The commander’s intent is a clear and concise expression of the purpose of an operation and the desired objectives and military end state (JP 3-0). The commander’s intent succinctly describes what constitutes success for the operation. It facilitates unity of effort as it allows subordinates to understand what is expected of them, what constraints apply, and most importantly, why the mission is being conducted. Understanding why a mission is conducted is important both in maintaining unity of effort and in bolstering the morale and will of subordinates. Soldiers who understand why they are called upon for a specific mission, and how that mission aligns with the higher echelon commander’s intent and concept of operations, are more committed to the success of that specific mission.
8-14. Commanders communicate their intent two echelons down to ensure subordinates understand the boundaries within which they may exercise initiative while maintaining unity of effort. They likewise understand the commander’s intent two echelons above them. A clear and concise commander’s intent should be easily remembered and understood even without an order. Commanders collaborate with subordinates to ensure their commander’s intent is understood. Soldiers who understand the commander’s intent are more able to exercise disciplined initiative in unexpected situations than those who do not.
INITIATIVE
8-15. Leaders at every echelon exercise initiative as they follow orders and adhere to a course of action or scheme of maneuver. When the enemy does something unexpected, or a new threat or opportunity emerges that offers a greater chance of success, subordinate leaders take action to adjust to the new situation and achieve their commander’s intent. Disciplined initiative requires a bias towards action rather than waiting on new orders. The mission command approach to C2 demands subordinates exercise initiative in the absence of orders, when current orders no longer apply, or when an opportunity or new threat presents itself. The cumulative effect of multiple subordinate commanders, leaders, and individual Soldiers exercising initiative produces agility in Army formations. It enables Army forces to seize the operational initiative as they pose multiple dilemmas on the enemy.
8-16. Commanders and subordinate leaders develop subordinates capable of exercising effective initiative during both training events and operations. Leaders create opportunities during training events in which subordinates must take action on their own. Commanders must foster a climate that encourages initiative during training, before the unit is committed to combat. Accepting risk and underwriting good faith mistakes establishes a unit culture that allows subordinates to learn and gain the experience they need to operate under their own responsibility. Endurance requires that the burdens of combat leadership be shared between leaders at each echelon, which is not possible without a leadership culture that demands disciplined initiative.
DISCIPLINE
8-17. Discipline underpins the effective application of initiative during operations. For many parts of an operation, the benefits of exercising disciplined initiative outweigh the cost in synchronization. At other times, when synchronization or a specific process is critical to successful execution, ill-advised initiative can be costly. Neither commanders nor subordinates are independent actors when exercising initiative. Subordinates consider at least two factors when deciding how to exercise initiative, assessing each in terms of the circumstances affecting it:
Whether the benefits of the action outweigh the risk of desynchronizing the overall operation.
Whether the action will further attainment of the desired end state.
(See ADP 6-0 for more information on disciplined initiative.)
ACCEPTING RISK TO CREATE AND EXPLOIT OPPORTUNITIES
8-18. Risk, uncertainty, and chance are inherent to all military operations. The pace and tempo of large-scale combat operations demands a high level of expertise for commanders and staffs. Commanders delegate risk acceptance to subordinates through their commander’s intent and other guidance. Based on this guidance, refined as necessary by the commander and staff as the situation changes, leaders accept risk during operations by massing effects in one area while taking economy of force measures in other areas to create opportunities that can be exploited. Understanding how much or what kind of risk to accept requires the ability to accurately see friendly and enemy forces and an operational environment in the context of a particular situation. Leaders and staff officers who are competent in all aspects of their specialties assist the commander in weighing the risk of various decisions and courses of action, balancing short-term versus longterm risk to the mission and the force. This analysis, coupled with imagination and the courage to act boldly, provides opportunities that outweigh the risk incurred. Successful commanders are aware of the effects of cumulative risk over time, and therefore they continuously assess it throughout an operation.
8-19. Opportunities to exploit a relative advantage are fleeting during large-scale combat operations against a capable enemy that adapts quickly. Delaying action while setting optimal conditions, waiting for perfect intelligence, or achieving greater synchronization may end up posing a greater danger than swift acceptance of significant risk now. Leaders’ judgment of risk must be thoroughly informed by their understanding of their operational environment, particularly how actions in other domains impact their forces and how their forces can generate effects outside the land domain. Leaders maintain a common operational picture with their counterparts in higher and lower echelons, since any risk accepted at one echelon may impose additional risk at other echelons. (See paragraphs 8-47 and 8-48 for further discussion on communicating with subordinates.)
8-20. Contingency planning enables commanders to swiftly decide and act when the unexpected occurs. By considering multiple enemy courses of action, available friendly capabilities, and developing appropriate branch and sequel plans, the staff and the commander develop a deeper appreciation for how an operation could unfold and build flexibility into their plans. Contingency planning also guards against confirmation bias, where situational cues are interpreted in ways that match preconceived ideas. Effective planning expands understanding of a situation and operational environment, allowing the commander and staff to be better postured to rapidly decide, adjust, or simply be proactive.
8-21. Commanders designate commander’s critical information requirements (CCIRs) linked to decision points during operations and the execution of branch and sequel plans developed during contingency planning. CCIRs help subordinate leaders prioritize allocation of information collection assets and other limited resources, including time. Detailed contingency planning and the development of CCIRs ensure that commanders and staffs are proactive rather than reactive in responding to enemy activity. CCIRs potentially become irrelevant as the situation changes; therefore, commanders, staffs, and other leaders must regularly review and update CCIRs to ensure relevance throughout the conduct of operations. This is a forcing function for questioning earlier assumptions made during planning that may no longer be valid. (See ADP 2-0 and ADP 6-0 for more detailed descriptions of what constitutes CCIR.)
8-22. Commanders and staffs remain alert to exceptional information during operations. Exceptional information results from an unexpected event or opportunity, or a new threat, which directly affects the success of operations. It would have been a CCIR if it had been foreseen. Identifying exceptional information requires initiative from subordinates, shared understanding of the situation, a thorough understanding of the commander’s intent, and the exercise of judgement based on experience.
COMMAND AND CONTROL DURING DEGRADED OR DENIED COMMUNICATIONS
8-23. U.S. adversaries, including Russia and China, have demonstrated the ability to contest communications in the electromagnetic spectrum and degrade friendly C2. Degraded connectivity to a secure communications network poses risks to situational understanding, C2, and ultimately mission accomplishment. Army forces must be prepared to continue operations and achieve mission objectives when out of contact with higher echelons or adjacent units. They should assume intermittent rather than continuous connectivity during the course of operations. A mission command approach to C2 empowers subordinate leaders to act within the commander’s intent with degraded communications, reporting their new situation when able to do so.
8-24. Exercising C2 with degraded connectivity does not begin when communications break down or when a crisis develops. It must be trained and rehearsed as part of an overall cultural norm designed to make friendly forces more difficult to detect. Commanders ensure that staffs are trained on analog and manual C2, and that units have rehearsed reliable primary, alternate, contingency, and emergency communications plans. During extended periods of communication breakdown, C2 becomes more difficult as shared understanding of a situation deteriorates over time. To maintain C2 with degraded communication, personnel should be trained and proficient in—
Employing all available C2 systems.
Operating dispersed command posts.
Maintaining an other-than-digital common operational picture (COP).
Managing information with analog processes.
Monitoring communications channels and crosstalk across echelons.
Maintaining manual running staff estimates.
Conducting command post battle drills.
8-25. Army forces improve readiness for degraded communications by decreasing vulnerabilities and preparing appropriately. Units decrease their vulnerability through electromagnetic protection, including emission control, electromagnetic masking, electromagnetic hardening, and electromagnetic security. (See FM 3-12 for more information on electromagnetic protection.) Units practice degraded communications during training and rehearsals, including those that involve allies, and they use the mission command approach to C2 during garrison events. Ultimately, the solution to degraded communications is mission command and training. Even under severely degraded conditions, Army forces continue to make decisions and act in the absence of orders, when existing orders no longer fit the situation, or when unforeseen opportunities arise.
8-26. All leaders must be prepared to take action and make timely decisions when communication is not possible. The commander responsible for a decision may not be available to make that decision for a variety of reasons, such as jammed communications, the loss of a command post, or being killed by the enemy. In all cases, the senior leader able to communicate must be ready to take charge and make the best decisions possible based on available information so operations can continue. The actions of Navy pilots in a degraded communications environment during the battle of Midway demonstrated the effectiveness of exercising disciplined initiative.
On 4 June 1942, American naval aviators, acting on initiative and without communications from higher echelon headquarters, struck a major blow in the Pacific War at the Battle of Midway. The Japanese First Air Fleet, known as Kido Butai, launched a massive raid against Midway Island, causing significant damage. The American carriers Hornet, Enterprise, and Yorktown launched unsynchronized strikes against Kido Butai by several different air groups. Once aloft these carrier groups were soon beyond radio range of their ships and had to rely on prior intelligence, intuition, and luck to find the enemy.
Lieutenant Commander John Waldron, commander of Torpedo 8 (Hornet), believed his air group commander was leading the group on an incorrect heading. He broke formation and led his squadron on another course. They found Kido Butai and attacked, but the entire squadron was shot down because it had no fighter cover. The torpedo bombers of Torpedo 6 (Enterprise) followed Waldron’s squadron and also suffered heavy losses without scoring a hit. The dive bombers of Bombing 6 (Enterprise) and Scouting 6 (Enterprise) had launched earlier in the day and arrived at their designated coordinates without finding the enemy. Lieutenant Commander Clarence McClusky, commander of Bombing 6, could not radio back to the Enterprise for further orders. Exercising disciplined initiative, he began to search the area despite running low on fuel and found a Japanese destroyer, which he followed to Kido Butai just as Japanese fighters completed the destruction of Torpedo 8 and Torpedo 6. The Japanese fighters and anti-aircraft guns were entirely focused on the low altitude attacks from the torpedo bombers, leaving them vulnerable to a high-altitude divebombing run. McClusky ordered an attack by Bombing 6 which, by chance, occurred at the same time as Bombing 3 (Yorktown) arrived on the scene. The resulting action by two squadrons acting on their own initiative to carry out the mission fatally damaged three Japanese carriers, the Kaga, Akagi, and Soryu, which sank later in the day, putting the formerly outnumbered Americans at a 3:1 advantage in aircraft carriers.
The performance of commanders like Waldron and McClusky, out of contact with higher commands and acting on their own initiative, led to victory at Midway.
DRIVING THE OPERATIONS PROCESS
8-27. Commanders employ the operations process to incorporate coalition and joint partners, empower subordinate initiative, and to ensure authorities and risk acceptance are delegated to the appropriate echelon required for the situation. Staffs and subordinate headquarters earn the commander’s trust by providing relevant information, anticipating needs, and directing supporting actions. (See ADP 5-0 for more information on the operations process and FM 6-0 for more on the role of commanders in operations.)
8-28. The major components of the operations process are planning, preparing, executing, and continuously assessing the operation. Planning normally begins upon receipt of orders from a higher echelon headquarters and continues through the execution of the operation. The commander and staff continually assess operations and revise the plan through fragmentary orders. Commanders, assisted by their chiefs of staff or executive officers, drive the preparation for an operation by allocating time, prioritizing resources, and supervising preparation activities such as rehearsals to ensure their forces are ready to execute operations. During execution, commanders and staffs focus their efforts on translating plans into direct action to achieve objectives in accordance with higher commander’s intent. (See figure 8-1 on page 8-8 for a graphic depiction of the operations process.)

UNDERSTAND
8-29. An operational environment includes portions of the land, maritime, air, space, and cyberspace domains encompassing the area of operations and area of interest, understood through three dimensions— human, physical, and information. Understanding how capabilities employed from each of the domains influence outcomes in the three dimensions is foundational to success during operations. Commanders communicate that understanding to subordinates. Commanders collaborate with their staffs, other commanders, and mission partners to accurate frame the operational environment encompassing the mission objectives. Commanders must be comfortable with a certain degree of uncertainty and ambiguity within an operational environment—delaying action while seeking perfect understanding may prevent a unit from exploiting a fleeting opportunity or make it vulnerable to enemy attack.
8-30. Commanders, supported by their operations and intelligence staff sections, direct the collection of information and allocate capabilities from as many domains as possible. They use operational and mission variables, intelligence preparation of the battlefield, and running estimates to help understand how capabilities in each domain affect operations on land and vice versa. Competent commanders circulate throughout their AORs as often as possible, collaborating with subordinate commanders and leaders while observing the situation for themselves. Subordinates often possess a deeper or more nuanced sense of the local situation or aspect of an operation than commanders. Direct exposure to conditions on the ground often allows them to detect trouble or opportunity before a higher echelon staff member does. Maintaining shared understanding is therefore a dynamic, ongoing process, since situations change as operations progress.
VISUALIZE
8-31. Commanders visualize a desired end state and potential solutions to solve or manage identified problems. Commanders look up, out, and down as they develop their visualization of an operational environment, relying on information and observations from superior and adjacent commanders, their staffs, and subordinate commanders. An operational approach may require capabilities provided by external organizations, and the effects delivered may be dependent on conditions in other domains.
DESCRIBE
8-32. Commanders describe their visualization to staffs and subordinate commanders to facilitate shared understanding and purpose. Through collaboration and dialogue, commanders ensure subordinates understand the visualization well enough to plan and conduct operations. Commanders continue to refine their visualization throughout the planning and execution of an operation and balance frequent communication of this updated visualization with the need to provide sufficient time and freedom of maneuver to subordinate leaders. Commanders’ descriptions of their visualizations should account for interdependencies among various domains and the desired end states within those domains.
DIRECT
8-33. Commanders direct action to achieve results and lead forces to mission accomplishment. Decision making and timely sharing of information ensures friendly forces reach a position of advantage relative to the enemy. Commanders who are able to sense, understand, decide, act, and assess faster and more effectively than enemy commanders can impose multiple dilemmas, requiring enemy forces to dedicate resources and combat power which otherwise might further their objectives. Creating and maintaining this state of decision dominance depends on the actions of the commander, informed by a knowledgeable and integrated staff. Communications systems and other technologies can help enable decision dominance, but leaders must take care to ensure they do not become overly reliant on technical solutions that may not always be available.
LEAD
8-34. Leadership is the most decisive element of combat power. Effective leadership can compensate for deficiencies, while poor leadership can negate advantages. Commanders lead by personal example, the quality of the guidance they provide throughout the operations process, and the actions they take during the execution of operations. They focus on the decisions only they can make. Operations encompassing the employment of capabilities from multiple domains demand rapid adjustments based on brief windows of opportunity. Tactical patience is required to develop the conditions that create those opportunities over time. When making or changing decisions, the commander’s will and personal presence provides the moral impetus for necessary action in a timely manner. Friction is inherent in all military operations, and leadership exerted by commanders and their subordinate leaders is what overcomes it.
ASSESS
8-35. Commanders, supported by their staffs, assess the situation before execution and throughout operations to understand conditions and determine what decisions they must or are likely to make. They compare the state of current operations to what was anticipated or planned, remain alert to variance from expectations, and watch for information indicating an emerging threat or opportunity. Continuous assessment helps commanders anticipate and adapt their forces to changing circumstances, enabling friendly forces to counter unexpected threats or exploit opportunities. Effective commanders encourage cross talk and dialogue between superior, subordinate, and adjacent staffs, and they conduct dialogue between commanders to share observations and maintain situational understanding. They continuously review assumptions and cumulative risk. Commanders must not be overly fixated on what is happening or may happen on the ground in the physical dimension. Not assessing the relevant events occurring in other domains, or not considering the information or human dimensions, increases the odds that enemy forces can achieve surprise.
ADAPTING FORMATIONS FOR MISSIONS AND TRANSITIONS
8-36. The conduct of successful operations requires leaders and units that are able to anticipate changes and quickly adapt their formations, dispositions, or activities to meet those changes. Anticipating and adapting to changes begins with commanders, but all leaders help create agile and adaptive units, develop subordinates, inspire resilience in their people, and maintain mission focus in the face of adversity.
8-37. Changing conditions and transitions may impact the teamwork and cohesion of a formation; both require adaptation and leader attention. Some examples include—
Task organization changes.
New or changing guidance.
Periods of intense privation and fatigue.
Mission transitions.
Mission failures or setbacks.
Reconstitution.
The example of VII Corps actions during the Gulf War demonstrate how teamwork and cohesion allow units to rapidly adapt and act when situations quickly change.
On the morning of 17 January 1991, the day after the start of U.S. Central Command’s major air operation against Iraq, the VII Corps commander, Lieutenant General Frederick Franks, was with the 1st Infantry Division as it honed tank and Bradley gunnery skills in the desert of Saudi Arabia. While there, he received a spot report from Brigadier General John Landry, Corps Chief of Staff, over the radio: “55 Iraqi tanks have crossed the Kuwaiti Border, heading southwest toward Hafir al-Batin and are engaging Egyptian coalition forces in what may be the beginnings of an Iraqi preemptive strike.”
Within seconds, Colonel Johnnie Hitt, commander of the Corps’ 11th Aviation Brigade, entered the net indicating that he had monitored the report and alerted two Apache battalions that could respond in 30 minutes if necessary. At the same time, Colonel Don Holder, commander of the 2d Armored Cavalry Regiment, the Corps unit closest to the reported enemy, called to notify Franks that he had issued orders for the entire regiment to occupy blocking positions in the area and to make contact with the enemy force with air and ground scouts. Those were the immediate and correct actions taken by commanders as a result of monitoring the command network and having the confidence to act—confidence developed through training, teamwork, and trust among the key players of the VII Corps team.
8-38. Commanders are responsible for developing subordinate leaders and units that are capable of adapting to the environment and the dynamic nature of operations. Training is the primary opportunity to do so, and all leaders must work to be experts at training formations and developing subordinates during that training. Successful adaptation and leader development depends on a command climate and learning environment that encourages subordinates at all levels to become subject matter experts, think independently, and take the initiative. Using a mission command approach, leaders foster a sense of shared commitment and involvement in decision making. (See FM 6-22 for more information on leader development in a learning environment.) Leaders help establish the conditions for subordinate adaptation by—
Developing leadership experience.
Fostering shared understanding.
Communicating with staff and subordinates.
Developing teams.
DEVELOPING LEADERSHIP EXPERIENCE
8-39. Commanders and leaders develop subordinates when they prepare and then challenge them with greater responsibility, authority, and accountability. They prepare their subordinates to succeed at the next level of responsibility, since during combat many subordinates will be required to move up and replace more senior leaders who become casualties, usually with no warning. It is the individual professional responsibility of all leaders to develop their subordinates. (See FM 6-22 for more information on leader development.)
8-40. Commanders and leaders may develop their subordinates by observing them in training, accepting subordinates’ risk taking when the consequences of failure are not decisive, and providing accurate feedback. Leaders allow subordinates to accept risk on their behalf. They ensure subordinates make analytic risk decisions as time and circumstances allow, while informing their higher echelon command of the risks they are accepting. During training, leaders may allow subordinates to accept excessive tactical risk as a teaching point to ensure they learn what types of risk are acceptable, which are not, and how to better assess risk. This sort of coaching helps leaders gain trust in their subordinates’ judgment and initiative, and it builds subordinates’ trust in their leader. During operations, leaders intervene when subordinates accept risk that exceeds the potential tactical benefits to the mission. Leaders inform subordinates, either at the time of the decision (if time permits) or in an after-action review, of the residual risk accepted and why. They ensure that risk management does not become risk aversion.
8-41. Inculcating risk acceptance goes hand in hand with accepting mistakes made in good faith. Subordinates who learn from bad decisions become better leaders, and commanders who underwrite those mistakes create a command climate where subordinates learn and gain the experience required to thrive under hardship. Leaders reinforce the importance of a bias towards action by highlighting the value of simply making a decision during operations, including imperfect decisions. Even so, commanders do not repeatedly underwrite subordinates’ mistakes resulting from repeated lack of judgment or an inability to learn. Nor do they tolerate repeated errors of omission or inaction where subordinates fail to exercise initiative. Leaders act to ensure subordinates learn from mistakes. Methods of doing this include—
Publicly discussing a mistake as part of an after-action review, including one made by the leader, to determine a better way to achieve the same purpose.
Correcting a subordinate directly, in situations when there is no time for an after-action review or to enable better shared understanding by the entire team.
Correcting the systemic problem that enabled the mistake.
8-42. Commanders prepare their subordinates to take their place when required, and they use training events and professional development sessions to reinforce the value and necessity of exercising bold, appropriate initiative. In addition to allowing progress over time, this prepares leaders to quickly assume greater responsibilities immediately during combat. If an echelon of command is destroyed or otherwise made mission ineffective during combat operations, a subordinate leader must assume command as quickly as possible. This may include elements of a subordinate echelon commander and staff assuming the responsibilities of a higher echelon headquarters.
8-43. Self-awareness enables leaders to recognize their strengths and weaknesses and then to take appropriate action. Leaders develop self-awareness through self-critique and self-regulation during training and operations. They actively seek feedback, adapt to change, and possess the humility to accurately examine their own experiences, performance, judgment, and decision making. Under rapidly changing conditions, leaders’ self-awareness is a critical factor in making accurate assessments of changes and their own personal capabilities to operate effectively in those conditions.
FOSTERING SHARED UNDERSTANDING
8-44. Shared understanding enables a mission command approach to C2. Commanders communicate their intent two echelons down, and leaders look two echelons up to gain an understanding of the commander’s intent, priorities of effort, and desired end state for operations. Commanders ensure understanding of their intent during continuous dialogue with their subordinates. When relayed in an environment of mutual trust and shared understanding, the commander’s intent frees commanders to move about the battlefield knowing their subordinates understand the end state and what must be done to achieve it, even as conditions change. Such climates allow leaders to operate knowing subordinates accurately and promptly report both positive and negative information. Prompt and accurate reporting is critical in maintaining the tempo of decentralized operations by dispersed forces along multiple axes.
8-45. Establishing shared understanding begins with leaders who educate and train themselves and their subordinates in applicable allied, joint, and Army doctrine and common tasks, techniques, and procedures. Training develops the teamwork, trust, and shared understanding that commanders need to exercise mission command and that forces need to achieve unity of effort. This is especially important when units are taskorganized and have different command structures than they had prior to an operation.
8-46. Coalition, joint, and Army C2 systems can enable distributed operations in a permissive environment. Some systems, however, will be degraded by enemy or other action to a point that they may not be usable. In these instances, the previously developed shared understanding enables subordinate leaders to take effective action on their own while still working towards their commander’s end state. (See paragraphs 8-23 through 8-26 for more information on degraded communications and leadership.)
COMMUNICATING WITH STAFF AND SUBORDINATES
8-47. Written orders continue to have an indispensable place in exercising C2, particularly before operations commence and during their early stages. Clearly written orders promote consistency of approach in all areas of C2, and they provide a common frame of reference from which to depart. During operations, oral communications tend to be more important than written communications, for reasons of time and because of the importance of personal interaction while leading. Face-to-face communication is the most effective method, because humans use more than words to express themselves and understand each other. It is, however, impossible to communicate face-to-face with all subordinates during engagements and battles. Operations at the BCT level and below during close combat are largely dependent upon rapid, efficient tactical radio communications. The military bearing of leaders when interacting in person, and the tone of voice they use during communications when not in person, have significant impacts on their subordinates.
8-48. Effective leaders take positive steps that encourage, rather than impede, communications among and with their subordinates and staff members. They make themselves available for dialogue, and they are open to new information. Leaders who react rashly to new information, or who create barriers to communication, whether intentional or not, decrease the chances that they will receive the timely information needed to make critical decisions, and they may hinder the initiative of subordinates. Failure to properly receive and act on new information leads to mission failure.
DEVELOPING TEAMS
8-49. Successful operations require shared understanding across domains and effective teamwork with the joint and multinational organizations operating in those domains. Developing teams requires continuous effort. It begins during home station activities and continues throughout preparation for and execution of operations. Leaders may serve with unfamiliar subordinate units or serve under an unfamiliar higher echelon headquarters, and they may have their task organization change multiple times during execution. To effectively understand capabilities and lead across domains, Army leaders must also build trust with elements of the joint force and Army units they may never see to effectively employ their capabilities. They need to interact effectively with host-nation, allied, and partner nation forces, along with interagency and intergovernmental partners, to ensure unity of effort when bringing to bear effects controlled by those outside the joint force.
8-50. Operational requirements may cause units to deploy with different command structures than those used at home station. Often they will not have trained with the higher echelon headquarters that employs them. Collaboration and dialogue across echelons can mitigate these potential obstacles to team building. Through these interactions, commanders gain insight into the needs of unfamiliar organizations while also sharing their own vision and understanding.
8-51. By circulating among subordinate units, commanders can assess readiness, get to know new units in the task organization, and personally motivate Soldiers. Leaders also visit and build productive personal relationships with civilian leaders in other agencies, nongovernmental organizations, and the local population in their AOs. Knowledge gained during these visits enables commanders to maintain situational understanding and continuously update their visualization prior to and during execution.
8-52. Different levels of training and cultures among organizations can pose challenges to building teams. Army leaders apply their understanding of different cultures and agencies to place military efforts in context and to serve on civil-military teams. To help build partnerships, commanders strive to have partners—
Represented, integrated, and actively involved in planning and coordinating activities.
Share an understanding of the situation and problems to solve.
Collectively determine the resources, capabilities, and activities necessary to achieve their goals.
Work for unity of effort toward achieving common goals.
8-53. Successful operations require leaders working with partners to develop a shared understanding of the environment and a common commitment to solutions. Achieving unity of effort requires Army leaders to have a high degree of cultural understanding and social skills. Without such understanding and skills, leaders may fail to collaborate with diverse partners.
8-54. Quality leader development and training is required to grow and develop leaders capable of success during operations. Deliberate investment in the abilities of individual leaders, teams, and units is foundational to prosecuting those operations successfully across the competition continuum. (See FM 6-0 for more information on C2, FM 6-22 for more information on leader development, FM 7-0 for more information on training, and ATP 6-22.6 for more information on Army team building.)
Appendix A - The Principles of War
This appendix discusses the traditional principles of war. It then discusses the principles of joint operations.
THE TRADITIONAL PRINCIPLES OF WAR
A-1. The nine principles of war represent the most important physical, human, and information factors that affect the conduct of operations at the strategic, operational, and tactical levels. The principles are not a checklist. While considered in all operations, they do not apply in the same way to every situation. Rather, they summarize characteristics of historically successful operations. Applied to the study of past campaigns, major operations, battles, and engagements, the principles of war are powerful analysis tools. Joint doctrine adds three principles of operations to the nine traditional principles.
A-2. Originally derived from J.F.C. Fuller’s published works for the British army, the principles have essentially remained the same over the last century, standing the test of analysis, experimentation, and practice in war. Fuller is not the only influence on the U.S. Army’s theory of victory, which is the sum of over two centuries of experience and study on the art of war and warfare. Eastern and Western military theorists have often debated constants in the nature of war, and the principles of war as currently described are informed by many points of view. Though the theories of victory and operational concepts have evolved to meet the demands of military operations throughout the decades, the principles have stayed relevant. Fuller ended his work in 1926 with a valuable maxim. Quoting Napoleon Bonaparte, he wrote, “The whole art of war consists in a well-reasoned and extremely circumspect defensive, followed by rapid and audacious attack.” Fuller closed his 1926 work, The Foundations of the Science of War, by summarizing the quote in three bold words: GUARD, MOVE, HIT.
A-3. In Army doctrine, a principle is a comprehensive and fundamental rule or an assumption of central importance that guides how an organization approaches and thinks about the conduct of operations (ADP 1-01). Principles apply to the conduct of operations in general and to specific organizations or functions. The principles of war are just one example. The nine traditional principles are organized deliberately, enabling a practitioner to begin with actions on the objective and cognitively work backwards to through the process of organizing forces and activities to accomplish their mission. The principles are—
Objective.
Offensive.
Mass.
Economy of force.
Maneuver.
Unity of command.
Security.
Surprise.
Simplicity.
OBJECTIVE
A-4. When undertaking any mission, commanders should have a clear understanding of the expected outcome and impact. The ultimate military purpose of war is the defeat of the enemy’s armed forces and will to fight by the use of organized violence or the threat of violence. The principle of objective drives all military activity toward that end, with the least possible employment of resources on secondary considerations. This requires a clear vision of the desired end state. Army commanders need to appreciate the political purpose that war aims to achieve, and they need to understand how military conditions contribute to national policy objectives. Commanders cannot separate the objective from the considerations of restraint and legitimacy. Without these considerations, military actions can make strategic objectives unobtainable.
A-5. Below the strategic level, objective means ensuring all actions contribute to the goals of the higher echelon headquarters. The attainment of intermediate objectives must be direct, quickly and economically contributing to the ultimate end state. Commanders designate objectives that are decisive to accomplishing the mission. These become the basis for all subordinate plans. Actions that do not contribute to achieving the objective should be avoided. Conversely, determining and denying enemy forces their objectives narrow options for enemy commanders to freely maneuver and exploit emerging opportunities. Denying enemy forces their objectives while achieving the friendly objective is the ultimate purpose of all operations.
OFFENSIVE
A-6. The principle of offensive suggests that offensive action, or maintaining the initiative, is the most effective and decisive way to pursue and attain a clearly defined common objective. This is fundamentally true across all levels of warfare. When it is necessary to defend, commanders and staffs maintain an aggressive mindset that seeks to attack the enemy throughout the depth of its formations and sets the conditions for offensive action. The offense ensures that a force captures and holds the initiative, maintains freedom of action, and achieves results. It permits political and military leaders to initiate operations on their own terms, impose their will on the enemy, set favorable conditions for battle, exploit vulnerabilities, and react rapidly to changing situations or emerging developments. No matter the echelon, the side that retains the initiative through offensive action forces its opponent to react, rather than act.
A-7. The offensive applies to the operations and activities Army forces conduct in each domain. An operational approach focused only on land can be defeated by opponents exploiting an offensive approach in the other domains. Likewise, an offensive approach should extend to the human and information dimensions of an operational environment Commanders and staffs maintain an offensive mindset during competition, crisis, and armed conflict.
MASS
A-8. Integrating all the elements of combat power and synchronizing their application against a decisive point achieves mass. Mass can be achieved in any of the domains and is mostly tied to the destroy defeat mechanism. Massing effects against one or more decisive points in one or more domains is typically an element of convergence. Concentrating forces, which should be done for only as long as necessary to avoid providing the enemy lucrative targets, is typically necessary to achieve favorable ratios during close combat. The massing of effects, together with the proper application of the other principles of war, may enable numerically inferior forces to achieve decisive campaign and battle outcomes. Mass, like objective, implies that it is best to minimize the use of resources on secondary efforts. The massing of effects at any echelon to produce a desired effect on enemy forces is crucial to enabling maneuver.
A-9. Denying enemy forces the ability to mass at the time or place of their choosing is another consideration for applying the principle of mass. Forcing enemy forces to maintain distributed operations, rather than massing effects or forces as they require for success, can keep an enemy force from achieving its objectives, reorganizing, or consolidating gains.
ECONOMY OF FORCE
A-10. A commander must employ available combat power in the most efficient way possible, and there is seldom enough combat power available to enjoy a favorable correlation of forces everywhere. Economy of force, a reciprocal of mass, demands the judicious employment and distribution of forces. It requires deliberately accepting risk in selected areas to achieve relative superiority—or overwhelming effects—in others. Economy of force involves the discriminating employment and distribution of forces. Commanders never leave any subordinate element without a purpose. The allocation of available combat power to tasks such as limited attacks, defense, delays, deception, or even retrograde operations is measured to achieve mass elsewhere. Accepting risk through economy of force creates opportunities to exploit.
MANEUVER
A-11. Maneuver is coordinated movement and fire in relation to enemy forces to put them at a disadvantage with the least cost to friendly forces. Firepower, mobility, protection, and leadership enable maneuver. Intelligence focuses–and sustainment enables–maneuver over distance and time. In the strategic sense, maneuver has three interrelated characteristics: flexibility, mobility, and maneuverability. Flexibility must characterize thought, plans, and operations to maintain the initiative during changing conditions with an adaptive enemy. Flexibility enhances rapid reaction to unforeseen circumstances. Mobility is the capacity to respond rapidly in crisis, move across strategic distances, and move to a position to conduct operational- and tactical-level maneuver.
A-12. Tactically, maneuver is about moving forces and firepower into better positions relative to enemy forces to gain a compelling advantage: the ability to destroy enemy forces unless they reposition while making friendly forces more difficult to fix and destroy. It contributes to seizing, retaining, and exploiting the initiative and preserving freedom of action. Maneuver allows commanders to concentrate and disperse forces to keep enemy forces off balance and out of position. Conversely, limiting enemy maneuver keeps them in positions of disadvantage, ideally leading to their eventual destruction or defeat at the time and place of the friendly commander’s choice.
UNITY OF COMMAND
A-13. This principle ensures that all efforts focus on a common goal. Unity of command means that a single commander coordinates the actions of all forces toward a common objective. Cooperation may produce coordination, but giving a single commander the required authority is the most effective way to achieve unity of effort. Ultimately a single commander is responsible for an objective at each echelon. Diffusing responsibility otherwise creates misunderstandings during the stress of combat. Commanders deny enemy forces unity of command by destroying or disrupting enemy C2, taking action to isolate enemy echelons, and exploiting boundaries between enemy formations. This makes coordination of forces, collaboration of planning, and cohesive operations more challenging for enemy commanders. Denying enemy forces unity of command is crucial to denying them the ability to exploit emerging tactical opportunities.
A-14. The joint, interagency, and multinational nature of operations creates situations where the commander does not directly control all organizations in the area of operations (AO). Achieving unity of effort under such conditions becomes the goal, which requires coordination and collaboration among forces-even though they may not be part of the command structure-toward a commonly recognized objective.
SECURITY
A-15. Security enhances freedom of action by protecting and preserving combat power while reducing friendly vulnerability to surprise. Every Army formation is responsible for its own security. The application of the principle of security does not suggest over-cautiousness or avoidance of risk but rather the unwillingness to cede any advantages to the enemy unnecessary. Security is closely related to the operational imperative that friendly forces operate under the assumption that they are under observation and always in contact with enemy forces. Security relies on gaining and maintaining enemy contact on friendly terms, and it is directly related to the principle of surprise. Preventing surprise by maintaining contact with enemy forces enhances security and denies them opportunities to seize the initiative.
A-16. At the strategic level, security requires active and passive measures to protect Army forces from espionage, subversion, and strategic intelligence collection. At the tactical level, it is essential to protection and the preservation of combat power. Security results from the protective measures commanders take to prevent surprise, observation, detection, interference, espionage, or sabotage.
SURPRISE
A-17. Surprise results from taking actions for which an enemy or adversary force is unprepared. It is a powerful, but temporary, combat multiplier. It is not essential to take adversary or enemy forces completely unaware; it is only necessary that they become aware too late to react effectively. When done well, surprise can decisively shift the balance of combat power in favor of friendly forces. Concealing capabilities and intentions is difficult. Rapid advances in strategic surveillance, information gathering, and data skimming, as well as the pervasiveness of social and mass media compound the difficulty of large-scale marshalling and movement of manpower and equipment.
A-18. Factors that contribute to surprise include speed of movement, employment of combat power the enemy does not expect, operations security, and variations in tactics that create ambiguity. Commanders can create surprise using changes to tempo, size of forces, direction or location of a main effort, and timing. Deception can aid in the probability of achieving surprise, and at the tactical level it is best practiced by showing enemy forces what they expect to see until the last possible moment and then doing something different. Proactive friendly reconnaissance and security measures deny enemy forces opportunities to surprise friendly forces.
SIMPLICITY
A-19. Guidance, plans, and orders should be as simple and direct as possible. Objectives and operations must be presented in clear, concise, understandable terms. At the tactical level, simplicity of plans and instructions contribute to successful operations and reduce the chances for misunderstanding and confusion. All factors being equal, a simple plan executed promptly is preferred to a complex plan executed too late. Simple plans allow better understanding and troop leading at all echelons, and they also permit branches and sequels to be easily nested, understood, and executed. Joint, interagency, and multinational operations place a premium on simplicity, accounting for differences in language and culture that can inherently complicate integration. Simple plans and orders minimize the confusion inherent in command posts during operations. The more complicated a plan is, the more vulnerable it is to friction. Simplicity addresses the fog and friction of war, helps commanders and their staffs to maintain shared understanding, and accounts for the nature of war as a human endeavor.
PRINCIPLES OF JOINT OPERATIONS
A-20. Joint doctrine adds three principles of operations (perseverance, legitimacy, and restraint) to the traditional nine principles of war to account for operations other than conventional large-scale combat, such as peacekeeping and counterinsurgency. The additional principles are relevant to how the joint force uses combat power across the competition continuum, particularly during limited contingency. Like the traditional principles, these three do not apply equally across all joint operations but can be universally important and directly relate to the laws of armed conflict. The additional principles are—
Restraint.
Perseverance.
Legitimacy.
(See JP 3-0 for more detailed information on the principles of joint operations.)
RESTRAINT
A-21. The purpose of restraint is to prevent the unnecessary use of force when better methods of achieving the objective exist. Restraint informs legitimacy.
A-22. Destructive force can have a negative military and political consequences in some contexts. Therefore, judicious use of force is necessary. Restraint requires the careful and disciplined balance of security, the conduct of military operations, and national objectives. Excessive force antagonizes those parties involved, thereby damaging the legitimacy of friendly forces and potentially enhancing the legitimacy of the adversary. Sufficiently detailed rules of engagement from a commander tailored to the specific circumstances of the operation can facilitate appropriate restraint.
PERSEVERANCE
A-23. The purpose of perseverance is to ensure the commitment necessary to achieve national objectives. Perseverance recognizes that enduring outcomes may require enduring commitment of forces.
A-24. Perseverance involves preparation for measured, protracted military operations in pursuit of national objectives. Some joint operations may require years to reach the desired end state. The underlying causes of the crisis may be elusive, making it difficult to achieve decisive resolution. The patient, resolute, and persistent pursuit of national goals and objectives is essential to success. This frequently involves diplomatic, economic, and informational measures to supplement military efforts. Army leaders contribute to perseverance by managing the expectations of seniors and subordinates while setting reasonable objectives to achieve over time.
LEGITIMACY
A-25. The purpose of legitimacy is to maintain legal and moral authority during the conduct of operations. It is relevant across the competition continuum and the range of military operations. Legitimacy, a decisive factor in the application of information in the operational environment, is based on the actual and perceived legality, morality, and rightness of the actions from the various perspectives of interested audiences. These audiences can include our national leadership and domestic population, governments, civilian populations, and nations and organizations around the world.
A-26. Committed forces must sustain the legitimacy of the operation and of the coalition and host government, particularly when the host or partner government’s legitimacy is decisive to the operation. All actions must be considered in the light of competing strategic and tactical requirements, and exhibit fairness in dealing with competing factions where appropriate. Legitimacy may depend on adherence to objectives agreed to by the international community, ensuring the action is appropriate to the situation and to the perception of fairness in dealing with various factions. Restricting the use of force, restructuring the type of forces employed, protecting civilians, and ensuring the disciplined conduct of the forces involved may reinforce legitimacy.
Appendix B - Command and Support Relationships
This appendix describes command and support relationships for joint, Army, and multinational forces.
COMMAND
B-1. Command is central to all military action, and unity of command is central to unity of effort. Inherent in command is the authority that a military commander lawfully exercises over subordinates, including the authority to assign missions and accountability for their successful completion. Command is exercised in both the administrative and operational branches of the chain of command, although the specific authorities differ. Although commanders may delegate authority to accomplish missions, they may not absolve themselves of the responsibility for the accomplishment of these missions. Authority is never absolute; the extent of authority is specified by the establishing authority, directives, and law. (See JP 1, Volume 2 for more information on command.)
SUPPORT RELATIONSHIPS
B-2. A support relationship is established by a common superior commander between subordinate commanders when one organization should aid, protect, complement, or sustain another force. The support relationship is used by the Secretary of Defense to establish and prioritize support between and among combatant commanders (CCDRs), and it is used by joint force commanders (JFCs) to establish support relationships between and among subordinate commanders. (See JP 1, Volume 2 for more information on support.)
CHAIN OF COMMAND
B-3. The President and Secretary of Defense exercise authority and control of the armed forces through two distinct branches of the chain of command, as described in JP 1, Volume 2: the operational and administrative branches. The operational branch runs from the President, through the Secretary of Defense, to the CCDRs for missions and forces assigned to combatant commands. The administrative branch runs from the President through the Secretary of Defense to the secretaries of the military departments.
B-4. The typical operational chain of command extends from the CCDR to a joint task force (JTF) commander, then to a functional component or Service component commander. JTFs comprise forces from more than one Service placed under the operational control (OPCON) of the JTF. Within their commands, CCDRs and JTF commanders establish joint command relationships among forces as described in paragraphs B-7 through B-12.
B-5. Under joint doctrine, each Unified Command includes a Service component command that provides administrative control (ADCON) for Service forces assigned to that Unified Command. A Service component command consists of the Service Component headquarters and all Service Forces assigned to the Unified Commander. Army doctrine distinguishes between the Army component of a combatant command and Army components of other joint forces. Under Army doctrine, Army Service component command (ASCC) refers to the Army component assigned to a combatant command. There is only one ASCC within a combatant command’s area of responsibility. The Army components of all other joint forces are called ARFORs. An ARFOR is the Army component and senior Army headquarters of all Army forces assigned or attached to a combatant command, subordinate joint force command, joint functional command, or multinational command. (FM 3-94) It consists of the senior Army headquarters and all Army forces that the CCDR subordinates to the JTF or places under the control of a multinational force commander. The ARFOR becomes the conduit for ADCON functions specified in unit deployment orders. (See FM 3-94 and JP 3-0 for more information on ARFOR.)
JOINT COMMAND RELATIONSHIPS
B-6. JP 1, Volume 2 specifies and details four types of joint command relationships. They are—
Combatant command (command authority) (COCOM).
Operational control.
Tactical control.
Support.
COMBATANT COMMAND (COMMAND AUTHORITY)
B-7. COCOM is the command authority over assigned and allocated forces vested only in commanders of combatant commands or as directed by the President or the Secretary of Defense in the Unified Command Plan and cannot be delegated or transferred. COCOM only extends to those forces assigned or allocated to the combatant command by the Secretary of Defense. COCOM is established in federal law by Section 164, Title 10, United States Code (USC). Normally, the CCDR exercises this authority through subordinate JFCs, Service components, and functional component commanders. COCOM includes the directive authority for logistics.
OPERATIONAL CONTROL
B-8. The authority to exercise OPCON is exclusively derived from COCOM authority. Forces provided by the Services and attached to a combatant command are typically in an OPCON command relationship. OPCON is the authority to perform those functions of command over subordinate forces involving—
Organizing and employing commands and forces.
Assigning tasks.
Designating objectives.
Giving authoritative direction necessary to accomplish missions.
B-9. OPCON normally includes authority over all aspects of operations and joint training necessary to accomplish missions. It does not include directive authority for logistics or matters of administration, discipline, internal organization, or unit training. OPCON does include the authority to delineate functional responsibilities and operational areas of subordinate JFCs. In two instances, the Secretary of Defense may specify adjustments to accommodate authorities beyond OPCON in an establishing directive: when transferring forces between CCDRs or when transferring members or organizations from the military departments to a combatant command. Adjustments will be coordinated with the participating CCDRs.
TACTICAL CONTROL
B-10. TACON is inherent in OPCON. TACON may be delegated to and exercised by commanders at any echelon at or below the level of combatant command. TACON provides sufficient authority for controlling and directing the application of force or tactical use of combat support assets within the assigned mission or task. TACON does not provide organizational authority or authoritative direction for administrative and logistics support; the commander of the parent unit continues to exercise these authorities unless otherwise specified in the establishing directive.
JOINT SUPPORT RELATIONSHIPS
B-11. Support is a command authority in joint doctrine. A superior commander establishes a supported and supporting relationship between subordinate commanders when one organization should aid, protect, complement, or sustain another force. Designating supporting relationships is important. It conveys priorities to commanders and staffs planning or executing joint operations. Designating a support relationship does not provide authority to organize and employ commands and forces, nor does it include authoritative direction for administrative and logistic support. (See figure B-1 for a depiction of joint command relationships. See table B-1 for a listing of joint doctrine support categories.)
Note. The joint command relationship of ‘Support’ is distinct from Army support relationships. See paragraphs B-23through B-28 for a discussion of Army support relationships.

| Category | Definition |
|---|
| General support | Support given to the supported force as a whole and not to any particular subdivision thereof (JP 3-09.3). |
| Mutual support | That support which units render each other against an enemy, because of their assigned tasks, their position relative to each other and to the enemy, and their inherent capabilities (JP 3-31). |
| Direct support | A mission requiring a force to support another specific force and authorizing it to answer directly to the supported force’s request for assistance (JP 3-09.3). |
| Close support | The action of the supporting force against targets or objectives that are sufficiently near the supported force as to require detailed integration or coordination of the supporting action (JP 3-31). |
B-12. Support is, by design, somewhat vague but very flexible. Establishing authorities ensure both supported and supporting commanders understand the authority of supported commanders. JFCs often establish supported and supporting relationships among components. An Army headquarters designated as the land component may be the supporting force during some campaign phases and the supported force in other phases. A joint support relationship is not used when an Army commander task-organizes Army forces in a supporting role. When task-organized to support another Army force, Army forces use one of four Army support relationships.
OTHER AUTHORITIES
B-13. Some authorities exist outside joint command relationships. These authorities include—
Administrative control.
Coordinating authority.
Direct liaison authorized.
B-14. Administrative control is direction or exercise of authority over subordinate or other organizations in respect to administration and support (JP 1, Volume 2). This includes organization of Service forces, control of resources and equipment, personnel management, unit logistics, individual and unit training, readiness, mobilization, demobilization, discipline, and other matters not included in the operational missions of the subordinate or other organizations.
B-15. Coordinating authority is the authority delegated to a commander or individual for coordinating specific functions or activities involving forces of two or more military departments, two or more joint force components, or two or more forces of the same Service. The commander or individual granted coordinating authority can require consultation between the agencies involved, but that person does not have the authority to compel agreement. In the event that essential agreement cannot be obtained, the matter shall be referred to the appointing authority. Coordinating authority is a consultation relationship, not an authority through which command may be exercised. (See JP 1, Volume 2 for more information on coordinating authority.)
B-16. Direct liaison authorized is that authority granted by a commander (any level) to a subordinate to directly consult or coordinate an action with a command or agency within or outside of the granting command (JP 1, Volume 2). Direct liaison authorized is more applicable to planning than operations, and it always carries with it the requirement of keeping the commander granting direct liaison authorized informed. Direct liaison authorized is a coordination relationship, not an authority through which command may be exercised.
ARMY COMMAND AND SUPPORT RELATIONSHIPS
B-17. Army command relationships are similar but not identical to joint command authorities and relationships. Differences stem from the way Army forces task-organize internally and the need for a system of support relationships between Army forces. Another important difference is the requirement for Army commanders to handle the administrative support requirements that meet the needs of Soldiers. These differences allow for flexible allocation of Army capabilities within various Army echelons.
ARMY COMMAND RELATIONSHIPS
B-18. Table B-2 lists the Army command relationships and authorities typically associated with each. Command relationships define superior and subordinate relationships between units. The type of command relationship often relates to the expected longevity of the relationship between the headquarters involved, and it quickly identifies the degrees of operational and administrative control that the gaining and losing Army commanders provide. Army command relationships include:
Organic.
Assigned.
Attached.
OPCON. (See paragraphs B-8 and B-9.)
TACON. (See paragraph B-10.)
If relationship is — Then the inherent responsibilities are: | Have command relationship with — | May be task-organized by — | Unless modified, ADCON responsibility goes through — | Are assigned position or AO by — | Provide liaison to — | Establish / maintain communications with — | Have priorities established by — | Authorities CDR can impose on gaining unit further command or support relationship of — |
|---|
| Organic | Organic HQ | Organic HQ | Organic HQ | Organic HQ | N/A | N/A | Organic HQ | Attached; OPCON; TACON; GS; GSR; R; DS |
| Assigned | Gaining HQ | Gaining HQ | Gaining HQ | Gaining HQ | N/A | N/A | Gaining HQ | Attached; OPCON; TACON; GS; GSR; R; DS |
| Attached | Gaining HQ | Gaining HQ | Gaining HQ | Gaining HQ | As required by gaining HQ | Unit to which attached | Gaining HQ | Attached; OPCON; TACON; GS; GSR; R; DS |
| OPCON | Gaining HQ | Parent unit and gaining unit; gaining unit may pass OPCON to lower HQ | Parent HQ | Gaining HQ | As required by gaining HQ | As required by gaining HQ and parent HQ | Gaining HQ | OPCON; TACON; GS; GSR; R; DS |
| TACON | Gaining HQ | Parent HQ | Parent HQ | Gaining HQ | As required by gaining HQ | As required by gaining unit and parent HQ | Gaining HQ | TACON; GS GSR; R; DS |
ADCON administrative control
ASCC Army Service component command
AO area of operations
CDR commander
DS direct support
GS general support
GSR general support—reinforcing
HQ headquarters
N/A not applicable
OPCON operational control
R reinforcing
TACON tactical control
B-19. Organic forces are those assigned to and forming an essential part of a military organization. For example, a brigade engineer battalion is an organic unit in a brigade combat team (BCT). The Army establishes organic command relationships through organizational documents such as tables of organization and equipment and tables of distribution and allowances. If temporarily task-organized with another headquarters, organic units return to the control of their organic headquarters after completing the mission.
B-20. Army assigned units remain subordinate to the higher echelon headquarters for extended periods, typically years. Assignment is based on the needs of the Army, and it is formalized by orders rather than organizational documents. Although force tailoring or task-organizing may temporarily detach units, they eventually return to either their headquarters of assignment or their organic headquarters. An Army headquarters is typically responsible for executing the ADCON responsibilities for subordinate Army units under its command unless modified by a higher headquarters.
B-21. Attached units are temporarily subordinated to the gaining headquarters, often for months or longer. They return to their parent headquarters (assigned or organic) when the reason for the attachment ends. The Army headquarters that receives another Army unit through assignment or attachment assumes responsibility for certain ADCON requirements, and particularly sustainment, that normally extend down to that echelon, as specified by directives or orders. For example, when an Army division commander attaches an air defense battery to a BCT, the brigade commander assumes responsibility for unit training, maintenance, resupply, and unit-level reporting for that battalion.
B-22. Army commanders normally place a unit OPCON or TACON to a gaining headquarters for a given mission, lasting perhaps a few days. OPCON lets the gaining commander task-organize and direct forces. TACON does not let the gaining commander task-organize the unit. Neither OPCON nor TACON affects ADCON responsibilities.
ARMY SUPPORT RELATIONSHIPS
B-23. Table B-3 lists Army support relationships. Army support relationships are not a command authority and are more specific than the joint support relationships. Commanders establish support relationships when subordination of one unit to another is inappropriate. If a unit has an established command relationship with a headquarters, a support relationship is unnecessary as the command relationship already grants the gaining commander all the authorities required. Commanders assign a support relationship when—
The support is more effective if a commander with the requisite technical and tactical expertise controls the supporting unit, rather than the supported commander.
The echelon of the supporting unit is the same as or higher than that of the supported unit. For example, the supporting unit may be a brigade, and the supported unit may be a battalion. It would be inappropriate for the brigade to be subordinated to the battalion, hence the use of an Army support relationship.
The supporting unit supports several units simultaneously. The requirement to set support priorities to allocate resources to supported units exists. Assigning support relationships is one aspect of command and control (C2).
B-24. Army support relationships allow supporting commanders to employ their units’ capabilities to achieve results required by supported commanders. Support relationships are graduated from an exclusive supported and supporting relationship between two units—as in direct support—to a broad level of support extended to all units under the control of the higher echelon headquarters—as in general support. Support relationships do not alter ADCON. Any transfer of ADCON responsibilities should be specified in the order establishing the support relationship.
If relationship is — Then the inherent responsibilities are: | Have command relationship with — | May be task-organized by — | Receives sustainment from — | Are assigned position or an area of operations by — | Provide liaison to — | Establish / maintain communications with — | Have priorities established by — | Authorities a CDR can impose on gaining unit further command or support relationship by — |
|---|
| Direct support | Parent HQ | Parent HQ | Parent HQ | Supported HQ | Supported HQ | Parent HQ; supported HQ | Supported HQ | See note. |
| Reinforcing | Parent HQ | Parent HQ | Parent HQ | Reinforced HQ | Reinforced HQ | Parent HQ; reinforced HQ | Reinforced HQ; then parent HQ | Not applicable |
| General support–reinforcing | Parent HQ | Parent HQ | Parent HQ | Parent HQ | Reinforced HQ and as required by parent HQ | Reinforced HQ and as required by parent HQ | Parent HQ; then reinforced HQ | Not applicable |
| General support | Parent HQ | Parent HQ | Parent HQ | Parent HQ | As required by parent HQ | As required by parent HQ | Parent HQ | Not applicable |
Note. Commanders of units in direct support may further assign support relationships between their subordinate units and elements of the supported unit after coordination with the supported commander
CDR commander
HQ headquarters
B-25. For the Army, direct support is a support relationship requiring a force to support another specific force and authorizing it to answer directly to the supported force’s request for assistance. A unit assigned a direct support relationship retains its command relationship with its parent unit, but it is positioned by and has priorities of support established by the supported unit. (Joint doctrine considers direct support a mission rather than a support relationship.) A field artillery unit in direct support of a maneuver unit is concerned primarily with the fire support needs of only that unit. The commander of a unit in direct support recommends position areas and coordinates for movement clearances where the unit can best support the maneuver commander’s concept of the operation.
B-26. General support is that support given to the supported force as a whole and not to any particular subdivision thereof. Units assigned a general support relationship are positioned and have priorities established by their parent unit. A field artillery unit assigned in general support of a force has all of its fires under the immediate control of the supported commander or his designated force field artillery headquarters.
B-27. Reinforcing is a support relationship requiring a force to support another supporting unit. Only like units (for example, artillery to artillery) can be given a reinforcing mission. A unit assigned a reinforcing support relationship retains its command relationship with its parent unit, but it is positioned by the reinforced unit. A unit that is reinforcing has priorities of support established by the reinforced unit, then the parent unit. For example, when a direct support field artillery battalion requires more fires to meet maneuver force requirements, another field artillery battalion may be directed to reinforce the direct support battalion.
B-28. General support—reinforcing is a support relationship assigned to a unit to support the force as a whole and to reinforce another similar type unit. A unit assigned a general support—reinforcing support relationship is positioned and has its priorities established by its parent unit and secondly by the reinforced unit. For example, an artillery unit that has a general support—reinforcing relationship supports the force as a whole and provides reinforcing fires for other artillery units.
OTHER RELATIONSHIPS
B-29. Several other relationships established by higher echelon headquarters exist with units that are not in command or support relationships. These relationships are limited or specialized to a greater degree than the command and support relationships, and they may be detailed in a command’s implementing directives. These limited relationships are not used when tailoring or task-organizing Army forces. Use of these specialized relationships helps clarify certain aspects of OPCON or ADCON. (See table B-4 for a listing of other relationships.)
| Relationship | Operational use | Established by | Authority and limitations |
|---|
| TRO | TRO is an authority exercised by a combatant commander over assigned RC forces not on active duty. Through TRO, CCDRs shape RC training and readiness. Upon mobilization of the RC forces, TRO is no longer applicable. | The CCDR identified in the “Forces for Unified Commands” memorandum. The CCDR normally delegates TRO to the ASCC. | TRO allows the CCDR to provide guidance on operational requirements and training priorities, review readiness reports, and review mobilization plans for RC forces. TRO is not a command relationship. ARNG forces remain under the command and control of their respective State Adjutant Generals until mobilized for Federal service. USAR forces remain under the command and control of the CG, USARC until mobilized. |
| TRA | TRA is an authority for a designated commander to give direction to an attached unit for leader development, individual and collective training, and unit readiness. | Higher commander. | TRA includes responsibility for all facets of command that enable commanders to accomplish their mission. It does not include those installation command authorities vested in the Army Senior Commander. |
| DIRLAUTH Note. See also paragraph B-16 | Allows planning and direct collaboration between two units assigned to different commands, often based on anticipated tailoring and task organization changes | The parent unit headquarters. This is a coordination relationship, not an authority through which command may be exercised. | Limited to planning and coordination between units. |
| Aligned | Informal relationship to facilitate planning between a theater army and other Army units identified in operations and exercises in a specific combatant command. | Theater army and parent command. | Normally establishes information channels for coordination between the gaining theater army and Army units that are likely to be committed to that area of responsibility. |
ASCC Army Service component command
ARNG Army National Guard
CCDR combatant commander
CG commanding general
DIRLAUTH direct liaison authorized
RC Reserve Component
TRO training and readiness oversight
USAR United States Army Reserve
USARC United States Army Reserve Command
B-30. Training and readiness oversight (known as TRO) is the authority that CCDRs may exercise over assigned Reserve Component forces when not on active duty or when on active duty for training. As a matter of Department of Defense policy, this authority includes—
Providing guidance to Service component commanders on operational requirements and priorities to be addressed in military department training and readiness programs.
Commenting on Service component program recommendations and budget requests.
Coordinating and approving participation by assigned Reserve Component forces in joint exercises and other joint training when on active duty for training or performing inactive duty for training.
Obtaining and reviewing readiness and inspection reports on assigned Reserve Component forces.
Coordinating and reviewing mobilization plans (including post-mobilization training activities and deployability validation procedures) developed for assigned Reserve Component forces.
(See JP 1, Volume 2 for more information on training and readiness oversight.)
B-31. Training and readiness authority (known as TRA) is the discrete authority, granted by a higher echelon commander, for a designated commander to give direction to an attached unit for leader development, individual and collective training, and unit readiness (to include maintenance, manning, and equipping). It also includes responsibility for the health, welfare, morale, and discipline of assigned and attached personnel, and all facets of command that enable unit commanders to accomplish their missions. It does not include those installation command authorities vested in the Army senior commander. The commander executing training and readiness authority has a responsibility to coordinate unit readiness with the applicable installation Army senior commander.
B-32. Alignment is an informal relationship between a theater army and other Army units identified for use in the area of responsibility of a specific geographic combatant command. Alignment helps focus unit exercises and other training on a particular region. This may lead to establishment of direct liaison authorized between the aligned unit and a different ASCC. Any modular Army force may find itself included in an expeditionary force package heading to a different combatant command. Therefore, Army commanders maintain a balance between regional focus and global capability.
MULTINATIONAL COMMAND AND SUPPORT CONSIDERATIONS
B-33. Army forces routinely serve in multinational operations, and echelons above brigade headquarters may form the core of a multinational headquarters. As such, it is important that Army commanders and staffs understand multinational command structures and authorities.
B-34. Multinational operations is a collective term to describe military actions conducted by forces of two or more nations, usually undertaken within the structure of the coalition or alliance. An alliance is the relationship that results from a formal agreement between two or more nations for broad, long-term objectives that further the common interests of the members. Alliances have standing headquarters, organizations, and standardized agreements for the conduct of operations. Examples include NATO and the Combined Forces Command, Korea. Operations conducted with units from two or more allies are referred to as combined operations.
B-35. A coalition is an ad hoc arrangement between two or more nations for a common action, and a coalition is formed for a limited purpose and time. Coalitions are formed by different nations with specific objectives, usually for a single occasion or for longer cooperation in a narrow sector of common interest. Operations conducted with units from two or more coalition members are referred to as coalition operations. (See FM 3-16 for further details on multinational operations.)
COMMAND AUTHORITY
B-36. The Army and joint force have doctrinal definitions for command and support relationships. However, these definitions and authorities only apply to U.S. forces. In multinational operations, each nation determines the authority it will delegate to multinational commanders for the employment of their forces. The nations involved also establish national caveats. Command authority for a multinational force’s command is normally negotiated between the participating nations, and it can vary from nation to nation. Command authority is specified in the implementing agreements, and it may include aspects of OPCON, TACON, support relationships, and coordinating authority. A clear and common understanding of what authorities are specified in the implementing agreement is essential to operations. This is particularly important when similar terms have different meanings to the various participants.
B-37. In many cases, coordinating authority may be the only acceptable means of accomplishing a multinational mission. Coordinating authority is a consultation relationship between commanders, not an authority by which C2 may be exercised. Normally, it is more applicable to planning than to operations. Use of coordinating authority requires agreement among participants, as the commander exercising coordinating authority does not have the authority to resolve disputes.
MULTINATIONAL COMMAND STRUCTURE
B-38. All multinational operations have two chains of command regardless of structure or authority. The first is a national chain of command extending back to national capitals. The second is the multinational chain of command constructed by the United Nations, alliance, or coalition. As unity of command is all but impossible given parallel national chains of command, multinational commanders strive for unity of effort. In doing so, multinational commanders develop a high level of mutual trust and comfort with other national contingents.
B-39. United Nations forces, alliances, and coalitions create command structures that meet the needs, diplomatic realities, constraints, and objectives of the participating nations. No single command structure fits the needs of all alliances, United Nations forces, and coalitions; however, the basic structures for multinational operations fall into one of four types:
Integrated.
Lead nation.
Parallel.
Combination
B-40. Regardless of how a multinational force is organized operationally, each nation furnishing forces normally establishes a national component, often called a national command element, to ensure effective administration of its forces. The logistic support element of this component is referred to as the national support element.
B-41. Integrated commands have representative members from the member nations in the command headquarters. Multinational commands organized under an integrated command help ensure the capabilities of member nations are represented and employed properly.
B-42. A lead nation command structure exists when all member nations place their forces under the control of one nation. The lead nation command can be distinguished by a dominant lead nation command and staff arrangement with subordinate elements retaining strict national integrity.
B-43. Under a parallel command structure, no single force commander is designated. The multinational force leaders must develop a means for coordination among the participants to attain unity of effort. This can be accomplished through the use of coordination centers. Nonetheless, because of the absence of a single multinational force command, the use of a parallel command structure should be avoided if possible.
B-44. In a combination command structure, the lead nation concept and a parallel command structure exist simultaneously in a coalition. This occurs when two or more nations are the controlling elements for a mix of international forces. This structure is more desirable than the parallel command structure, but an effort to achieve a total lead-nation concept for unity of command is preferred.
NORTH ATLANTIC TREATY ORGANIZATION COMMAND RELATIONSHIPS AND AUTHORITIES
B-45. NATO is an example of a multinational organization with agreed upon structure and authorities. When planning and conducting operations as part of NATO, it is particularly important for leaders to understand the command relationships and the specified authorities, whether they are attached to a NATO command or receiving NATO capabilities. It is also important to understand that NATO terms and acronyms are similar to U.S. acronyms at times, but they often describe different authorities than joint and Army terms. NATO has five command relationships:
Full command (FULLCOM).
Operational command (OPCOM).
OPCON.
Tactical command (TACOM).
TACON.
(See table B-5 on page B-12 for a listing of NATO treaty organization command relationships. See Allied Tactical Publication 3.2.2 and AJP-3 for additional discussion of the authorities for each command relationship.)
<< More authority
Less authority >>
| Authority | FULLCOM | OPCOM | OPCON | TACOM | TACON |
|---|
| May further delegate command authority | OPCOM OPCON TACOM TACON | OPCOM OPCON TACOM TACON | OPCON TACOM TACON | TACOM TACON | TACON |
| Task-organize the assigned element | X | X | |||
| Assign missions to the assigned element | X | X | X (limited) | ||
| Assign tasks to the assigned element for the purpose of which it has been assigned | X | X | X | X (limited) | |
| Coordinate movement, local defense, and force protection | X | X | X | X | X |
| Planning and coordination | X | X | X | X | X |
| Administrative and logistic responsibility | X |
B-46. FULLCOM is the military authority and responsibility of a commander to issue orders to subordinates. It covers every aspect of military operations and administration and exists only within national services. The term command, as used internationally, implies a lesser degree of authority than when it is used in the national sense. NATO or coalition commanders do not have FULLCOM over the forces assigned to them, since, in assigning forces to NATO, nations delegate only OPCOM or OPCON.
B-47. OPCOM in NATO is the authority granted to a commander to assign missions or tasks to subordinate commanders, to deploy units, to reassign forces, and to retain or delegate OPCON and TACON as the commander deems necessary. It does not necessarily include responsibility for administration or logistics.
B-48. OPCON in NATO is the authority delegated to a commander to direct assigned forces so that commander may accomplish specific missions or tasks, which are usually limited by function, time, or location, and to deploy assigned units, and to retain or assign TACON of those units. It does not include authority to assign separate employment of components of the units concerned. By itself, it does not include administrative or logistics control. For forces allocated under OPCON, the gaining commander may not break up the organizational integrity of the force for separate employment. Under OPCON forces assigned may only be employed within certain constraints such as function, time, or location imposed by the higher echelon authority.
B-49. TACOM in NATO is the authority delegated to a commander to assign tasks to forces under that command for the accomplishment of the mission assigned by higher authority. Under TACOM the gaining commander may only allocate to the assigned force a specific task consistent for the accomplishment of the mission and purpose assigned by the higher commander. Under TACOM the assigned force is allocated for specific tasks, and it is normally allocated for a limited period. This prevents the gaining commander from employing the assigned force in a role or manner not intended by the higher commander. When the task is complete or the specific timeframe expires, the TACOM relationship with the gaining force ends.
B-50. TACON in NATO is the detailed and usually local direction and control of movements or maneuvers necessary to accomplish missions or assigned tasks. TACON is generally used to indicate those units that will be located in another unit or formation’s assigned geographic boundaries, where the gaining unit becomes responsible for coordination aspects within the shared AO. The gaining commander has authority to coordinate local defense, including force protection and terrain allocation.
Appendix C - Contested Deployments
This appendix discusses unit considerations for conducting deployment operations contested by a peer threat. It begins with an overview and a discussion of threat capabilities that can affect force projection. It then covers considerations when moving from home station to port of embarkation, when in transit from port of embarkation to port of debarkation, and when conducting reception, staging, onward movement, and integration (RSOI) in a theater of operations. The appendix further expands upon the homeland as a specific operational area where homeland defense and defense support of civil authorities (DSCA) missions will likely be conducted as other units deploy. It concludes with considerations for training and preparation that Army leaders can incorporate into preexisting exercises or conduct as separate events.
FORCE PROJECTION AND THREAT CAPABILITIES
C-1. Army forces cannot expect to deploy without being challenged by the threat. For decades, U.S. military forces conducted uncontested and generally predictable deployments from home stations to operational theaters because threat actors lacked the capability to significantly affect deploying units at home station or while in transit to a theater of operations. This is no longer the case. Peer threats possess the capability and capacity to observe, disrupt, delay, and attack U.S. forces at any stage of force projection, including while still positioned at home stations in the United States and overseas. Commanders and staffs must therefore plan and execute deployments with the assumption that friendly forces are always under observation and in contact.
C-2. A peer threat’s ability to impact U.S. military operations prior to arrival in an operational area extends beyond directly targeting unit personnel and equipment. The Army relies on various interdependent infrastructures, the majority of which it does not own or operate, making its domestic operations heavily reliant on external resources. This includes the use of civilian transportation infrastructure to move from installations to ports of embarkation, and it also includes home station military dependencies on civilian infrastructure for power, communications, fuel, water, and other life support.
C-3. During armed conflict, Army forces should expect deployments to be contested by enemy actions in all domains. Army forces will require greater emphasis on protection functions to conserve combat power and should expect to provide forces to support homeland defense and DSCA operations. Defending U.S. territory against attacks by state and non-state actors through an active, layered defense while simultaneously seeking to project forces in a conflict with a peer enemy requires coordination across organizations, agencies, and jurisdictions at the local, state, and federal levels.
C-4. Threat actions to contest a deployment are most visible during crisis and armed conflict, but they can also occur during competition. Army forces deploy globally as part of operations during competition to meet national objectives, assure allies and partners, and deter adversary malign actions. Adversary abilities to disrupt these deployments create risks that leaders must assess and mitigate during movement planning and execution. While a conventional attack on U.S. forces conducting operations during competition is unlikely, the greater the perceived danger to their vital national interests, the greater the chance a peer threat will contest U.S. military force projection. Leaders account for this intensified risk during planning and conduct training to improve their units’ resilience and ability to mitigate risk, coordinate with appropriate partner organizations, and respond effectively.
C-5. While a threat’s use of lethal capabilities to target the U.S. homeland or deploying forces is unlikely before a crisis or the commencement of armed conflict, it may choose to use other methods to surveil and disrupt Army forces during competition. Russia, China, and other threats possess wide-ranging capabilities to conduct cyberspace attacks, disrupt space capabilities, and conduct information warfare to influence the perceptions and behavior of target audiences. Attribution for these malign activities is challenging. Adversaries take steps to deliberately obscure the source of these activities, and they take full advantage of the ambiguity provided by operating below the threshold of armed response. Cyberspace attacks can be used to compromise government, private sector, and military capabilities, potentially targeting military dependencies on civilian infrastructure. Disruption of space capabilities can be used to hamper communication and navigation capabilities of both military forces and the civilian infrastructure they rely upon. Information warfare, including dissemination of or support for disinformation and misinformation, can be used to attempt to fracture bonds among elements of society. This may include seeking to create or exacerbate divisions between the military, government, private sector, and the public, both nationally and in local municipalities.
C-6. Peer threats use a variety of means to understand and predict U.S. and allied force projection, including open source and cyberspace collection. Army leaders should understand threat collection capabilities to reduce the chance of effective detection. Different ways threat forces are able to collect on a division’s deployment are described in this notional scenario.
A division has received prepare to deploy orders. Division leaders considered this deployment routine, and they failed to address operations security or force protection at home station during the planning process. As a result, threat forces are able to understand many details of the pending deployment through open-source and cyberspace collection.
Threat intelligence agencies read aircraft tail numbers arriving and departing from air bases that typically support division operations, analyzing observations posted by hobbyists to assess likely missions and cargo. They also analyze publicly available movement contracts for taking unit equipment from fort to port. Increased availability of rental residences near the installation indicates that Soldiers are invoking deployment clauses in their leases, and decreased availability of personal storage units indicates Soldiers are storing their belongings for a deployment. Commercially available applications and databases that track food ordering, cell phone presence and activity, and other data are used to show a continued staff presence after normal business hours at the division headquarters.
As the deployment gets closer, Soldier and family member social media posts increase in volume and provide information about upcoming deployment timelines and locations. Threat agents go through financial transactions and credit card data stored on accessible servers to better understand specific unit and key leader timelines and vulnerabilities. Threat agents also comb through Soldier and family member personal data collected as part of application and device user agreements. Some of this data, normally sold for advertising purposes, was purchased through shell companies on the open market. Other credit, banking, and identity data was illegally obtained on the dark web or through other illicit methods.
C-7. Threat forces will conduct information warfare operations to slow or otherwise degrade force projection. These campaigns can vary in scope and size, and may target local communities, Service members, Department of Defense (DOD) Civilians, contractors, and Soldiers’ family members. This includes, but is not limited to—
Targeted threats through social media, email, or other means designed to frighten and distract deploying Soldiers and their families.
Cyberspace attacks against Soldier and family member banks and credit agencies, cutting off or disrupting access to personal funds.
Cyberspace attacks against civilian infrastructure (including transportation, supply, fuel, and navigation) used to support military operations.
Targeted strikes against defense communications infrastructure to disrupt communications between units, installations, and other unified action partners that assist in deployment.
Disinformation dissemination and misinformation support designed to—
Undermine the legitimacy of, or otherwise reduce support for, U.S. Government action.
Incite civil unrest in local communities and along rail and road lines of communications that deploying forces need or plan to use to reach ports of embarkation.
Reduce trust in future official communications, from government, law enforcement, or military officials, by releasing disinformation that appears genuine but contains incorrect or confusing information.
C-8. Threat information warfare operations can be conducted at a very low cost compared to conventional warfare methods, and they have global reach. At low levels, they can be used to hamper military deployments. With sufficient scale or precision, they have the potential to completely halt effective unit deployment operations. Targeted disinformation and threats delivered via social media to the family members of every Soldier in a unit could potentially be devastating without prior planning, preparation, and trust building.
C-9. Commanders and their staffs must understand the potential effects of adversarial disinformation operations on units and leaders. Targeted adversary or enemy activities in the information dimension could rapidly degrade the performance of Soldiers, impacting their readiness. It could also degrade civilian performance and affect the critical infrastructure they manage. Leaders combat this through public communications both prior to and during deployment operations, coordination with relevant public affairs personnel, and Service member and family preparation. This preparation can include incorporating response strategies for disinformation dissemination into exercises and other training.
C-10. As U.S. forces transition from competition to crisis or armed conflict, threat actors will increase the intensity and lethality of their tactics. This could include infrastructure sabotage by pre-positioned agents, cyber or information attacks broader in scope (such as targeting an oil pipeline supplying a large region rather than only a specific port), or long-range precision strikes using a variety of munitions. Concurrently, they posture for, and may eventually escalate through, nonlethal and lethal actions of increasing intensity to improve stand-off and prevent power projection from the U.S. homeland and other basing and staging areas. Threat actors may also strike transport vessels along sea lines of communication while these vessels are en route to a seaport of debarkation.
C-11. Peer threats may choose to support proxy forces or influence unwitting groups, including irregular forces, saboteurs, sympathetic civil organizations, and criminals. These groups may be used to prevent timely deployment operations by denying access to roads or facilities with crowds, protests, or looting. Use of these forces may also allow for direct action against U.S. targets while masking culpability. Threat actors may design these activities to affect the economy and global trade in addition to the political-military balance in the United States or overseas. Additionally, other state and non-state actors may exploit the situation with attacks in pursuit of their own objectives. These attacks may be conducted within the United States or allied nations, in the theater into which Army forces are preparing to deploy, or in other, unrelated regions.
C-12. Leaders anticipate adversary activities in all domains while preparing for or conducting deployment operations. Disruptions may not be preventable. They can, however, be mitigated through training, preparation, and coordination with unified action partners. Effective mitigation in planning, preparation, and execution ensures the Army provides the required forces to combatant commanders (CCDRs) and other joint force commanders (JFCs). (See AR 525-93 for Army deployment policies and responsibilities.)
FORT TO PORT
C-13. As part of the strategic support area, home station installations, Reserve Centers, National Guard Armories, and other designated points of origin are where force projection begins. They present targets that enemy forces may attack to delay, disrupt, and degrade force flow into theater. Additional vulnerabilities are present along all routes of movement, and at all potential sea and aerial ports of embarkation. Army forces at all echelons must comprehensively assess emerging threat capabilities that will impede deployment in a contested environment. To the greatest extent possible, formations should account for being under constant observation through strict operations security, including the safeguarding of information on specific deployment timelines and locations and maintaining dispersion of critical assets. The effects of attacks on critical military, national, or private infrastructure could halt or delay unit deployment operations before units have departed the United States.
C-14. Contested deployments are a national issue, and they require coordination with a large number of civilian unified action partners to overcome the challenges peer threats can create. However, moving Army forces from military installations to ports of embarkation is also a local and regional challenge. When routine deployment is not possible, installations and units should have a plan to mitigate deployment disruptions.
C-15. Deployment disruption mitigation planning requires collaboration between the deploying unit, the installation, appropriate federal, state, and local agencies (both government and law enforcement), and U.S. Army Reserve and National Guard elements. Installations are responsible for building these relationships and understanding how threats will likely affect their local areas. Installations do this by modifying their threat working groups to incorporate relevant military, government, and other local and regional stakeholders. The working group shares information about threats that promote civil unrest, cyber threats that impact critical transportation infrastructure, and other threat activities that impact deployment operations. Key planning and training considerations are—
The local, state, and federal authorities able to mitigate deployment disruptions.
Coordination and relationship building with local, state, and federal civilian law enforcement agencies to ensure effective movement control from fort to port.
Understanding about critical infrastructure vulnerable to sabotage and unsuited for the movement of heavy equipment along surface lines of communication, both road and rail.
Planning to use alternate railheads and marshalling yards and multiple lines of communication to reach ports of embarkation.
Developing alternate surface transportation options to deliver unit equipment to a sea port of embarkation when rail service is degraded or disrupted.
Establishment of fuel, maintenance, and rest locations along lines of communications.
Implementation of a communication plan that informs the public while maintaining operations security.
Establishing specific cyber defenses for systems and associated data used to support movement.
C-16. Having an understanding of the requirements and developing mitigation plans to move from the installation to the assigned port of embarkation can help overcome threat activities that could stop or hinder deployments. An example of this is using Army heavy equipment transportation systems (known as HETS) to move tanks, using contract carriers to move other tracked vehicles, and convoying wheeled vehicles to a seaport of embarkation if rail transportation from the installation is degraded or disrupted.
C-17. To effectively implement a mitigation plan, deploying units and the installation must have an understanding of the capabilities of civilian infrastructure (such as weight limitations on routes from the installation to the port). This includes using data from, and potentially requires coordination with, the Military Surface Deployment and Distribution Command about rail lines and roads designated as part of the strategic rail and highway corridor networks. Planners must consider the security of critical nodes and terrain along projected routes and conduct prior coordination with local and state authorities for security. Existing adversary capabilities that could be used to target civilian infrastructure were exercised during EXERCISE JACK VOLTAIC 3.0, conducted in 2020.
Exercises and research projects provide insight into how peer threats could disrupt the deployment of Army forces by targeting civilian infrastructure. In the Army Cyber Institute’s EXERCISE JACK VOLTAIC 3.0, military, interagency, municipal, state, and commercial partners collaborated to assess interdependencies and available actions by different stakeholders in response to such targeting.
During the scenario, the movement of military equipment was disrupted by a combination of traffic delays; social media-incited protests; port access manipulation; the manipulation of rail and vessel cargo manifests; natural gas and electrical disruptions; and, ultimately, interference with the weight distribution for the automated load plan for a ship in port (causing it to tip and dump containers into the shipping channel).
None of the measures, taken individually, prevented movement of unit equipment from reaching the destination by the required delivery date. Taken together, however, the actions caused cascading effects that challenged Army unit and installation leaders, port officials, and state and municipal government and law enforcement personnel.
C-18. Units establish and maintain an accurate common operational picture (COP) when subordinate or supported units and equipment are en route to ports of embarkation. This includes maintaining visibility of friendly forces and potential threat actions. It also encompasses awareness of partner civilian and military entities supporting the deployment, including law enforcement, mobilized reserve component units, and air and rail activities.
C-19. Deploying units and installations coordinate with agencies at ports of embarkation to take action should an adversary’s efforts impact deployment operations. This coordination can help Army forces rapidly adjust to emerging circumstances. Unit and installation personnel that manage deployments must rapidly develop new transportation plans if needed, using previously developed branch plans as a start point.
C-20. When load planning, Army leaders and staffs must work with transportation authorities to ensure sufficient enabling forces are paired with combat arms forces during transit. Army leaders, working with transportation officials, develop methods to effectively load combat-configured forces in a manner that maximizes available deck space on the transport vessel while making these units operationally relevant upon arrival. Generally, it is desirable for tactical units to be configured as company teams or battalion task forces with the requisite supporting enablers to allow immediate employment.
C-21. In most circumstances when threat actions have not significantly degraded port operations, the port support activity stevedores load Army equipment once it arrives at the port of embarkation for transport to the operational theater. In these circumstances, Army forces effectively lose physical control of this equipment until it arrives in theater. Prior to departure for the port, Army forces coordinate with transportation and port officials to ensure that unit containers, rolling stock, and other unit equipment sets are loaded in ways to balance requirements for transport efficiency, combat readiness upon offloading, and risk to readiness if a transport vessel or craft is destroyed en route.
PORT TO PORT
C-22. Ports of embarkation in the strategic support area, whether in the United States or overseas, are likely targets of cyberspace attack, space capability degradation or denial, and other impacts designed to reduce capabilities or capacity as U.S. forces conduct deployment operations into other theaters. During armed conflict, enemy forces have the range and capacity to target ports with long-range fires, special operations forces, and other capabilities.
C-23. Port authorities open, close, and manage port operations based on their pre-existing requirements, not based on what is necessarily most advantageous to a given unit’s deployment requirements. This might include requirements for other Army forces, the joint force, or other government or commercial entities designated as priorities for a period of time. Early, frequent, and detailed coordination with port authorities helps mitigate potential disruptions to deployment operations. Installations and units incorporate port officials into deployment readiness exercises and other training events to improve mutual understanding and effectiveness.
C-24. Adversary actions may directly or indirectly cause port officials to close their port or reduce operations. If this occurs, and if authority is granted to use another port, commanders consider the impacts to both their unit and the broader military effort, and to civilian requirements, before recommending or deciding to move assets to another port of embarkation. Port operations conducted by other government agencies or civilian officials may take priority over those that Army forces need to conduct based on current local, state, or national requirements. Additionally, other ports may become congested or disrupted by the time Army forces arrive. Adhering to the original plan while adapting to challenges at the port is generally less disruptive to the overall deployment effort than moving to another port.
C-25. Depending on the level of conflict and assessed threat to their interests, peer enemies may attempt to disrupt or destroy unit equipment while in transit. If all of a unit’s equipment is placed on one transport this could lead to the catastrophic loss of land component capability for the JFC. Spreading unit equipment across multiple transport ships increases the likelihood that some will arrive and be available for employment. While this is not the most efficient or expeditious method to transport Army equipment, it helps ensure that the JFC receives some employable level of Army tactical and operational capability.
C-26. During armed conflict, Army forces conduct additional protection activities based on enemy capabilities. Effective targeting by enemy lethal and nonlethal effects will drive protection and mitigation actions for unit personnel and equipment. Army forces maybe called on to provide additional protection capabilities to support port authorities. Unit commanders and staffs should balance protection requirements, both at the port and in-transit, against requirements to get as many critical capabilities to the required operational theater as quickly as possible and requirements to have combat-ready units arrive at ports of debarkation for employment by JFCs.
C-27. Whether conducting operations at a port during competition, crisis, or armed conflict, Army forces coordinate with the relevant authorities to mitigate potential complications at the port. This includes—
Coordinating for products that provide a general layout of the port and flow of port operations.
Obtaining an understanding of transport ship loading.
Understanding port authority structure and decision making.
Understanding reliance of the port on local infrastructure to conduct operations and identifying potential redundancies (for example, if power is lost can port gantry cranes load containers).
Planning to train Soldiers on port equipment, such as material handling equipment.
C-28. Additional considerations for port-to-port transport are the use of unit personnel to improve, monitor, and maintain equipment readiness while in transit. Units should anticipate execution of vehicle maintenance at the port, and leaders may place a limited number of unit personnel on a transport vessel to ensure enabling and combat arms equipment is ready for immediate employment upon arrival in theater.
RSOI DURING CONTESTED DEPLOYMENTS
C-29. Historically, even during armed conflict, Army forces enjoyed high degrees of sanctuary in rear areas to receive and organize forces before moving them forward. However, the long-range strike capabilities of peer adversaries mean that sanctuary to conduct unimpeded RSOI operations in rear areas can no longer be assumed. It is likely that strikes by peer threats will degrade or destroy port and other transportation infrastructure vital to U.S force projection. This could cause Army forces to arrive in a disaggregated manner and disrupt RSOI operations. While integrating U.S. forces in theater could be challenging, Army planners must also consider host-nation requirements for logistics infrastructure. The host nation’s response to an attack on its infrastructure, including its military mobilization, can affect freedom of movement for U.S. forces. All of these challenges may require JFCs to alter their operational plans or stay in a defensive posture for an extended period until sufficient combat power is built to enable offensive operations.
C-30. The theater army has primary responsibility for conducting RSOI for the entire joint land force. Army equipment may arrive in a piecemeal fashion across numerous ports. Commanders must establish secure communications across the distributed footprint, which allows staff coordination for unit personnel to meet their equipment and facilitate ship offloading. Units provide port support teams with the right personnel and capabilities to expedite port operations, such as licensed vehicle operators and communications. This helps ensure ports of debarkation are not congested with disabled equipment or frustrated cargo. If some unit equipment is lost in transit due to destruction of transport vessels, some tactical unit personnel may be temporarily held at theater facilities to facilitate re-equipping efforts or be otherwise retasked by the combatant command or theater army commander.
C-31. If ports are unavailable, are severely degraded, or do not have the draft required for deep draft strategic sealift vessels, the JFC may consider joint logistics over-the-shore (JLOTS) operations. JLOTS provides the JFC with a limited capability to discharge strategic sealift ships. JLOTS requires a significant amount of lead time to build the needed conditions for successful operations, and it entails significant risk that strategic leaders will need to balance against its potential benefits. (See Chapter 6 of this publication or JP 4-01.6 for more information on JLOTS.)
C-32. After reception is complete, staging occurs. Staging during force projection contested by a peer threat requires understanding of threat standoff and friendly protection capabilities. Units must disperse and seek concealment to improve survivability. Operation plans (OPLANs) should take into account the need for expanded assembly areas to increase distances between vehicles and between unit assembly areas. As deploying units assemble, efforts focus on preparing for future operations and integrating into the joint force. Theater-specific training requirements may need to be conducted while afloat or at home station prior to movement to the theater to minimize staging timelines.
C-33. Onward movement during contested deployments requires units to execute movement and sustainment along multiple, dispersed routes. Road, rail, and other lines of communication must be assessed and classified for use by arriving forces. Units can avoid aggregation, enhance survivability, and achieve balance by directing personnel, equipment, materiel, and information flow at a rate that can be accommodated at every point along the entire network, from origin to destination. Key to the onward movement process is speed of movement to rapidly get combat power to the operational area for employment.
C-34. To facilitate rapid onward movement and overcome the likely degradation of Global Positioning System (known as GPS) and other enabling transportation technology, units conduct convoy briefs, have paper maps, and conduct detailed route planning. This helps prepare Soldiers for the unique considerations of the host-nation transportation infrastructure, and it mitigates vulnerability to threat attacks. Theater-level personnel may augment or conduct separate briefings to share information about current conditions and threat tactics.
C-35. RSOI concludes with integration. Effective and efficient integration operations can reduce force vulnerability by ensuring units quickly assess vulnerabilities and counter potential threats to forces, infrastructure, and information systems as they transfer capabilities to an operational commander’s force. When forces are fully integrated, operational control (OPCON) is transferred to the gaining unit. (See Chapter 4 and ATP 3-35 for additional information on RSOI operations.)
HOMELAND DEFENSE AND DEFENSE SUPPORT OF CIVIL AUTHORITIES
C-36. While Army forces are preparing to deploy during crisis response or armed conflict against a peer threat, other units may be tasked to support homeland defense or DSCA. The circumstances that lead to national authorities directing the deployment of Army forces may also necessitate operations to simultaneously defend the U.S. homeland or support civil authorities. Additionally, the act of deploying forces may incite enemy attacks on the homeland, causing some forces to be mobilized for homeland defense or DSCA while others deploy forward to the operational theater. Homeland defense is the protection of United States sovereignty, territory, domestic population, and critical infrastructure against external threats and aggression or other threats as directed by the President (JP 3-27). Defense support of civil authorities is support provided by U.S. Federal military forces, DOD Civilians, DOD contract personnel, DOD component assets, and National Guard forces (when the Secretary of Defense, in coordination with the governors of the affected states, elects and requests to use those forces in Title 32, USC status) in response to requests for assistance from civil authorities for domestic emergencies, law enforcement support, and other domestic activities, or from qualifying entities for special events (DODD 3025.18).
C-37. Homeland defense and DSCA operations are conducted in a complex operational environment that contains layers of different jurisdictions (federal, state, territorial, tribal, and local), many agencies and organizations, the private sector, and several allies and multinational partners. Interorganizational coordination and synchronization with governmental and nongovernmental entities may assume a level of importance not matched in most overseas theaters of operations. Within the same city, Army forces may be simultaneously conducting different missions, each with distinct authorities and requirements. This could include adjacent units conducting—
Deployment preparation activities.
Homeland defense missions as directed by U.S. Northern Command or U.S. Indo-Pacific Command.
DSCA in support of the Department of Homeland Security or other organizations.
C-38. Changes in an operational environment based on threat action or other circumstances may cause changes to planned and ongoing operations. Army forces preparing to deploy to another theater may be tasked to support U.S. Army North instead. Additionally, units conducting DSCA may be required to transition to homeland defense, or vice versa. Commanders and staffs must remain agile to ensure they understand the responsibilities and authorities for different missions, remaining in constant contact with other unified action partners to ensure shared understanding. Depending on mission requirements and available personnel, this may include agency representatives, liaison officers, and staff representatives able to collaborate, share information, analyze ongoing activities, and participate in planning.
HOMELAND DEFENSE
C-39. When conducting homeland defense missions, U.S. Army North has been designated to serve as the land component command for U.S. Northern Command. Depending on the threat, defending critical infrastructure and maintaining force projection capability for joint and Army forces will require significant augmentation and cross-command integration. Commercial infrastructure plays a critical role in enabling the communications systems that directly support operations. This infrastructure may be damaged to the point that military and supporting operations are adversely affected.
C-40. Protection functions are essential during any operation, and they take on specific importance during homeland defense. Protection during homeland defense includes measures and activities not only conducted for use by the joint force, but also for commercial, law enforcement, and government partners. These protection functions can be supported through a number of activities. Planning for these operations should include deception, mobility, dispersion, systems resiliency and redundancy, protective construction, warning and surveillance, and operations security. Additional coordination will be required if Army units are tasked to provide these capabilities for government and commercial partners or to build upon existing capabilities so that partners can conduct them themselves.
C-41. Army forces support joint force and national efforts to provide the latest relevant information to the American public while maintaining operations security, and they will also counter disinformation posted on social media and distributed through other means. Timely, relevant, and effective responses are critical to mission accomplishment when a peer threat is using high volumes of disinformation to achieve its objectives. Unit commanders and other leaders follow their supported command’s public affairs guidance and act in a supporting role to local, state, and federal agencies.
DEFENSE SUPPORT OF CIVIL AUTHORITIES
C-42. Army support of civil authorities is vital to enabling other units that are deploying under contested conditions. The range of DSCA responses by Army forces includes support provided by the Regular Army, activated Army Reserve, and the National Guard in Title 32 United States Code (USC) or Title 10 USC status. Even in the absence of orders or in uncertain and chaotic situations, units providing support in the homeland enable core DSCA activities to provide support for domestic disasters, provide support for domestic CBRN incidents, provide support for domestic civilian law enforcement, and provide other designated domestic support. Domestic military operations are constrained by statute and policy to a greater degree than military operations conducted abroad, and units should become familiar with requisite authorities.
C-43. Homeland defense and DSCA operations may also be conducted in a wide range of circumstances not tied to the preparation or execution of force projection to another operational theater. This can include responses to both external and internal threats, natural or manmade disasters, support to law enforcement, and other activities. (See DODD 3025.18, JP 3-27, JP 3-28, and ADP 3-28 for more information on DSCA and homeland defense.)
TRAINING AND PREPARATION CONSIDERATIONS
C-44. Training and preparation to conduct deployment operations contested by threat forces will stress joint and unified action partner interoperability and coordination. The Army and other unified action partners conduct joint deployment exercises whenever possible, develop information and intelligence sharing architectures, and collaborate during other preparation activities. Preparing for a contested deployment, defending the homeland, and executing DSCA operations are not primary considerations for most Army units. However, when preparing for large-scale combat operations, units should augment their training plans to help prepare for deployments contested by threat forces and related activities. Examples include—
Conduct deployment readiness exercises that include port authority, law enforcement, and other stakeholder participation from municipal, state, federal, and commercial organizations.
Conduct a road march to a training center rotation from an Army installation to simulate extended convoy operations and test maintenance capability of Army equipment and personnel.
Conduct tabletop exercises with members of the installation threat working group to discover gaps in planning and build a cohesive team.
Conduct training with local communities to test the ability of the installation and local law enforcement to handle demonstrations that may occur due to misinformation.
Conduct training to improve Soldier and family member awareness of likely threat information warfare actions and potential response strategies.
Coordinate to ensure installation and unit threat working groups, emergency response centers, and cyber security measures are expanded to account for critical civilian dependencies, including reliance on civilian infrastructure.
Establish and test a primary, alternate, contingency, and emergency (known as PACE) communication plan among key Army units, installations, armories, and unified action partners that facilitate deployment operations.
Identify requisite command and logistics nodes along primary and alternate routes to ports of embarkation, across multiple modes of transportation if appropriate.
Prepare numerous road march plans to compensate for degraded or disrupted lines of communications.
Maintain port overview packages for likely ports of embarkation.
Build and implement an installation strategic communication plan that informs the public while maintaining operations security.
Prepare Soldiers and family members for extended periods of no direct connectivity during initial stages of crisis or armed conflict to maintain operations security.
Create plans for direct communication between Army installations and family members during the initial stages of a crisis or armed conflict to help mitigate the effects of threat disinformation and answer family questions.
Ensure ready access to relief funds and supplies for dependents in case of threat attacks against financial institutions.
Work with local, state, and federal law enforcement agencies to build relationships and understand requirements if later tasked to conduct homeland defense or DSCA.
Glossary
The glossary lists acronyms and terms with Army or joint definitions. Where Army and joint definitions differ, (Army) precedes the definition. The proponent publication for terms is listed in parentheses after the definition.
SECTION I – ACRONYMS AND ABBREVIATIONS
A2 antiaccess
AAMDC Army air and missile defense command
AD area denial
ADA air defense artillery
ADCON administrative control
ADP Army doctrine publication
AFTTP Air Force tactics, techniques, and procedures
AJP Allied joint publication
AMD air and missile defense
AO area of operations
AOR area of responsibility
APS Army pre-positioned stocks
AR Army regulation
ASCC Army Service component command
ASOS Army support to other Services
ATP Army techniques publication
BCD battlefield coordination detachment
BCT brigade combat team
C2 command and control
CBRN chemical, biological, radiological, and nuclear
CCDR combatant commander
CCIR commander’s critical information requirement
CCP combatant command campaign plan
CFLCC coalition forces land component commander
COCOM combatant command (command authority)
COP common operational picture
DOD Department of Defense
DODD Department of Defense directive
DSCA defense support of civil authorities
FDO flexible deterrent option
FID foreign internal defense
FM field manual
FRO flexible response option
FULLCOM full command
ISR intelligence, surveillance, and reconnaissance
JFC joint force commander
JFLCC joint force land component commander
JLOTS joint logistics over-the-shore
JOA joint operations area
JP joint publication
JSA joint security area
JTF joint task force
MCRP Marine Corps Reference Publication
MCTP Marine Corps tactical publication
MCWP Marine Corps Warfighting Publication
MDTF multi-domain task force
METT-TC (I) mission, enemy, terrain and weather, troops and support available, time available, civil considerations, and informational considerations
MIB-T military intelligence brigade-theater
NATO North Atlantic Treaty Organization
NEO noncombatant evacuation operation
NKPA North Korean People’s Army
NTTP Navy tactics, techniques, and procedures
OPCOM operational command
OPCON operational control
OPLAN operation plan
RSOI reception, staging, onward movement, and integration
SFA security force assistance
SFAB security force assistance brigade
SHORAD short-range air defense
STANAG standardization agreement
TACOM tactical command
TACON tactical control
TEC theater engineer command
TPFDD time-phased force and deployment data
TRADOC United States Army Training and Doctrine Command
TSC theater sustainment command
UAS unmanned aircraft system
U.S. United States
USAFFE United States Army Forces in the Far East
USAID United States Agency for International Development
USC United States Code
USSOCOM United States Special Operations Command
SECTION II – TERMS
administrative control
Direction or exercise of authority over subordinate or other organizations in respect to administration and support. (JP 1, Volume 2)
adversary
A party acknowledged as potentially hostile to a friendly party and against which the use of force may be envisaged. (JP 3-0)
*agility
The ability to move forces and adjust their dispositions and activities more rapidly than the enemy.
air domain
The atmosphere, beginning at the Earth’s surface, extending to the altitude where its effects upon operations become negligible. (JP 3-30)
antiaccess
Action, activity, or capability, usually long-range, designed to prevent an enemy force from entering an operational area. (JP 3-0)
area defense
A type of defensive operation that concentrates on denying enemy forces access to designated terrain for a specific time rather than destroying the enemy outright. (ADP 3-90)
area denial
Action, activity, or capability, usually short-range, designed to limit an enemy force’s freedom of action within an operational area. (JP 3-0)
area of influence
An area inclusive of and extending beyond an operational area wherein a commander is capable of direct influence by maneuver, fire support, and information normally under the commander’s command or control. (JP 3-0)
area of interest
That area of concern to the commander, including the area of influence, areas adjacent to it, and extending into enemy territory. (JP 3-0)
area of operations
An operational area defined by a commander for the land or maritime force commander to accomplish their missions and protect their forces. (JP 3-0)
area reconnaissance
A type of reconnaissance operation that focuses on obtaining detailed information about the terrain or enemy activity within a prescribed area. (ADP 3-90)
area security
A type of security operation conducted to protect friendly forces, lines of communications, and activities within a specific area. (ADP 3-90)
ARFOR
The Army component and senior Army headquarters of all Army forces assigned or attached to a combatant command, subordinate joint force command, joint functional command, or multinational command. (FM 3-94)
attack
A type of offensive operation that destroys or defeats enemy forces, seizes and secures terrain, or both. (ADP 3-90)
battle
A set of related engagements that lasts longer and involves larger forces than an engagement. (ADP 3-90)
breach
A synchronized combined arms activity under the control of the maneuver commander conducted to allow maneuver through an obstacle. (ATP 3-90.4)
civil preparation of the environment
The continuous development of civil knowledge within an area of operations to help commanders identify capabilities within civil society that can be integrated with operations for stability and security activities. (FM 3-57)
civil reconnaissance
A targeted, planned, and coordinated observation and evaluation of specific civil aspects of the environment such as areas, structures, capabilities, organizations, people, or events. (JP 3-57)
clearing
A mobility task that involves the elimination or neutralization of an obstacle that is usually performed by follow-on engineers and is not done under fire. (ATP 3-90.4)
close combat
Warfare carried out on land in a direct-fire fight, supported by direct and indirect fires and other assets. (ADP 3-0)
*close operations
Tactical actions of subordinate maneuver forces and the forces providing immediate support to them, whose purpose is to employ maneuver and fires to close with and destroy enemy forces.
close support
The action of the supporting force against targets or objectives that are sufficiently near the supported force as to require detailed integration or coordination of the supporting action. (JP 3-31)
combat power
The total means of destructive and disruptive force that a military unit/formation can apply against an enemy at a given time. (JP 3-0)
combined arms
The synchronized and simultaneous application of arms to achieve an effect greater than if each element was used separately or sequentially. (ADP 3-0)
command and control warfighting function
The related tasks and a system that enable commanders to synchronize and converge all elements of combat power. (ADP 3-0)
commander’s intent
A clear and concise expression of the purpose of an operation and the desired objectives and military end state. (JP 3-0)
common operational picture
(Army) A display of relevant information within a commander’s area of interest tailored to the user’s requirements and based on common data and information shared by more than one command. (ADP 6-0)
contingency plan
A branch of a campaign plan that is planned based on hypothetical situations for designated threats, catastrophic events, and contingent missions outside of crisis conditions. (JP 5-0)
*conventional warfare
A violent struggle for domination between nation-states or coalitions of nation-states.
consolidate gains
Activities to make enduring any temporary operational success and to set the conditions for a sustainable security environment, allowing for a transition of control to other legitimate authorities. (ADP 3-0)
*convergence
An outcome created by the concerted employment of capabilities from multiple domains and echelons against combinations of decisive points in any domain to create effects against a system, formation, decision maker, or in a specific geographic area.
countermobility
A set of combined arms activities that use or enhance the effects of natural and man-made obstacles to prevent the enemy freedom of movement and maneuver. (ATP 3-90.8)
cover
(Army) A type of security operation done independent of the main body to protect them by fighting to gain time while preventing enemy ground observation of and direct fire against the main body. (ADP 3-90)
crisis
An emerging incident or situation involving a possible threat to the United States, its citizens, military forces, or vital interests that develops rapidly and creates a condition of such diplomatic, economic, or military importance that commitment of military forces and resources is contemplated to achieve national and/or strategic objectives. (JP 3-0)
*cyberspace domain
(Army) The interdependent networks of information technology infrastructures and resident data, including the Internet, telecommunication networks, computer systems, embedded processors and controllers, and relevant portions of the electromagnetic spectrum (ADP 3-0)
decisive point
Key terrain, key event, critical factor, or function that, when acted upon, enables commanders to gain a marked advantage over an enemy or contribute materially to achieving success. (JP 5-0)
*deep operations
Tactical actions against enemy forces, typically out of direct contact with friendly forces, intended to shape future close operations and protect rear operations.
defeat
To render a force incapable of achieving its objectives. (ADP 3-0)
defeat in detail
Concentrating overwhelming combat power against separate parts of a force rather than defeating the entire force at once. (ADP 3-90)
defeat mechanism
A method through which friendly forces accomplish their mission against enemy opposition. (ADP 3-0)
defense support of civil authorities
Support provided by U.S. Federal military forces, DOD Civilians, DOD contract personnel, DOD component assets, and National Guard forces (when the Secretary of Defense, in coordination with the governors of the affected states, elects and requests to use those forces in Title 32, USC status) in response to requests for assistance from civil authorities for domestic emergencies, law enforcement support, and other domestic activities, or from qualifying entities for special events. (DODD 3025.18)
defensive operation
An operation to defeat an enemy attack, retain key terrain, gain time, and develop conditions favorable for offensive or stability operations. (ADP 3-0)
deployment
The movement of forces into and out of an operational area. (JP 3-35)
depth
The extension of operations in time, space, or purpose to achieve definitive results. (ADP 3-0)
destroy
A tactical mission task that physically renders an enemy force combat-ineffective until it is reconstituted. Alternatively, to destroy a combat system is to damage it so badly that it cannot perform any function or be restored to a usable condition without being entirely rebuilt. (FM 3-90-1)
direct liaison authorized
That authority granted by a commander (any level) to a subordinate to directly consult or coordinate an action with a command or agency within or outside of the granting command. (JP 1, Volume 2)
direct support
A mission requiring a force to support another specific force and authorizing it to answer directly to the support force’s request for assistance. (JP 3-09.3)
*direct support
(Army) A support relationship requiring a force to support another specific force and authorizing it to answer directly to the supported force’s request for assistance.
*disintegrate
To disrupt the enemy’s command and control, degrading the synchronization and cohesion of its operations.
*dislocate
To employ forces to obtain significant positional advantage in one or more domains, rendering the enemy’s dispositions less valuable, perhaps even irrelevant.
*domain
A physically defined portion of an operational environment requiring a unique set of warfighting capabilities and skills.
electromagnetic reconnaissance
The detection, location, identification, and evaluation of foreign electromagnetic radiations (energy). (JP 3-85)
electromagnetic warfare
Military action involving the use of electromagnetic and directed energy to control the electromagnetic spectrum or to attack the enemy. (JP 3-85)
end state
The set of required conditions that defines achievement of the commander’s objectives. (JP 3-0)
*endurance
The ability to persevere over time throughout the depth of an operational environment.
enemy
A party identified as hostile against which the use of force is authorized. (ADP 3-0)
engagement
A tactical conflict, usually between opposing lower echelon maneuver forces. (JP 3-0)
essential element of friendly information
A critical aspect of a friendly operation that, if known by a threat would subsequently compromise, lead to failure, or limit success of the operation and therefore should be protected from enemy detection. (ADP 6-0)
exploitation
(Army) A type of offensive operation that usually follows a successful attack and is designed to disorganize the enemy in depth. (ADP 3-90)
fires warfighting function
The related tasks and systems that create and converge effects in all domains against the adversary or enemy to enable operations across the range of military operations. (ADP 3-0)
fixing force
A force designated to supplement the striking force by preventing the enemy from moving from a specific area for a specific time. (ADP 3-90)
force projection
The ability to project the military instrument of national power from the United States, or another theater in response to requirements for military operations. (JP 3-0) force tailoring
The process of determining the right mix of forces and the sequence of their deployment in support of a joint force commander. (ADP 3-0)
forcible entry
Seizing and holding of a military lodgment in the face of armed opposition or forcing access into a denied area to allow movement and maneuver to accomplish the mission. (JP 3-18)
foreign internal defense
Participation by civilian agencies and military forces of a government or international organizations in any of the programs and activities undertaken by a host nation government to free and protect its society from subversion, lawlessness, insurgency, terrorism, and other threats to its security. (JP 3-22)
forward passage of lines
Occurs when a unit passes through another unit’s positions while moving toward the enemy. (ADP 3-90)
friendly force information requirement
Information the commander and staff need to understand the status of friendly force and supporting capabilities. (JP 3-0)
gap
A ravine, mountain pass, river, or other terrain feature that presents an obstacle that may be bridged. (ATP 3-90.4)
general support
Support given to the supported force as a whole and not to any particular subdivision thereof. (JP 3-09.3)
*general support—reinforcing
(Army) A support relationship assigned to a unit to support the force as a whole and to reinforce another similar type unit.
guard
A type of security operation done to protect the main body by fighting to gain time while preventing enemy ground observation of and direct fire against the main body. (ADP 3-90)
homeland defense
The protection of United States sovereignty, territory, domestic population, and critical infrastructure against external threats and aggression or other threats as directed by the President. (JP 3-27)
*human dimension
Encompasses people and the interaction between individuals and groups, how they understand information and events, make decisions, generate will, and act within an operational environment.
*informational considerations
Those aspects of the human, information, and physical dimensions that affect how humans and automated systems derive meaning from, use, act upon, and are impacted by information.
information collection
An activity that synchronizes and integrates the planning and employment of sensors and assets and as well as the processing, exploitation, and dissemination systems in direct support of current and future operations. (FM 3-55)
*information dimension
The content and data that individuals, groups, and information systems communicate and exchange, as well as the analytics and technical processes used to exchange information within an operational environment.
integration
The arrangement of military forces and their actions to create a force that operates by engaging as a whole. (JP 1, Volume 1)
intelligence preparation of the battlefield
The systematic process of analyzing the mission variables of enemy, terrain, weather, and civil considerations in an area of interest to determine their effect on operations. (ATP 2-01.3)
intelligence warfighting function
The related tasks and systems that facilitate understanding the enemy, terrain, weather, civil considerations, and other significant aspects of the operational environment. (ADP 3-0)
interagency coordination
The planning and synchronization of efforts that occur between elements of Department of Defense and participating United States Government departments and agencies. (JP 3-0)
interoperability
The ability to act together coherently, effectively, and efficiently to achieve tactical, operational, and strategic objectives. (JP 3-0)
interorganizational cooperation
The interaction that occurs among elements of the Department of Defense; participating United States Government departments and agencies; state, territorial, local, and tribal agencies; foreign military forces and government agencies; international organizations; nongovernmental organizations; and the private sector. (JP 3-08)
*irregular warfare
(Army) The overt, clandestine, and covert employment of military and non-military capabilities across multiple domains by state and non-state actors through methods other than military domination of an adversary, either as the primary approach or in concert with conventional warfare.
isolate
To separate a force from its sources of support in order to reduce its effectiveness and increase its vulnerability to defeat. (ADP 3-0)
joint force
A force composed of elements, assigned or attached, of two or more Military Departments operating under a single joint force commander. (JP 3-0)
joint operations
Military actions conducted by joint forces and those Service forces employed in specified command relationships with each other, which, of themselves, do not establish joint forces. (JP 3-0)
joint security area
A specific area to facilitate protection of joint bases and their connecting lines of communications that support joint operations. (JP 3-10)
land domain
The area of the Earth’s surface ending at the high water mark and overlapping with the maritime domain in the landward segment of the littorals. (JP 3-31)
large-scale combat operations
Extensive joint combat operations in terms of scope and size of forces committed, conducted as a campaign aimed at achieving operational and strategic objectives. (ADP 3-0)
leadership
The activity of influencing people by providing purpose, direction, and motivation to accomplish the mission and improve the organization. (ADP 6-22)
*lethality
The capability and capacity to destroy.
levels of warfare
A framework for defining and clarifying the relationship among national objectives, the operational approach, and tactical tasks. (ADP 1-01)
lighterage
The process in which small craft are used to transport cargo or personnel from ship-to-shore using amphibians, landing craft, discharge lighters, causeways, and barges. (JP 4-01.6)
lodgment
A designated area in a hostile or potentially hostile operational area that, when seized and held, makes the continuous landing of troops and materiel possible and provides maneuver space for subsequent operations. (JP 3-18)
main effort
A designated subordinate unit whose mission at a given point in time is most critical to overall mission success. (ADP 3-0)
maritime domain
The oceans, seas, bays, estuaries, islands, coastal areas, and the airspace above these, including the littorals. (JP 3-32)
meeting engagement
A combat action that occurs when a moving force, incompletely deployed for battle, engages an enemy at an unexpected time and place. (ADP 3-90)
military engagement
Contact and interaction between individuals or elements of the Armed Forces of the United States and those of another nation’s armed forces, or foreign and domestic civilian authorities or agencies, to build trust and confidence, share information, coordinate mutual activities, and maintain influence. (JP 3-0)
mobile defense
A type of defensive operation that concentrates on the destruction or defeat of the enemy through a decisive attack by a striking force. (ADP 3-90)
mobility
A quality or capability of military forces which permits them to move from place to place while retaining the ability to fulfill their primary mission. (JP 3-36)
mobility tasks
Those combined arms activities that mitigate the effects of obstacles to enable freedom of movement and maneuver. (ATP 3-90.4)
mobilization
The process by which the Armed Forces of the United States, or part of them, are brought to a state of readiness for war or other national emergency. (JP 4-05)
movement and maneuver warfighting function
The related tasks and systems that move and employ forces to achieve a position of relative advantage over the enemy and other threats. (ADP 3-0)
movement to contact
(Army) A type of offensive operation designed to develop the situation and to establish or regain contact. (ADP 3-90)
*multidomain operations
The combined arms employment of joint and Army capabilities to create and exploit relative advantages to achieve objectives, defeat enemy forces, and consolidate gains on behalf of joint force commanders.
multinational operations
A collective term to describe military actions conducted by forces of two or more nations, usually undertaken within the structure of a coalition or alliance. (JP 3-16)
mutual support
That support which units render each other against an enemy, because of their assigned tasks, their position relative to each other and to the enemy, and their inherent capabilities. (JP 3-31)
*national strategic level of warfare
The level of warfare at which the U.S. government formulates policy goals and ways to achieve them by synchronizing action across government and unified action partners and employing the instruments of national power.
offensive operation
An operation to defeat or destroy enemy forces and gain control of terrain, resources, and population centers. (ADP 3-0)
operation
A sequence of tactical actions with a common purpose or unifying theme. (JP 1, Volume 1)
operational approach
A broad description of the mission, operational concepts, tasks, and actions required to accomplish the mission. (JP 5-0)
operational environment
The aggregate of the conditions, circumstances, and influences that affect the employment of capabilities and bear on the decisions of the commander. (JP 3-0)
operational framework
A cognitive tool used to assist commanders and staffs in clearly visualizing and describing the application of combat power in time, space, purpose, and resources in the concept of operations. (ADP 1-01)
operational level of warfare
The level of warfare in which campaigns and operations are planned, conducted, and sustained to achieve operational objectives to support achievement of strategic objectives. (JP 3-0)
operational reach
The distance and duration across which a force can successfully employ military capabilities. (JP 3-0)
passage of lines
An operation in which a force moves forward or rearward through another force’s combat positions with the intention of moving into or out of contact with the enemy. (JP 3-18)
peace operations
Multiagency and multinational crisis response and limited contingency operations involving all instruments of national power with military missions to contain conflict, redress the peace, and shape the environment to support reconciliation and rebuilding and facilitate the transition to legitimate governance. (JP 3-07.3)
*physical dimension
The material characteristics and capabilities, both natural and manufactured, within an operational environment.
principle
A comprehensive and fundamental rule or an assumption of central importance that guides how an organization approaches and thinks about the conduct of operations. (ADP 1-01)
priority intelligence requirement
The intelligence component of commander’s critical information requirements used to focus the employment of limited intelligence assets and resources against competing demands for intelligence support. (JP 2-0)
*protection warfighting function
The related tasks, systems, and methods that prevent or mitigate detection, threat effects, and hazards to preserve combat power and enable freedom of action.
pursuit
A type of offensive operation designed to catch or cut off a hostile force attempting to escape, with the aim of destroying it. (ADP 3-90)
*rear operations
Tactical actions behind major subordinate maneuver forces that facilitate movement, extend operational reach, and maintain desired tempo.
rearward passage of lines
Occurs when a unit passes through another unit’s positions while moving away from the enemy. (ADP 3-90)
reception
The process of receiving, offloading, marshalling, accounting for, and transporting of personnel, equipment, and materiel from the strategic and/or intratheater deployment phase to a sea, air, or surface transportation point of debarkation to the marshalling area. (JP 3-35)
reconnaissance
A mission undertaken to obtain, by visual observation or other detection methods, information about the activities and resources of an enemy or adversary, or to secure data concerning the meteorological, hydrographic, or geographic characteristics of a particular area. (JP 2-0)
reconnaissance in force
A type of reconnaissance operation designed to discover or test the enemy’s strength, dispositions, and reactions or to obtain other information. (ADP 3-90)
reconstitution
(Army) An operation that commanders plan and implement to restore units to a desired level of combat effectiveness commensurate with mission requirements and available resources. (ATP 3-94.4)
redeployment
The transfer or rotation of forces and materiel to support another commander’s operational requirements, or to return personnel, equipment, and materiel to the home and/or demobilization stations for reintegration and/or out-processing. (JP 3-35)
*reinforcing
A support relationship requiring a force to support another supporting unit.
*relative advantage
A location or condition, in any domain, relative to an adversary or enemy that provides an opportunity to progress towards or achieve an objective.
relief in place
An operation in which, by direction of higher authority, all or part of a unit is replaced in an area by the incoming unit and the responsibilities of the replaced elements for the mission and the assigned zone of operations are transferred to the incoming unit. (JP 3-07.3)
reserve
That portion of a body of troops that is withheld from action at the beginning of an engagement to be available for a decisive movement. (ADP 3-90)
retrograde
(Army) A type of defensive operation that involves organized movement away from the enemy. (ADP 3-90)
route reconnaissance
A type of reconnaissance operation to obtain detailed information of a specified route and all terrain from which the enemy could influence movement along that route. (ADP 3-90)
screen
A type of security operation that primarily provides early warning to the protected force. (ADP 3-90)
seabasing
The deployment, assembly, command, projection, reconstitution, sustainment, and re-employment of joint power from the sea without reliance on land bases within the operational area. (JP 3-02)
*sector
An operational area assigned to a unit in the defense that has rear and lateral boundaries and interlocking fires.
security cooperation
All Department of Defense interactions with foreign security establishments to build security relationships that promote specific United States security interests, develop allied and partner nation military and security capabilities for self-defense and multinational operations, and provide United States forces with peacetime and contingency access to allied and partner nations. (JP 3-20)
security force assistance
The Department of Defense activities that support the development of the capacity and capability of foreign security forces and their supporting institutions. (JP 3-20)
security forces
Duly constituted military, paramilitary, police, and constabulary forces of a state. (JP 3-22)
security operations
Those operations performed by commanders to provide early and accurate warning of enemy operations, to provide the force being protected with time and maneuver space within which to react to the enemy, and to develop the situation to allow commanders to effectively use their protected forces. (ADP 3-90)
security sector reform
A comprehensive set of programs and activities undertaken by a host nation to improve the way it provides safety, security, and justice. (JP 3-07)
*setting the theater
The broad range of activities continuously conducted to establish conditions for the successful execution of operations in a theater.
simultaneity
The execution of related and mutually supporting tasks at the same time across multiple locations and domains. (ADP 3-0)
situational understanding
The product of applying analysis and judgment to relevant information to determine the relationships among the operational and mission variables. (ADP 6-0)
*space domain
The area above the altitude where atmospheric effects on airborne objects become negligible.
special reconnaissance
Reconnaissance and surveillance actions conducted as a special operation in hostile, denied, or diplomatically and/or politically sensitive environments to collect or verify information of strategic or operational significance, employing military capabilities not normally found in conventional forces. (JP 3-05)
stability mechanism
The primary method through which friendly forces affect civilians in order to attain conditions that support establishing a lasting, stable peace. (ADP 3-0)
stability operation
An operation conducted outside the United States in coordination with other instruments of national power to establish or maintain a secure environment and provide essential governmental services, emergency infrastructure reconstruction, and humanitarian relief. (ADP 3-0)
staging
Assembling, holding, and organizing arriving personnel, equipment, and sustaining materiel in preparation for onward movement. (JP 3-35)
striking force
A dedicated counterattack force in a mobile defense constituted with the bulk of available combat power. (ADP 3-90)
*support area operations
The tactical actions securing lines of communications, bases, and base clusters that enable an echelon’s sustainment and command and control.
supporting distance
The distance between two units that can be traveled in time for one to come to the aid of the other and prevent its defeat by an enemy or ensure it regains control of a civil situation. (ADP 3-0)
supporting effort
A designated subordinate unit with a mission that supports the success of the main effort. (ADP 3-0)
supporting range
The distance one unit may be geographically separated from a second unit yet remain within the maximum range of the second unit’s weapons systems. (ADP 3-0)
survivability
(Army) A quality or capability of military forces which permits them to avoid or withstand hostile actions or environmental conditions while retaining the ability to fulfill their primary mission. (ATP 3-37.34)
sustainment warfighting function
The related tasks and system that provide support and services to ensure freedom of action, extended operational reach, and prolong endurance. (ADP 3-0)
synchronization
The arrangement of military actions in time, space, and purpose to produce maximum relative combat power at a decisive place and time. (JP 2-0)
tactical level of warfare
The level of warfare at which forces plan and execute battles and engagements to achieve military objectives. (JP 3-0)
tactics
The employment, ordered arrangement, and directed actions of forces in relation to each other. (ADP 3-90)
task-organizing
The act of designing a force, support staff, or sustainment package of specific size and composition to meet a unique task or mission. (ADP 3-0)
tempo
The relative speed and rhythm of military operations over time with respect to the enemy. (ADP 3-0)
*theater strategic level of warfare
The level of warfare at which combatant commanders synchronize with unified action partners and employ all elements of national power to fulfill policy aims within the assigned theater in support of the national strategy.
threat
Any combination of actors, entities, or forces that have the capability and intent to harm United States forces, United States national interests, or the homeland. (ADP 3-0)
troop movement
The movement of Soldiers and units from one place to another by any available means. (ADP 3-90)
understanding
In the context of decision making, knowledge that has been synthesized and had judgment applied to comprehend the situation’s inner relationships, enable decision making, and drive action. (ADP 6-0)
unified action
The synchronization, coordination, and/or integration of the activities of governmental and nongovernmental entities with military operations to achieve unity of effort. (JP 1, Volume 1)
unity of effort
Coordination and cooperation toward common objectives, even if the participants are not necessarily part of the same command or organization, which is the product of successful unified action. (JP 1, Volume 2)
warfighting function
A group of tasks and systems united by a common purpose that commanders use to accomplish missions and training objectives. (ADP 3-0)
*zone
An operational area assigned to a unit in the offense that only has rear and lateral boundaries.
zone reconnaissance
A type of reconnaissance operation that involves a directed effort to obtain detailed information on all routes, obstacles, terrain, and enemy forces within a zone defined by boundaries. (ADP 3-90)
Index
A
accepting risk to create and exploit opportunities, 8-18– 8-22 account for being under constant observation and all forms of enemy contact, 3-56–3-68 account for constant enemy observation, 3-62–3-65 achieving convergence, 3-22– 3-26 activities, joint, 2-55–2-57 to achieve strategic goals, 4–5–4-8 to control escalation, 5-7 to counter a United States response, 4-9 to mitigate U.S. deterrence, 5–8 to preclude United States access to a region, 4-10– 4–11 adapting formations for missions and transitions, 8-36–8-54 administrative control, defined, B-14 provide, 4-60 advantages, human, during armed conflict, 6-32 human, during crisis, 5-14 information, during armed conflict, 6-31 information, during crisis, 5-13 physical, during armed conflict, 6-25–6-30 physical, during crisis, 5-11–5-12 relative, 5-10–5-14 advantages during armed conflict, relative, 6-24–6-32 adversary, activities to shape a crisis, 5-5–5-6 methods during competition, 4-4–4-11 methods during crisis, 5-4– 5-8 agility, 3-8–3-11 defined, 3-8 air, 2-69–2-70 air and missile defense, provide theater, 7-52–7-53 air and missile threats, counter, 6-54–6-62 air domain, 1-93–1-96 defined, 1-93 aligned, B-32 amphibious operations, 7-58– 7-63 antiaccess, defined, 2-48 antiaccess and area denial, defeat enemy, 7-52–7-62 approaches, defeating, 6-79–6-86 anticipate, plan, and execute transitions, 3-85–3-90 applying, defeat mechanisms, 6-106–6-132 mutual support, 6-39–6-44 the art of command, 8-5– 8-26 the operational framework, 7–27–7-34 arctic region, 7-7–7-9 area defense, defined, 6-187 area denial, defined, 2-49 area of influence, defined, 3-137 area of interest, defined, 3-138 area of operations, assigning, 7-30 defined, 3-129 area reconnaissance, defined, 6-138 area security, defined, 6-150 ARFOR, defined, B-5 armed conflict, 1-72–1-73 and large-scale combat operations, 6-1–6-171 enemy approaches to, 6-8– 6-23 transition to, 4-101–4-110 Army air and missile defense command, 4-78 Army command and support relationships, B-17–B-32 Army command relationships, B-18–B-22 Army echelons, 2-79–2-94 Army echelons during competition, roles of, 4-55– 4-96 Army echelons during crisis, 5–52–5-63 Army field support brigade, 4–85 Army force posture, 2-77–2-78 Army forces, challenges for, 1–15–1-22 Army forces in the theater, exercise command and control over, 4-64–4-65 Army operations, 1-1–1-8 in maritime environments, 7-1–7-79 Army strategic contexts, 1-65– 1-77 Army support relationships, B-23–B-28 Army support to the joint force during crisis, 5-15–5-19 Army-specific considerations, maritime environment, 7-18– 7-21 art of command, and the commander, 8-1–8-4 applying, 8-5–8-26 assess, 8-35 assigned, B-20 assigned areas, 3-128–3-132 assigning, joint operations area within an area of responsibility, 7-28 area of operations, 7-30 land areas, 6-38 assistance, humanitarian, 4-54 attached, B-21–B-22 attack, defined, 6-230 authorities, other, B-13–B-16
B
battle, defined, 1-63 battlefield coordination detachment, 4-82–4-83 breach, defined, 6-169 brigade combat teams, 2-90– 2-91 during competition, 4-96 brigades, 5-62 during transition to postconflict competition, 6-265–6-267 multifunctional and functional, 2-92–2-94 build allied and partner capabilities and capacity, 4-16–4-17
C
chain of command, B-3–B-5 challenges, for Army forces, 1-15–1-22 overcoming, 1-23–1-25 chaotic, war is, 1-32 characteristics, defense, 6-179 offense, 6-222 warfare, 1-35 China, 6-15–6-23 civil preparation of the environment, defined, 4-70 clearing, defined, 6-170 close operations, 3-147–3-151 defined, 3-147 during armed conflict, 6-240–6-244 in maritime environments, 7-32 combat power, 2-15–2-31 defined, 2-15 combatant command (command authority), B-7 combatant commander daily operational requirements, 4-59 combination command structure, B-44 combined arms, 1-50–1-53 defined, 1-50 command, B-1 chain of, B-3–B-5 full, B-46 operational, B-47 tactical, B-49 unity of, A-13–A-14 command and control, during degraded or denied communications, 8-23–8-26 establish in maritime environments, 7-36 establish on land, 6-36– 6-53 exercise over Army forces in the theater, 4-64–4-65 of deep, close, and rear operations, 3-160–3-162 command and control, warfighting function, 2-3–2-5 defined, 2-3 command and support considerations, multinational, B-33–B-50 command and support relationships, B-1–B-50 command authority, B-36–B-37 command relationships, Army, B-18–B-22 joint, B-6–B-16 command relationships and authorities, North Atlantic Treaty Organization, B-45– B-50 command structure, combination, B-44 integrated, B-41 lead nation, B-42 multinational, B-38–B-44 command structures, parallel, B-43 commander, art of command and, 8-1–8-4 commander presence on the battlefield, 8-6–8-12 commander’s intent, 8-13–8-14 defined, 8-13 common operational picture, 3-52–3-55 defined, 3-52 communicating with staff and subordinates, 8-47–8-48 competition, activities, 4-36– 4-54 adversary methods during, 4-4–4-11 below armed conflict, 1-68 roles of Army echelons during, 4-55–4-96 competition or armed conflict, transition to, 5-64–5-68 conduct large-scale combat operations, 6-89 conduct theater sustainment operations, 7-70–7-78 conflict, contingency planning for, 4-67-4-70 conflict type determination, 4-106 considerations unique to the maritime environment, 7-10– 7-21 consolidate gains, continuously, 3-93–3-95 defined, 1-74 during armed conflict, 6-98– 6-105 consolidating gains, 1-74–1-77 during competition, 4-97– 4-102 during crisis, 5-63 contested deployments, C-1– C-44 contingency plan, defined, 4-67 contingency planning for crisis and conflict, 4-67-4-70 control, operational, B-8–B-9, B-48 control, strategic lines of communications and key terrain, 6-69–6-74 control, tactical, B-10, 50 conventional, and special operations forces integration, 2-63–2-65 conventional warfare, 1-37– 1-39 defined, 1-37 convergence, 3-12–3-14 achieving, 3-22–3-26 defined, 3-12 coordinating authority, B-15 coordination, interagency, 4-30–4-35 corps, 2-87–2-88 during transition to postconflict competition, 6-261–6-262 roles during competition, 4-90–4-91 roles during crisis, 5-56– 5-60 counter air and missile threats, 6-54–6-62 countering weapons of mass destruction, 4-53 countermobility, defined, 6-162 countermobility operations, 6-162–6-164 country team, 4-34–4-35 cover, defined, 6-151 create and exploit relative physical, information, and human advantages in pursuit of decision dominance, 3-69–3-74 crisis, 1-69–1-71 adversary methods during, 5-4–5-8 Army echelons during, 5-53–5-63 Army support to the joint force during, 5-15–5-19 contingency planning for, 4-67-4-70 defined, 1-69 transition to, 4-101–4-110 cyberspace, 2-73–2-74 domain, 1-101–1-105 cyberspace domain, defined, 1-101
D
decisive point, defined, 3-105 deep operations, 3-142–3-146 defined, 3-142 during defensive operations, 6-194–6-198 during offensive operations, 6-235–6-239 in maritime environments, 7-31 deep, close, and rear operations, 3-140–3-160 command and control of, 3-160–3-162 defeat, components of enemy antiaccess and area denial, 6-75–6-86 defined, 3-101 enemy antiaccess and area denial, 7-52–7-63 mechanisms, 3-106–3-114 defeat in detail, defined, 3-104 defeat mechanisms, defined, 3-106 applying, 6-106–6-132 defeating, antiaccess and area denial approaches, 6-79– 6-86 enemy forces in detail, 3-101–3-105 defend and control key terrain, during armed conflict, 6-63– 6-74 in maritime environments, 7-37–7-38 defense, by forward-stationed forces, 6-64–6-68 characteristics of, 6-179 enemy, 6-223–6-227 protection support to the, 7-39–7-47 purpose and conditions for, 6-173–6-178 support of civil authorities, C-42–C-43 transition to, 6-252–6-254 defense support of civil authorities, homeland defense and, C-36–C-43 defensive, operational framework considerations, 6-191–6-217 operations, 6-172–6-219 defensive operation, defined, 1-44 defensive operations, types of, 6-186–6-190 degraded communications, command and control during, 8-23–8-26 denied communications, command and control during, 8-23–8-26 deployment, 5-31–5-32 defined, 5-31 depth, 3-32–3-36 defined, 3-32 describe, 8-32 designate, weight, and sustain the main effort, 3-91–3-92 designating a joint security area, 7-29 destroy, 6-108–6-111 defined, 3-109 determination, conflict type, 4-103 develop, leaders, 4-24 developing, leadership experience, 8-39–8-43 teams, 8-49–8-54 dimension, human, 1-115– 1-117 information, 1-111–1-114 physical, 1-107–1-100 dimensions, 1-106–1-117 diplomatic mission, United States, 4-32–4-33 direct, 8-33 direct liaison authorized, defined, B-16 direct support, defined, B-25 discipline, 8-17 disintegrate, 6-121–6-123 defined, 3-112 disintegration, operational-level, 6-124– 6-128 tactical-level, 6-129–6-132 dislocate, 6-112–6-116 defined, 3-110 division, 2-89, 5-61 roles during competition, 4-92–4-95 divisions during transition to post-conflict competition, 6-263–6-264 domain, air, 1-93–1-96 cyberspace, 1-101–1-105 defined, 1-82 interdependence, 2-68– 2-76 land domain, 1-83–1-87 maritime, 1-88–1-92 space, 1-97–1-100 domains, 1-82–1-105 driving the operations process, 8-27–8-35
E
echelons, Army, 2-79–2-94 integrating, 6-45–6-49 economy of force, A-10 electromagnetic reconnaissance, defined, 6-143 electromagnetic warfare, defined, 2-40 employment of forces, initial, 5-49 enable joint offensive operations, 7-52–7-63 enabling operations, 6-133– 6-171 end state, defined, 2-55 endurance, 3-27–3-31 defined, 3-27 enemy antiaccess and area denial, defeat components of, 6-75–6-86 enemy antiaccess and area denial, defeat in maritime environments, 7-52–7-63 enemy approaches to armed conflict, 6-8–6-23 enemy courses of action unique to the maritime environment, 7-14–7-17 enemy defense, 6-223–6-227 enemy integrated fires command, 6-76–6-78 enemy offense, 6-180–6-185 engagement, defined, 1-63 essential element of friendly information, defined, 3-41 establish command and control, in maritime environments, 7-36 on land, 6-36–6-53 establish protected reception, staging, onward movement, and integration, 7-65–7-69 execute operation plans, prepare to, 4-22–4-23 exercise command and control over Army forces in the theater, 4-64–4-65 exploitation, defined, 6-231 extended deep area, 3-123– 3-126 during offensive operations, 6-234 extended deep operations, 6-192–6-193
F
field army, 2-84–2-86 firepower, 2-19–2-21 fires warfighting function, defined, 2-11 fixing force, defined, 6-188 force posture, Army, 2-77–2-78 force projection, 5-20–5-51 and threat capabilities, C-1– C-12 defined, 5-20 force protection, 4-107 force tailoring, defined, 4-71 forces, initial employment of, 5-49 forcible entry, defined, 6-81 forcible entry operations, 7-55– 7-56 joint, 6-87–6-88 foreign internal defense, 4-47– 4-49 defined, 4-47 fort to port, C-13–C-21 forward passage of lines, defined, 6-159 forward-stationed forces, defense by, 6-64–6-68 initial employment of, 4-110 fostering shared understanding, 8-44–8-46 foundations of operations, 1-1– 1-119 friendly force information requirement, defined, 3-40 full command, B-46 functional brigades, 2-92–2-94 fundamentals of operations, 3-1–3-166
G
gap, defined, 6-171 general support—reinforcing, defined, B-28 generating and applying combat power, 2-1–2-94 guard, defined, 6-152
H
homeland defense, C-39–C-41 and defense support of civil authorities, C-36–C-43 human advantages, 6-32 during competition, 4-29 during crisis, 5-14 human dimension, 1-115– 1-117 defined, 1-115 human endeavor, war as, 1-31 humanitarian assistance, 4-54
I
imperatives, 3-37–3-97 implementing dispersion, 3-66– 3-68 impose multiple dilemmas on the enemy, 3-80–3-84 information, 2-22–2-25 information advantages, 6-31 during competition, 4-28 during crisis, 5-13 information collection, defined, 1-80 information dimension, 1-111– 1-114 defined, 1-111 information warfare, 2-40–2-44 informational considerations, defined, 1-119 initial employment, of forces, 5-49 of forward-stationed forces, 4-110 initiative, 8-15–8-16 instruments of national power, defined, 1-56 integrated command structure, B-41 integrated fires command, enemy, 6-76–6-78 integrating echelons, 6-45– 6-49 integration, 3-15–3-17 conventional and special operations forces, 2-63– 2-65 defined, 3-15 of forces, 5-45–5-48 intelligence preparation of the battlefield, defined, 3-43 intelligence warfighting function, 2-9–2-10 defined, 2-9 interagency coordination, 4-30–4-35 defined, 2-61 interdependence, domain, 2-64–2-76 joint, 2-66–2-67 interoperability, 4-18–4-19 defined, 4-18 interorganizational cooperation, defined, 2-62 irregular warfare, 1-40–1-41 defined, 1-40 isolate, 6-117–6-120 defined, 3-111 isolation, 2-50–2-51
J
joint command relationships, B-6–B-16 joint force, considerations in a maritime environment, 7-11– 7-13 defined, 2-55 operating as part of the, 6-33–6-105 joint forcible entry operations, 6-87–6-88 joint interdependence, 2-66– 2-67 joint operations, and activities, 2-55–2-57 defined, 2-55 principles of, A-19–A-26 joint operations area, assigning within an area of responsibility, 7-28 joint roles of limited scope and duration, perform, 4-66 joint security area, 3-121– 3-122 defined, 3-121 designating a, 7-29 joint support relationships, B-11–B-12
K
key terrain, control, 6-69–6-74 defend and control during armed conflict, 6-63–6-74 defend and control in a maritime environment, 7-37–7-38
L
land areas, assigning, 6-38 land domain, 1-83–1-87 defined, 1-83 large-scale combat operations, 1-46–1-49 conduct, 6-89 defined, 1-46 preparation for, 4-12–4-24 sustain, 6-90–6-97 sustain in maritime environments, 7-63–7-78 lead, 8-34 lead nation command structure, B-42 leaders, train and develop, 4-24 leadership, 2-17–2-18 defined, 2-17 during operations, 8-1–8-54 leadership experience, developing, 8-39–8-43 legitimacy, A-25–A-26 lethality, defined, 1-23 overcoming challenges, 1-23–1-25 levels of warfare, 1-54–1-64 defined, 1-54 littoral regions, 7-5–7-6 lodgment, defined, 6-87
M
main battle area operations, 6—206–6-208 main effort, 3-163 defined, 3-91 maintain the theater, 4-61–4-62 make initial contact with the smallest element possible, 3-75–3-79 maneuver, A-11–A-12 maritime, 2-75–2-76 maritime domain, 1-88–1-92 defined, 1-88 maritime environment, considerations unique to the, 7-10–7-21 enemy courses of action unique to, 7-14–7-17 joint force considerations in a, 7-11–7-13 operational considerations for, 7-35–7-79 overview of the, 7-1–7-21 physical characteristics of the, 7-2–7-9 planning and operational framework, 7-22–7-33 planning considerations for a, 7-23–7-26 maritime environments, Army operations in, 7-1–7-79 mass, A-8–A-9 mechanisms, defeat and stability, 3-106–3-114 meeting engagement, defined, 6-229 methods of warfare, 1-36–1-41 military engagement, 4-39– 4-40 defined, 4-39 military intelligence brigade-theater, 4-75–4-76 mission, variables, 1-118– 1-119 missions, adapting formations for, 8-36–8-54 mobile defense, 6-188–6-189 defined, 6-188 mobility, 2-26–2-28 defined, 2-26 mobility operations, 6-165– 6-171 mobility tasks, defined, 6-166 mobilization, 5-27–5-30 defined, 5-27 movement and maneuver warfighting function, 2-6–2-8 defined, 2-6 movement to contact, defined, 6-229 multidomain operations, 1-9– 1-14 defined, 1-9 the Army’s operational concept, 3-1–3-4 multi-domain task force, 4-86– 4-87 multifunctional brigades, 2-92– 2-94 multinational, command and support considerations, B-33–B-50 command structure, B-38– B-44 operations, 2-58–2-60 multinational operations, defined, 2-58 mutual support, 3-133–3-135 applying, 6-39–6-44 defined, 3-133
N
national strategic level of warfare, defined, 1-56 nature of war, 1-29–1-32 noncombatant evacuation operations, 4-108–4-109 North Atlantic Treaty Organization command relationships and authorities, B-45–B-50 nuclear deterrence, 4-53
O
objective, A-4–A-5 offense, characteristics, 6-222 enemy, 6-180–6-185 purpose and conditions for, 6-221 transition to, 6-218–6-219 offensive, A-6–A-7 operational framework considerations, 6-233– 6-251 operations, 6-220–6-267 offensive operation, defined, 1-43 offensive operations, types of, 6-228–6-232 onward movement, 5-43–5-44 opening the theater, 5-26 operating as part of the joint force, 6-33–6-105 operational, variables, 1-118– 1-119 operational approach, 3-100– 3-118 and operational framework, 3-98–3-166 defined, 3-100 operational areas, set and support, 4-63 operational command, B-47 operational concept, multidomain operations, 3-1–3-4 operational considerations for a maritime environment, 7-35– 7-79 operational control, B-8–B-9 in North Atlantic Treaty Organizations, B-48 operational environment, defined, 1-78 understand the, 3-47–3-55 understanding an, 1-78–119 operational framework, 3-127– 3-166 applying in maritime environments, 7-27–7-34 defined, 3-127 operational framework considerations, defensive, 6-191–6-217 offensive, 6-233–6-251 operational level of warfare, 1-58–1-61 defined, 1-58 operational reach, defined, 3-33 operational requirements, combatant commander daily, 4-59 operational-level disintegration, 6-124–6-128 operations, amphibious, 7-58– 7-63 Army, 1-1–1-8 close, 3-147–3-151 close, during armed conflict, 6-240–6-244 conduct theater sustainment, 7-67–7-79 deep, 3-142–3-146 deep during defensive operations, 6-194–6-198 deep during offensive operations, 6-235–6-239 during armed conflict, 6-1– 6-267 during competition below armed conflict, 4-1–4-110 during competition overview, 4-1–4-3 enabling, 6-133–6-171 extended deep, 6-192– 6-193 forcible entry, 7-55–7-56 foundations of, 1-1–1-119 fundamentals of, 3-1–3-166 joint, 2-55–2-57 large-scale combat, 1-46– 1-49 main battle area, 6-206– 6-208 multidomain, 1-9–1-14 multinational, 2-58–2-60 offensive, 6-220–6-267 rear, 3-152–3-159 rear during defensive operations, 6-215–6-217 rear during the offense, 6-245–6-251 security, 5-9 security area, 6-199–6-205 security in maritime environments, 7-48–7-51 sustain large-scale combat in maritime environments, 7-63–7-78 tenets of, 3-6–3-36 operations during crisis, 5-1– 5-68 overview of, 5-1–5-3 operations process, driving the, 8-27–8-35 opportunities, accepting risk to create and exploit, 8-18– 8-22 organic, B-19 other authorities, B-13–B-16 other relationships, B-29–B-32 overview, maritime environment, 7-1–7-21 operations during crisis, 5-1–5-3
P-Q
parallel command structures, B-43 passage of lines, 6-159–6-161 defined, 6-159 peace operations, defined, 4–102 perseverance, A-23–A-24 physical advantages, 6-25– 6-30 during competition, 4-27 during crisis, 5-11–5-12 physical characteristics of the maritime environment, 7-2– 7-9 physical dimension, 1-107– 1-110 defined, 1-107 planning and operational framework, maritime environment, 7-22–7-33 planning considerations, support area operations, 3-157–3-158 political purpose, war, 1-30 port to port, C-22–C-28 post-conflict competition, transition to, 6-255–6-267 preclusion, 2-48–2-49 preparation for large-scale combat operations, 4-12– 4-24 prepare to transition and execute operation plans, 4-22–4-23 presence on the battlefield, 8-6–8-12 principle, defined, A-2 principles of joint operations, A-19–A-26 principles of war, 1-33–1-34, A-1–A-26 principles of war, traditional, A-1–A-19 priority intelligence requirement, defined, 3-44 protect forward-stationed forces, 4-20–4-21 protection, during transit, 5-33– 5-38 support to the defense, 7-39–7-47 protection warfighting function, 2-14 defined, 2-14 provide theater air and missile defense, 7-53–7-54 purpose, for the defense, 6-173–6-178 for the offense, 6-221 pursuit, defined, 6-232
R
rear operations, 3-152–3-159 defined, 3-152 during defensive operations, 6-215–6-217 during the offense, 6-245– 6-251 in maritime environments, 7-33–7-34 rearward passage of lines, defined, 6-159 reception, 5-40–5-41 defined, 5-40 reception, staging, onward movement, and integration, 5-39–5-48 reception, staging, onward movement, and integration, during contested deployments, C-29–C-35 reception, staging, onward movement, and integration, establish protected, 7-64– 7-68 reconnaissance, 6-134–6-146 defined, 6-134 reconnaissance in force, defined, 6-140 reconstitution, defined, 6-95 redeployment, defined, 5-51 reinforcing, defined, B-27 relative advantage, defined, 1-12 relative advantages, 5-10–5-14 during armed conflict, 6-24– 6-32 during competition, 4-25–4- 29 relief in place, defined, 6-158 reserve, 3-165–3-166 defined, 3-165 during armed conflict, 6-209–6-214 restraint, A-21–A-22 retrograde, defined, 6-190 risk, 3-115–3-118 accepting to create and exploit opportunities, 8-18–8-22 roles of Army echelons during competition, 4-55–4-96 route reconnaissance, defined, 6-139 Russia, 6-9–6-14
S
sanctuary, 2-52–2-53 screen, defined, 6-153 sector, defined, 3-131 security, A-15–A-16 security area operations, 6-199–6-205 security assistance, 4-44 security cooperation, 4-41– 4-52 defined, 4-41 security force assistance, 4-45–4-46 defined, 4-45 security force assistance brigades, 4-88–4-89 security forces, defined, 4-45 security operations, 6-147– 6-156 defined, 6-149 in maritime environments, 7-48–7-51 security sector reform, defined, 4-50 support to, 4-50–4-52 see the enemy, 3-43–3-46 see yourself, 3-40–3-42 see yourself, see the enemy, and understand the operational environment, 3-38–3-55 set, and maintain the theater, 4-61–4-62 operational areas, 4-63 the theater, 4-13–4-15 setting the theater, defined, 4-13 shared understanding, 3-50– 3-51 fostering, 8-44–8-46 signal command (theater), 4-79–4-80 simplicity, A-19 simultaneity, defined, 3-20 situational understanding, defined, 3-49 space, 2-71–2-72 space domain, 1-97–1-100 defined, 1-97 special operations forces, and conventional forces integration, 2-63–2-65 special reconnaissance, defined, 6-141 stability, transition to, 6-252– 6-254 stability mechanism, defined, 3-114 stability mechanisms, 3-106– 3-114 stability operation, defined, 1-45 staff, communicating with, 8-47–8-48 staging, defined, 5-42 strategic contexts, Army, 1-65– 1-77 strategic environment, 2-32– 2-53 strategic framework, 3-119– 3-126 strategic lines of communications, control, 6-69–6-74 strategic signal brigade, 4-79– 4-80 strategic support area, 3-120 striking force, defined, 6-188 subordinates, communicating with, 8-47–8-48 support area operations, 3-156–3-157 defined, 3-156 planning considerations, 3-158–3-159 support operational areas, 4-63 support relationships, B-2 Army, B-23–B-28 joint, B-11–B-12 support to security sector reform, 4-50–4-52 supporting distance, defined, 3-135 supporting effort, defined, 3-164 surprise, A-17–A-18 survivability, 2-29–2-31 defined, 2-29 sustain large-scale combat operations, 6-90–6-97 in maritime environments, 7-63–7-78 sustainment, defined, 5-50 sustainment warfighting function, 2-12–2-13 defined, 2-12 synchronization, 3-18–3-21 defined, 3-18 systems warfare, 2-45–2-47
T
tactical command, B-49 tactical control, B-10 in the North Atlantic Treaty Organization, B-50 tactical level of warfare, 1-62– 1-64 defined, 1-62 tactical-level disintegration, 6-129–6-132 tactics, defined, 1-62 task-organizing, 6-50–6-53 defined, 6-50 teams, developing, 8-49–8-54 tempo, defined, 3-11 tenets, of operations, 3-6–3-36 tenets and imperatives, 3-5– 3-97 theater, opening the, 5-26 set and maintain, 4-61–4-62 theater armies during transition to post-conflict competition, 6-257–6-260 theater army, 2-83 assigned forces, 4-72-4-89 theater army roles, during competition, 4-56–4-58 theater army roles, during crisis, 5-53–5-55 theater aviation elements, 4-77 theater engineer command, 4-81 theater fires command or element, 4-84 theater strategic level of warfare, theater strategic level of warfare, 1-57 theater sustainment command, 4-73–4-74 theater sustainment operations, conduct, 7-69– 7-79 threat capabilities, and force projection, C-1–C-12 threat methods, 2-39–2-53 threats, 2-35–2-38 traditional principles of war, A-1–A-19 train, leaders, 4-24 training, and preparation considerations, C-44 and readiness authority, B-31 and readiness oversight, B-30 transit, protection during, 5-33– 5-38 transition, prepare to, 4-22– 4-23 back to competition, 5-65– 5-67 to armed conflict, 5-68 to competition or armed conflict, 5-64–5-68 to crisis and armed conflict, 4-103–4-110 to defense and stability, 6-252–6-254 to offense, 6-218–6-219 to post-conflict competition, 6-255–6-267 transition to post-conflict competition, brigades during, 6-265–6-267 transition to post-conflict competition, corps during, 6-261–6-262 transition to post-conflict competition, divisions during, 6-263–6-264 transition to post-conflict competition, theater armies during, 6-257–6-260 transitions, adapting formations for, 8-36–8-54 troop movement, defined, 6-157 types, of offensive operations, 6-228–6-232 of defensive operations, 6-186–6-190
U
uncertain, war, 1-32 understand, 8-29–8-30 and manage the effects of operations on units and soldiers, 3-96–3-97 the operational environment, 3-47–3-55 understanding, an operational environment, 1-76–117 defined, 3-48 unified action, and Army forces, 2-54–2-94 defined, 2-54 United States diplomatic mission, 4-32–4-33 unity of command, A-13–A-14 unity of effort, defined, 2-54
V
variables, mission, 1-118– 1-119 operational, 1-118–1-119 visualize, 8-31
W
war, and warfare, 1-26–1-77 human endeavor, 1-31 inherently chaotic, 1-32 nature of, 1-29–1-32 political purpose, 1-30 principles of, 1-33–1-34 principles of, A-1–A-26 uncertain, 1-32 warfare, and war, 1-26–1-77 characteristics of, 1-35 conventional, 1-37–1-39 information, 2-40–2-44 irregular, 1-40–1-41 levels of, 1-54–1-64 methods of, 1-36–1-41 national strategic level of, 1-56 operational level of, 1-58– 1-61 systems, 2-45–2-47 tactical level of, 1-62–1-64 theater strategic level of, 1-57 warfighting function, command and control, 2-3–2-5 defined, 2-1 fires, 2-11 intelligence, 2-9–2-10 movement and maneuver, 2-6–2-8 protection, 2-14 sustainment, 2-12–2-13 warfighting functions, 2-1–2-14 weapons of mass destruction, countering, 4-53
X-Y-Z
zone, defined, 3-130 zone reconnaissance, defined, 6-137
By Order of the Secretary of the Army:
JAMES C. MCCONVILLE
General, United States Army Chief of Staff
Official:
MARK F. AVERILL
Administrative Assistant to the Secretary of the Army